This document provides an overview and instructions for using an Access database to track insurance certificates. It describes:
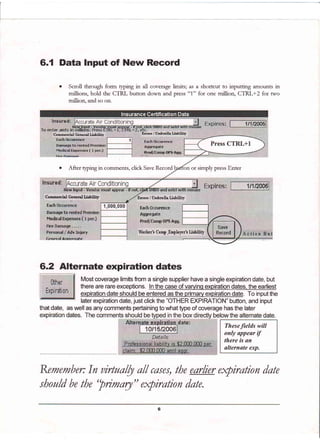
1) The database was created to replace an Excel workbook for tracking supplier insurance coverage amounts and expiration dates. It allows inputting a single or alternate expiration date per supplier.
2) Users with the run-time version can only view existing records while full Access users can edit the database design.
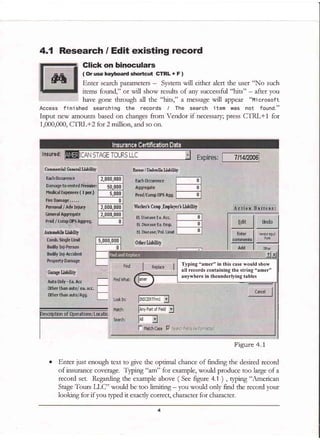
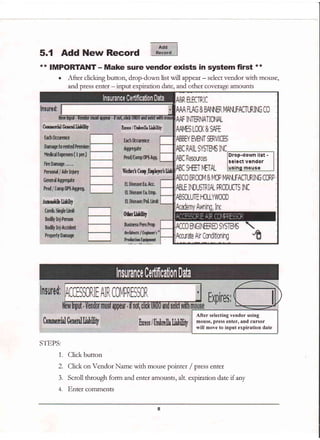
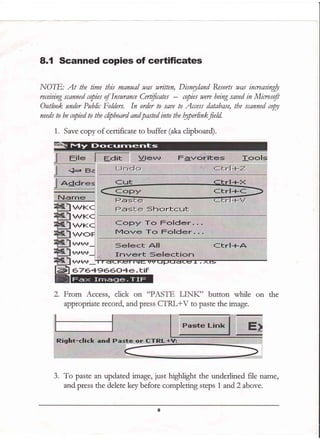
3) Records can be searched, added, and edited. Shortcuts allow quickly entering coverage amounts in millions. Scanned certificates can be attached by copying to the clipboard.
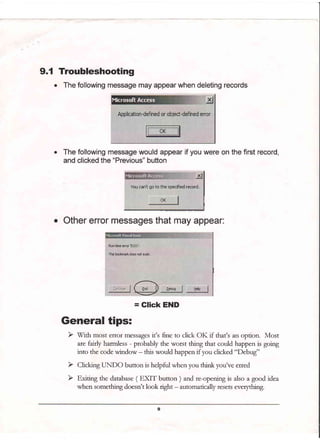
4) Navigation buttons and the last input by field help manage the records. Troubleshooting tips address potential error messages.

![Overview
Background:
Ttacking of Insurance Certificates was transidoned ftom an Excel Wotkbook ( See Figute 1.1) to an
Access database in November,2005. The Excel document was a listing of Supplien, with coverage
limits segtegated by type of covetage; Commercial Geneml, Auto, Worker's Comp, and so on.
The same layout was implemented in an Access Database, the only excepdon being the e>gimtion
date. In Access, onllr one expiration date is capnred, and a separate field is designated for the
uncommon scenado of a Supplier having different expiration dates fot different types of coverage.
Editing and new Certificate input will be take place primadly via the input sceen (F19.1.2 below )
* 3 a s s t 6 H I x rlw
ru|ttHr
Gdrtrt**H. etrffa*. t u3t[El *ut{t{f*l1t ur3|tilt
lttItrg Ltfil f3
hl *'rhl
?.,litr
lrr.l
llrltrl
lr.t rr,
prnrI
hrrlnl *rrrl
ft1*4!r
7*h&t,
*di7
h*
Crliej
9rlilr
.i-tfu',
a*trr.l
h*il1
qi.'1lfr
?,.y41
0lr9
bo
rnilrrfl
5ir1b tiril
F-l
*rilm$
...;&rll
AsCB{trstsrlMS tt{C tot?/2*0! aoq,wl 30{,0r 10"0& t,{F0,oal :.0s.0*i a,&m.$l ts'?,:*d
f,tfi€utft*ctal 'tlil(,1r0, t,8s0,0*t !,00{,0} 10.60r 1,0r0,&i 4,00d.001 1,000,0?l il$n00, t.fr0,0q
aSsorurtltr tfqmca fil't1m#r t.000.041 t0$,00: 5.0tt 1,090.0$t a,s0f.0{r rcMrd
ACCISSORE#R ft 9'f3nl?*0! 7.gtfl.041 1.0sS.06i g|,00 a 0e0.0fl t.t0f"00! a.c(p.00i 3,]0i:t{! i@q.s
Figure 1. 1
EL Di5eaR fa, Aqr.
EL Di5easeta Fmp.
EL Diseaser?ol, Limit
& Adv Injury: Excluded: Emp Ben : ExcludedWC insurance c
Figure 1.2](https://image.slidesharecdn.com/685872b6-6a3b-4e72-a0d5-4d7d6ede8a00-150321131833-conversion-gate01/85/Technical_Writing_Example-PDF-3-320.jpg)