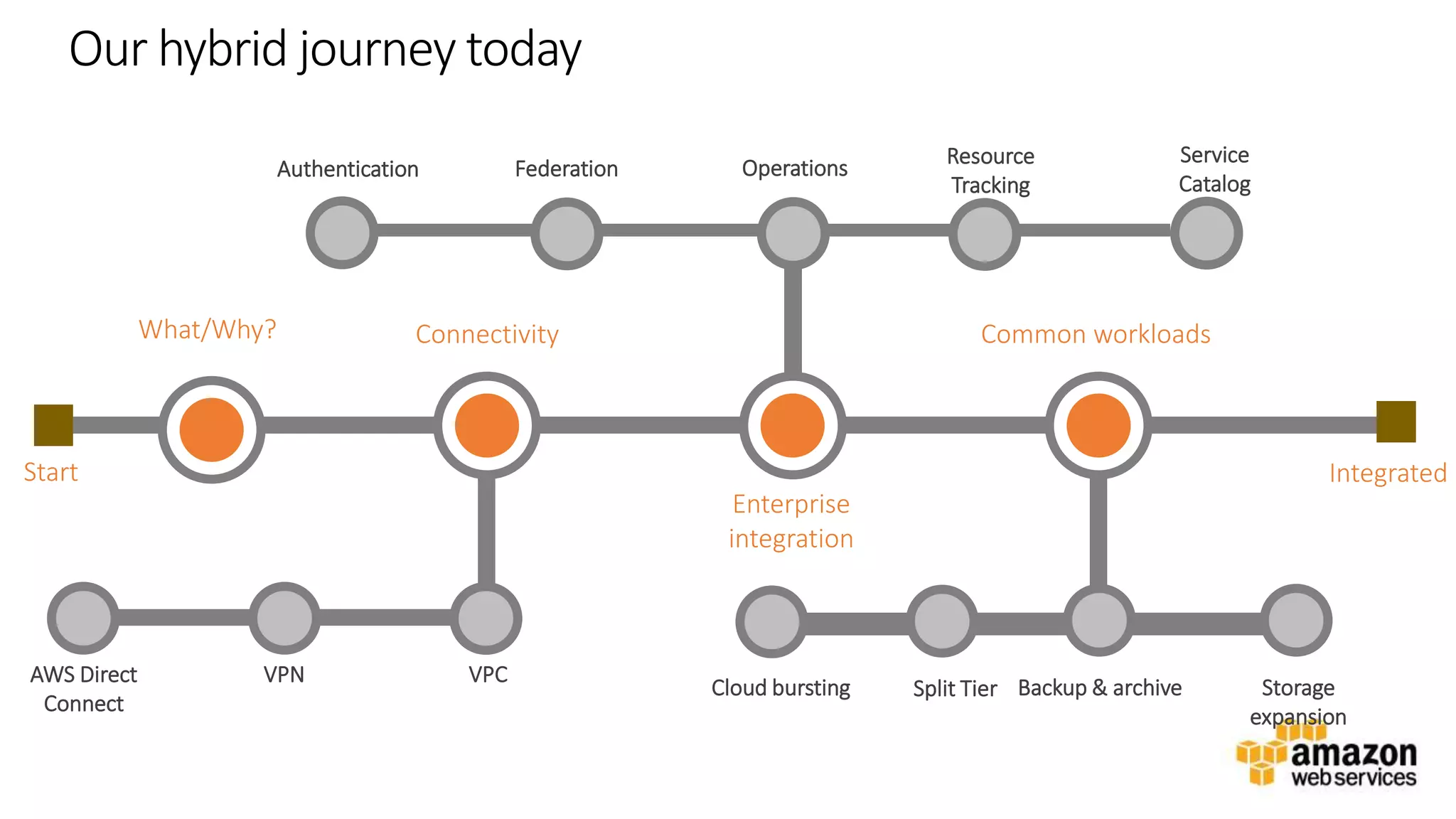
