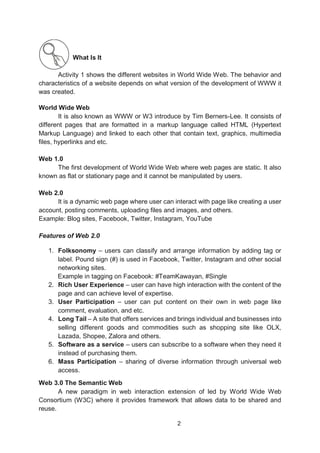
Here are some key points about online safety habits based on the self-check activity:
- Talking to strangers online can put your personal information and safety at risk. It's best to only interact with people you know personally.
- Sharing passwords allows others access to your accounts which can enable cybercrimes like identity theft. Keep passwords private.
- Posting about future vacations alerts potential burglars when your home will be empty. It's safer to share travel plans after returning.
- Unsecured websites may download malware or steal personal data. Only visit reputable sites using HTTPS encryption.
- Ranting online can have real-life consequences like damaging your reputation or career. Consider thoughts carefully before