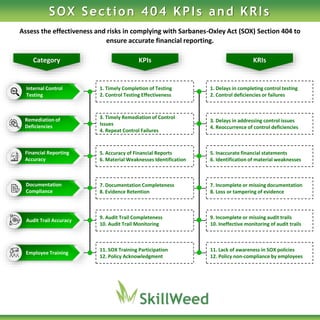
The document outlines key performance indicators (KPIs) and key risk indicators (KRIs) related to Sarbanes-Oxley Act (SOX) Section 404 compliance. It addresses various issues such as the timely completion of internal control testing, remediation of control deficiencies, accuracy of financial reports, and employee training on SOX policies. The focus is on identifying and mitigating risks to ensure accurate financial reporting and effective internal controls.