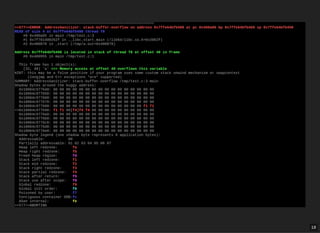
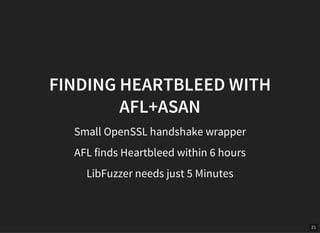
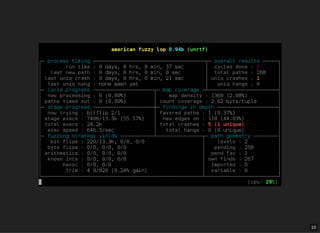
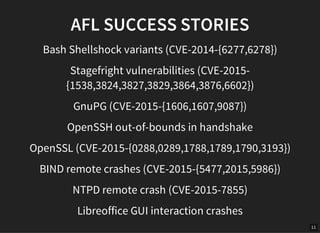
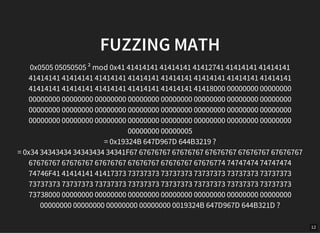
The document discusses the fuzzing project initiated by Hanno Böck to improve the reliability of C/C++ programming by identifying and mitigating common bugs through techniques like smart fuzzing and AddressSanitizer (ASan). It highlights the challenges and successes of fuzzing, including specific vulnerabilities found in notable software, and emphasizes the importance of using ASan for detecting memory access bugs. The presentation calls for increased usage of fuzzing tools and ASan in software development to enhance security.



![17
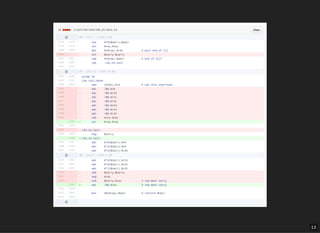
SPOT THE BUG!
int main() {
int a[2] = {1, 0};
printf("%i", a[2]);
}](https://image.slidesharecdn.com/32c3-fuzzing-160101201802/85/The-Fuzzing-Project-32C3-17-320.jpg)