Embed presentation
Download as PDF, PPTX

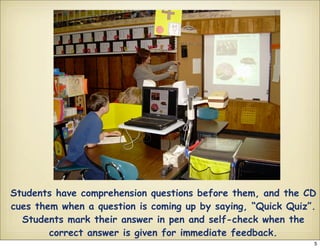
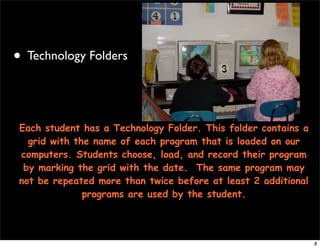
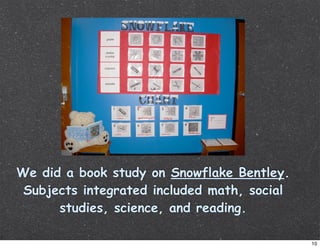










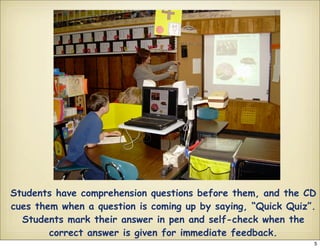
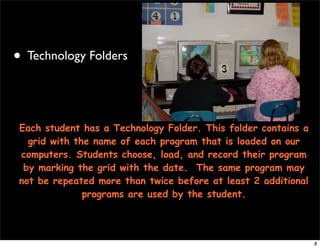
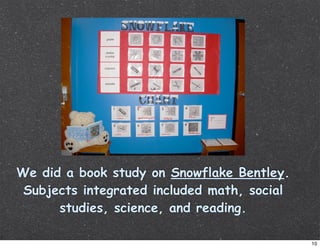
This document outlines how a special education classroom integrates various web 2.0 technologies to enhance student learning, such as using online lessons and assessments through ClassServer, having students complete research and book studies using educational websites, and creating podcasts for literacy and field trip activities. Technology is also used for behavior management, communication with parents, and future project ideas like portable science labs and audiobooks on flash drives. The document provides contact information for the special education teachers implementing these strategies.