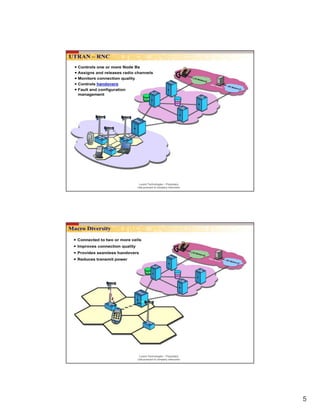
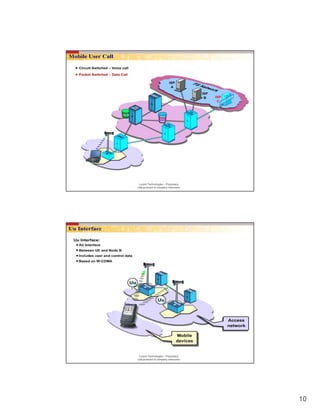
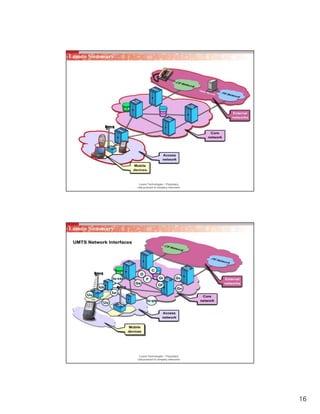
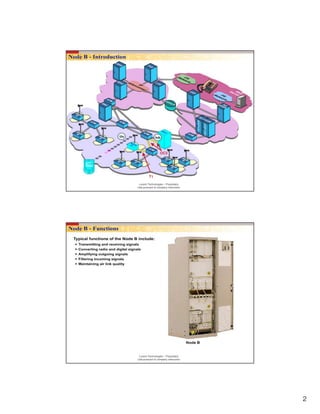
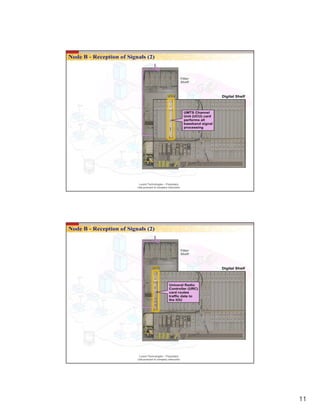
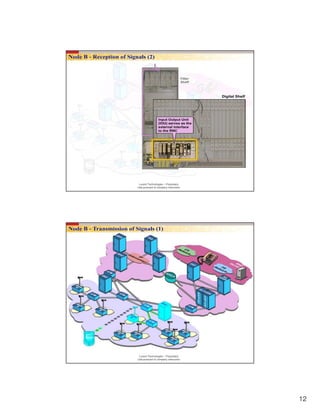
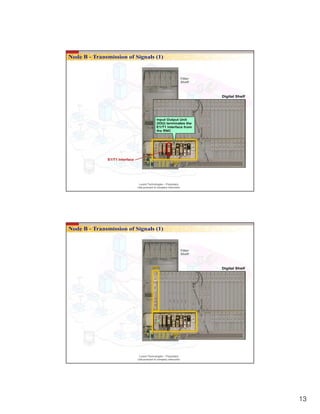
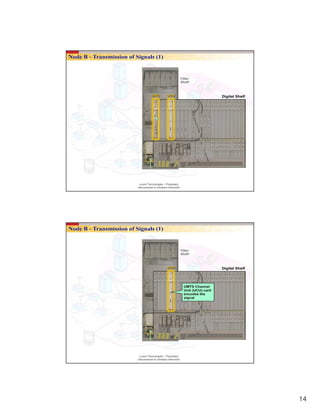
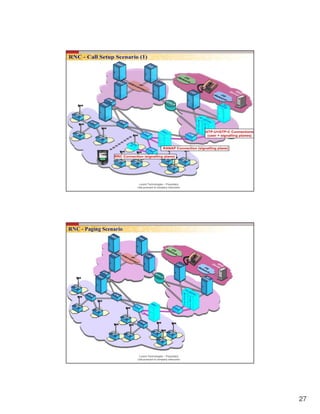
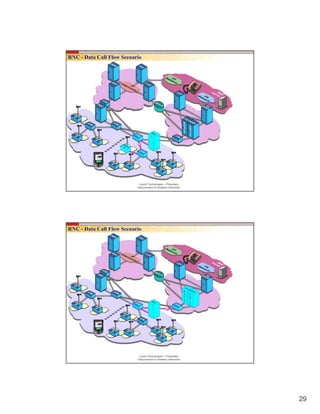
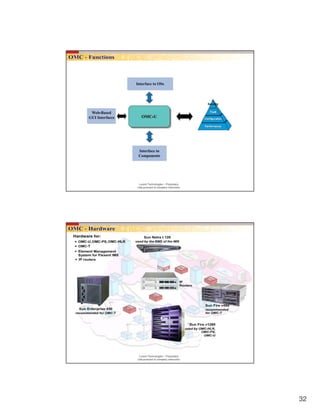
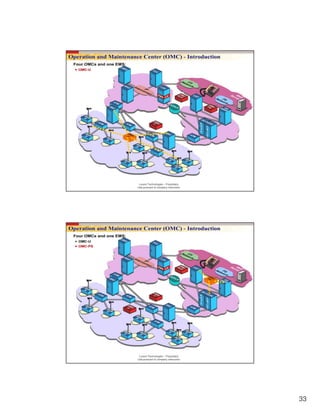
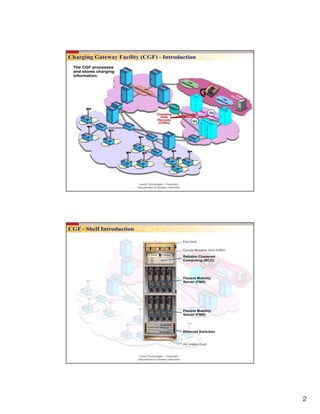
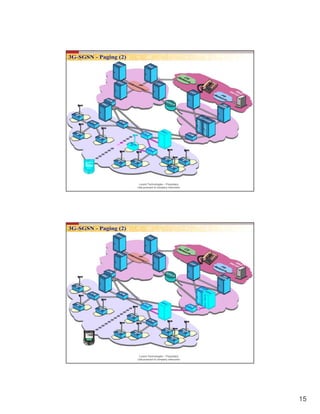
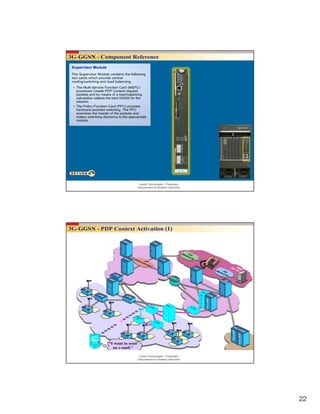
