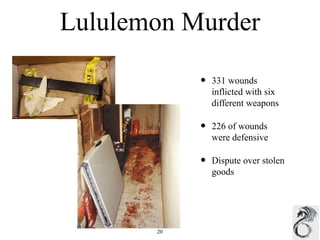
This document provides a security primer for small business owners, outlining steps to assess risks and implement security measures. It discusses recognizing threats, conducting inspections to identify vulnerabilities, implementing preventative measures like access controls and clutter removal, and identifying internal and external threats like employee misconduct, random visitors, and weather-related events. The document also provides solutions to common security issues like using CCTV systems, security fencing, and conflict de-escalation techniques to help small businesses safeguard against crime.