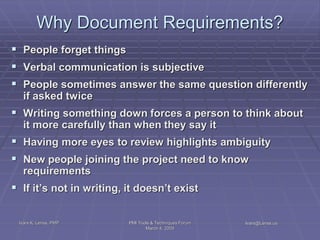
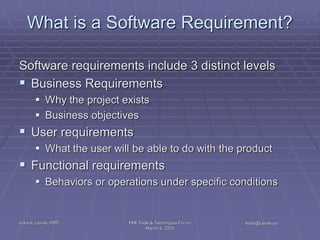
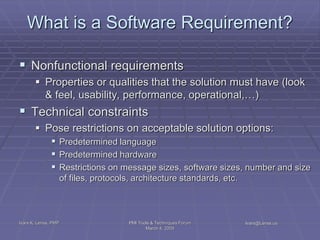
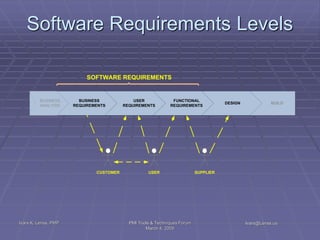
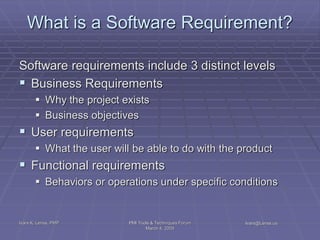
The document discusses the software requirements process and what constitutes a software requirement. It addresses that a software requirement can exist at the business, user, or functional level and includes conditions or capabilities needed by stakeholders. Requirements must be well-formed to be unambiguous and validateable. They should be documented to ensure common understanding as a project progresses.
![What Is a Requirement?
The IIBA built on the IEEE definition:
A requirement is a condition or capability needed by a
stakeholder to solve a problem or achieve an
objective.
[source: IIBA Business Analysis Body of Knowledge (IIBA, 2008]
Ivars K. Lenss, PMP PMI Tools & Techniques Forum Ivars@Lenss.us
March 4, 2009](https://image.slidesharecdn.com/softwarerequirementsworkshoppresentation-13294807240994-phpapp01-120217062913-phpapp01/85/Software-Requirements-Workshop-Presentation-3-320.jpg)
![What Does a Requirement Look Like?
• A sentence (“The system shall…”)
• A structured sentence (as in a business rule)
• A structured text template
• A table or spreadsheet (list of stakeholders)
• A diagram (workflow)
• A model (entity-relationship diagram and details)
• A prototype
• A graph
• Any format that communicates
[source: Seven Steps to Mastering Business Analysis, Barret, 2009]
Ivars K. Lenss, PMP PMI Tools & Techniques Forum Ivars@Lenss.us
March 4, 2009](https://image.slidesharecdn.com/softwarerequirementsworkshoppresentation-13294807240994-phpapp01-120217062913-phpapp01/85/Software-Requirements-Workshop-Presentation-4-320.jpg)
![Software Requirements Specification
Basic issues addressed in an SRS are:
Functionality
External interfaces
Performance
Non-functional requirements
Constraints imposed on the solution
[IEEE Standard]
Ivars K. Lenss, PMP PMI Tools & Techniques Forum Ivars@Lenss.us
March 4, 2009](https://image.slidesharecdn.com/softwarerequirementsworkshoppresentation-13294807240994-phpapp01-120217062913-phpapp01/85/Software-Requirements-Workshop-Presentation-21-320.jpg)
![Software Requirements Attributes
Stability
Status
Acceptance criteria [metric]
Complexity [metric]
Performance [metric]
Urgency [metric]
Business value [metric]
Risk [metric]
Ivars K. Lenss, PMP PMI Tools & Techniques Forum Ivars@Lenss.us
March 4, 2009](https://image.slidesharecdn.com/softwarerequirementsworkshoppresentation-13294807240994-phpapp01-120217062913-phpapp01/85/Software-Requirements-Workshop-Presentation-29-320.jpg)