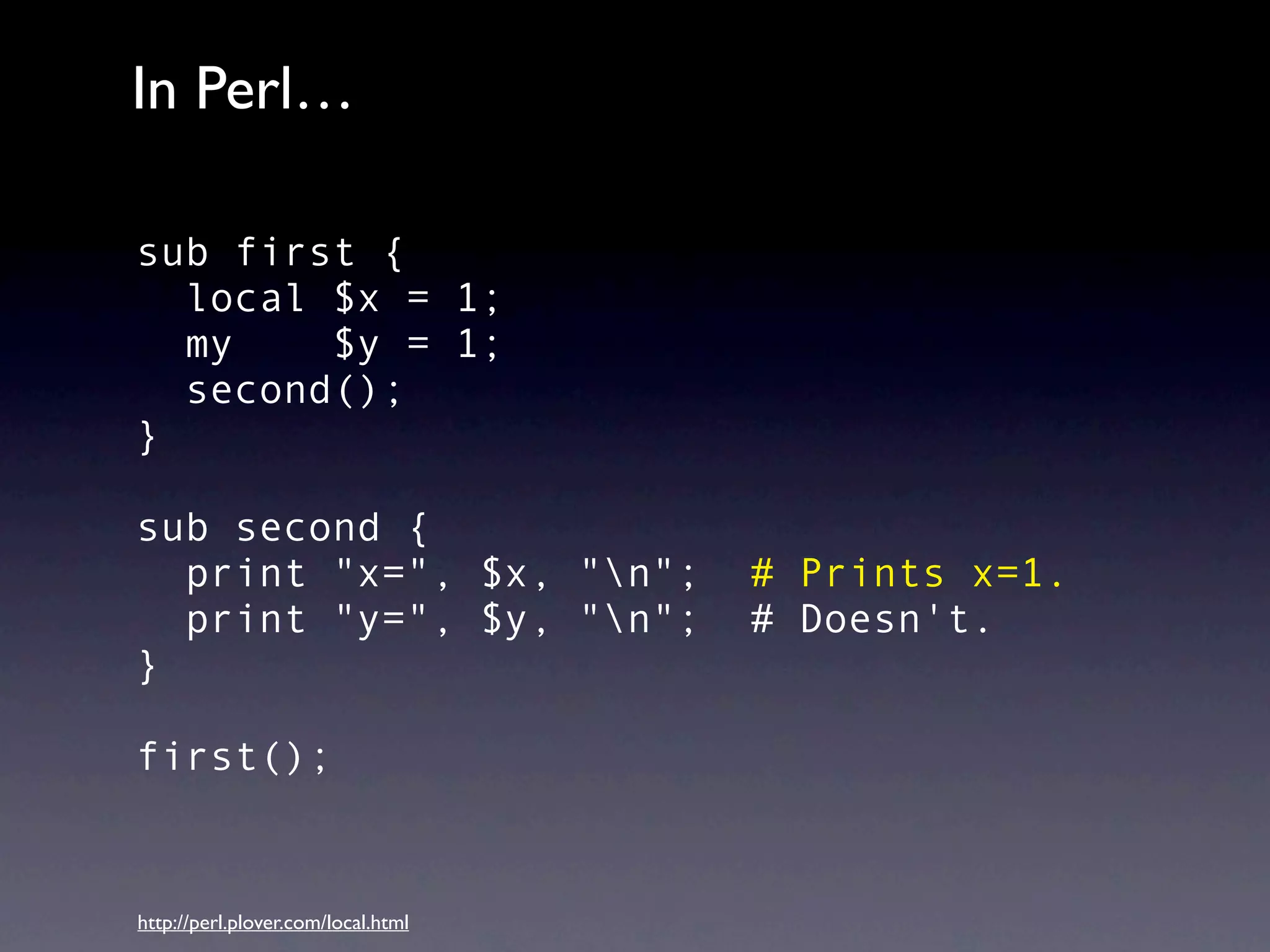
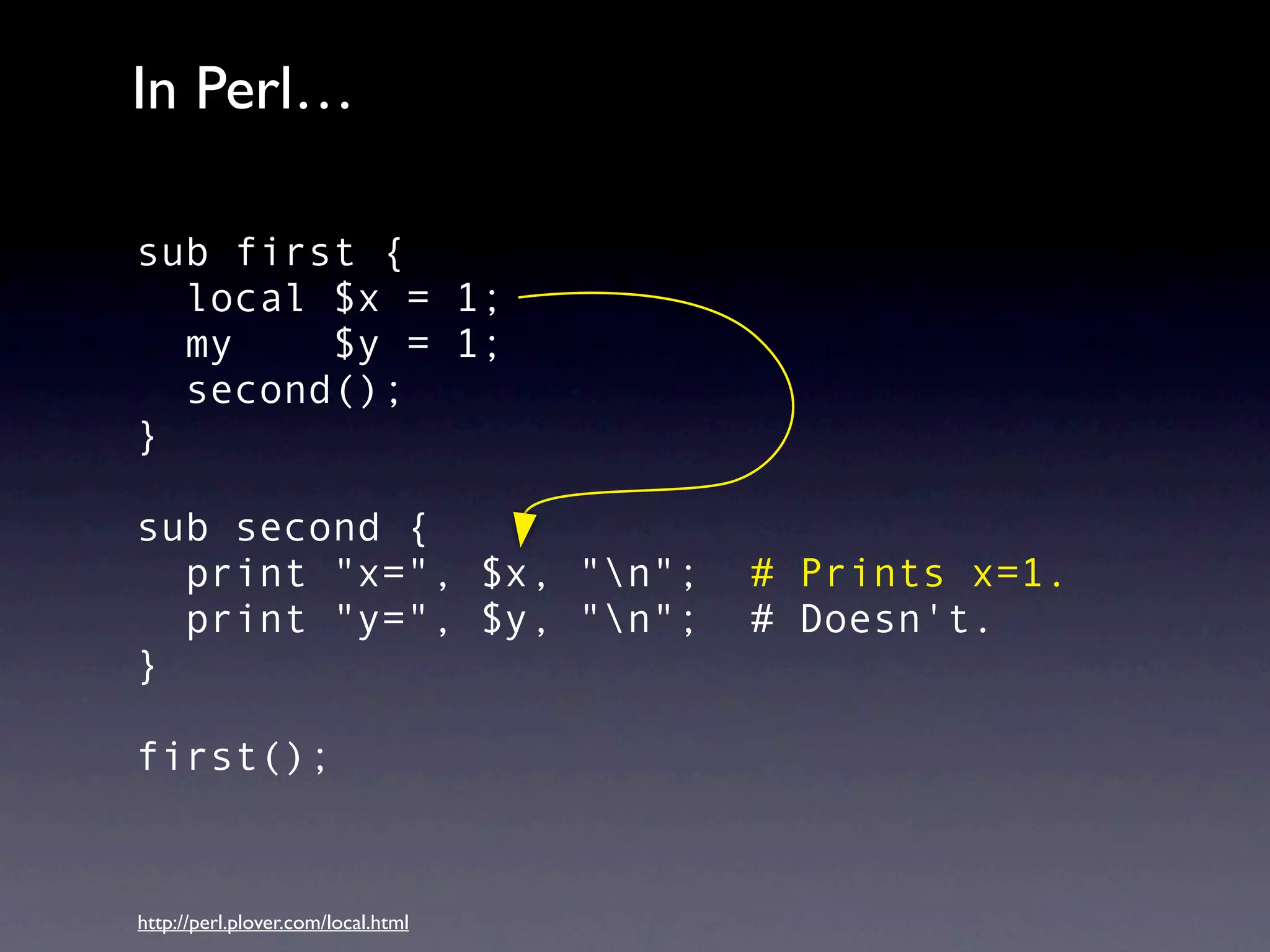
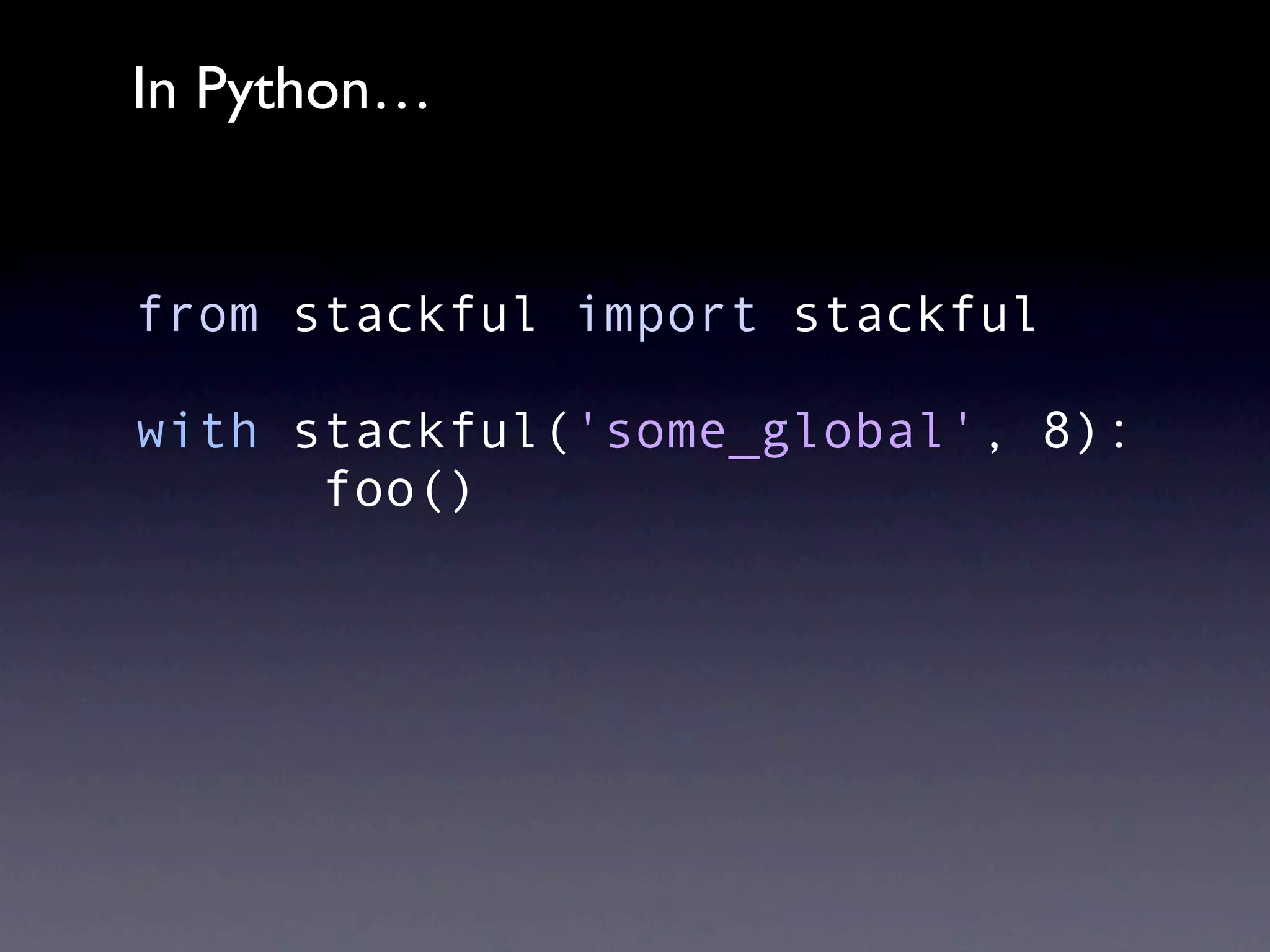
