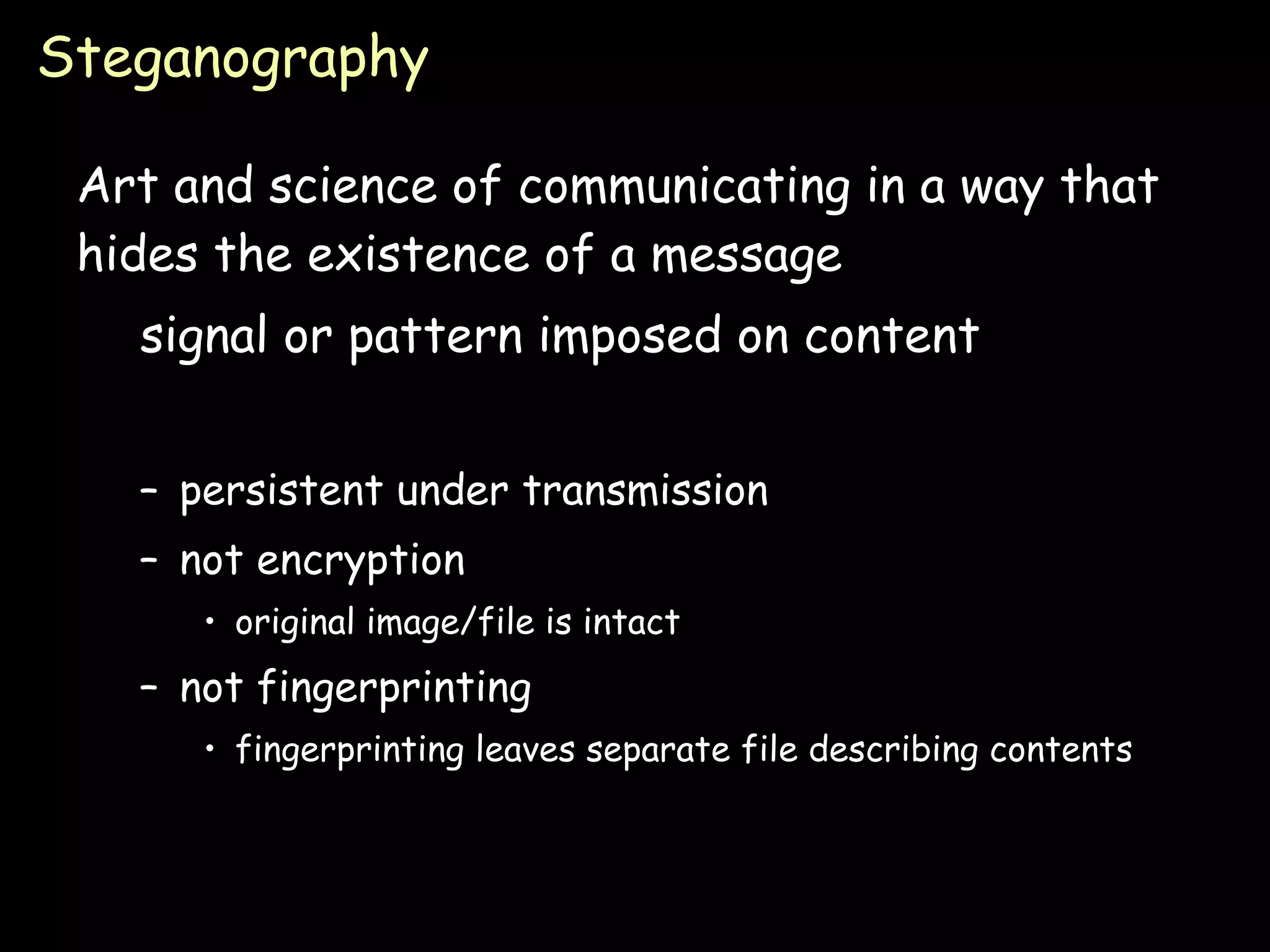
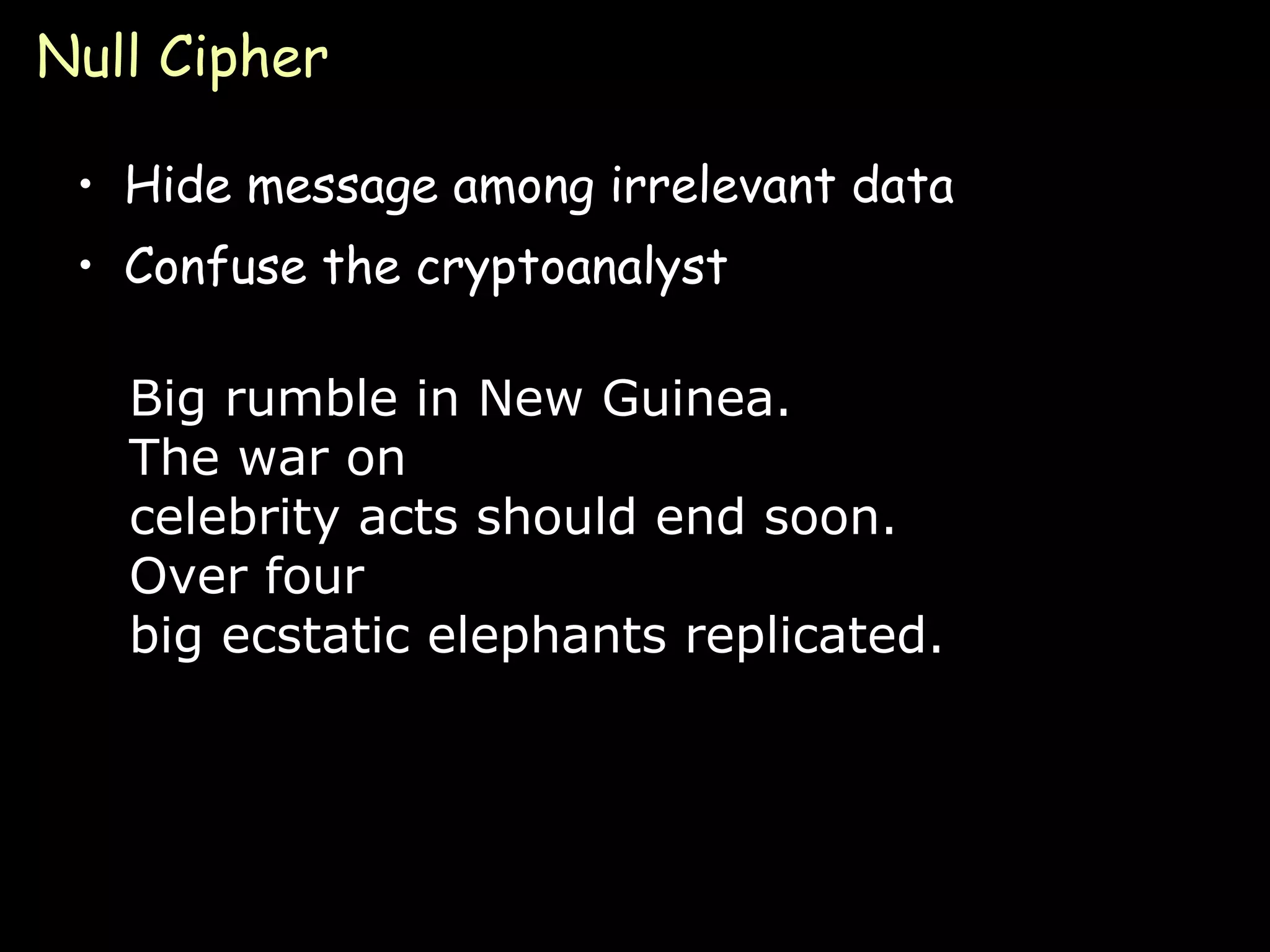
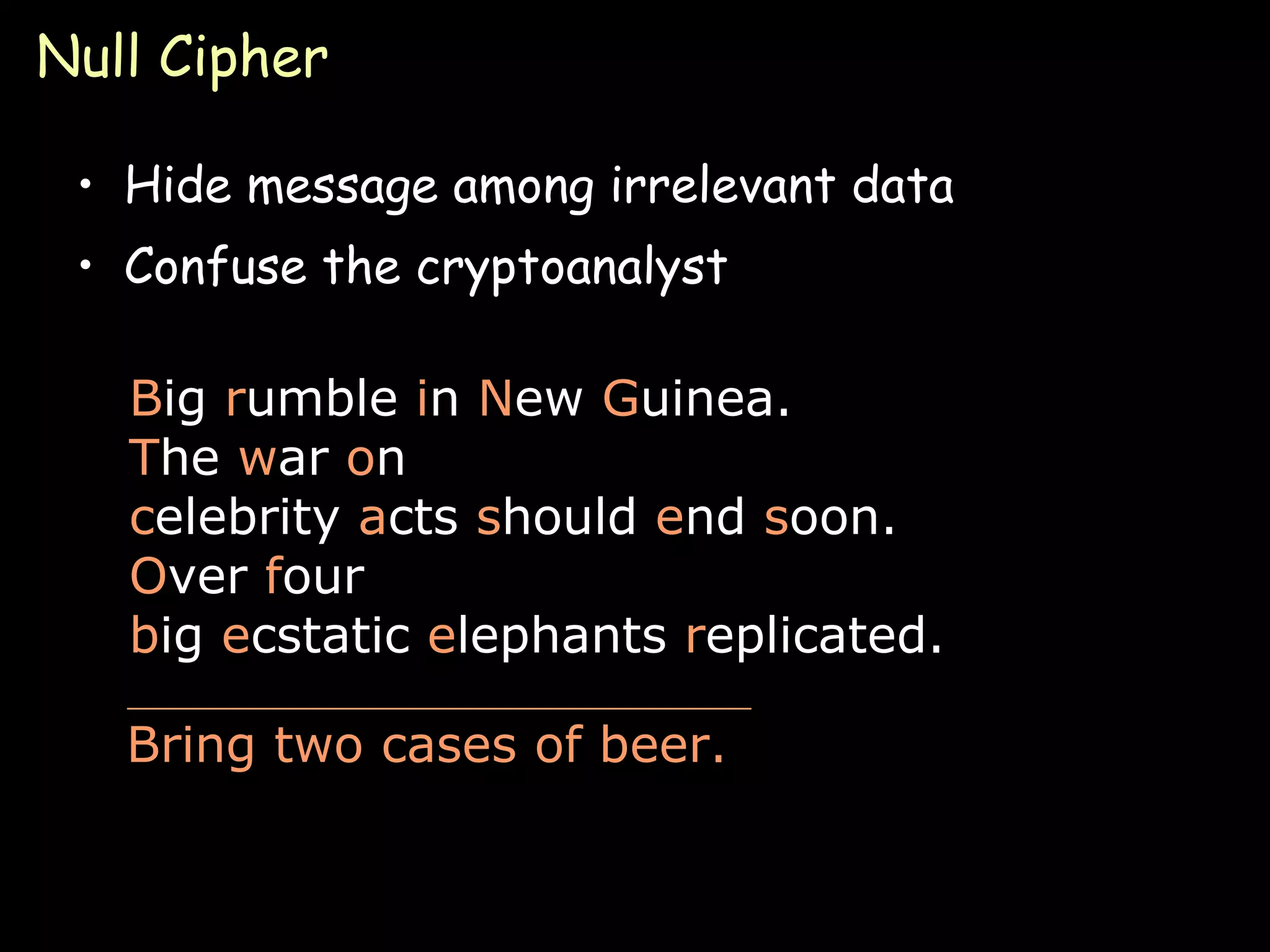
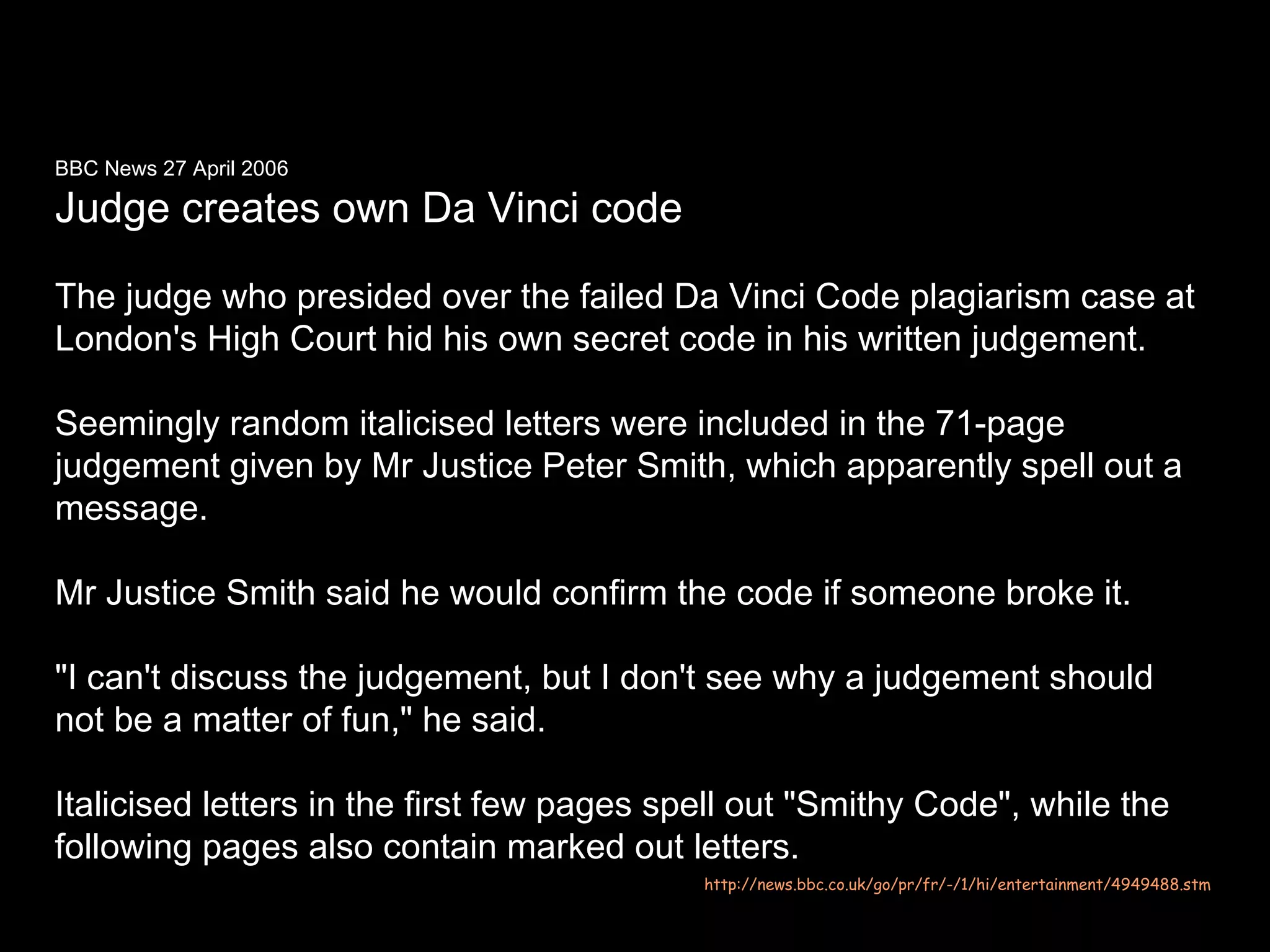
