Use the built-in PHP variables $_POST, $_GET, $_REQUEST or filter_in.pdf
•
0 likes•2 views
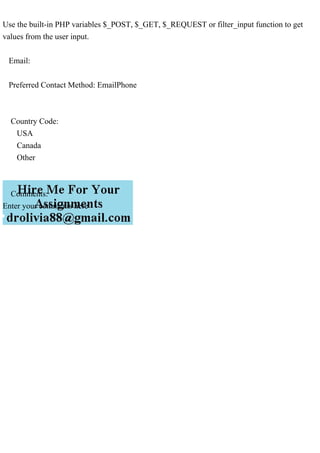
Use the built-in PHP variables $_POST, $_GET, $_REQUEST or filter_input function to get values from the user input. Email: Preferred Contact Method: EmailPhone Country Code: USA Canada Other Comments: Enter your comments here.
Report
Share
Report
Share
Download to read offline
Recommended
Una mujer de 36 a�os que se someti� a un trasplante de ri��n hace 2 .pdf

Una mujer de 36 aos que se someti a un trasplante de rin hace 2 meses desarroll fiebre, malestar
general, mialgias y leucopenia. los medicamentos incluyen prednisona y ciclosporina. una
radiografa de trax muestra infiltrados pulmonares intersticiales bilaterales. durante los siguientes
2 das, su estado respiratorio se deteriora y es intubada y ventilada mecnicamente. Se muestra el
tejido obtenido en una biopsia del pulmn. El tratamiento ms adecuado incluye la administracin
de cul de los siguientes frmacos? y por qu
aciclovir
B.ganciclovir
C. interfern-gamma
D. lamivudina.
Una empresa tiene un ciclo operativo de 120 d�as, un per�odo promedi.pdf

Una empresa tiene un ciclo operativo de 120 das, un perodo promedio de cobro de 40 das y un
perodo promedio de pago de 30 das. La antigedad promedio del inventario de la empresa es
________ das.
80
70
90
50
80
70
90
50.
Una empresa pag� por �ltima vez un dividendo de �3. Si el rendimient.pdf

Una empresa pag por ltima vez un dividendo de 3. Si el rendimiento esperado de su capital se
estima en 12% y sus acciones se cotizan actualmente en la Bolsa de Valores de Londres a 75, cul
debera ser la tasa de crecimiento de dividendos para asegurar que el precio sea consistente con el
precio de una perpetuidad creciente?.
Una cartera eficiente es una combinaci�n de activos que 0 1 pun.pdf

Una cartera eficiente es una combinacin de activos que:
0 / 1 punto
Logra la mayor covarianza posible entre sus activos.
Ofrece una tasa de rendimiento libre de riesgo al minimizar el riesgo de la cartera.
Logra el rendimiento ms alto para un riesgo dado.
Minimiza el riesgo al garantizar que solo permanezca el riesgo diversificable..
Un objetivo a corto plazo esOpci�n multiple A) una meta espec.pdf

Un objetivo a corto plazo es:
Opcin multiple
A) una meta especfica que los gerentes deben lograr en no ms de un ao para alcanzar sus metas a
largo plazo.
B) una accin especfica que usan los gerentes para alcanzar sus metas a largo plazo.
C) una tctica especfica implementada para apoyar el plan estratgico.
d) un componente especfico de la cuenta de resultados presupuestada..
Tyco International, una empresa de fabricaci�n, demand� a su ex dire.pdf

Tyco International demandó a su ex director ejecutivo Dennis Kozlowski por apropiarse indebidamente de más de $100 millones en fondos de la empresa en forma de bonificaciones y gastos personales no autorizados, incluyendo $18 millones para redecorar su apartamento y $1 millón para la fiesta de cumpleaños de su esposa en Italia con una escultura de hielo de David orinando vodka. Kozlowski actualmente cumple una sentencia de entre 8 y 25 años en prisión por estos delitos corporativos.
Un informe de an�lisis de estados financieros no incluye A) una dec.pdf

Un informe de anlisis de estados financieros no incluye: A) una declaracin del auditor, B) una
descripcin general del anlisis, C) material probatorio, D) factores clave cualitativos y
cuantitativos, E) Inferencias tales como previsiones.
El anlisis vertical se utiliza para revelar patrones en los datos que cubren dos o ms perodos
sucesivos. Verdadero o falso?
El ndice de flujo de efectivo sobre activos totales en comparacin con el ndice de activos totales
se puede utilizar como indicador de la calidad de las ganancias. Verdadero o falso.
ubat 2015te Hazine 4 78lik 2044 alt aylk bileik vadeye kadar 2,8.pdf

ubat 2015'te Hazine 4 7/8'lik 2044 alt aylk bileik vadeye kadar %2,80 getiri teklif etti. Kuponlarn
alt ayda bir dendiini kabul ederek tahvilin fiyatn hesaplayn. Nominal deerin 1.000 $ olduunu
varsayalm. (Ara hesaplamalar yuvarlamayn. Cevabnz 2 ondalk basamaa yuvarlayn.)
tahvil fiyat.
Recommended
Una mujer de 36 a�os que se someti� a un trasplante de ri��n hace 2 .pdf

Una mujer de 36 aos que se someti a un trasplante de rin hace 2 meses desarroll fiebre, malestar
general, mialgias y leucopenia. los medicamentos incluyen prednisona y ciclosporina. una
radiografa de trax muestra infiltrados pulmonares intersticiales bilaterales. durante los siguientes
2 das, su estado respiratorio se deteriora y es intubada y ventilada mecnicamente. Se muestra el
tejido obtenido en una biopsia del pulmn. El tratamiento ms adecuado incluye la administracin
de cul de los siguientes frmacos? y por qu
aciclovir
B.ganciclovir
C. interfern-gamma
D. lamivudina.
Una empresa tiene un ciclo operativo de 120 d�as, un per�odo promedi.pdf

Una empresa tiene un ciclo operativo de 120 das, un perodo promedio de cobro de 40 das y un
perodo promedio de pago de 30 das. La antigedad promedio del inventario de la empresa es
________ das.
80
70
90
50
80
70
90
50.
Una empresa pag� por �ltima vez un dividendo de �3. Si el rendimient.pdf

Una empresa pag por ltima vez un dividendo de 3. Si el rendimiento esperado de su capital se
estima en 12% y sus acciones se cotizan actualmente en la Bolsa de Valores de Londres a 75, cul
debera ser la tasa de crecimiento de dividendos para asegurar que el precio sea consistente con el
precio de una perpetuidad creciente?.
Una cartera eficiente es una combinaci�n de activos que 0 1 pun.pdf

Una cartera eficiente es una combinacin de activos que:
0 / 1 punto
Logra la mayor covarianza posible entre sus activos.
Ofrece una tasa de rendimiento libre de riesgo al minimizar el riesgo de la cartera.
Logra el rendimiento ms alto para un riesgo dado.
Minimiza el riesgo al garantizar que solo permanezca el riesgo diversificable..
Un objetivo a corto plazo esOpci�n multiple A) una meta espec.pdf

Un objetivo a corto plazo es:
Opcin multiple
A) una meta especfica que los gerentes deben lograr en no ms de un ao para alcanzar sus metas a
largo plazo.
B) una accin especfica que usan los gerentes para alcanzar sus metas a largo plazo.
C) una tctica especfica implementada para apoyar el plan estratgico.
d) un componente especfico de la cuenta de resultados presupuestada..
Tyco International, una empresa de fabricaci�n, demand� a su ex dire.pdf

Tyco International demandó a su ex director ejecutivo Dennis Kozlowski por apropiarse indebidamente de más de $100 millones en fondos de la empresa en forma de bonificaciones y gastos personales no autorizados, incluyendo $18 millones para redecorar su apartamento y $1 millón para la fiesta de cumpleaños de su esposa en Italia con una escultura de hielo de David orinando vodka. Kozlowski actualmente cumple una sentencia de entre 8 y 25 años en prisión por estos delitos corporativos.
Un informe de an�lisis de estados financieros no incluye A) una dec.pdf