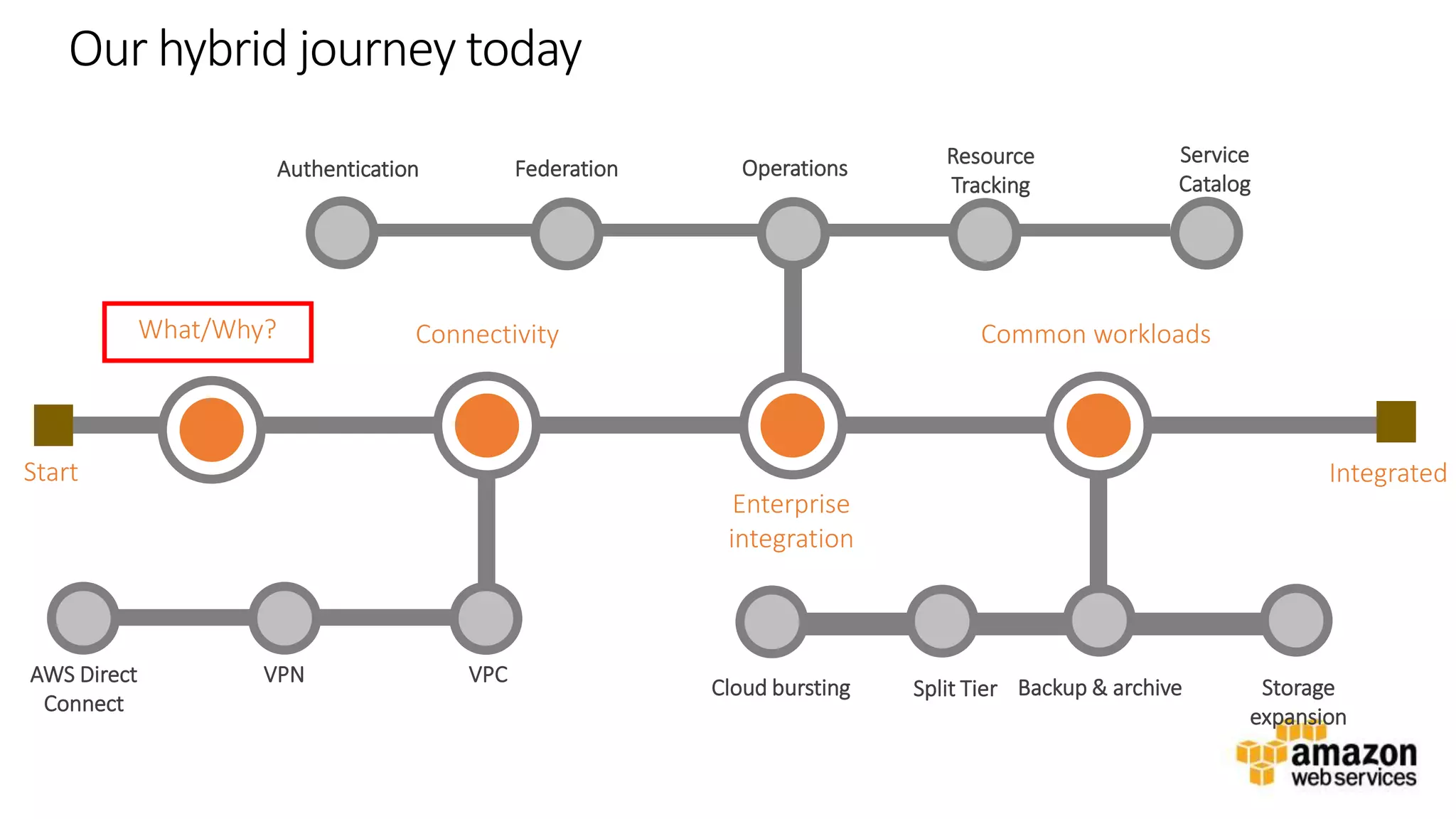
