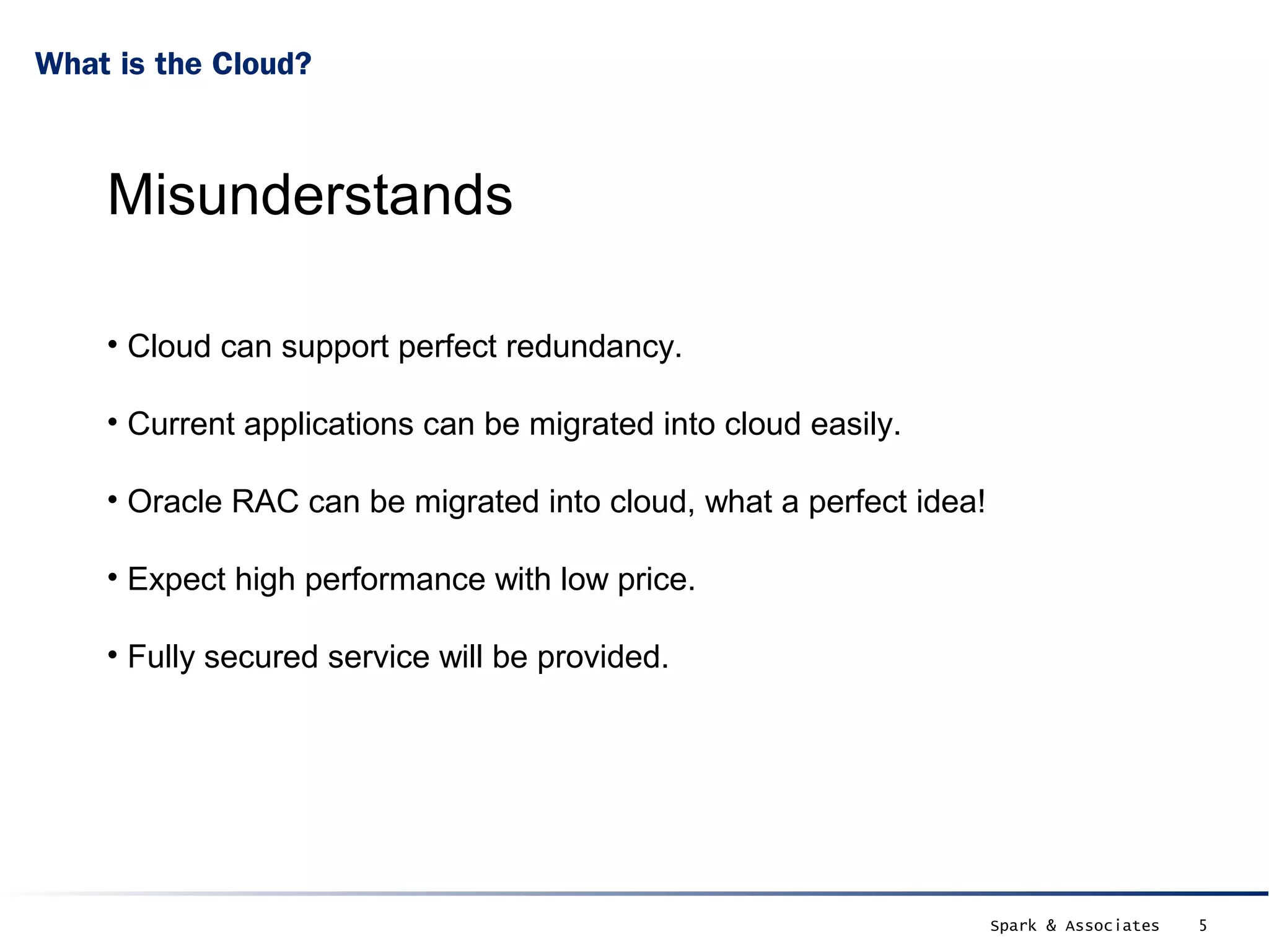
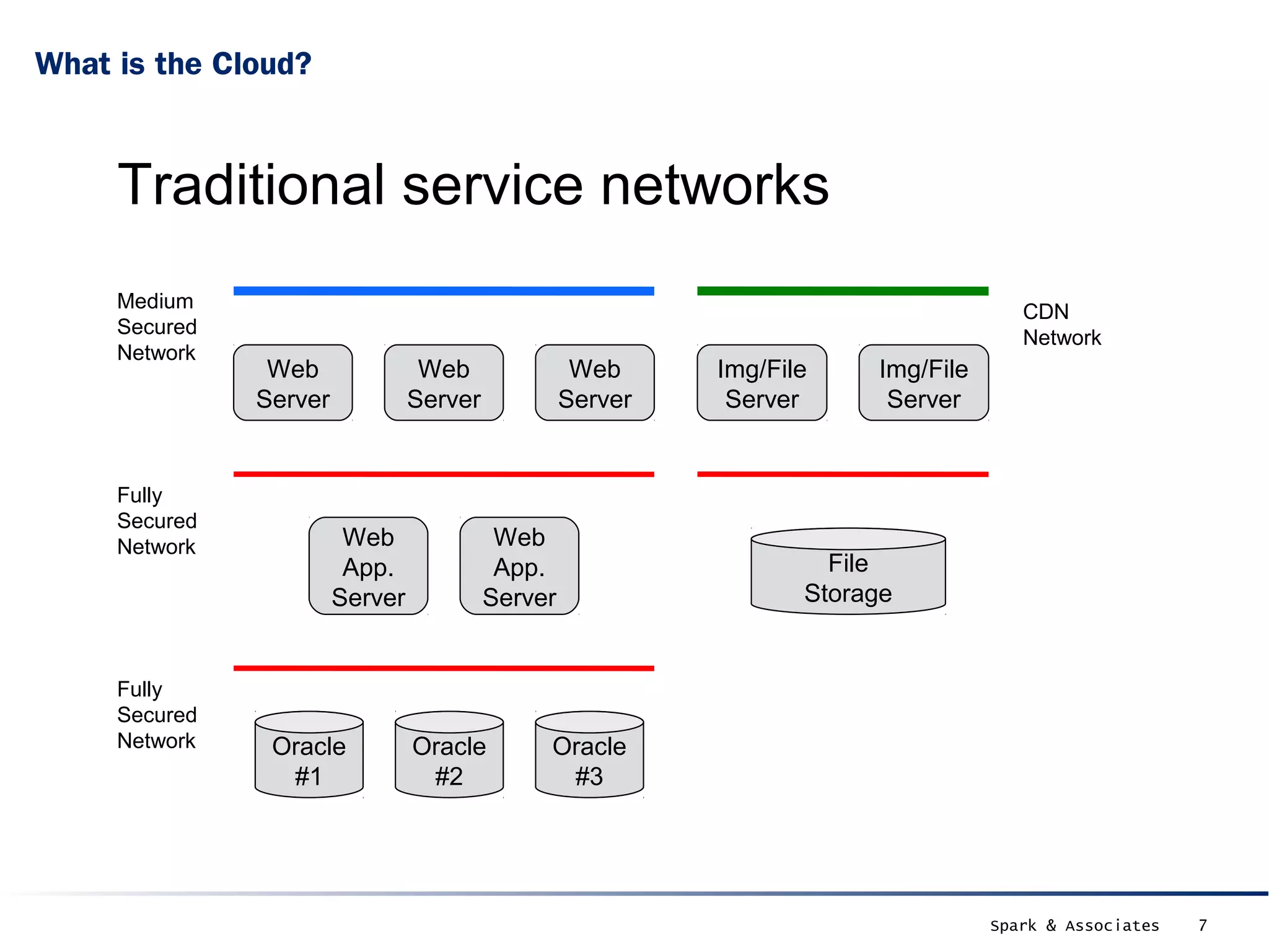
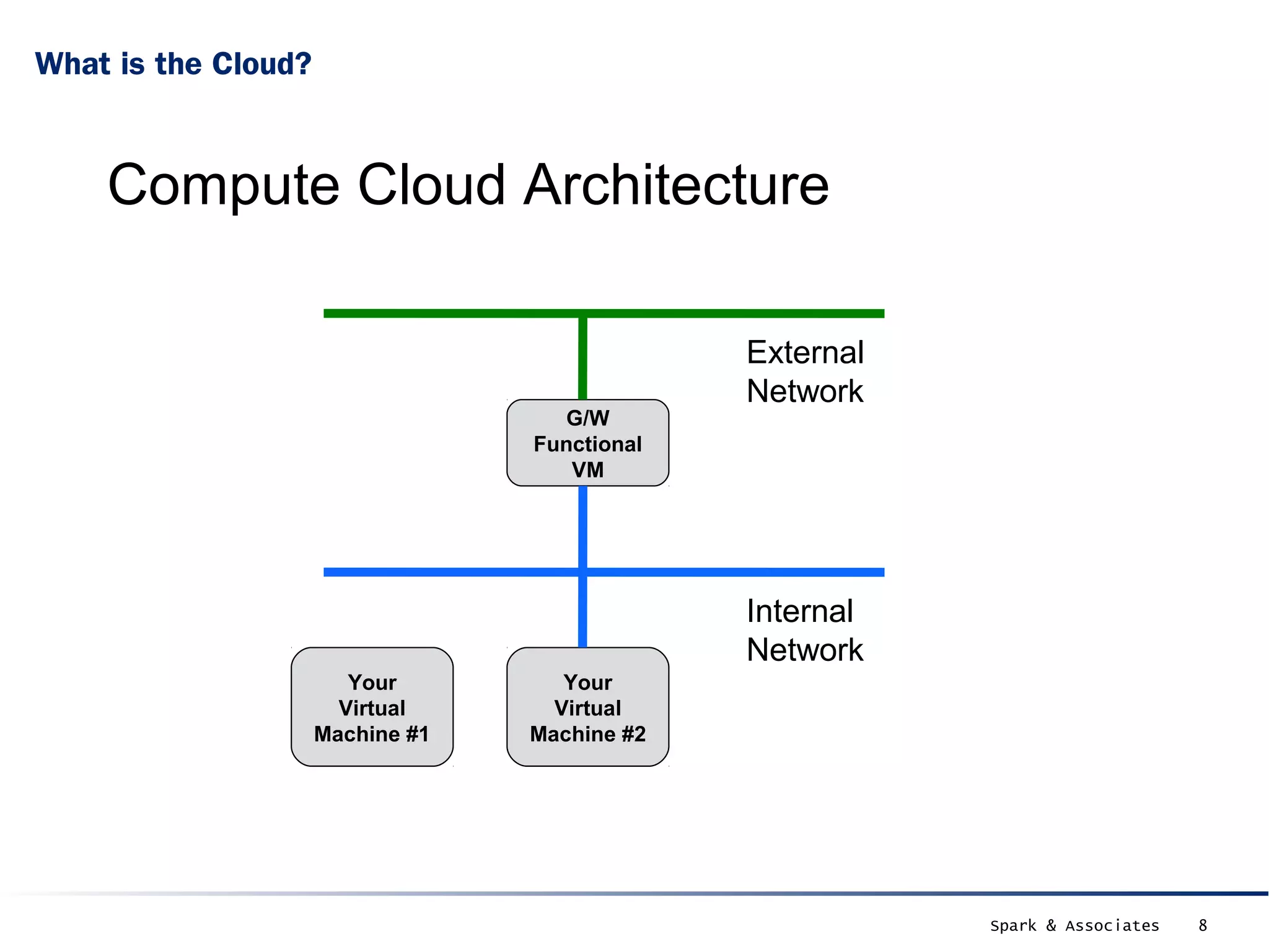
