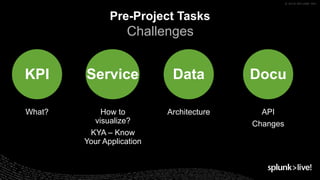
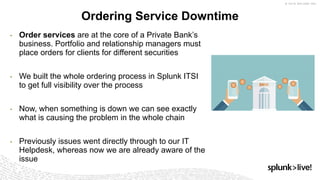
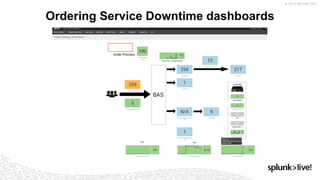
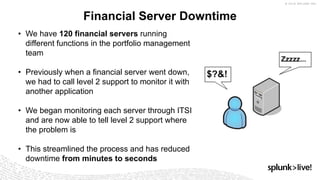
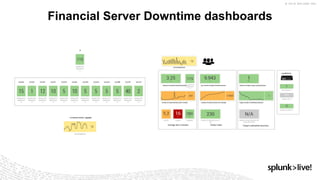
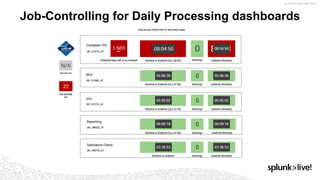
The document presents a presentation by Sebastian Schoer on IT service monitoring and data visualization using Splunk ITSI. Key topics include the importance of defining KPIs, the challenges of complex system architecture, and the significant improvements achieved in monitoring financial servers and order services, which reduced downtime and streamlined processes. The presentation emphasizes integrating applications and overall monitoring as next steps in enhancing operational efficiency.