Embed presentation
Download as PDF, PPTX

















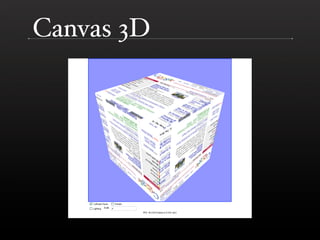
The document discusses the future of Firefox and JavaScript, highlighting advancements in web applications, including offline capabilities, improved graphics with Canvas 3D, and new media support. It also covers upcoming versions of JavaScript, including features like optional type annotations and block-scoped variables. The presentation outlines the integration of Tamarin, Adobe's new virtual machine, into Firefox's JavaScript engine and the potential for server-side JavaScript growth.