Un informe de anlisis de estados financieros no incluye: A) una declaracin del auditor, B) una
descripcin general del anlisis, C) material probatorio, D) factores clave cualitativos y
cuantitativos, E) Inferencias tales como previsiones.
El anlisis vertical se utiliza para revelar patrones en los datos que cubren dos o ms perodos
sucesivos. Verdadero o falso?
El ndice de flujo de efectivo sobre activos totales en comparacin con el ndice de activos totales
se puede utilizar como indicador de la calidad de las ganancias. Verdadero o falso.
ubat 2015te Hazine 4 78lik 2044 alt aylk bileik vadeye kadar 2,8.pdf

ubat 2015'te Hazine 4 7/8'lik 2044 alt aylk bileik vadeye kadar %2,80 getiri teklif etti. Kuponlarn
alt ayda bir dendiini kabul ederek tahvilin fiyatn hesaplayn. Nominal deerin 1.000 $ olduunu
varsayalm. (Ara hesaplamalar yuvarlamayn. Cevabnz 2 ondalk basamaa yuvarlayn.)
tahvil fiyat.
Two categories of attackers include hacktivists and state actors. .pdf

Two categories of attackers include hacktivists and state actors.
What are the differences between hacktivists and state-sponsored attackers? Write a report
detailing what you were able to find..
Twitter, el popular sitio de microblogs, se ha enfrentado a graves c.pdf

El valor de las acciones de Twitter ha disminuido a pesar del crecimiento de sus ingresos, debido a su base de usuarios más pequeña en comparación con Facebook e Instagram, y su ritmo de crecimiento más lento. Los inversores también están preocupados por la fuerte competencia de otras redes sociales. Para hacer frente a estos desafíos, Twitter ha introducido nuevas funciones y ha cambiado su liderazgo ejecutivo.
Turner, Roth y Lowe son socios que comparten ingresos y p�rdidas en .pdf

Los socios Turner, Roth y Lowe, en una proporción de capital de 2:3:5 respectivamente, deciden liquidar su sociedad debido a desacuerdos. Antes de la liquidación, los activos sumaban $164,400, los pasivos $110,000 y los capitales de cada socio eran $5,700, $15,600 y $33,100. La venta de activos dejó un déficit de $44,000 que debe ser cubierto por los socios en proporción a sus participaciones.
Uber - Bir Startupn K�kenleri ve lk G�nleriDava M�terileri ele.pdf

Uber - Bir Startup'n Kkenleri ve lk Gnleri
Dava:
Mterileri eletirmek. Ksa deien iiler. Saldrgan dzenleyiciler. Aldatc yetkililer. "Her ne pahasna
olursa olsun kazan" iyeri kltrnde kural ihlali ve acmaszln vurgulanmas. Sadece yedi ylda
balangtan 70 milyar dolarlk bir iletmeye gemek iin gereken bu mu? Yoksa bu nitelendirmeler,
kskan rakiplerin eletirileri yanl m? Uber ya da dnyann nde gelen ulam hizmetlerinden biri olan
Uber Technologies Inc. olarak bilinen dk maliyetli ara arma hizmetinin heyecanl yolculuuna
uzunca bir gz atalm.
Balarken
2008 ylnda Paris'te bir konferansa katlan teknoloji giriimcileri Garrett Camp ve Travis Kalanick,
karl bir gecede taksi bulmann zorluundan ikayet ediyorlard. Bu dei tokutan, bir dmeye
dokunarak talep zerine bir araba aracak yeni teknoloji yaratma fikri geldi. The Upstarts'ta yazar
Brad Stone, en azndan irketin resmi kken efsanesinin bu olduuna dikkat ekiyor. Aslnda bu fikri
ortaya atan Camp, bir sredir arkada Kalanick ile akll telefon tabanl bir ehir arabas (lks araba veya
siyah araba) paylam hizmeti kavramn tartyordu.
Camp, yelerin favori web sitelerini dier insanlarla paylamalarna olanak tanyan keif ve neri
arama motoru StumbleUpon'un kurucu ortayd. Kalanick ("cal-a-nick" olarak telaffuz edilir) ilk
iini 18 yanda kurdu, bu bir SAT-hazrlk zel ders hizmetiydi. Bir dosya paylam ve hizmet ii olan
Scour, onun ikinci i macerasyd, ancak Kalanick'in byk abasna ve srarna ramen baarsz oldu. Bir
sonraki giriimi, bir video ak giriimi olan Red Swoosh'du. 2007'de 23 milyon dolara satld. Mart
2009'da Camp, Calgary'den eski yksek lisans rencileri Oscar Salazar ve Conrad Whelan ile
birlikte Kalanick'in "mega danman" olarak grev yapt yeni ehir arabas fikrinin denenmesinde ba
ekti. . Bunlardan biri, ilk olarak Haziran 2007'de Apple tarafndan piyasaya srlen ve yalnzca akll
telefon endstrisinde devrim yaratmakla kalmayp ayn zamanda genellikle "paylam ekonomisi"
olarak adlandrlan modern ibirliki ekonomiyi yaratmasyla tannan iPhone iin bir mobil
uygulamann prototipiydi.
Mart 2009'da UberCab olarak kurulan irket, mobil uygulama konseptini ilk olarak New York'ta
test etti, ardndan 2011'de San Francisco'da kullanclarn siyah lks bir araba talep etmek iin
iPhone'larnda bir dmeye basmalarna veya bir metin gndermelerine olanak tanyan bir hizmet
olarak resmi olarak lanse edildi. (limuzin), geleneksel bir taksinin fiyatnn sadece 1,5 kat.
Ancak o zamanki taksi irketlerinden farkl olarak, UberCab'in ayrt edici zellii, bir ulam a irketi
olarak adlandrlmasyd; bu irkette yolcular, mobil uygulama veya web sitesi araclyla hizmet talep
edebilir ve srcnn konumunu (GPS araclyla) takip edebilirdi. telefonlarnda) ve arabann tam olarak
ne zaman geleceini biliyorlar.
Birka arabas olmasna ve ok az kiinin bunu bilmesine ramen, giriim byk bir hit oldu. 2011 ylnda,
ehir ve eyalet dzenleyicilerinin srar zerine, irket adn UberCab'den (nk bir ehir arabas veya taksi
firmasnn ruhsat gerekliliklerini karlamad iin) "sper" anlamna gelen Uber'e (Almanca ber
kelimesi.
Trilogy Enterprises Inc. de Austin, Texas, es una empresa de softwar.pdf

Trilogy Enterprises Inc. de Austin, Texas, es una empresa de software de rpido crecimiento y
proporciona soluciones de software a empresas globales gigantes para mejorar las ventas y el
rendimiento. Se enorgullece de su cultura nica y poco ortodoxa. Muchos de sus enfoques de la
prctica comercial son inusuales, pero en el entorno altamente competitivo y cambiante de
Trilogy, parecen funcionar. No existe un cdigo de vestimenta y los empleados establecen sus
propios horarios, a menudo muy extensos. Tienden a socializar juntos (la edad promedio es de 26
aos), tanto en la cocina bien surtida de la oficina como en eventos patrocinados por la empresa y
viajes a lugares como clubes de baile locales y retiros en Las Vegas y Hawi. Se ha desarrollado
una jerga interna y la historia compartida de la firma ha adquirido el estatus de leyenda. La
responsabilidad es pesada y llega temprano, con una actitud de "hazlo ahora" que prescinde de
largos aprendizajes. Los nuevos reclutas reciben unas pocas semanas de capacitacin intensiva,
conocida como "Universidad de Triloga" y los participantes la describen como "ms como un
campo de entrenamiento que una escuela de negocios".
La informacin se entrega como si fuera una manguera contra incendios y se espera que los
nuevos empleados comprometan su experiencia y vitalidad en todo lo que hacen. Jeff Daniel,
director de reclutamiento universitario, admite que la empresa intensa y poco convencional no es
el empleador para todos. Pero definitivamente es un entorno donde las personas apasionadas por
lo que hacen pueden prosperar. La empresa emplea a unas 700 personas tan apasionadas. Los
gerentes de Trilogy saben que el rpido crecimiento que buscan depende de tener un personal de
las mejores personas que puedan encontrar, capacitadas rpidamente y con amplia responsabilidad
y libertad lo antes posible. El CEO Joe Liemandt dice: En una empresa de software, las personas
lo son todo. No puedes construir la prxima gran empresa de software, que es lo que estamos
tratando de hacer aqu, a menos que ests totalmente comprometido con eso. Por supuesto, los
lderes de todas las empresas dicen: "La gente lo es todo". Pero no actan en consecuencia. Trilogy
hace que encontrar a las personas adecuadas (las llama "grandes personas") sea una misin de toda
la empresa. Los reclutadores buscan activamente a las personas ms frescas, si al menos con
experiencia, en el mercado laboral, buscando ferias de carreras universitarias y departamentos de
ciencias de la computacin para personas talentosas con ambicin e instinto empresarial.
Los altos directivos llevan a cabo las primeras rondas de entrevistas y les informan a los
prospectos que se vern presionados para lograr logros pero que sern bien recompensados. Los
empleados llevan a los reclutas y a sus seres queridos a la ciudad cuando vuelan a Austin para la
visita preliminar estndar de 3 das. Un da tpico puede comenzar con entrevistas agotadoras, pero
terminar con ciclismo de montaa, patinaje sob.
Transforming Data - Creating a Data Set Creating a JOIN between two .pdf