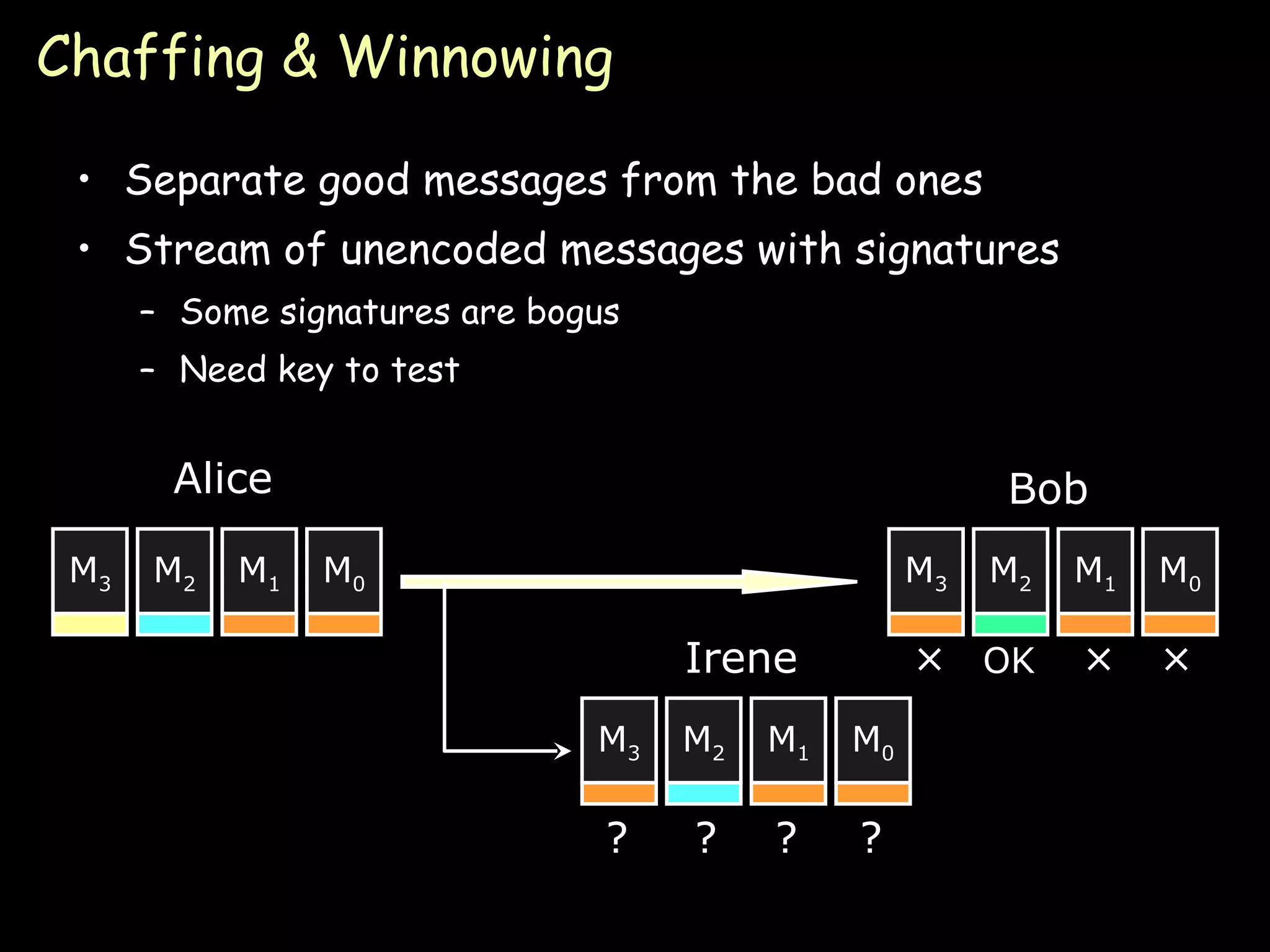
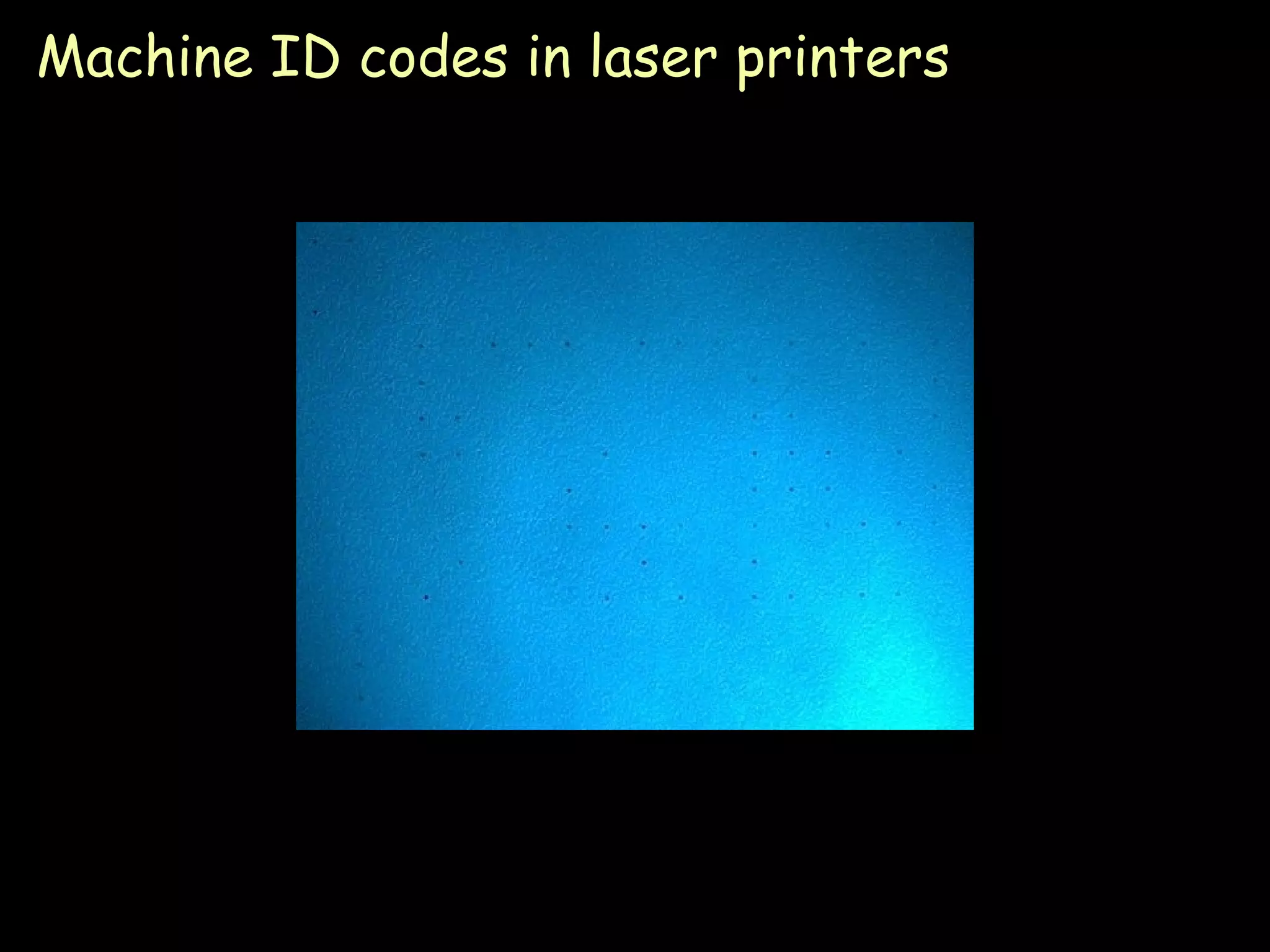
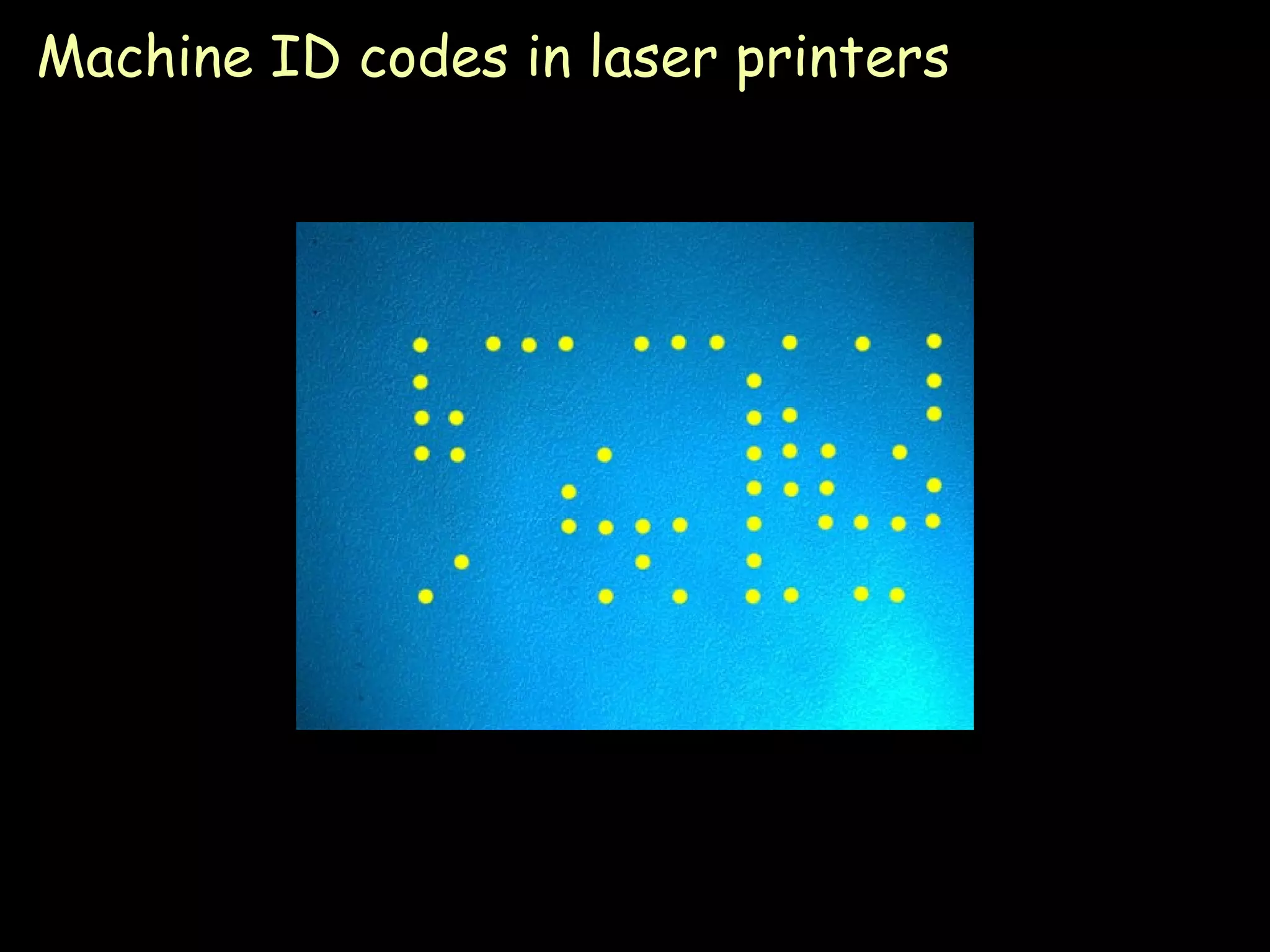
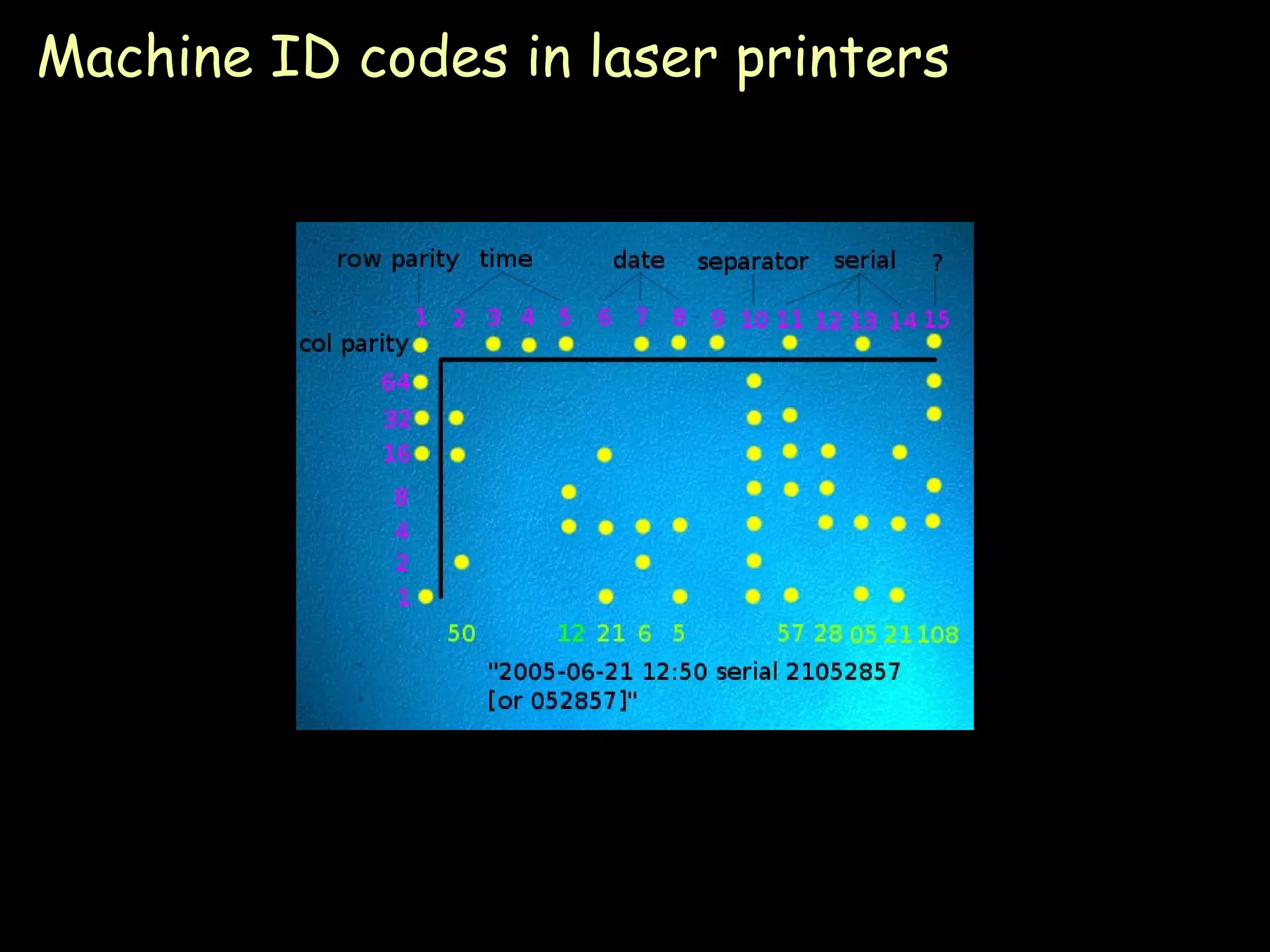
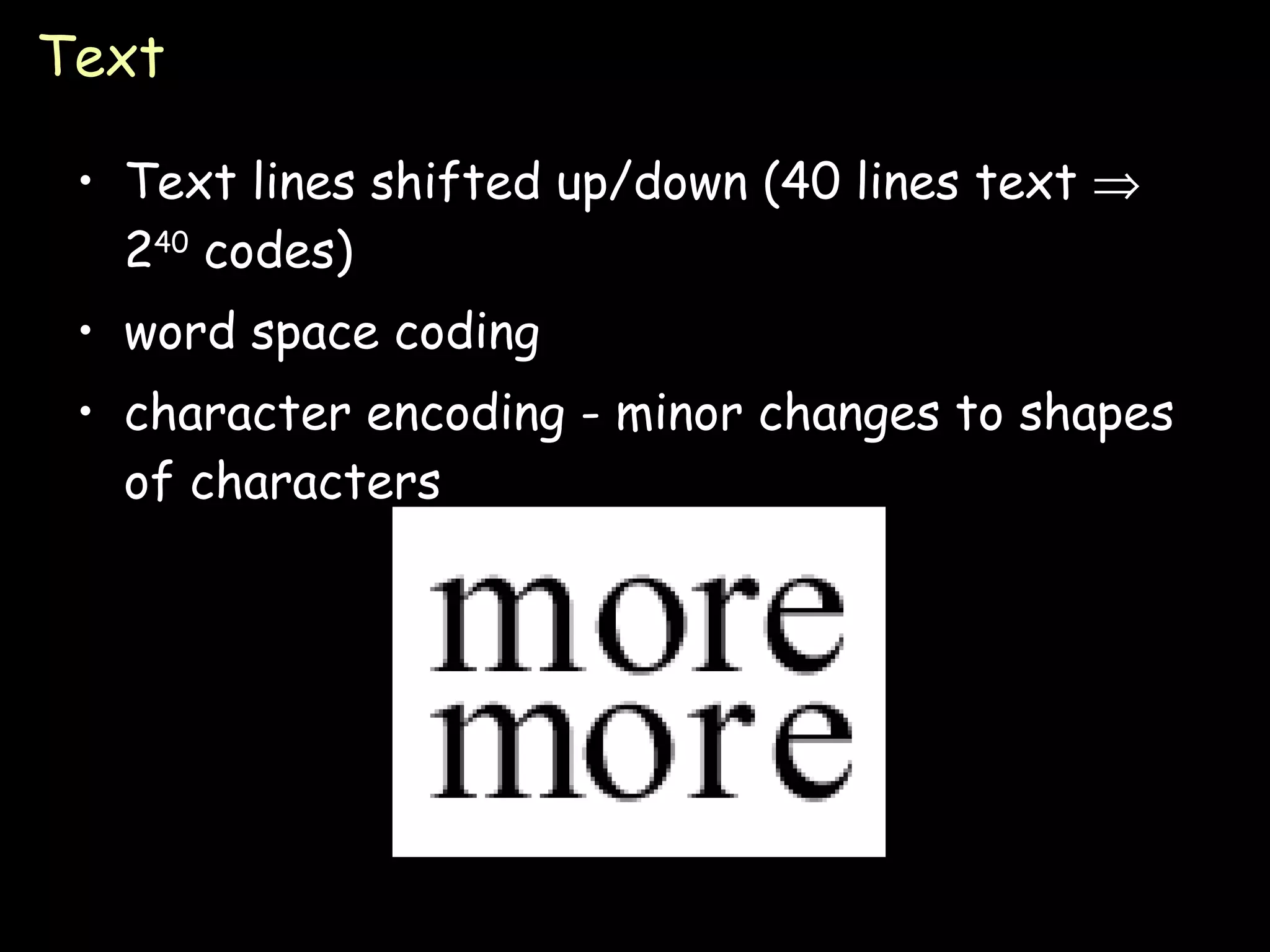
