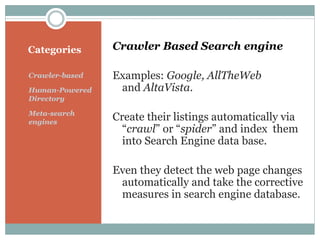
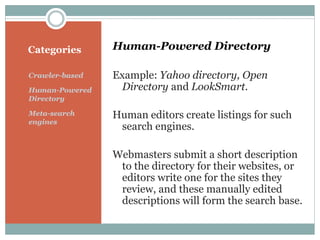
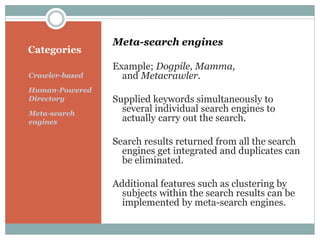
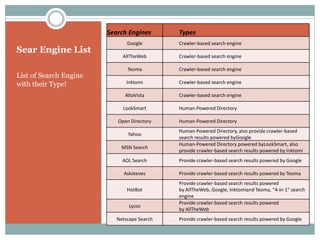
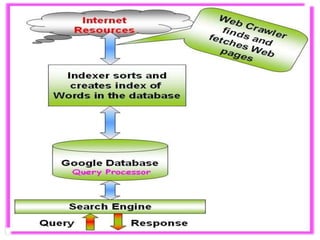
The document discusses different types of search engines including crawler-based, human-powered directories, and meta-search engines. It provides examples of each type, detailing how they operate, such as automated crawling for crawler-based engines and manual editing for human-powered directories. Additionally, it lists various search engines along with their categories, highlighting unique features like keyword integration in meta-search engines.