Technology Terms & Requirements
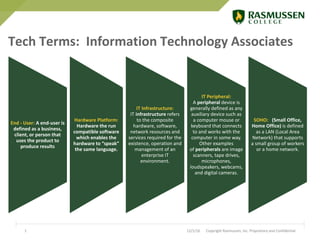
- 1. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential1 Hardware Platform: Hardware the run compatible software which enables the hardware to “speak” the same language. End - User: A end-user is defined as a business, client, or person that uses the product to produce results IT Infrastructure: IT infrastructure refers to the composite hardware, software, network resources and services required for the existence, operation and management of an enterprise IT environment. IT Peripheral: A peripheral device is generally defined as any auxiliary device such as a computer mouse or keyboard that connects to and works with the computer in some way. Other examples of peripherals are image scanners, tape drives, microphones, loudspeakers, webcams, and digital cameras. SOHO: (Small Office, Home Office) is defined as a LAN (Local Area Network) that supports a small group of workers or a home network. Tech Terms: Information Technology Associates
- 2. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential2 Client PC: A client computer is an individual computer that accesses the information and programs stored on a server as part of a network environment. Server: A server is a computer designed to process requests and deliver data to other (client) computers over a local network or the internet. IT Infrastructure: IT infrastructure refers to the composite hardware, software, network resources and services required for the existence, operation and management of an enterprise IT environment. IT Peripheral: A peripheral device is generally defined as any auxiliary device such as a computer mouse or keyboard that connects to and works with the computer in some way. Other examples of peripherals are image scanners, tape drives, microphones, loudspeakers, webcams, and digital cameras. IT Network: A network is defined as a group of two or more computer systems linked together. There are many types of computer networks, including the following: local- area networks(LANs) and Wide Area Networks (WAN) and Cloud networks. Tech Terms: Network Systems Administration Associates
- 3. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential3 Systems Analysis: The process of studying a procedure or business in order to identify its goals and purposes and create systems and procedures that will achieve them in an efficient way Merriam-Webster Project Management: The discipline of initiating, planning, executing, controlling, and closing the work of a team to achieve specific goals and meet specific success criteria. Wikipedia IT Infrastructure: IT infrastructure refers to the composite hardware, software, network resources and services required for the existence, operation and management of an enterprise IT environment. Techopedia Organizational Policies: Policies and procedures are designed to influence and determine all major decisions and actions, and all activities take place within the boundaries set by them. BusinessDictionary Risk Mitigation: A systematic reduction in the extent of exposure to a risk and/or the likelihood of its occurrence. Also called risk reduction. BusinessDictionary Tech Terms: Information Technology Management Bachelors
- 4. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential4 R: is an open source programming language and software environment for statistical computing widely used for data analysis. Python: is a programming language common in Data Analytics that allows programmers to express concepts in fewer lines of code. Tableau: is software that produces interactive data visualization products focused on business intelligence. SAS: is a software suite developed by SAS Institute for analytics, business intelligence, and more. SQL: (Structured Query Language) communicates with databases and extracts content for web use, reports, etc. “Sequel” or “S Q L” Tech Terms: Data Analytics Bachelors
- 5. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential5 SDN: Software defined networking (SDN) is an approach to using open protocols, to apply globally aware software control at the edges of the network to access network switches and routers that typically would use closed and proprietary firmware. Cloud Computing: Cloud computing means storing and accessing data and programs over the Internet instead of your computer's hard drive. SOT Sandbox: Customized Could Lab Environment managed by Rasmussen SOT. Penetration Testing: Penetration testing (also called pen testing) is the practice of testing a computer system, network or Web application to find vulnerabilities that an attacker could exploit. Risk Management: Security risk management. Risk management is the identification, assessment and prioritization of risks followed by coordinated and economical application of resources to minimize, monitor, and control the probability and/or impact of unforeseen events. Tech Terms: Cyber Security Bachelors
- 6. 12/1/16 Copyright Rasmussen, Inc. Proprietary and Confidential6 Computer Science Bachelors: Technical Requirements September 6, 2017 Copyright Rasmussen, Inc. 2011. Proprietary and Confidential. Universal Windows Computer Windows 8 Access to Dream Spark Apple (IOS) Application Development MAC Computer (iPad/iPhone is not enough) Apple IOS 10 Access to Apple Vendor (iTunes and Cloud Space)