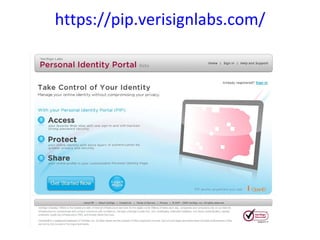
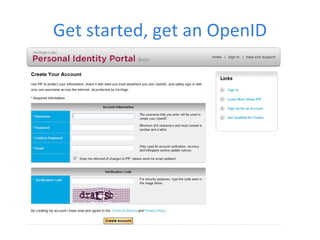
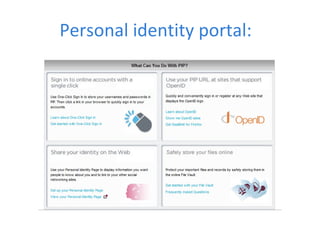
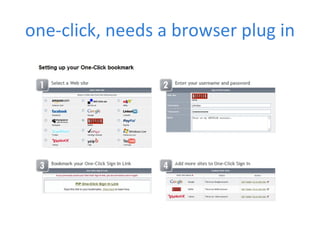
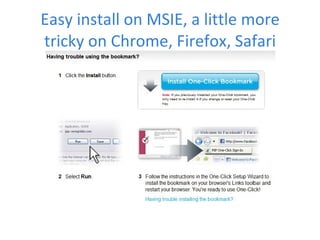
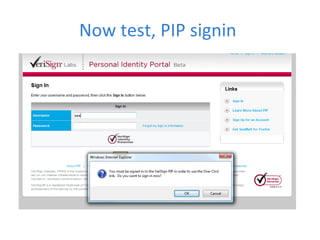
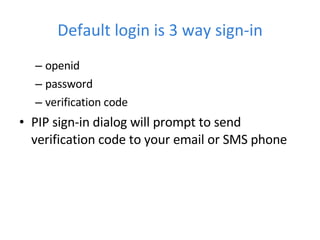
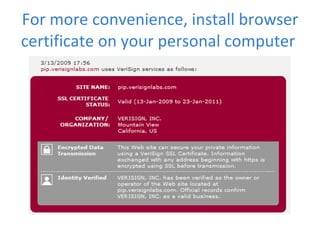
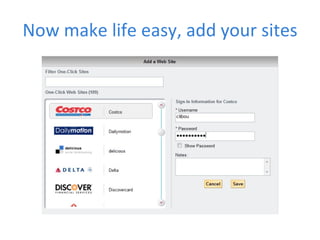
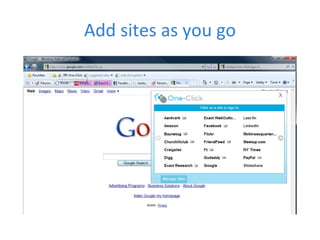
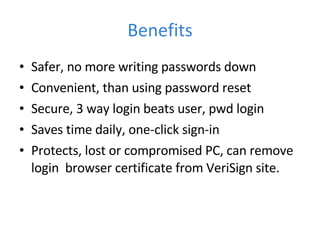
The document discusses password management and login solutions from VeriSign. It describes VeriSign's Personal Identity Portal (PIP) which allows for one-click login to websites using a browser plugin. PIP uses a three-way login with OpenID, password verification, and a code sent to your email or phone. The plugin can be installed on browsers for convenience. PIP allows users to easily add websites and offers benefits like safer login than just a username and password, convenience of one-click login, and protection if your PC is lost or compromised by removing the browser certificate.
![Rightly frustrated! Via twitter Cannot get any worse, oh yes it can You get the point now! “ FiretrUCKing password recovery XO.com / CNChost driving me crazy. has to be worst goddamn UI i've ever experienced, bar none. DIE DIE DIE.” there is no need to blank out characters for security Q answers, you idiots. all it does is make ME forget. get a FiretrUCKing clue. and immediately after i [finally] reset password successfully, it DOES NOT WORK. is there latency in your reset? i don't know but i HATE YOU.](https://image.slidesharecdn.com/verisignone-clicksign-in-090421014817-phpapp01/85/Web-site-sign-on-using-VeriSign-PIP-7-320.jpg)