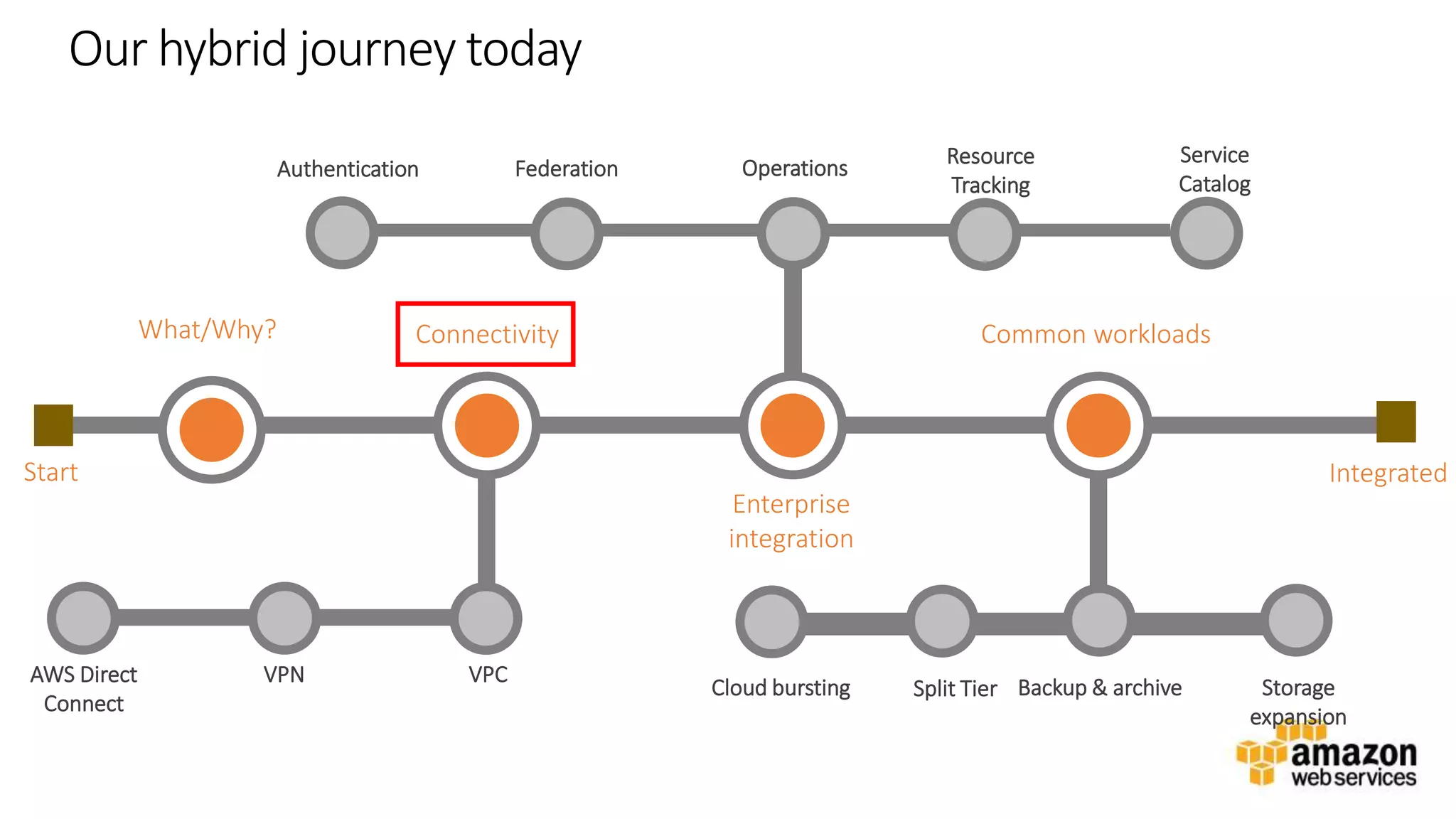
