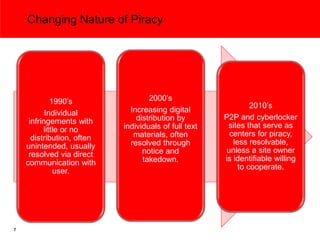
The document discusses the importance of copyright in the knowledge economy and its role in fostering economic growth, innovation, and transparency. It highlights the challenges posed by digital piracy and the need for international norms to protect copyright and encourage investment. The relationship between copyright, freedom of expression, and privacy rights is explored, emphasizing that copyright serves as both a limit and a facilitator of expression.






![Copyright and Freedom of Expression
“Concerning the First Amendment, we recognized that some
restriction on expression is the inherent and intended effect
of every grant of copyright.”
“[W]e observed that the Framers [of the Constitution]
regarded copyright protection not simply as a limit on the
manner in which expressive works may be used. They also
saw copyright as an ‘engine of free expression[:] By
establishing a marketable right to the use of one’s
expression, copyright supplies the economic incentive to
create and disseminate ideas.’”
U.S. Supreme Court, Golan v. Holder, 565 U. S. ____ (2012)
(emphasis added; citations omitted)
9](https://image.slidesharecdn.com/tpppresentation9912-120911121945-phpapp01/85/Copyright-and-Knowledge-Expansion-Dan-Duncan-of-The-McGraw-Hill-Companies-10-320.jpg)
![Internet Piracy and Privacy Rights
“….[T]here is no legitimate reposing of trust
pursuant to contract or reasonable
expectation…[of anonymity] when a person goes
on the internet with a view to uploading or
downloading what does not belong to them. That
circumstance does not give rise to any
constitutional entitlement or human right to
remain immune from a…[content owner] also
participating in that open forum to discover the
economic damage being done to it….”
EMI & Others v. Eircomm, The High Court of Ireland, Commercial Judicial Review,
2012/167 JR (emphasis added)
11](https://image.slidesharecdn.com/tpppresentation9912-120911121945-phpapp01/85/Copyright-and-Knowledge-Expansion-Dan-Duncan-of-The-McGraw-Hill-Companies-12-320.jpg)