Transforming Data - Creating a Data Set Creating a JOIN between two tables is one of several
ways to consolidate data. Which of the following is NOT true about table JOINS in Tableau?
Select one. JOINs effectively create one physical table of combined data. All JOIN types
combine data in the same way. To JOIN two tables in Tableau, you must first double-click on the
primary table, to reveal the physical layer. After performing a JOIN, we should hide one of the
JOIN keys to ensure we do not have duplicate columns..
Using the location quotients(LQ) for year 2020 for 10 provinces anal.pdf

Using the location quotients(LQ) for year 2020 for 10 provinces analyze what province has the
most relational importance in the following sectors. (i)Agriculture (ii)Forestry, fishing, mining,
quarrying, oil, and gas (iii)Manufacturing In this answer can you please mention the names of
the provinces like Manitoba, Alberta and in the answer its mentions like province A and province
B which don't indicate the province clearly instead please provide the names for them..
Using the packet tracer simulator, create a network topology that in.pdf

Using the packet tracer simulator, create a network topology that includes at least one router, one
switch, and several PCs.
4. Assign IP addresses and subnet masks to the devices in the network, making sure to use
appropriate IP addressing scheme.
5. Connect the devices together using the appropriate cables or connections, including
configuring VLANs on the switch.
6. Configure basic router and switch security features such as ACLs, port security, and VLAN
access controls.
7. Save the network diagram as a reference for future use.
8. Describe the process of creating a network diagram that documents the necessary data,
including IP addresses, subnet masks, and connections between devices, as well as the security
configurations implemented.
9. Submit the network diagram along with a brief report that explains the purpose and role of
each device in the network, as well as the security measures implemented and their justification
10. Analyse a sample medium complex network segment and identify common areas for
improvement and potential risks. 3. Using the packet tracer simulator, create a network topology
that includes at least one router, one switch, and several PCs. 4. Assign IP addresses and subnet
masks to the devices in the network, making sure to use appropriate IP addressing scheme. 5.
Connect the devices together using the appropriate cables or connections, including configuring
VLANs on the switch. 6. Configure basic router and switch security features such as ACLs, port
security, and VLAN access controls. 7. Save the network diagram as a reference for future use.
8. Describe the process of creating a network diagram that documents the necessary data,
including IP addresses, subnet masks, and connections between devices, as well as the security
configurations implemented. 9. Submit the network diagram along with a brief report that
explains the purpose and role of each device in the network, as well as the security measures
implemented and their justification 10. Analyse a sample medium complex network segment and
identify common areas for improvement and potential risks..
using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Accou.pdf

using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Account Listing Students
A Allowance
Step 18 of 40 - General Journal Entries
1415161718YouRTURN:Createjournalentriestorecordtheincreaseordecreaseintheatlowancebased
upontheamounteyouenteredintheTaccount..
Using financial data and information from Yahoo Finance only, calcul.pdf

Using financial data and information from Yahoo Finance only, calculate the intrinsic value (or
calculated price) of Tesla, Inc.
Using the Free Cash Flow Method of Valu.
using IRAC method Joseph was a team manager of an excursion in the O.pdf

using IRAC method Joseph was a team manager of an excursion in the Okavango Delta. Two of
Joseph' s team were attacked by elephants and left, claiming that it has become too dangerous.
With that Joseph promised the other colleague who remained, Karabo, that if she stayed and all
of the excursion work was completed, Karabo would get monies of one of the colleagues who
left without completing work. Karabo went on and agreed, but after the excursion was done, to
Karabo's surprise Joseph refuses to pay the money to Karabo. in 250-350 words ,advice Karabo
whether she is entitled to the extra payment.
Using Java programming language solve the followingSLL CLASS.pdf

Using Java programming language solve the following:
SLL CLASS:
//************************** SLL.java *********************************
// a generic singly linked list class
public class SLL {
private class SLLNode {
private T info;
private SLLNode next;
public SLLNode() {
this(null,null);
}
public SLLNode(T el) {
this(el,null);
}
public SLLNode(T el, SLLNode ptr) {
info = el; next = ptr;
}
}
protected SLLNode head, tail;
public SLL() {
head = tail = null;
}
public boolean isEmpty() {
return head == null;
}
public void addToHead(T el) {
head = new SLLNode(el,head);
if (tail == null)
tail = head;
}
public void addToTail(T el) {
if (!isEmpty()) {
tail.next = new SLLNode(el);
tail = tail.next;
}
else head = tail = new SLLNode(el);
}
public T deleteFromHead() { // delete the head and return its info;
if (isEmpty())
return null;
T el = head.info;
if (head == tail) // if only one node on the list;
head = tail = null;
else head = head.next;
return el;
}
public T deleteFromTail() { // delete the tail and return its info;
if (isEmpty())
return null;
T el = tail.info;
if (head == tail) // if only one node in the list;
head = tail = null;
else { // if more than one node in the list,
SLLNode tmp; // find the predecessor of tail;
for (tmp = head; tmp.next != tail; tmp = tmp.next);
tail = tmp; // the predecessor of tail becomes tail;
tail.next = null;
}
return el;
}
public void delete(T el) { // delete the node with an element el;
if (!isEmpty())
if (head == tail && el.equals(head.info)) // if only one
head = tail = null; // node on the list;
else if (el.equals(head.info)) // if more than one node on the list;
head = head.next; // and el is in the head node;
else { // if more than one node in the list
SLLNode pred, tmp;// and el is in a nonhead node;
for (pred = head, tmp = head.next;
tmp != null && !tmp.info.equals(el);
pred = pred.next, tmp = tmp.next);
if (tmp != null) { // if el was found;
pred.next = tmp.next;
if (tmp == tail) // if el is in the last node;
tail = pred;
}
}
}
@Override
public String toString() {
if(head == null)
return "[ ]";
String str = "[ ";
SLLNode tmp = head;
while(tmp != null){
str += tmp.info + " ";
tmp = tmp.next;
}
return str+"]";
}
public boolean contains(T el) {
if(head == null)
return false;
SLLNode tmp = head;
while(tmp != null){
if(tmp.info.equals(el))
return true;
tmp = tmp.next;
}
return false;
}
public int size(){
if(head == null)
return 0;
int count = 0;
SLLNode p = head;
while(p != null) {
count++;
p = p.next;
}
return count;
}
}
Part I: Programming Use the singly linked list class (Given below) to implement integers of
unlimited size. Each node of the list should store one digit of the integer. You are required to
implement the addition, subtraction and multiplication operations. In addition, provide a test
class that will do the following: It will keep asking the user to enter two integers, choose one of
the operations (addition, subtraction, multiplication) and then display the result. The program
will stop upon e.
using IRAC method Mary is an explorer and is about to set off on a.pdf

using IRAC method
Mary is an explorer and is about to set off on a ground-breaking expedition at the Debswana
mines. Rose and John , who are Mary's friends are also professional explorers themselves, they
then entered into a written agreement with each other that they will each help Mary from the
start to the the end of her expedition. John breaks the agreement and does not help Mary to the
end of her expedition, and instead returns home early.
in 250-350 words advise Mary as to whether she can sue John for breach of contract.
USING httpsraw.githubusercontent.comBeeDrHUIntroduction-to-Py.pdf