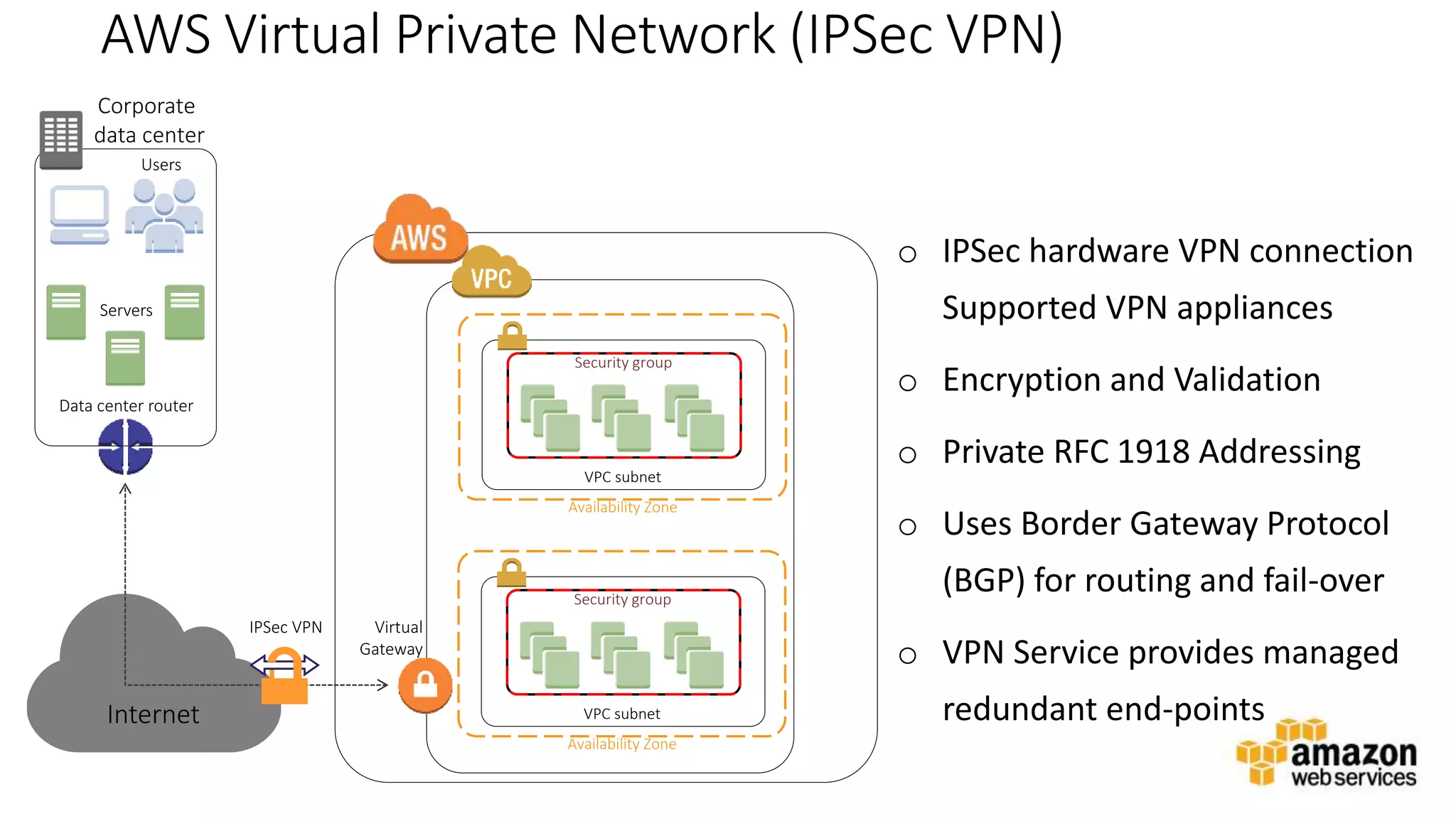
