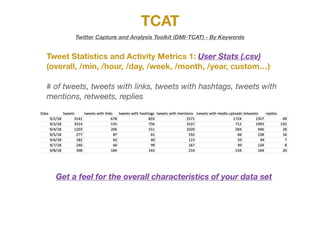
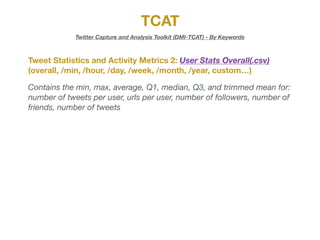
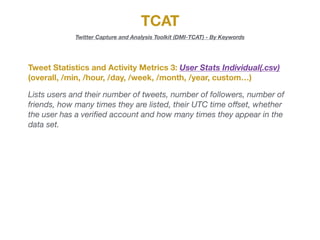
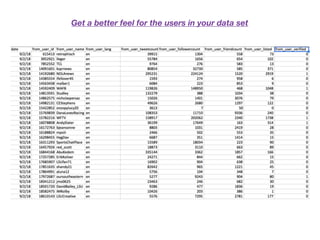
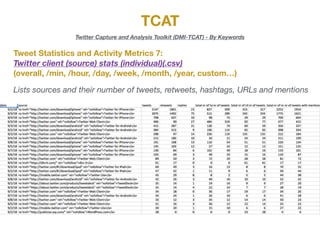
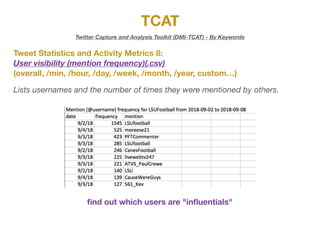
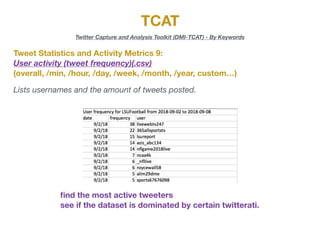
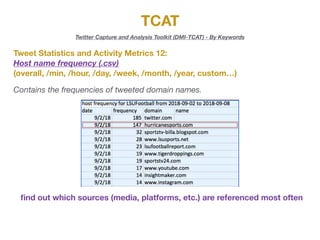
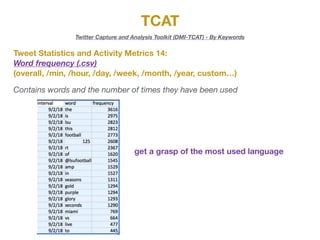
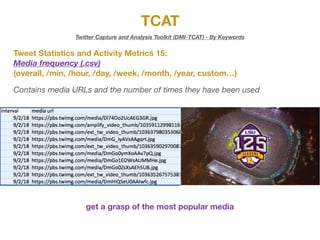
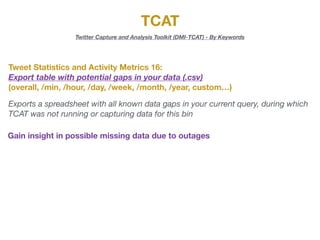
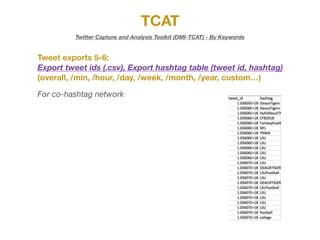
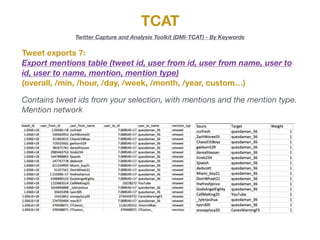
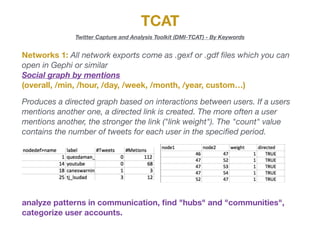
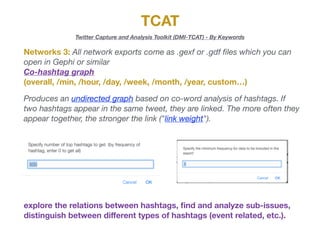
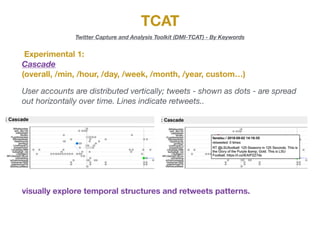
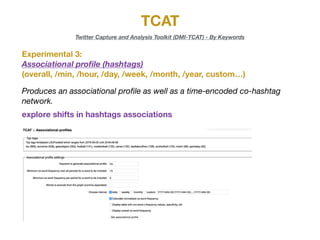
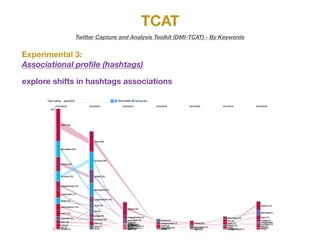
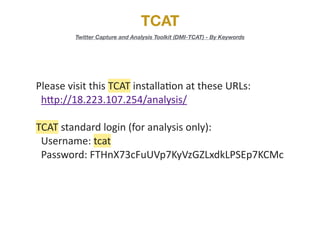
The document describes the various metrics and exports available from the Twitter Capture and Analysis Toolkit (TCAT). TCAT can generate metrics on tweet statistics, user activity, hashtag usage, mention networks, and more. It exports data in CSV and network graph formats for analyzing characteristics of Twitter data collected by keyword searches.