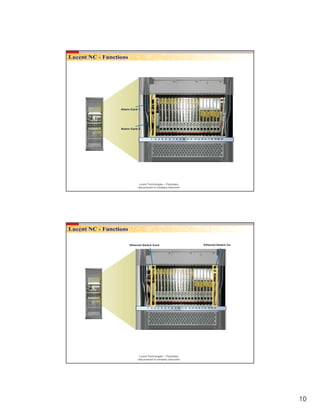
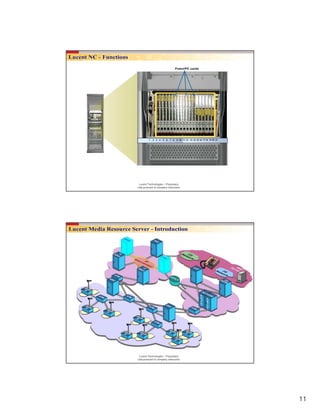
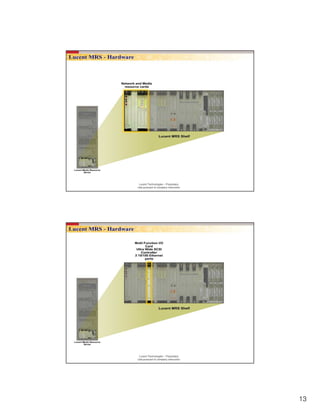
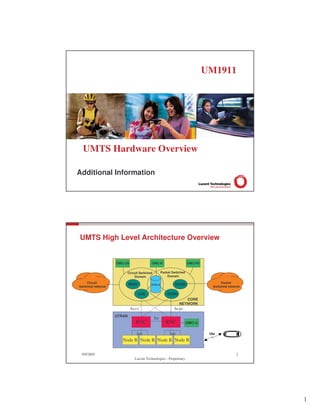
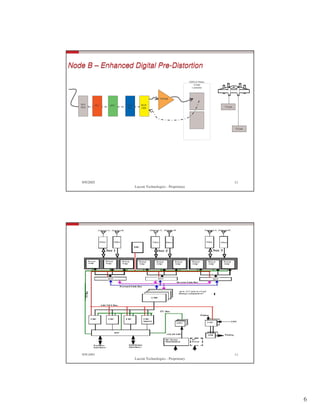
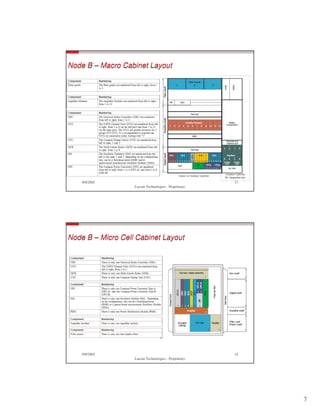
The document is a lesson on UMTS network introduction from Lucent Technologies. It is proprietary and intended for use pursuant to company instruction. The document contains diagrams and descriptions of UMTS network components such as Node B, RNC, MSC and core network elements. It also includes questions related to the UMTS network topics discussed.