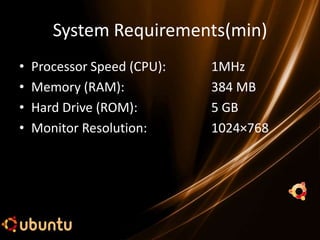
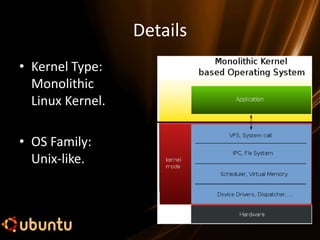
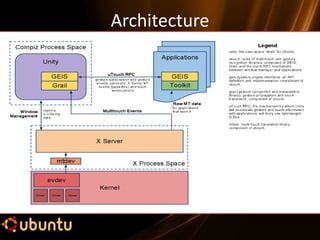
Ubuntu is a rapidly growing, open-source Linux-based operating system focused on usability and ease of installation, named after the African concept of humanity. It has minimum system requirements, various versions, and offers features like web browsing, office applications, and security. While it is free and regularly updated, it has some limitations, such as lack of offline support and compatibility issues with certain programs.

















![How to get Ubuntu???
Four ways to acquire Ubuntu 11.04:
1.) Download from its official website:
www.ubuntu.com
2.) Download using torrents.
[Warning: About 750 MB to download.]
3.) Send application request for a free CD on its
website.
4.) Ask us. (We will make you a copy.)](https://image.slidesharecdn.com/mainubuntu-120831000331-phpapp02/85/Ubuntu-11-04-Natty-Narwhal-30-320.jpg)