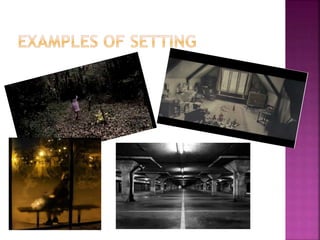
Thrillers use techniques like suspense, tension, and excitement to stimulate the viewer's emotions. Elements of mise-en-scene, sound, editing, narrative structure, setting, characters, iconography, and cinematography help films stick to the thriller genre. For example, dark lighting, ominous music, abrupt cuts, isolated settings, and characters in danger are common codes and conventions used to create anxiety and fear in viewers. Camera shots like close-ups are also important to clearly show emotions and increase tension.