*USING 'https://raw.githubusercontent.com/BeeDrHU/Introduction-to-Python-CSPC-323-
/main/sales_forecast.csv'
please fix the errors for the RNN using python so the code can run without errors, Thank you*
##Defining Function to Build Multivariate Data Structure
def multivariate_data(dataset, target, start_index, end_index, history_size,
target_size, step, single_step=False):
data = []
labels = []
start_index = start_index + history_size
if end_index is None:
end_index = len(dataset) - target_size
for i in range(start_index, end_index):
indices = range(i-history_size, i, step)
data.append(dataset[indices])
if single_step:
labels.append(target[i+target_size])
else:
labels.append(target[i:i+target_size])
return np.array(data), np.array(labels)
##Define the Multi-step Plotting Structure
def multi_step_plot(history, true_future, prediction):
plt.figure(figsize=(12, 6))
num_in = create_time_steps(len(history))
num_out = len(true_future)
plt.plot(num_in, np.array(history[:, 1]), label='History')
plt.plot(np.arange(num_out)/STEP, np.array(true_future), 'bo',
label='True Future')
if prediction.any():
plt.plot(np.arange(num_out)/STEP, np.array(prediction), 'ro',
label='Predicted Future')
plt.legend(loc='upper left')
plt.show()
##Define Function to Plot training and Validation over Time
def plot_train_history(history, title):
loss = history.history['loss']
val_loss = history.history['val_loss']
epochs = range(len(loss))
plt.figure()
plt.plot(epochs, loss, 'b', label='Training loss')
plt.plot(epochs, val_loss, 'r', label='Validation loss')
plt.title(title)
plt.legend()
plt.show()
##How far into the past do you want the model to see?
past_history=
##How far into the future do you want the model to see?
future_target=
##
STEP=
df_val = len(dataset) - past_history - future_target
x_train_multi, y_train_multi = multivariate_data(dataset, dataset[:, 1], 0,
df_train, past_history,
future_target, STEP)
x_val_multi, y_val_multi = multivariate_data(dataset, dataset[:, 1],
df_train, df_val, past_history,
future_target, STEP)
##Define Constants
BATCH_SIZE =
BUFFER_SIZE =
EPOCHS =
EVALUATION_INTERVAL =
##Adding Layers Due to Complexity
train_data_multi = tf.data.Dataset.from_tensor_slices(())
train_data_multi = train_data_multi.cache().shuffle().batch().repeat()
val_data_multi = tf.data.Dataset.from_tensor_slices(())
val_data_multi = val_data_multi.batch().repeat()
multi_step_model = tf.keras.models.Sequential()
multi_step_model.add(tf.keras.layers.LSTM())
multi_step_model.add(tf.keras.layers.LSTM())
multi_step_model.add(tf.keras.layers.Dense(72))
multi_step_model.compile(optimizer=tf.keras.optimizers.RMSprop(clipvalue=1.0), loss='mae')
##Train the Model
multi_step_history = multi_step_model.fit(train_data_multi, epochs=,
steps_per_epoch=,
validation_data=,
validation_steps=50)
##Predict Future Data
for x, y in .take(3):
multi_step_plot(x[0], y[0], .predict(x)[0])
#Evaluate the model on the test data
test_data_multi = tf.data.Dataset.from_tensor_slices())
test_data_mu.
Using facial recognition software in shelters for victims of domesti.pdf

Using facial recognition software in shelters for victims of domestic violence raises several
ethical concerns that must be carefully considered before pursuing such a project. Firstly, using
this technology in such a sensitive and vulnerable setting raises serious concerns about privacy,
safety, and the potential abuse of power by staff. It is essential to obtain informed consent from
guests and staff and ensure that their personal information is securely stored and not misused.
Additionally, there is a risk that this technology could be used to track and monitor guests'
movements, which could violate their rights and compromise their safety. Secondly, there is the
issue of potential bias in the technology itself, as facial recognition software has been shown to
be less accurate when identifying people of colour and women, which could result in false
accusations and wrongful identification. To address these ethical concerns, engaging in a
thorough ethical review process that involves input from diverse stakeholders, including legal
experts, privacy advocates, and survivors of domestic violence is crucial. This process should
prioritize transparency, accountability, and the protection of guests and staff's rights. Other
ethical issues that designers and developers of such an application would need to address include
the potential for hacking and data breaches, the impact on civil liberties and human rights, and
the potential for unintended consequences and harm.
Response to this article is required, please provide In-Text Citations and credible references with
the response. Thanks!.
Using a bash shell write a script using getops with options that dis.pdf

Using a bash shell write a script using getops with options that display user information based on
the users shell by searching an /etc/passwd-like file. The command will allow these options:
-a Display users with all shells. Cannot be used with -s.
-f FILE Search in FILE. FILE must be formatted like /etc/passwd.
-h Display usage information.
-s SHELL Display users with SHELL shell. SHELL must be in /etc/shells. Cannot be used with -
a..
Use the modified abstract below to answer the following two question.pdf

Use the modified abstract below to answer the following two questions:
OBJECTIVES:
The human immunodeficiency virus (HIV) and M. tuberculosis co-infection is a major global
challenge. It is not properly clear why some HIV-positive people are co-infected with
tuberculosis (TB) while others are not. This study answered this question.
METHODS:
This case-control study was conducted in Tehran, Iran, in June 2004, enrolling 2388 HIV-
positive people. Cases were selected from those who were co-infected with TB and controls from
those without TB. Multiple logistic regression analysis was performed to assess the association
between M. tuberculosis/HIV co-infection and several predictors.
RESULTS:
In this study, 241 cases were compared with 2147 controls. Sex, age, marital status, educational
level, imprisonment, smoking, narcotic addiction, route of HIV transmission, previous TB
infection, isoniazid preventive therapy (IPT), antiretroviral therapy (ART), and CD4 count were
independently associated with M. tuberculosis/HIV co-infection. However, after adjusting for all
other variables in the model, only the association between M. tuberculosis/HIV co-infection and
the following predictors were of importance: imprisoned (OR=3.82), previous TB infection
(OR=5.54).
CONCLUSIONS:
Conclusions: Several predictors are associated with M. tuberculosis/HIV co-infection, but, there
are only a few indicators that significantly affect the risk of M. tuberculosis/HIV co-infection. It
is estimated that a number of predictors of M. tuberculosis/HIV co-infection still remain
unknown and require further investigations.
Original Abstract: Molaeipoor L et al. Predictors of Tuberculosis and Human Immunodeficiency
Virus Co-infection: A Case-Control Study. Epidemiol Health. 2014 Oct 30
Flag question: Question 2
Question 2
Is there enough evidence to conclude if imprisonment or prior TB infection might have caused
co-infection with tuberculosis and HIV?
A.Yes
B. No
Question 3
What additional information would help you determine if the Odds Ratios were significantly
different form the null hypothesis (OR = 1)? Select all that apply.
Group of answer choices
A. A 95% Confidence Interval
B. The study hypothesis
C. A full list of potentially confounding variables
D. The Standard Error or Variance of the Odds Ratios
Question 4
Which of the following measures of effect are statistically significant? Select all that apply.
Group of answer choices
A. Odds Ratio = 5.0, p-value = 0.04
B. Incidence Density Ratio = 2.0, 95% CI [0.9 - 3.1]
C. Attributable Risk = 0.5, 95% CI [0.1 - 1.1]
D. Population Attributable Risk = 0.1, 95% CI = [-0.1, 0.2]
E. Cumulative Incidence Ratio = 0.5, 95% CI = [0.1 - 0.9]
F. Odds Ratio = 20, p-value = 0.2.
Use the info that os provided. I just need basic sketch I H.I. H..1..pdf

Use the info that os provided. I just need basic sketch I H.I. H..1.1.11... IHH. HHHHH1.1..
IHH.1.1.H1HHH..11 HI IHI 31 IH 11 I.1.1.1 II 1 i) 1111 IH!t!l! IIH H II 1 I If
III 11 11111 HithHI..H1...I.H1.1...11.. 11H IIIII. IHH1. .HH II HI II fif
ShImu!llumu!lluhiluIlIIIIIII fintimentintititu it.
Tory and Cathy entered into a contract under which Cathy was suppose.pdf

Tory and Cathy entered into a contract under which Cathy was supposed to provide the floral
arrangements for Torys wedding on May 23. The day of the wedding arrives, but Cathy does not
deliver the floral arrangements. Cory is devastated and feels that her wedding was ruined by the
lack of floral arrangements. She sues Cathy successfully for breach of contract and then asks for
punitive damages because her wedding was ruined. The evidence presented at court only shows
that Cathy did not deliver the arrangements because she had accidentally written the wrong
delivery date on her calendar. Answer following the IRAC method..
use Selenium to write a Java code that will Scrape data from a podca.pdf

use Selenium to write a Java code that will Scrape data from a podcast site, such as episode titles,
descriptions, and ratings. Java program should do the following: Open the website in a web
browser using Selenium. Find and interact with various elements on the page (e.g., links,
buttons, text boxes) using Selenium commands. Extract data from the page using Selenium
commands, such as finding and storing text, images, or other content. Save the scraped data in a
CSV file or other format of podcast site..
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
More Related Content
More from adonisjpr
Two categories of attackers include hacktivists and state actors. .pdf