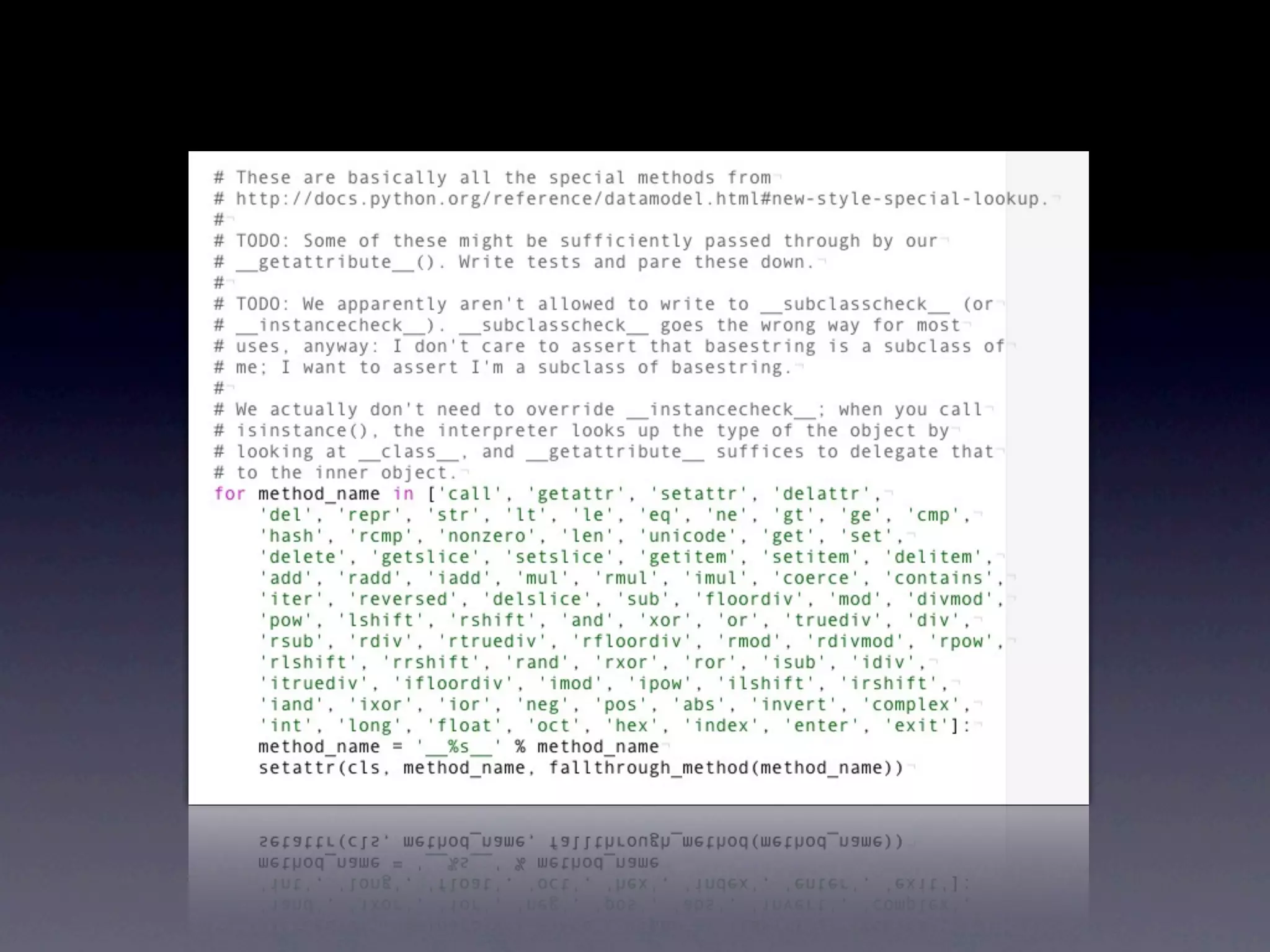
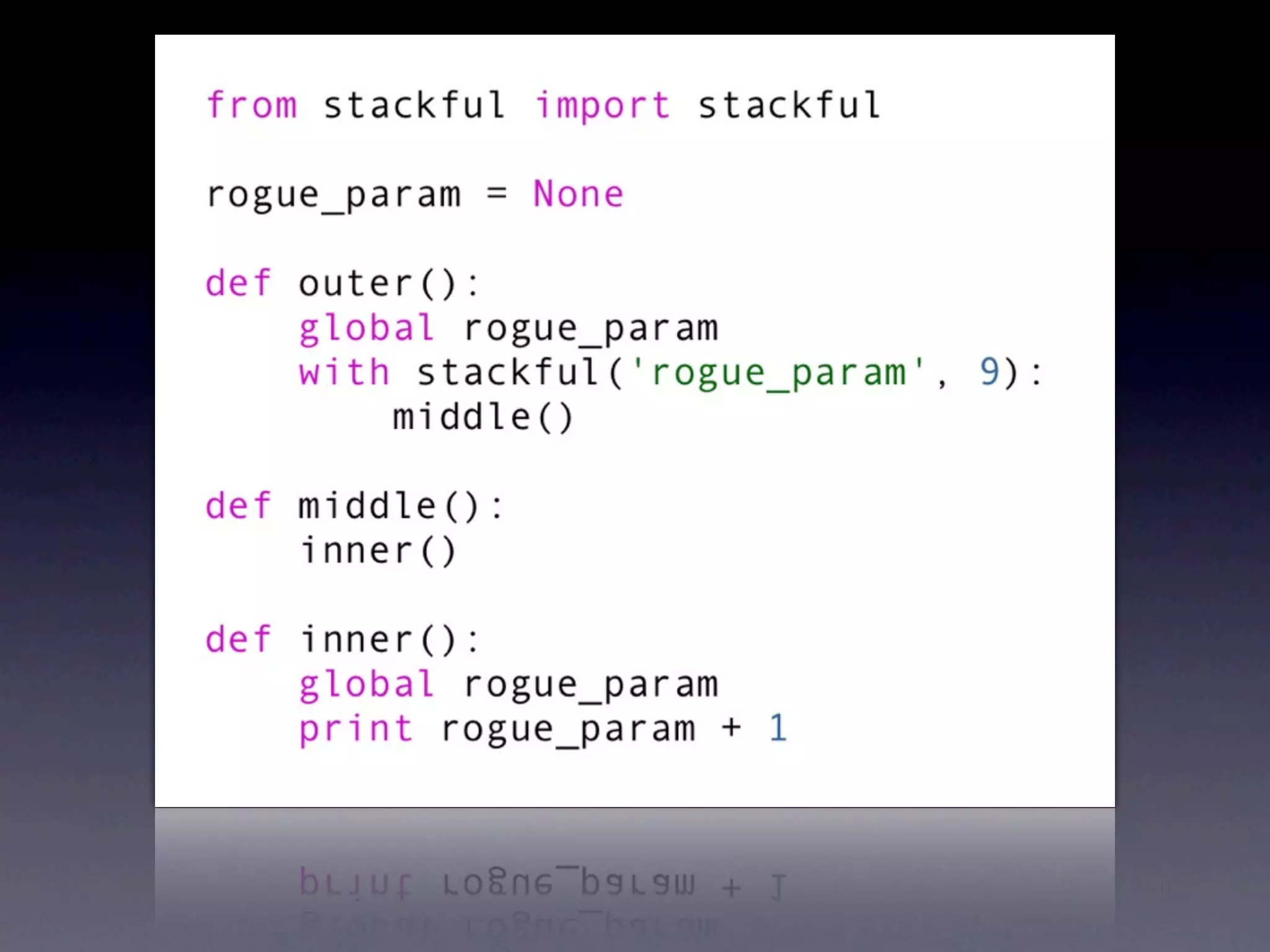
The document discusses the concept of stackful dynamically scoped variables in Python, illustrating the idea with examples from Perl. It contrasts the scoping behaviors of local variables in both programming languages. The author, Erik Rose, suggests that implementing this feature in Python is a 'ridiculous idea' while providing links to related resources.