The securitization of online activism
- 1. The Securitization of Online Activism
- 2. Outline Introduction Background Anonymous Speech Act The Audience Emergency Measures Conclusion
- 3. Key Question How are government actors in the United States taking action to securitize hacktivism? Hacktivism: the act of hacking, or breaking into a computer system, for a politically or socially motivated purpose. The individual who performs an act of hacktivism is said to be a hacktivist (TechTarget, 2001).
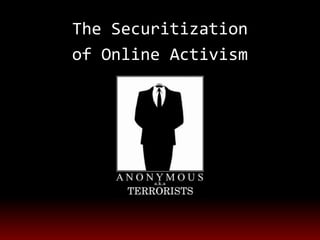
- 4. Hypothesis Hacktivism, and particularly the online activism group Anonymous, is being securitized by government actors in the United States through dialogue and legal mechanisms that frame hacktivists as terrorists.
- 5. Background How has hacktivism evolved, and in which ways do hacktivists interact with government actors? Method: a literature review of academic, government and news documents on the subject of online activism, with a focus on the United States.
- 6. Anonymous a loosely-affiliated group of computer programmers organizes itself to coordinate online protests methods include DDOS attacking websites, hacking into organizations' servers and leaking documents. Anonymous hasn't once used its capabilities to physically harm another human being or the general public.
- 7. Civil Disobedience Electronic civil disobedience is borrowing the non-violent direct action tactics from earlier social movements (Wray, 1998). Diverting traffic away from a website is akin to setting up a roadblock of picking a building Organizing a denial of service attack is akin to a sit-in (Auty, 2004) Acts of cyber disobedience are de facto illegal, but hacktivist acts are only those that serve as social or political forms of protest (Huschle, 2002).
- 8. Speech Act What language have government actors in the United States used to frame hacktivism as a threat to national security? Method: Document analysis of government documents, academic and news articles Theory: Framing theory
- 9. Speech Act Terrorism remains the FBI’s top priority. But in the not too distant future, we anticipate that the cyber threat will pose the number one threat to our country. We need to take lessons learned from fighting terrorism and apply them to cyber crime. We must continue to push forward, because our adversaries are relentless. They want our money, our property, and our secrets, and some seek to harm us well beyond that. Together, we can turn the tide against them and bolster the security of our nation’s information, networks, and infrastructure.
- 10. Speech Act Today, our adversaries sit on fiber optic cables and wi-fi networks, unknown and undetected…They seek our technology, our intelligence and our intellectual property, even our military weapons and strategies. In short, they have everything to gain, and we have a great deal to lose. The end result will be the same: we will lose our data. We may lose access to our own information. And we may well lose our security.
- 11. The Audience How are citizens and the private sector responding to the message that hacktivists pose an imminent threat? Method: Document analysis News articles, public sector reports and online blogs Theory: Constructivist theory
- 12. Emergency Measures What emergency measures are government actors promoting in order to strengthen their nation’s security against hacktivism? Method: Document analysis of government, academic, and news documents and blogs. Theory: Constructivist theory
- 13. Conclusion Government actors in the United States are in the process of securitizing hacktivism, and in particular the online activism group Anonymous. They are already framing hacktivism as a form of terrorism, and highlighting the future potential threats to national security.
Editor's Notes
- What documents?What will I be looking for?What words or phrases?Who are the key players?
- For example, diverting trafficaway from a Web site is akin to setting up aroadblock or picketing a building, and organising adenial of service attack is equivalent to a sit-in.Huschle believes that all acts of cyber disobedienceare de facto illegal, but that hacktivist acts are onlythose that serve as social or political forms ofprotest – discounting malicious acts.
- What documents?What will I be looking for?What words or phrases?Who are the key players?This will be explored through document analysis of FBI speeches, Department of Homeland Security briefings, legal mechanisms and relevant academic and news documents. These sources will allow for analysis, through a framing theory lens, of the words and phrases used by government actors, and the interpretations of their choice of language by academics and journalists.
- Terrorism remains the FBI’s top priority. But in the not too distant future, we anticipate that the cyber threat will pose the number one threat to our country. We need to take lessons learned from fighting terrorism and apply them to cyber crime.We must continue to push forward, because our adversaries are relentless. They want our money, our property, and our secrets, and some seek to harm us well beyond that. Together, we can turn the tide against them and bolster the security of our nation’s information, networks, and infrastructure. Amongst all of the crimes our country faces, the FBI considers high-tech crimes to be the most significant. As a result, the FBI’s top three priorities are the previously mentioned counterterrorism and counterintelligence, followed immediately by cyber. Espionage once pitted spy versus spy, country against country. Today, our adversaries sit on fiber optic cables and wi-fi networks, unknown and undetected. They may be nation-state actors or mercenaries for hire, rogue hackers or transnational criminal syndicates. These hackers actively target our government networks. They seek our technology, our intelligence and our intellectual property, even our military weapons and strategies. In short, they have everything to gain, and we have a great deal to lose.The end result will be the same: we will lose our data. We may lose access to our own information. And we may well lose our security.
- Terrorism remains the FBI’s top priority. But in the not too distant future, we anticipate that the cyber threat will pose the number one threat to our country. We need to take lessons learned from fighting terrorism and apply them to cyber crime.We must continue to push forward, because our adversaries are relentless. They want our money, our property, and our secrets, and some seek to harm us well beyond that. Together, we can turn the tide against them and bolster the security of our nation’s information, networks, and infrastructure. Amongst all of the crimes our country faces, the FBI considers high-tech crimes to be the most significant. As a result, the FBI’s top three priorities are the previously mentioned counterterrorism and counterintelligence, followed immediately by cyber. Espionage once pitted spy versus spy, country against country. Today, our adversaries sit on fiber optic cables and wi-fi networks, unknown and undetected. They may be nation-state actors or mercenaries for hire, rogue hackers or transnational criminal syndicates. These hackers actively target our government networks. They seek our technology, our intelligence and our intellectual property, even our military weapons and strategies. In short, they have everything to gain, and we have a great deal to lose.The end result will be the same: we will lose our data. We may lose access to our own information. And we may well lose our security.
- This will be explored, through a constructivist lends, by document analysis of the previously listed sources, as well as reports issued by private sector players and opinions of citizens published on blogs. These sources will allow for analysis of the messages being directed at private sector players and citizens, and the reaction of the audience to the concept of hacktivists posing an imminent threat.
- This will be explored through document analysis of all previously listed sources. There sources will allow for analysis of the actions government actors have already taken, and are promoting should be taken, in order to diminish the threat of hacktivism to national security.
- While there are certainly voices of opposition to the comparison of hacktivists to terrorists, the discourse is dominated by those who perceive a security threat. The successful securitization of hacktivism is likely to lead to stricter penalties for hacktivists, increased government security online, and an increase in the level of monitoring and censorship of online communications and activities by the United States government