Two categories of attackers include hacktivists and state actors.
What are the differences between hacktivists and state-sponsored attackers? Write a report
detailing what you were able to find..
Twitter, el popular sitio de microblogs, se ha enfrentado a graves c.pdf

El valor de las acciones de Twitter ha disminuido a pesar del crecimiento de sus ingresos, debido a su base de usuarios más pequeña en comparación con Facebook e Instagram, y su ritmo de crecimiento más lento. Los inversores también están preocupados por la fuerte competencia de otras redes sociales. Para hacer frente a estos desafíos, Twitter ha introducido nuevas funciones y ha cambiado su liderazgo ejecutivo.
Turner, Roth y Lowe son socios que comparten ingresos y p�rdidas en .pdf

Los socios Turner, Roth y Lowe, en una proporción de capital de 2:3:5 respectivamente, deciden liquidar su sociedad debido a desacuerdos. Antes de la liquidación, los activos sumaban $164,400, los pasivos $110,000 y los capitales de cada socio eran $5,700, $15,600 y $33,100. La venta de activos dejó un déficit de $44,000 que debe ser cubierto por los socios en proporción a sus participaciones.
Uber - Bir Startupn K�kenleri ve lk G�nleriDava M�terileri ele.pdf

Uber - Bir Startup'n Kkenleri ve lk Gnleri
Dava:
Mterileri eletirmek. Ksa deien iiler. Saldrgan dzenleyiciler. Aldatc yetkililer. "Her ne pahasna
olursa olsun kazan" iyeri kltrnde kural ihlali ve acmaszln vurgulanmas. Sadece yedi ylda
balangtan 70 milyar dolarlk bir iletmeye gemek iin gereken bu mu? Yoksa bu nitelendirmeler,
kskan rakiplerin eletirileri yanl m? Uber ya da dnyann nde gelen ulam hizmetlerinden biri olan
Uber Technologies Inc. olarak bilinen dk maliyetli ara arma hizmetinin heyecanl yolculuuna
uzunca bir gz atalm.
Balarken
2008 ylnda Paris'te bir konferansa katlan teknoloji giriimcileri Garrett Camp ve Travis Kalanick,
karl bir gecede taksi bulmann zorluundan ikayet ediyorlard. Bu dei tokutan, bir dmeye
dokunarak talep zerine bir araba aracak yeni teknoloji yaratma fikri geldi. The Upstarts'ta yazar
Brad Stone, en azndan irketin resmi kken efsanesinin bu olduuna dikkat ekiyor. Aslnda bu fikri
ortaya atan Camp, bir sredir arkada Kalanick ile akll telefon tabanl bir ehir arabas (lks araba veya
siyah araba) paylam hizmeti kavramn tartyordu.
Camp, yelerin favori web sitelerini dier insanlarla paylamalarna olanak tanyan keif ve neri
arama motoru StumbleUpon'un kurucu ortayd. Kalanick ("cal-a-nick" olarak telaffuz edilir) ilk
iini 18 yanda kurdu, bu bir SAT-hazrlk zel ders hizmetiydi. Bir dosya paylam ve hizmet ii olan
Scour, onun ikinci i macerasyd, ancak Kalanick'in byk abasna ve srarna ramen baarsz oldu. Bir
sonraki giriimi, bir video ak giriimi olan Red Swoosh'du. 2007'de 23 milyon dolara satld. Mart
2009'da Camp, Calgary'den eski yksek lisans rencileri Oscar Salazar ve Conrad Whelan ile
birlikte Kalanick'in "mega danman" olarak grev yapt yeni ehir arabas fikrinin denenmesinde ba
ekti. . Bunlardan biri, ilk olarak Haziran 2007'de Apple tarafndan piyasaya srlen ve yalnzca akll
telefon endstrisinde devrim yaratmakla kalmayp ayn zamanda genellikle "paylam ekonomisi"
olarak adlandrlan modern ibirliki ekonomiyi yaratmasyla tannan iPhone iin bir mobil
uygulamann prototipiydi.
Mart 2009'da UberCab olarak kurulan irket, mobil uygulama konseptini ilk olarak New York'ta
test etti, ardndan 2011'de San Francisco'da kullanclarn siyah lks bir araba talep etmek iin
iPhone'larnda bir dmeye basmalarna veya bir metin gndermelerine olanak tanyan bir hizmet
olarak resmi olarak lanse edildi. (limuzin), geleneksel bir taksinin fiyatnn sadece 1,5 kat.
Ancak o zamanki taksi irketlerinden farkl olarak, UberCab'in ayrt edici zellii, bir ulam a irketi
olarak adlandrlmasyd; bu irkette yolcular, mobil uygulama veya web sitesi araclyla hizmet talep
edebilir ve srcnn konumunu (GPS araclyla) takip edebilirdi. telefonlarnda) ve arabann tam olarak
ne zaman geleceini biliyorlar.
Birka arabas olmasna ve ok az kiinin bunu bilmesine ramen, giriim byk bir hit oldu. 2011 ylnda,
ehir ve eyalet dzenleyicilerinin srar zerine, irket adn UberCab'den (nk bir ehir arabas veya taksi
firmasnn ruhsat gerekliliklerini karlamad iin) "sper" anlamna gelen Uber'e (Almanca ber
kelimesi.
Trilogy Enterprises Inc. de Austin, Texas, es una empresa de softwar.pdf

Trilogy Enterprises Inc. de Austin, Texas, es una empresa de software de rpido crecimiento y
proporciona soluciones de software a empresas globales gigantes para mejorar las ventas y el
rendimiento. Se enorgullece de su cultura nica y poco ortodoxa. Muchos de sus enfoques de la
prctica comercial son inusuales, pero en el entorno altamente competitivo y cambiante de
Trilogy, parecen funcionar. No existe un cdigo de vestimenta y los empleados establecen sus
propios horarios, a menudo muy extensos. Tienden a socializar juntos (la edad promedio es de 26
aos), tanto en la cocina bien surtida de la oficina como en eventos patrocinados por la empresa y
viajes a lugares como clubes de baile locales y retiros en Las Vegas y Hawi. Se ha desarrollado
una jerga interna y la historia compartida de la firma ha adquirido el estatus de leyenda. La
responsabilidad es pesada y llega temprano, con una actitud de "hazlo ahora" que prescinde de
largos aprendizajes. Los nuevos reclutas reciben unas pocas semanas de capacitacin intensiva,
conocida como "Universidad de Triloga" y los participantes la describen como "ms como un
campo de entrenamiento que una escuela de negocios".
La informacin se entrega como si fuera una manguera contra incendios y se espera que los
nuevos empleados comprometan su experiencia y vitalidad en todo lo que hacen. Jeff Daniel,
director de reclutamiento universitario, admite que la empresa intensa y poco convencional no es
el empleador para todos. Pero definitivamente es un entorno donde las personas apasionadas por
lo que hacen pueden prosperar. La empresa emplea a unas 700 personas tan apasionadas. Los
gerentes de Trilogy saben que el rpido crecimiento que buscan depende de tener un personal de
las mejores personas que puedan encontrar, capacitadas rpidamente y con amplia responsabilidad
y libertad lo antes posible. El CEO Joe Liemandt dice: En una empresa de software, las personas
lo son todo. No puedes construir la prxima gran empresa de software, que es lo que estamos
tratando de hacer aqu, a menos que ests totalmente comprometido con eso. Por supuesto, los
lderes de todas las empresas dicen: "La gente lo es todo". Pero no actan en consecuencia. Trilogy
hace que encontrar a las personas adecuadas (las llama "grandes personas") sea una misin de toda
la empresa. Los reclutadores buscan activamente a las personas ms frescas, si al menos con
experiencia, en el mercado laboral, buscando ferias de carreras universitarias y departamentos de
ciencias de la computacin para personas talentosas con ambicin e instinto empresarial.
Los altos directivos llevan a cabo las primeras rondas de entrevistas y les informan a los
prospectos que se vern presionados para lograr logros pero que sern bien recompensados. Los
empleados llevan a los reclutas y a sus seres queridos a la ciudad cuando vuelan a Austin para la
visita preliminar estndar de 3 das. Un da tpico puede comenzar con entrevistas agotadoras, pero
terminar con ciclismo de montaa, patinaje sob.
Transforming Data - Creating a Data Set Creating a JOIN between two .pdf