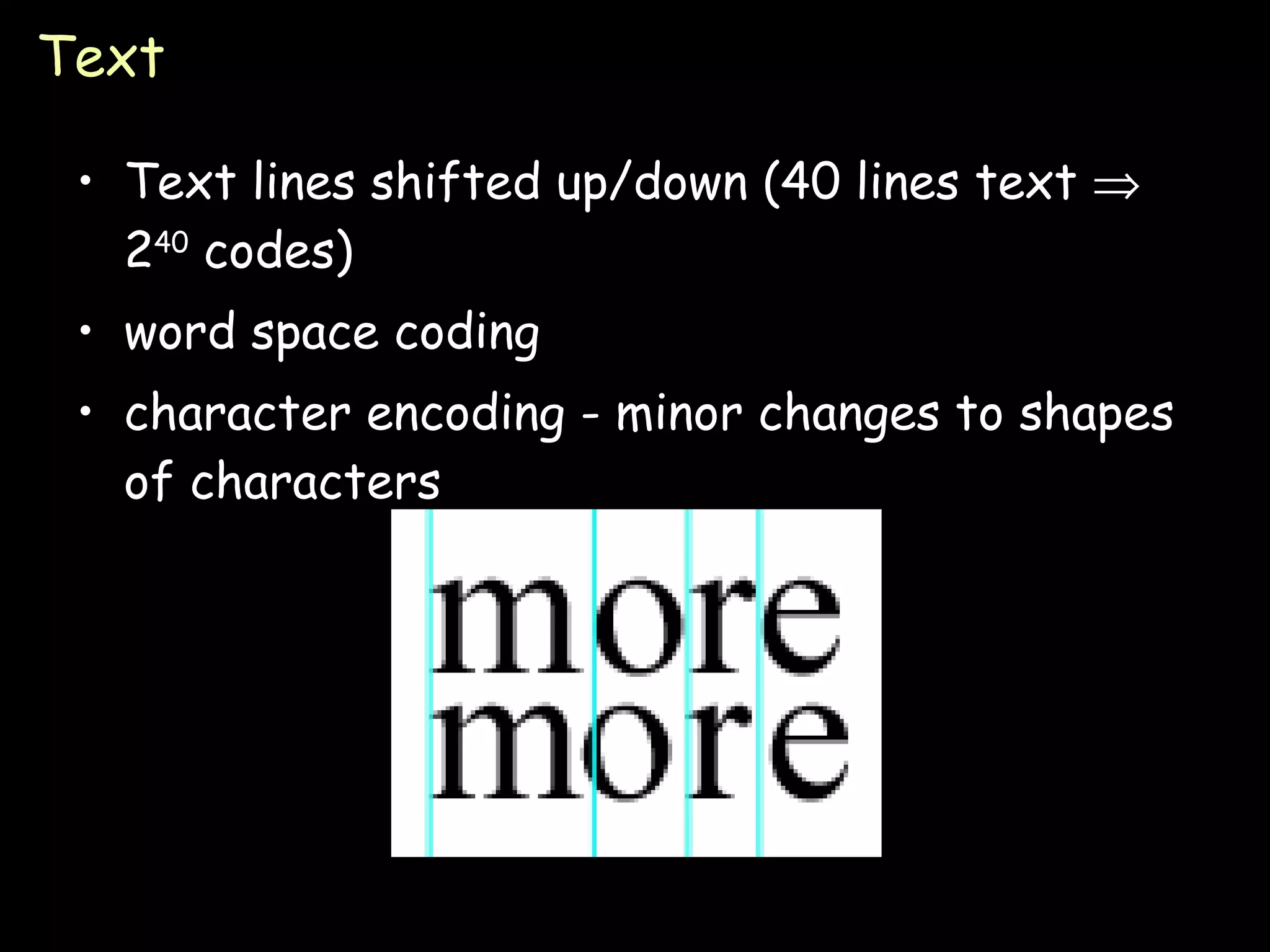
The document discusses different techniques for secret communication, including steganography, cryptography, and digital watermarking. It provides examples of classic steganography techniques like invisible ink and microdots. It also explains modern digital steganography methods like hiding messages in the least significant bits of images, altering text documents, and embedding codes in audio, video, and printer output. The key difference between steganography and watermarking is that the goal of steganography is to prevent detection of any hidden message, while watermarking aims to prevent unauthorized removal or alteration of an embedded message.
![Steganography Paul Krzyzanowski [email_address] [email_address] Distributed Systems Except as otherwise noted, the content of this presentation is licensed under the Creative Commons Attribution 2.5 License.](https://image.slidesharecdn.com/18-steganography-090902071119-phpapp01/75/Steganography-Distributed-computing-1-2048.jpg)