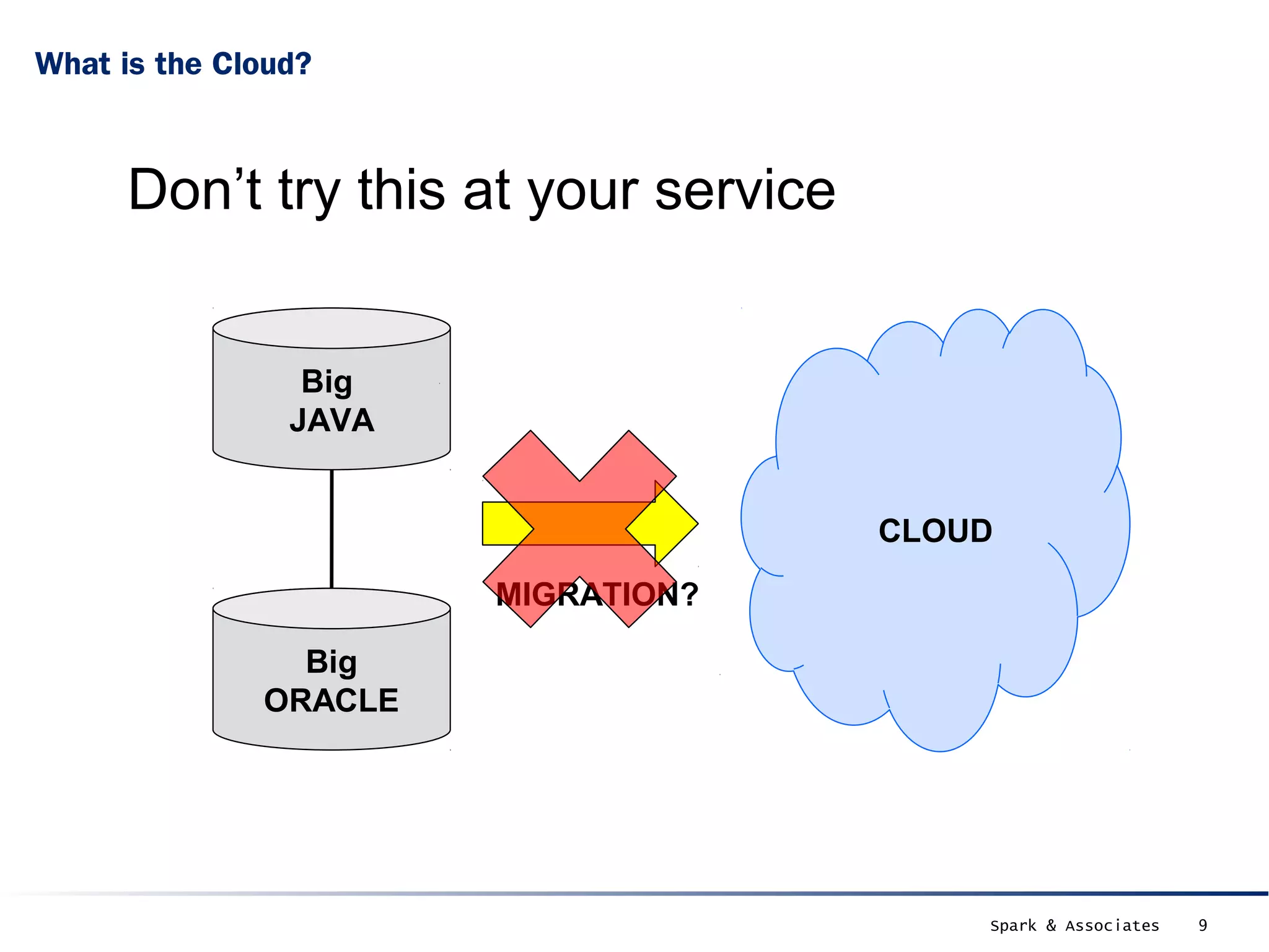
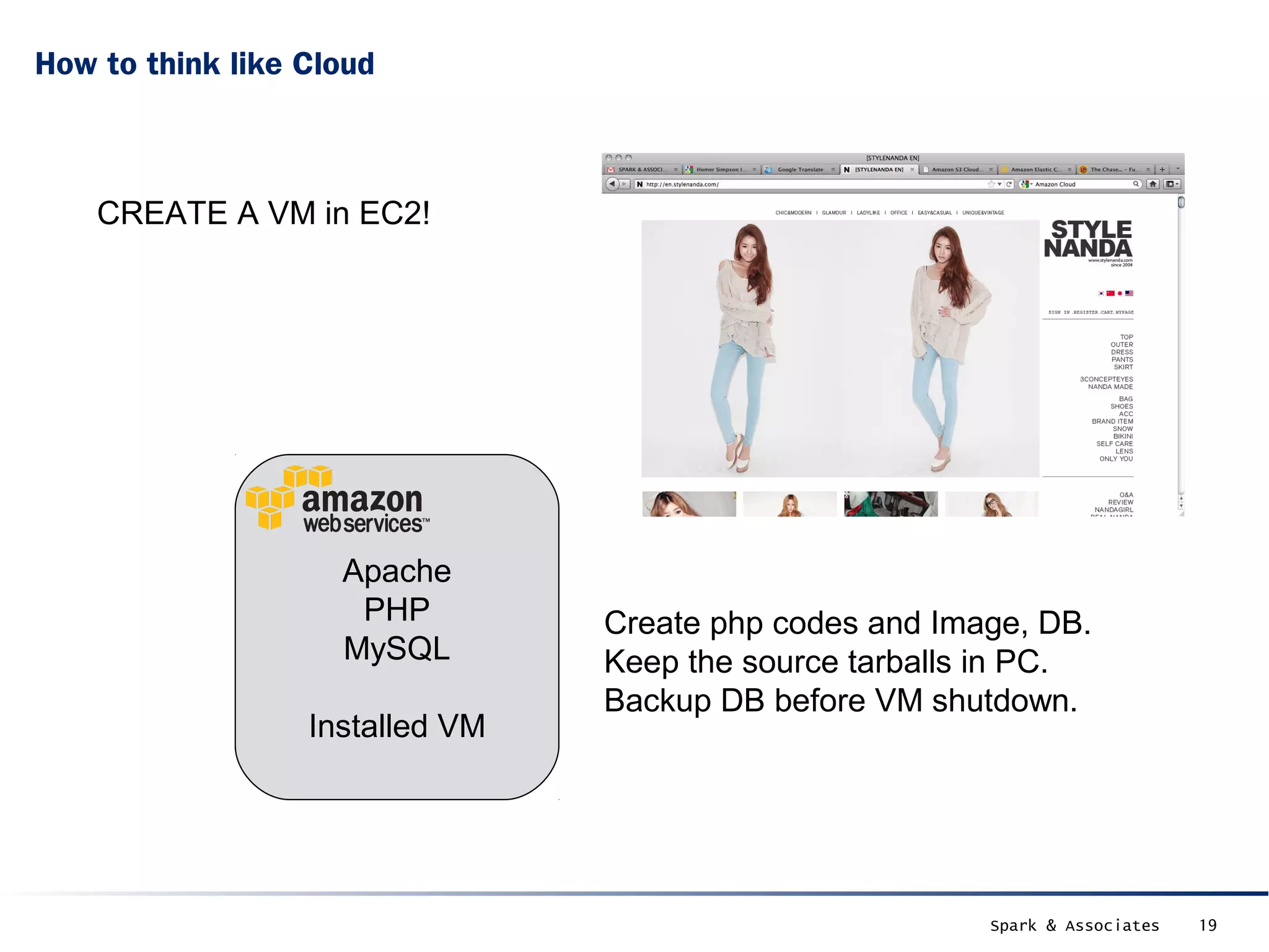
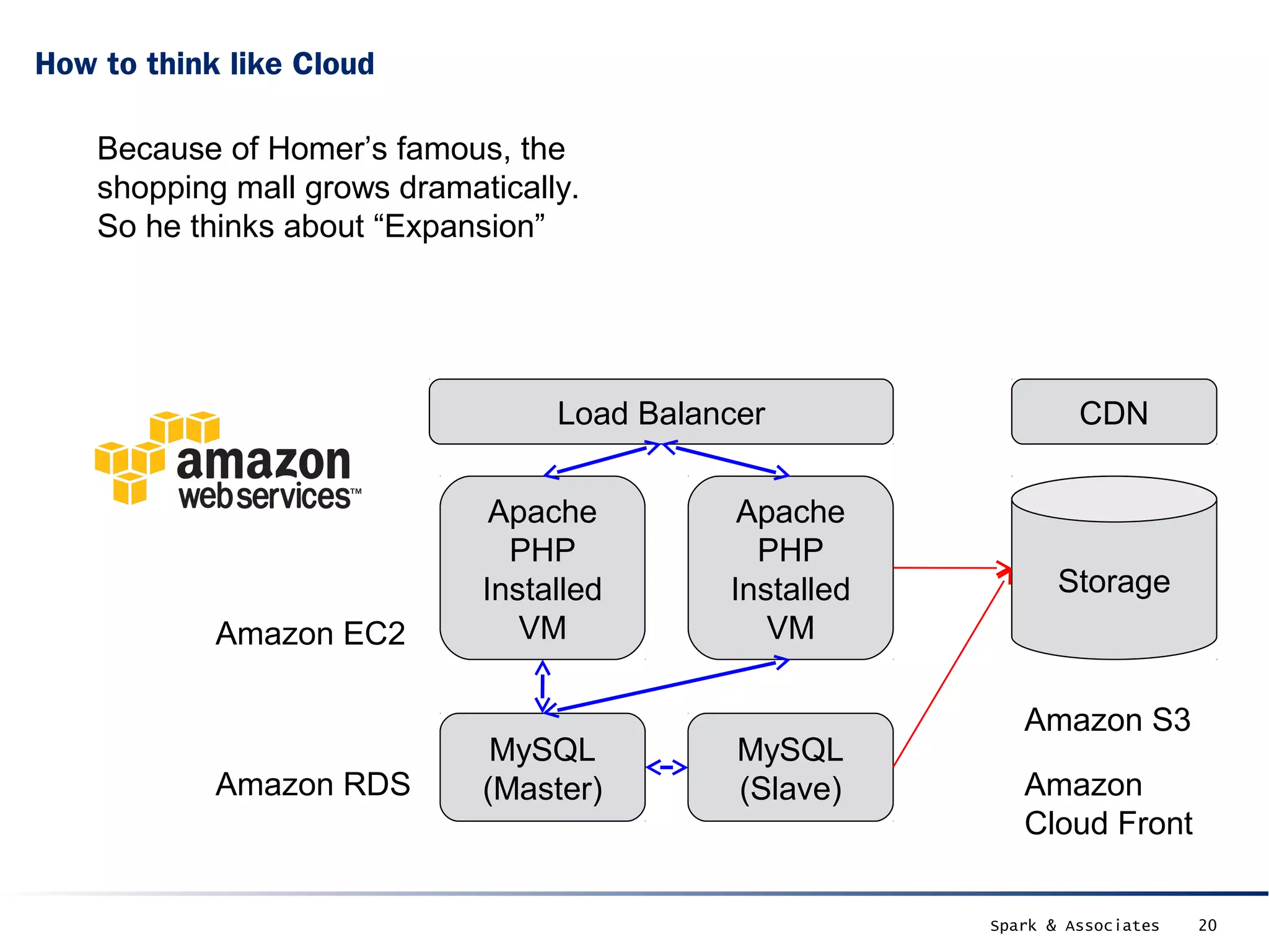
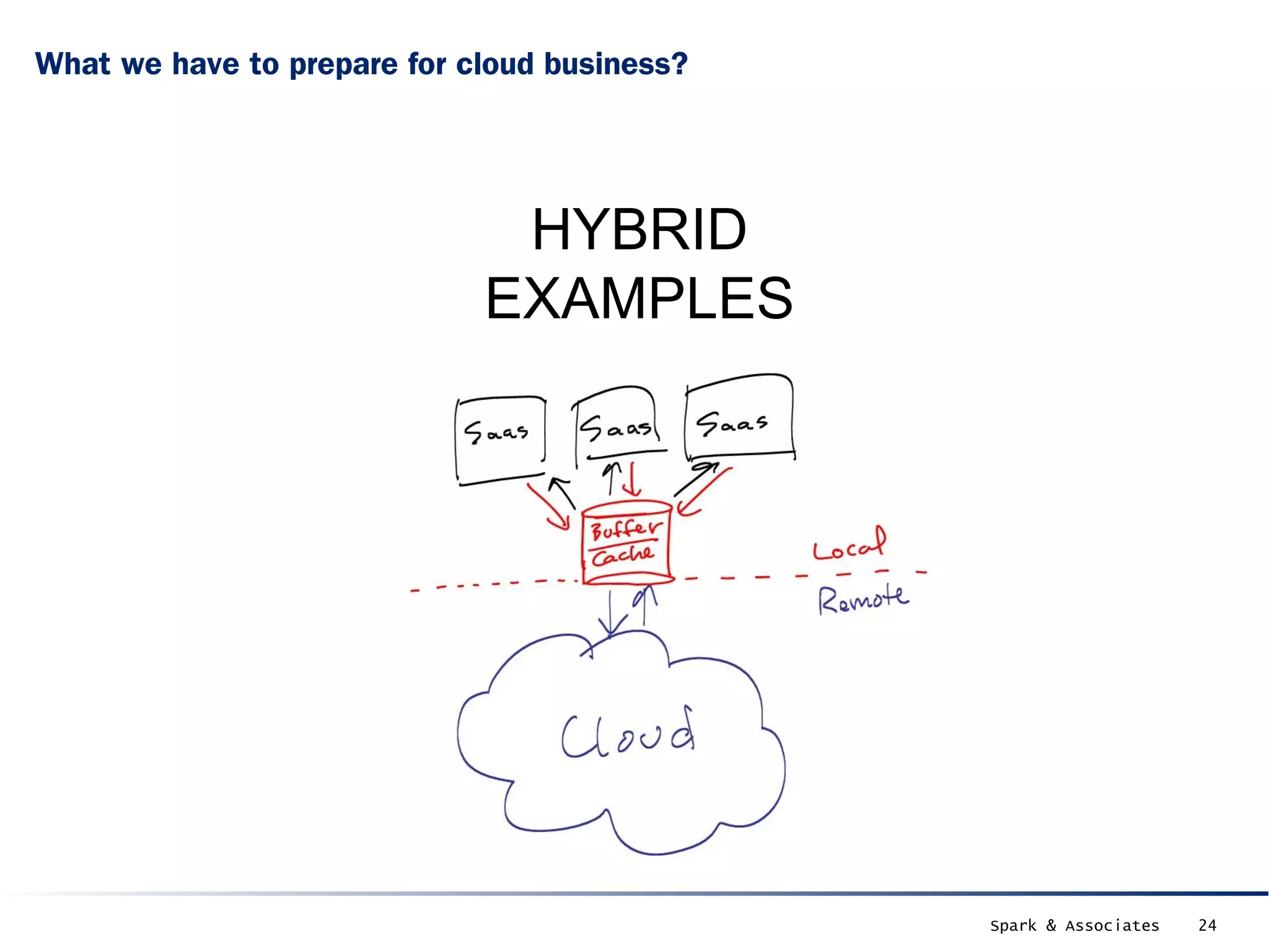
