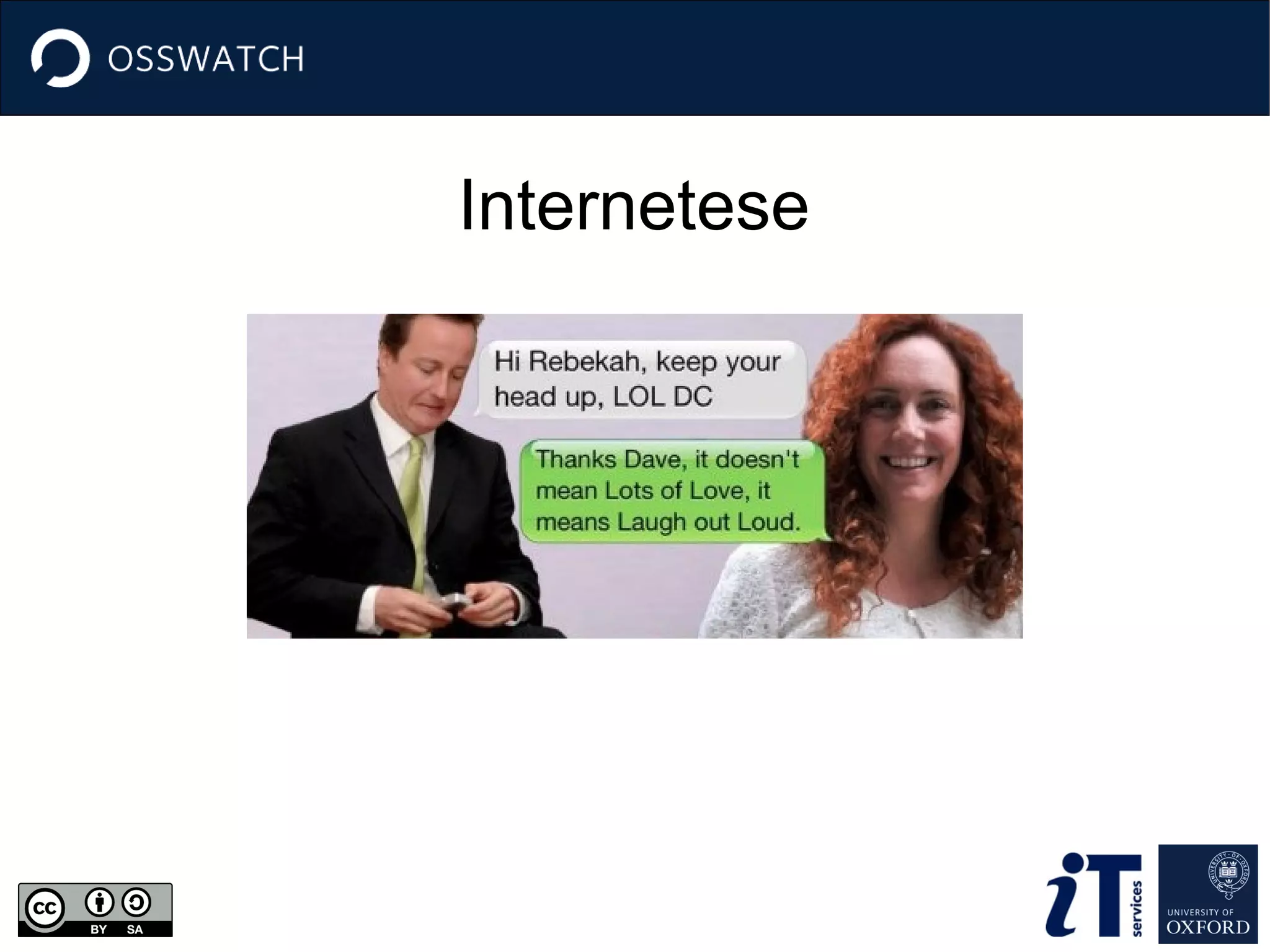
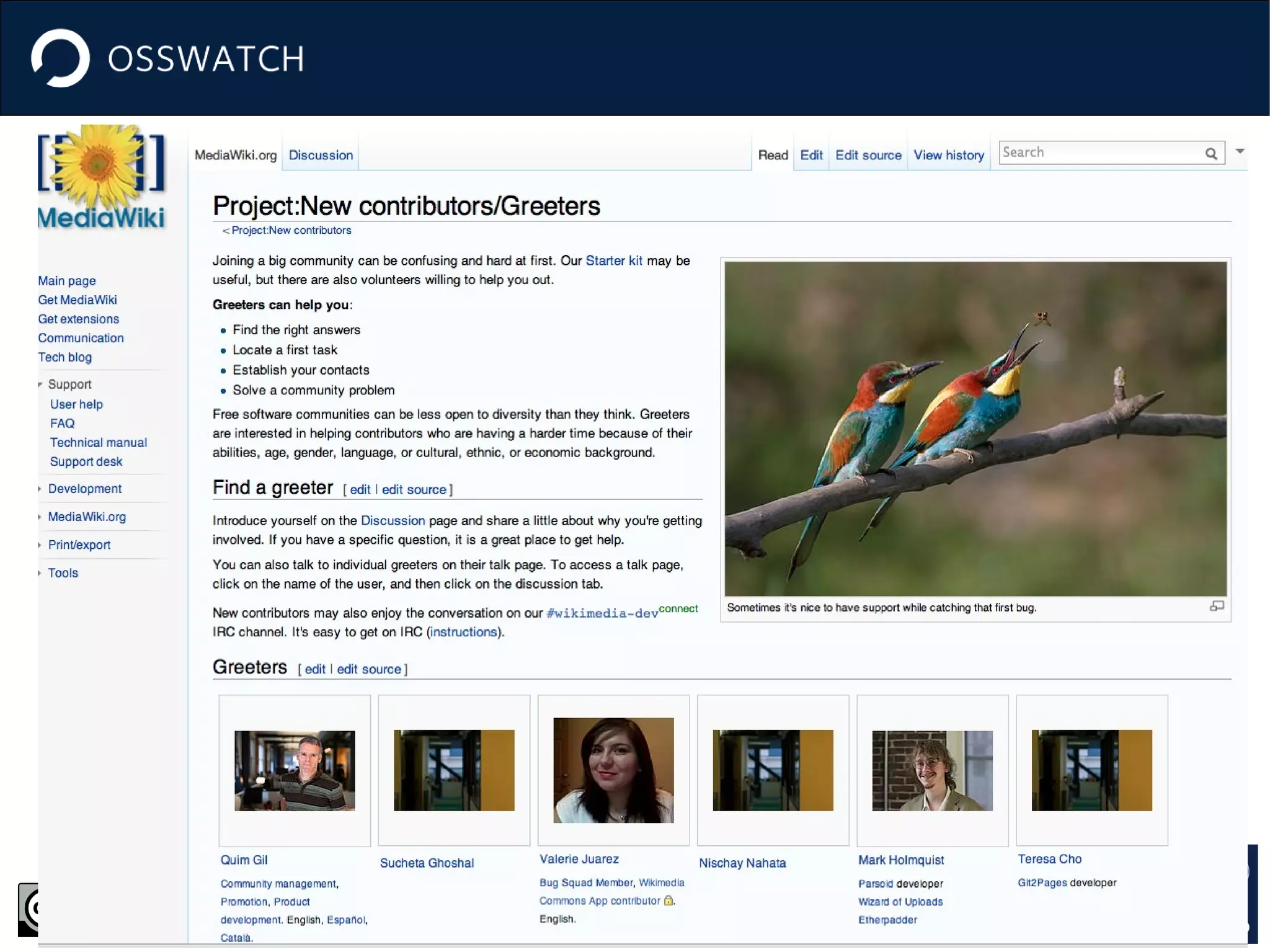
Communication is critical in open source projects as most interactions occur through written communication channels. It is important to understand the various communication channels, their purposes and norms. When communicating, one must consider tone, being appropriate and sensitive to different groups. Common communication acts in open source include inquiring, paraphrasing and acknowledging. Establishing communication policies helps set ground rules and guidelines for welcoming newcomers and handling issues.