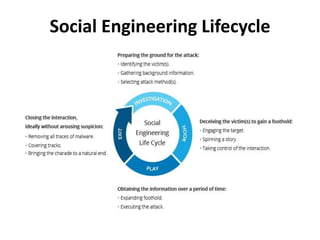
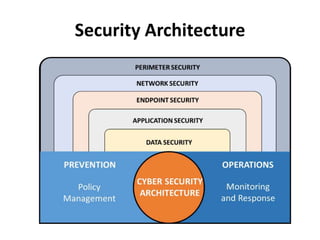
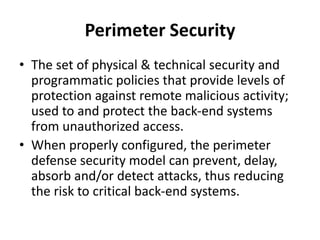
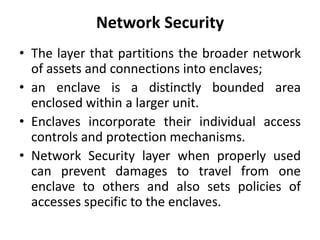
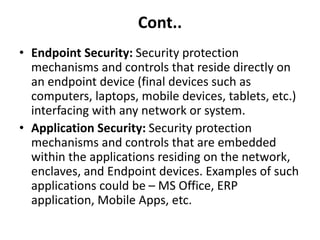
This document provides an introduction to cyber security, including definitions and key concepts. It describes cyber security as protecting internet-connected systems from malicious attacks. The document then outlines different types of cyber security such as network security, application security, information security, identity management, cloud security, mobile security, endpoint security, and IoT security. It discusses the importance of cyber security and its goals of ensuring data protection, confidentiality, integrity, and availability. Finally, it defines common cyber security terminology.