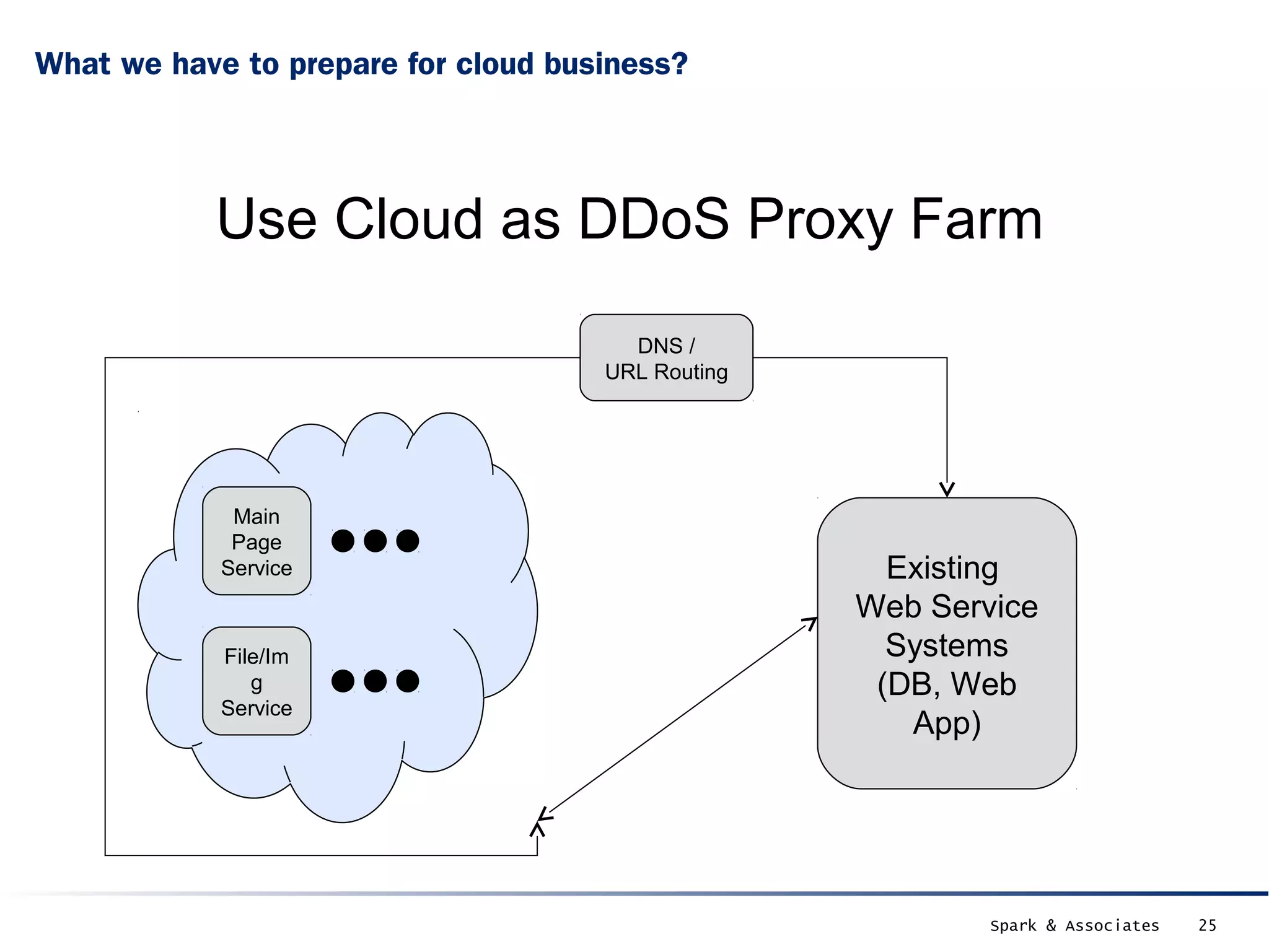
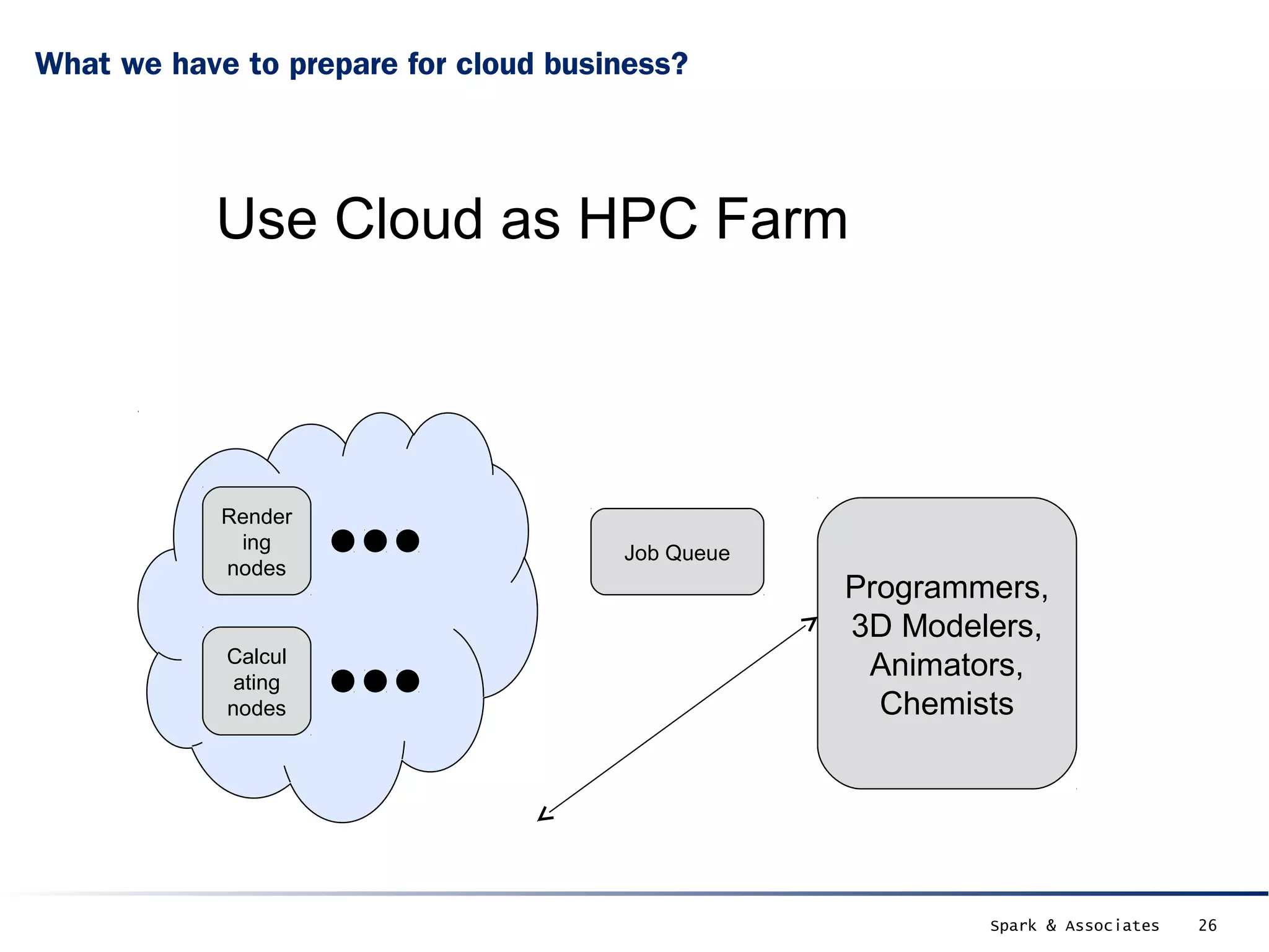
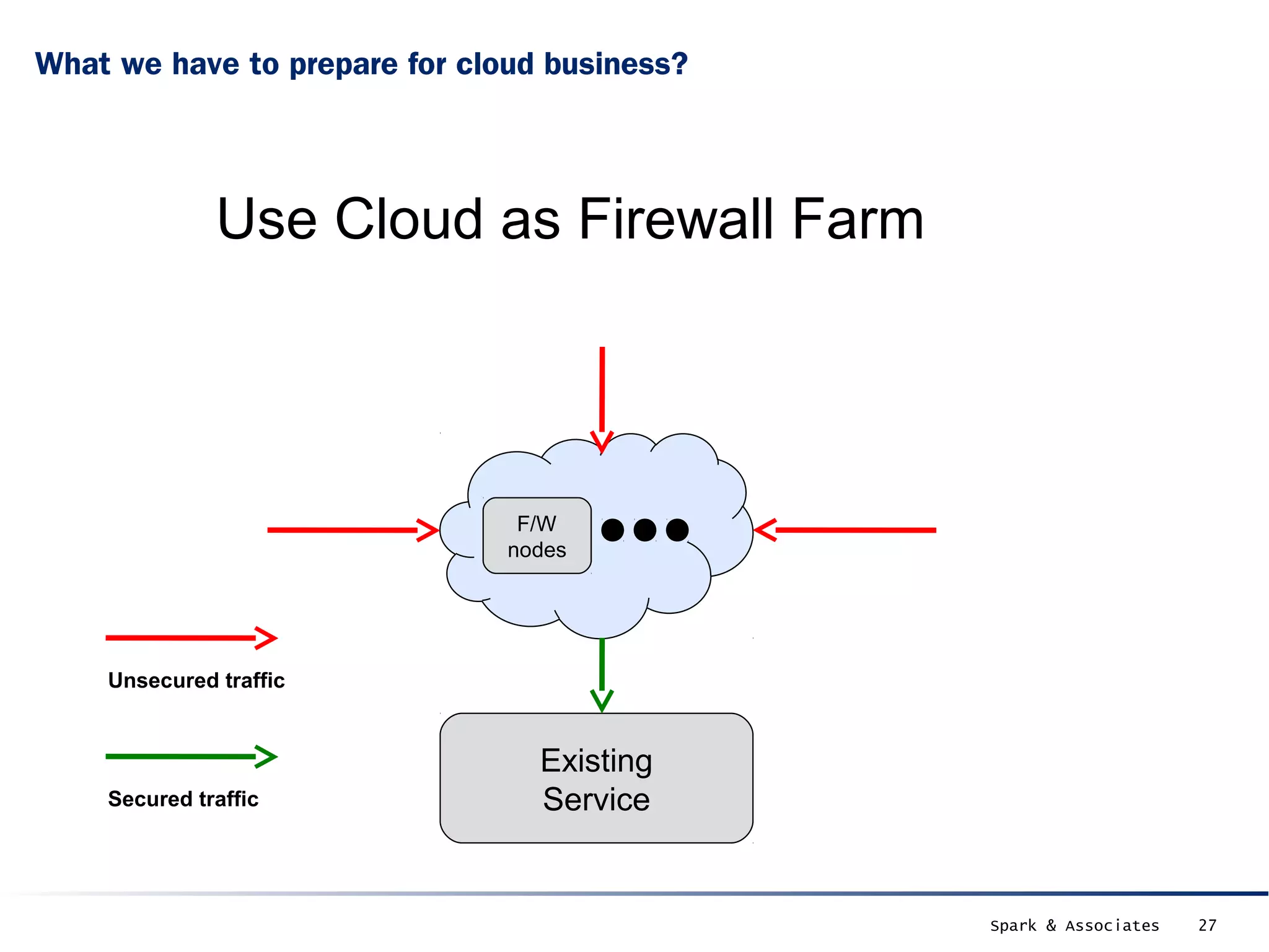
