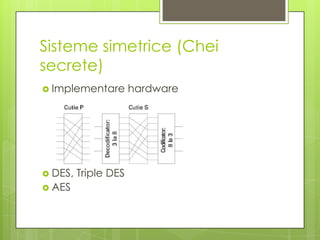
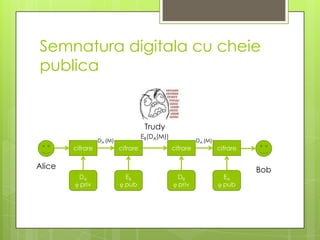
Documentul discută problemele de securitate în secolul 21, inclusiv confidențialitatea, autentificarea și integritatea datelor, precum și metodele de rezolvare, cum ar fi criptarea și semnăturile digitale. Se detaliază criptografia simetrică și asimetrică, metodele de cifrare și descifrare, precum și importanța educației și politicilor de securitate. În plus, sunt evaluate problemele asociate cu utilizarea cheilor publice și private, împreună cu soluții și tehnici pentru a asigura securitatea informațiilor.