Transforming Data - Creating a Data Set Creating a JOIN between two tables is one of several
ways to consolidate data. Which of the following is NOT true about table JOINS in Tableau?
Select one. JOINs effectively create one physical table of combined data. All JOIN types
combine data in the same way. To JOIN two tables in Tableau, you must first double-click on the
primary table, to reveal the physical layer. After performing a JOIN, we should hide one of the
JOIN keys to ensure we do not have duplicate columns..
Using the location quotients(LQ) for year 2020 for 10 provinces anal.pdf

Using the location quotients(LQ) for year 2020 for 10 provinces analyze what province has the
most relational importance in the following sectors. (i)Agriculture (ii)Forestry, fishing, mining,
quarrying, oil, and gas (iii)Manufacturing In this answer can you please mention the names of
the provinces like Manitoba, Alberta and in the answer its mentions like province A and province
B which don't indicate the province clearly instead please provide the names for them..
Using the packet tracer simulator, create a network topology that in.pdf

Using the packet tracer simulator, create a network topology that includes at least one router, one
switch, and several PCs.
4. Assign IP addresses and subnet masks to the devices in the network, making sure to use
appropriate IP addressing scheme.
5. Connect the devices together using the appropriate cables or connections, including
configuring VLANs on the switch.
6. Configure basic router and switch security features such as ACLs, port security, and VLAN
access controls.
7. Save the network diagram as a reference for future use.
8. Describe the process of creating a network diagram that documents the necessary data,
including IP addresses, subnet masks, and connections between devices, as well as the security
configurations implemented.
9. Submit the network diagram along with a brief report that explains the purpose and role of
each device in the network, as well as the security measures implemented and their justification
10. Analyse a sample medium complex network segment and identify common areas for
improvement and potential risks. 3. Using the packet tracer simulator, create a network topology
that includes at least one router, one switch, and several PCs. 4. Assign IP addresses and subnet
masks to the devices in the network, making sure to use appropriate IP addressing scheme. 5.
Connect the devices together using the appropriate cables or connections, including configuring
VLANs on the switch. 6. Configure basic router and switch security features such as ACLs, port
security, and VLAN access controls. 7. Save the network diagram as a reference for future use.
8. Describe the process of creating a network diagram that documents the necessary data,
including IP addresses, subnet masks, and connections between devices, as well as the security
configurations implemented. 9. Submit the network diagram along with a brief report that
explains the purpose and role of each device in the network, as well as the security measures
implemented and their justification 10. Analyse a sample medium complex network segment and
identify common areas for improvement and potential risks..
using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Accou.pdf

using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Account Listing Students
A Allowance
Step 18 of 40 - General Journal Entries
1415161718YouRTURN:Createjournalentriestorecordtheincreaseordecreaseintheatlowancebased
upontheamounteyouenteredintheTaccount..
Using financial data and information from Yahoo Finance only, calcul.pdf

Using financial data and information from Yahoo Finance only, calculate the intrinsic value (or
calculated price) of Tesla, Inc.
Using the Free Cash Flow Method of Valu.
using IRAC method Joseph was a team manager of an excursion in the O.pdf

using IRAC method Joseph was a team manager of an excursion in the Okavango Delta. Two of
Joseph' s team were attacked by elephants and left, claiming that it has become too dangerous.
With that Joseph promised the other colleague who remained, Karabo, that if she stayed and all
of the excursion work was completed, Karabo would get monies of one of the colleagues who
left without completing work. Karabo went on and agreed, but after the excursion was done, to
Karabo's surprise Joseph refuses to pay the money to Karabo. in 250-350 words ,advice Karabo
whether she is entitled to the extra payment.
Using Java programming language solve the followingSLL CLASS.pdf

Using Java programming language solve the following:
SLL CLASS:
//************************** SLL.java *********************************
// a generic singly linked list class
public class SLL {
private class SLLNode {
private T info;
private SLLNode next;
public SLLNode() {
this(null,null);
}
public SLLNode(T el) {
this(el,null);
}
public SLLNode(T el, SLLNode ptr) {
info = el; next = ptr;
}
}
protected SLLNode head, tail;
public SLL() {
head = tail = null;
}
public boolean isEmpty() {
return head == null;
}
public void addToHead(T el) {
head = new SLLNode(el,head);
if (tail == null)
tail = head;
}
public void addToTail(T el) {
if (!isEmpty()) {
tail.next = new SLLNode(el);
tail = tail.next;
}
else head = tail = new SLLNode(el);
}
public T deleteFromHead() { // delete the head and return its info;
if (isEmpty())
return null;
T el = head.info;
if (head == tail) // if only one node on the list;
head = tail = null;
else head = head.next;
return el;
}
public T deleteFromTail() { // delete the tail and return its info;
if (isEmpty())
return null;
T el = tail.info;
if (head == tail) // if only one node in the list;
head = tail = null;
else { // if more than one node in the list,
SLLNode tmp; // find the predecessor of tail;
for (tmp = head; tmp.next != tail; tmp = tmp.next);
tail = tmp; // the predecessor of tail becomes tail;
tail.next = null;
}
return el;
}
public void delete(T el) { // delete the node with an element el;
if (!isEmpty())
if (head == tail && el.equals(head.info)) // if only one
head = tail = null; // node on the list;
else if (el.equals(head.info)) // if more than one node on the list;
head = head.next; // and el is in the head node;
else { // if more than one node in the list
SLLNode pred, tmp;// and el is in a nonhead node;
for (pred = head, tmp = head.next;
tmp != null && !tmp.info.equals(el);
pred = pred.next, tmp = tmp.next);
if (tmp != null) { // if el was found;
pred.next = tmp.next;
if (tmp == tail) // if el is in the last node;
tail = pred;
}
}
}
@Override
public String toString() {
if(head == null)
return "[ ]";
String str = "[ ";
SLLNode tmp = head;
while(tmp != null){
str += tmp.info + " ";
tmp = tmp.next;
}
return str+"]";
}
public boolean contains(T el) {
if(head == null)
return false;
SLLNode tmp = head;
while(tmp != null){
if(tmp.info.equals(el))
return true;
tmp = tmp.next;
}
return false;
}
public int size(){
if(head == null)
return 0;
int count = 0;
SLLNode p = head;
while(p != null) {
count++;
p = p.next;
}
return count;
}
}
Part I: Programming Use the singly linked list class (Given below) to implement integers of
unlimited size. Each node of the list should store one digit of the integer. You are required to
implement the addition, subtraction and multiplication operations. In addition, provide a test
class that will do the following: It will keep asking the user to enter two integers, choose one of
the operations (addition, subtraction, multiplication) and then display the result. The program
will stop upon e.
using IRAC method Mary is an explorer and is about to set off on a.pdf

using IRAC method
Mary is an explorer and is about to set off on a ground-breaking expedition at the Debswana
mines. Rose and John , who are Mary's friends are also professional explorers themselves, they
then entered into a written agreement with each other that they will each help Mary from the
start to the the end of her expedition. John breaks the agreement and does not help Mary to the
end of her expedition, and instead returns home early.
in 250-350 words advise Mary as to whether she can sue John for breach of contract.
USING httpsraw.githubusercontent.comBeeDrHUIntroduction-to-Py.pdf