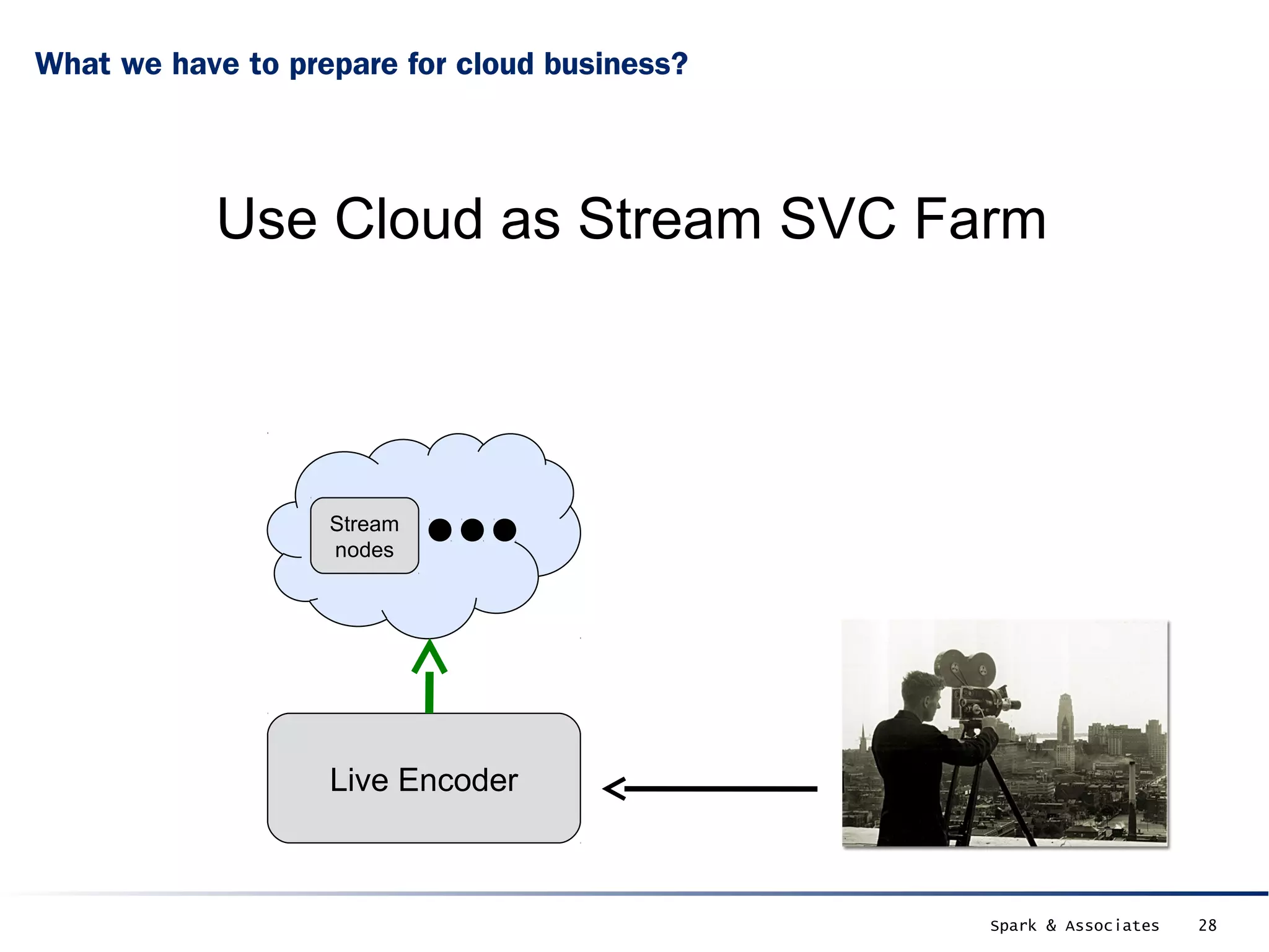
This document discusses how to think like the cloud and prepare for cloud business. It explains that the cloud is not magic and cannot solve complexity, but can provide elasticity. It advises analyzing applications to see which parts are best for the cloud. Using examples of Homer's shopping mall growing and needing expansion, it shows how to distribute applications across cloud services like EC2, RDS, and S3 for scalability. It also provides examples of using hybrid cloud and cloud services for tasks like DDoS protection, HPC, and streaming. The conclusion emphasizes thinking distributed and elastic and finding the best cloud solutions.