Embed presentation
Download to read offline




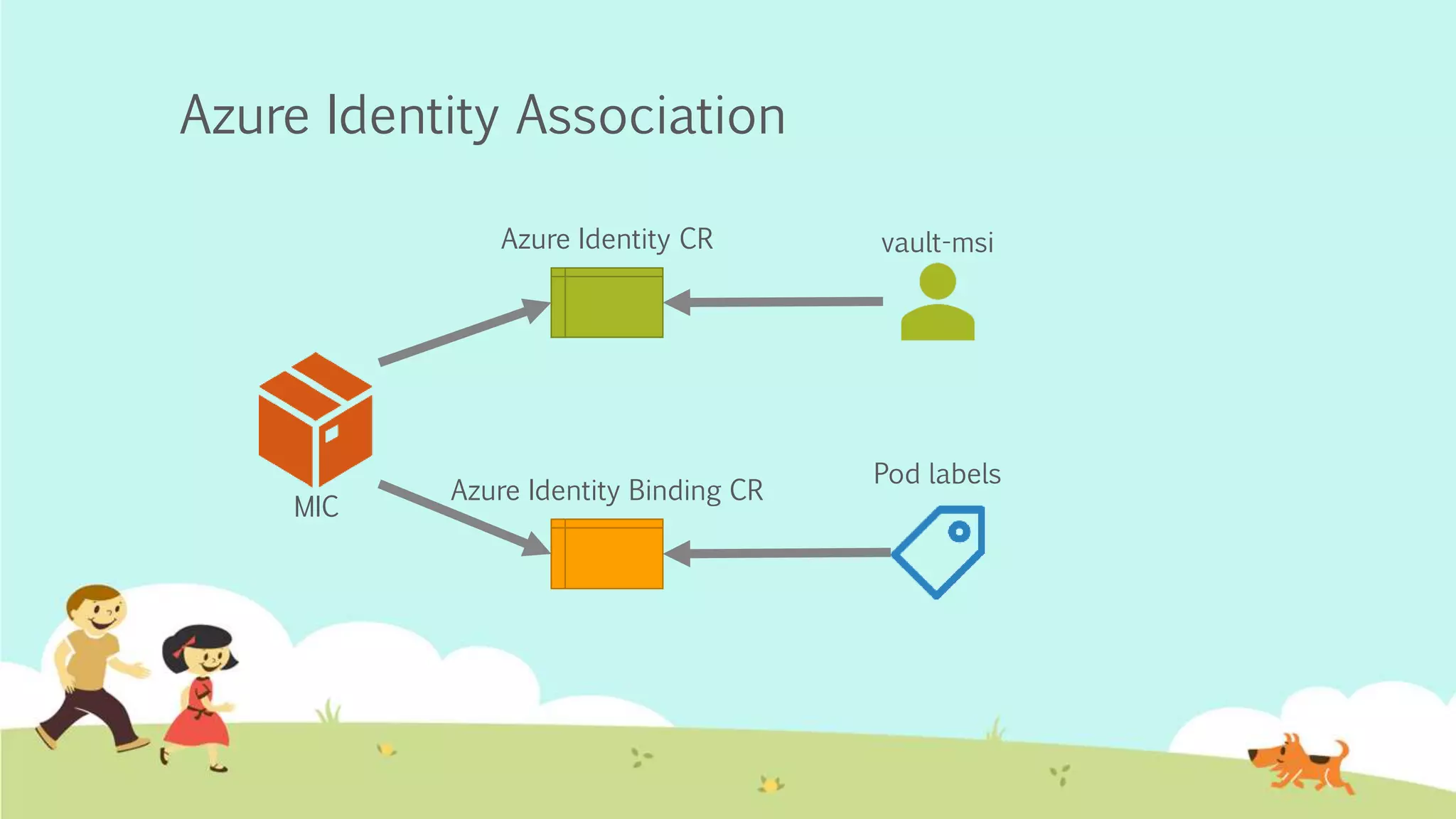



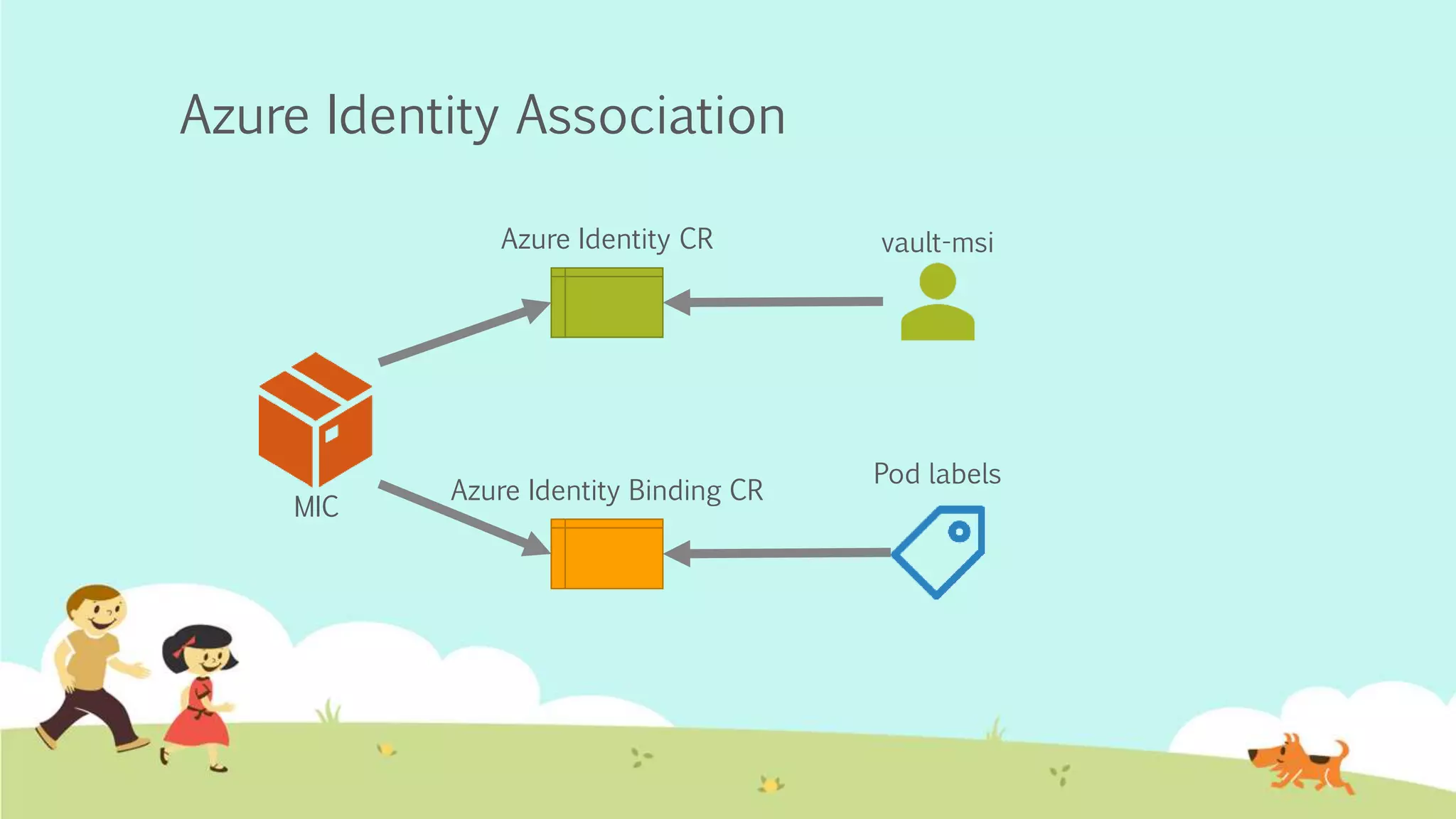
AKS Pod Identity allows assigning a service principal or managed service identity to nodes and matching pods to an Azure identity. This provides credentials through the metadata service to access Vault through Azure authentication. However, Azure authentication in Vault only supports system-assigned identities, while AKS Pod Identity uses user-assigned identities, so pods cannot currently use Azure authentication to access Vault.