*USING 'https://raw.githubusercontent.com/BeeDrHU/Introduction-to-Python-CSPC-323-
/main/sales_forecast.csv'
please fix the errors for the RNN using python so the code can run without errors, Thank you*
##Defining Function to Build Multivariate Data Structure
def multivariate_data(dataset, target, start_index, end_index, history_size,
target_size, step, single_step=False):
data = []
labels = []
start_index = start_index + history_size
if end_index is None:
end_index = len(dataset) - target_size
for i in range(start_index, end_index):
indices = range(i-history_size, i, step)
data.append(dataset[indices])
if single_step:
labels.append(target[i+target_size])
else:
labels.append(target[i:i+target_size])
return np.array(data), np.array(labels)
##Define the Multi-step Plotting Structure
def multi_step_plot(history, true_future, prediction):
plt.figure(figsize=(12, 6))
num_in = create_time_steps(len(history))
num_out = len(true_future)
plt.plot(num_in, np.array(history[:, 1]), label='History')
plt.plot(np.arange(num_out)/STEP, np.array(true_future), 'bo',
label='True Future')
if prediction.any():
plt.plot(np.arange(num_out)/STEP, np.array(prediction), 'ro',
label='Predicted Future')
plt.legend(loc='upper left')
plt.show()
##Define Function to Plot training and Validation over Time
def plot_train_history(history, title):
loss = history.history['loss']
val_loss = history.history['val_loss']
epochs = range(len(loss))
plt.figure()
plt.plot(epochs, loss, 'b', label='Training loss')
plt.plot(epochs, val_loss, 'r', label='Validation loss')
plt.title(title)
plt.legend()
plt.show()
##How far into the past do you want the model to see?
past_history=
##How far into the future do you want the model to see?
future_target=
##
STEP=
df_val = len(dataset) - past_history - future_target
x_train_multi, y_train_multi = multivariate_data(dataset, dataset[:, 1], 0,
df_train, past_history,
future_target, STEP)
x_val_multi, y_val_multi = multivariate_data(dataset, dataset[:, 1],
df_train, df_val, past_history,
future_target, STEP)
##Define Constants
BATCH_SIZE =
BUFFER_SIZE =
EPOCHS =
EVALUATION_INTERVAL =
##Adding Layers Due to Complexity
train_data_multi = tf.data.Dataset.from_tensor_slices(())
train_data_multi = train_data_multi.cache().shuffle().batch().repeat()
val_data_multi = tf.data.Dataset.from_tensor_slices(())
val_data_multi = val_data_multi.batch().repeat()
multi_step_model = tf.keras.models.Sequential()
multi_step_model.add(tf.keras.layers.LSTM())
multi_step_model.add(tf.keras.layers.LSTM())
multi_step_model.add(tf.keras.layers.Dense(72))
multi_step_model.compile(optimizer=tf.keras.optimizers.RMSprop(clipvalue=1.0), loss='mae')
##Train the Model
multi_step_history = multi_step_model.fit(train_data_multi, epochs=,
steps_per_epoch=,
validation_data=,
validation_steps=50)
##Predict Future Data
for x, y in .take(3):
multi_step_plot(x[0], y[0], .predict(x)[0])
#Evaluate the model on the test data
test_data_multi = tf.data.Dataset.from_tensor_slices())
test_data_mu.
Using facial recognition software in shelters for victims of domesti.pdf

Using facial recognition software in shelters for victims of domestic violence raises several
ethical concerns that must be carefully considered before pursuing such a project. Firstly, using
this technology in such a sensitive and vulnerable setting raises serious concerns about privacy,
safety, and the potential abuse of power by staff. It is essential to obtain informed consent from
guests and staff and ensure that their personal information is securely stored and not misused.
Additionally, there is a risk that this technology could be used to track and monitor guests'
movements, which could violate their rights and compromise their safety. Secondly, there is the
issue of potential bias in the technology itself, as facial recognition software has been shown to
be less accurate when identifying people of colour and women, which could result in false
accusations and wrongful identification. To address these ethical concerns, engaging in a
thorough ethical review process that involves input from diverse stakeholders, including legal
experts, privacy advocates, and survivors of domestic violence is crucial. This process should
prioritize transparency, accountability, and the protection of guests and staff's rights. Other
ethical issues that designers and developers of such an application would need to address include
the potential for hacking and data breaches, the impact on civil liberties and human rights, and
the potential for unintended consequences and harm.
Response to this article is required, please provide In-Text Citations and credible references with
the response. Thanks!.
Using a bash shell write a script using getops with options that dis.pdf

Using a bash shell write a script using getops with options that display user information based on
the users shell by searching an /etc/passwd-like file. The command will allow these options:
-a Display users with all shells. Cannot be used with -s.
-f FILE Search in FILE. FILE must be formatted like /etc/passwd.
-h Display usage information.
-s SHELL Display users with SHELL shell. SHELL must be in /etc/shells. Cannot be used with -
a..
Use the modified abstract below to answer the following two question.pdf

Use the modified abstract below to answer the following two questions:
OBJECTIVES:
The human immunodeficiency virus (HIV) and M. tuberculosis co-infection is a major global
challenge. It is not properly clear why some HIV-positive people are co-infected with
tuberculosis (TB) while others are not. This study answered this question.
METHODS:
This case-control study was conducted in Tehran, Iran, in June 2004, enrolling 2388 HIV-
positive people. Cases were selected from those who were co-infected with TB and controls from
those without TB. Multiple logistic regression analysis was performed to assess the association
between M. tuberculosis/HIV co-infection and several predictors.
RESULTS:
In this study, 241 cases were compared with 2147 controls. Sex, age, marital status, educational
level, imprisonment, smoking, narcotic addiction, route of HIV transmission, previous TB
infection, isoniazid preventive therapy (IPT), antiretroviral therapy (ART), and CD4 count were
independently associated with M. tuberculosis/HIV co-infection. However, after adjusting for all
other variables in the model, only the association between M. tuberculosis/HIV co-infection and
the following predictors were of importance: imprisoned (OR=3.82), previous TB infection
(OR=5.54).
CONCLUSIONS:
Conclusions: Several predictors are associated with M. tuberculosis/HIV co-infection, but, there
are only a few indicators that significantly affect the risk of M. tuberculosis/HIV co-infection. It
is estimated that a number of predictors of M. tuberculosis/HIV co-infection still remain
unknown and require further investigations.
Original Abstract: Molaeipoor L et al. Predictors of Tuberculosis and Human Immunodeficiency
Virus Co-infection: A Case-Control Study. Epidemiol Health. 2014 Oct 30
Flag question: Question 2
Question 2
Is there enough evidence to conclude if imprisonment or prior TB infection might have caused
co-infection with tuberculosis and HIV?
A.Yes
B. No
Question 3
What additional information would help you determine if the Odds Ratios were significantly
different form the null hypothesis (OR = 1)? Select all that apply.
Group of answer choices
A. A 95% Confidence Interval
B. The study hypothesis
C. A full list of potentially confounding variables
D. The Standard Error or Variance of the Odds Ratios
Question 4
Which of the following measures of effect are statistically significant? Select all that apply.
Group of answer choices
A. Odds Ratio = 5.0, p-value = 0.04
B. Incidence Density Ratio = 2.0, 95% CI [0.9 - 3.1]
C. Attributable Risk = 0.5, 95% CI [0.1 - 1.1]
D. Population Attributable Risk = 0.1, 95% CI = [-0.1, 0.2]
E. Cumulative Incidence Ratio = 0.5, 95% CI = [0.1 - 0.9]
F. Odds Ratio = 20, p-value = 0.2.
Use the info that os provided. I just need basic sketch I H.I. H..1..pdf

Use the info that os provided. I just need basic sketch I H.I. H..1.1.11... IHH. HHHHH1.1..
IHH.1.1.H1HHH..11 HI IHI 31 IH 11 I.1.1.1 II 1 i) 1111 IH!t!l! IIH H II 1 I If
III 11 11111 HithHI..H1...I.H1.1...11.. 11H IIIII. IHH1. .HH II HI II fif
ShImu!llumu!lluhiluIlIIIIIII fintimentintititu it.
Tory and Cathy entered into a contract under which Cathy was suppose.pdf

Tory and Cathy entered into a contract under which Cathy was supposed to provide the floral
arrangements for Torys wedding on May 23. The day of the wedding arrives, but Cathy does not
deliver the floral arrangements. Cory is devastated and feels that her wedding was ruined by the
lack of floral arrangements. She sues Cathy successfully for breach of contract and then asks for
punitive damages because her wedding was ruined. The evidence presented at court only shows
that Cathy did not deliver the arrangements because she had accidentally written the wrong
delivery date on her calendar. Answer following the IRAC method..
use Selenium to write a Java code that will Scrape data from a podca.pdf

use Selenium to write a Java code that will Scrape data from a podcast site, such as episode titles,
descriptions, and ratings. Java program should do the following: Open the website in a web
browser using Selenium. Find and interact with various elements on the page (e.g., links,
buttons, text boxes) using Selenium commands. Extract data from the page using Selenium
commands, such as finding and storing text, images, or other content. Save the scraped data in a
CSV file or other format of podcast site..
More from adonisjpr (20)
Two categories of attackers include hacktivists and state actors. .pdf

Two categories of attackers include hacktivists and state actors. .pdf
Twitter, el popular sitio de microblogs, se ha enfrentado a graves c.pdf

Twitter, el popular sitio de microblogs, se ha enfrentado a graves c.pdf
Turner, Roth y Lowe son socios que comparten ingresos y p�rdidas en .pdf

Turner, Roth y Lowe son socios que comparten ingresos y p�rdidas en .pdf
Uber - Bir Startupn K�kenleri ve lk G�nleriDava M�terileri ele.pdf

Uber - Bir Startupn K�kenleri ve lk G�nleriDava M�terileri ele.pdf
Trilogy Enterprises Inc. de Austin, Texas, es una empresa de softwar.pdf

Trilogy Enterprises Inc. de Austin, Texas, es una empresa de softwar.pdf
Transforming Data - Creating a Data Set Creating a JOIN between two .pdf

Transforming Data - Creating a Data Set Creating a JOIN between two .pdf
Using the location quotients(LQ) for year 2020 for 10 provinces anal.pdf

Using the location quotients(LQ) for year 2020 for 10 provinces anal.pdf
Using the packet tracer simulator, create a network topology that in.pdf

Using the packet tracer simulator, create a network topology that in.pdf
using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Accou.pdf

using silde 2 to answer silde 1 and 3 Step 17 of 40 - Create T Accou.pdf
Using financial data and information from Yahoo Finance only, calcul.pdf

Using financial data and information from Yahoo Finance only, calcul.pdf
using IRAC method Joseph was a team manager of an excursion in the O.pdf

using IRAC method Joseph was a team manager of an excursion in the O.pdf
Using Java programming language solve the followingSLL CLASS.pdf

Using Java programming language solve the followingSLL CLASS.pdf
using IRAC method Mary is an explorer and is about to set off on a.pdf

using IRAC method Mary is an explorer and is about to set off on a.pdf
USING httpsraw.githubusercontent.comBeeDrHUIntroduction-to-Py.pdf

USING httpsraw.githubusercontent.comBeeDrHUIntroduction-to-Py.pdf
Using facial recognition software in shelters for victims of domesti.pdf

Using facial recognition software in shelters for victims of domesti.pdf
Using a bash shell write a script using getops with options that dis.pdf

Using a bash shell write a script using getops with options that dis.pdf
Use the modified abstract below to answer the following two question.pdf

Use the modified abstract below to answer the following two question.pdf
Use the info that os provided. I just need basic sketch I H.I. H..1..pdf

Use the info that os provided. I just need basic sketch I H.I. H..1..pdf
Tory and Cathy entered into a contract under which Cathy was suppose.pdf

Tory and Cathy entered into a contract under which Cathy was suppose.pdf
use Selenium to write a Java code that will Scrape data from a podca.pdf

use Selenium to write a Java code that will Scrape data from a podca.pdf
Recently uploaded
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
Advanced Java[Extra Concepts, Not Difficult].docx![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This is part 2 of my Java Learning Journey. This contains Hashing, ArrayList, LinkedList, Date and Time Classes, Calendar Class and more.
The Diamonds of 2023-2024 in the IGRA collection

A review of the growth of the Israel Genealogy Research Association Database Collection for the last 12 months. Our collection is now passed the 3 million mark and still growing. See which archives have contributed the most. See the different types of records we have, and which years have had records added. You can also see what we have for the future.
South African Journal of Science: Writing with integrity workshop (2024)

South African Journal of Science: Writing with integrity workshop (2024)Academy of Science of South Africa
A workshop hosted by the South African Journal of Science aimed at postgraduate students and early career researchers with little or no experience in writing and publishing journal articles.Chapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptxMohd Adib Abd Muin, Senior Lecturer at Universiti Utara Malaysia
This slide is special for master students (MIBS & MIFB) in UUM. Also useful for readers who are interested in the topic of contemporary Islamic banking.
Introduction to AI for Nonprofits with Tapp Network

Dive into the world of AI! Experts Jon Hill and Tareq Monaur will guide you through AI's role in enhancing nonprofit websites and basic marketing strategies, making it easy to understand and apply.
Top five deadliest dog breeds in America

Thinking of getting a dog? Be aware that breeds like Pit Bulls, Rottweilers, and German Shepherds can be loyal and dangerous. Proper training and socialization are crucial to preventing aggressive behaviors. Ensure safety by understanding their needs and always supervising interactions. Stay safe, and enjoy your furry friends!
Types of Herbal Cosmetics its standardization.

Physiology and chemistry of skin and pigmentation, hairs, scalp, lips and nail, Cleansing cream, Lotions, Face powders, Face packs, Lipsticks, Bath products, soaps and baby product,
Preparation and standardization of the following : Tonic, Bleaches, Dentifrices and Mouth washes & Tooth Pastes, Cosmetics for Nails.
Assessment and Planning in Educational technology.pptx

In an education system, it is understood that assessment is only for the students, but on the other hand, the Assessment of teachers is also an important aspect of the education system that ensures teachers are providing high-quality instruction to students. The assessment process can be used to provide feedback and support for professional development, to inform decisions about teacher retention or promotion, or to evaluate teacher effectiveness for accountability purposes.
Main Java[All of the Base Concepts}.docx

This is part 1 of my Java Learning Journey. This Contains Custom methods, classes, constructors, packages, multithreading , try- catch block, finally block and more.
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama UniversityAkanksha trivedi rama nursing college kanpur.
Natural birth techniques are various type such as/ water birth , alexender method, hypnosis, bradley method, lamaze method etcHow to Build a Module in Odoo 17 Using the Scaffold Method

Odoo provides an option for creating a module by using a single line command. By using this command the user can make a whole structure of a module. It is very easy for a beginner to make a module. There is no need to make each file manually. This slide will show how to create a module using the scaffold method.
Hindi varnamala | hindi alphabet PPT.pdf

हिंदी वर्णमाला पीपीटी, hindi alphabet PPT presentation, hindi varnamala PPT, Hindi Varnamala pdf, हिंदी स्वर, हिंदी व्यंजन, sikhiye hindi varnmala, dr. mulla adam ali, hindi language and literature, hindi alphabet with drawing, hindi alphabet pdf, hindi varnamala for childrens, hindi language, hindi varnamala practice for kids, https://www.drmullaadamali.com
Pollock and Snow "DEIA in the Scholarly Landscape, Session One: Setting Expec...

Pollock and Snow "DEIA in the Scholarly Landscape, Session One: Setting Expec...National Information Standards Organization (NISO)
This presentation was provided by Steph Pollock of The American Psychological Association’s Journals Program, and Damita Snow, of The American Society of Civil Engineers (ASCE), for the initial session of NISO's 2024 Training Series "DEIA in the Scholarly Landscape." Session One: 'Setting Expectations: a DEIA Primer,' was held June 6, 2024.Recently uploaded (20)
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
Liberal Approach to the Study of Indian Politics.pdf

Liberal Approach to the Study of Indian Politics.pdf
South African Journal of Science: Writing with integrity workshop (2024)

South African Journal of Science: Writing with integrity workshop (2024)
Chapter 4 - Islamic Financial Institutions in Malaysia.pptx

Chapter 4 - Islamic Financial Institutions in Malaysia.pptx
Introduction to AI for Nonprofits with Tapp Network

Introduction to AI for Nonprofits with Tapp Network
Digital Artefact 1 - Tiny Home Environmental Design

Digital Artefact 1 - Tiny Home Environmental Design
Assessment and Planning in Educational technology.pptx

Assessment and Planning in Educational technology.pptx
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama University
How to Build a Module in Odoo 17 Using the Scaffold Method

How to Build a Module in Odoo 17 Using the Scaffold Method
Pollock and Snow "DEIA in the Scholarly Landscape, Session One: Setting Expec...

Pollock and Snow "DEIA in the Scholarly Landscape, Session One: Setting Expec...
Use the built-in PHP variables $_POST, $_GET, $_REQUEST or filter_in.pdf
- 1. Use the built-in PHP variables $_POST, $_GET, $_REQUEST or filter_input function to get values from the user input. Email: Preferred Contact Method: EmailPhone Country Code: USA Canada Other Comments: Enter your comments here