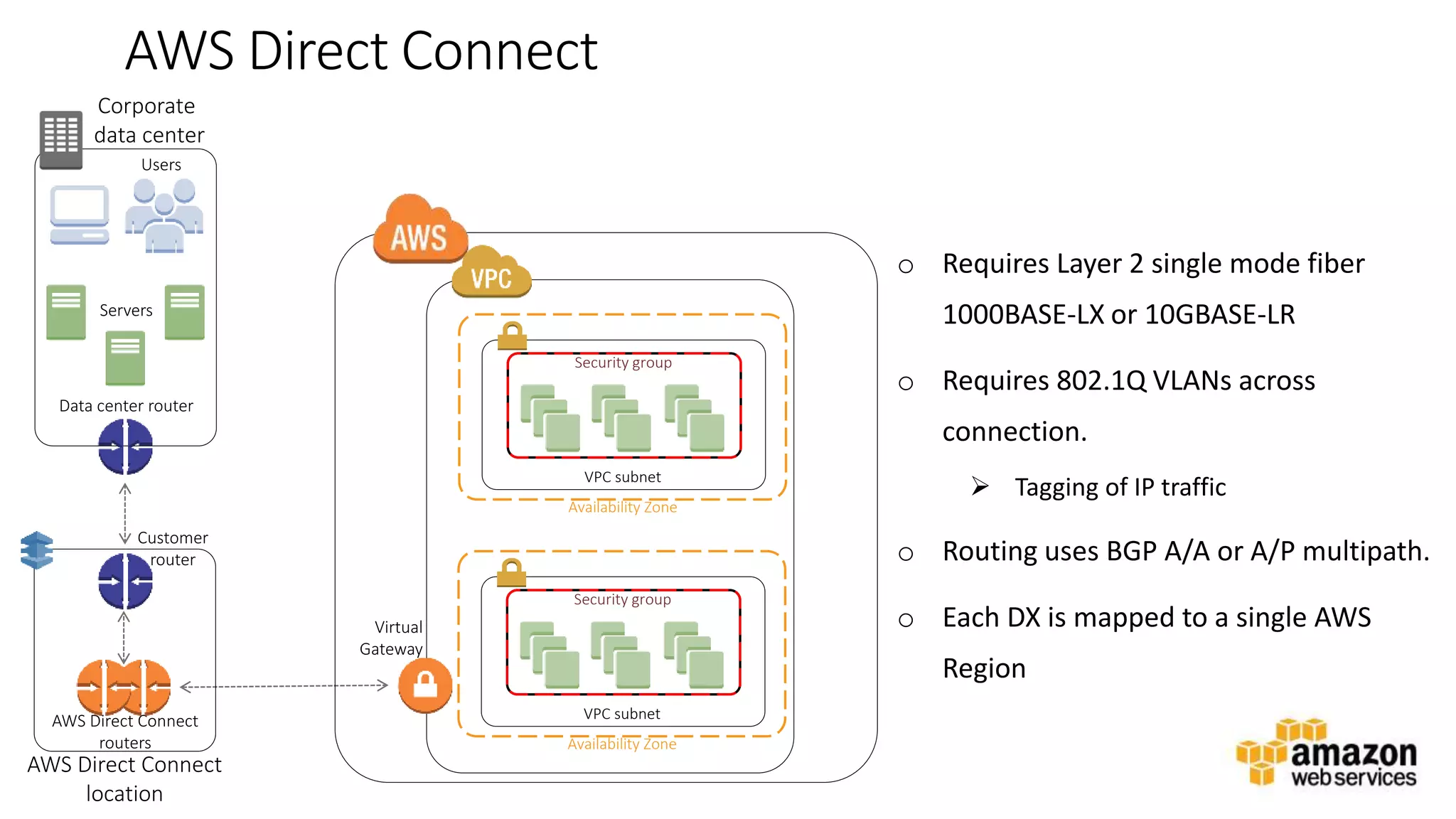
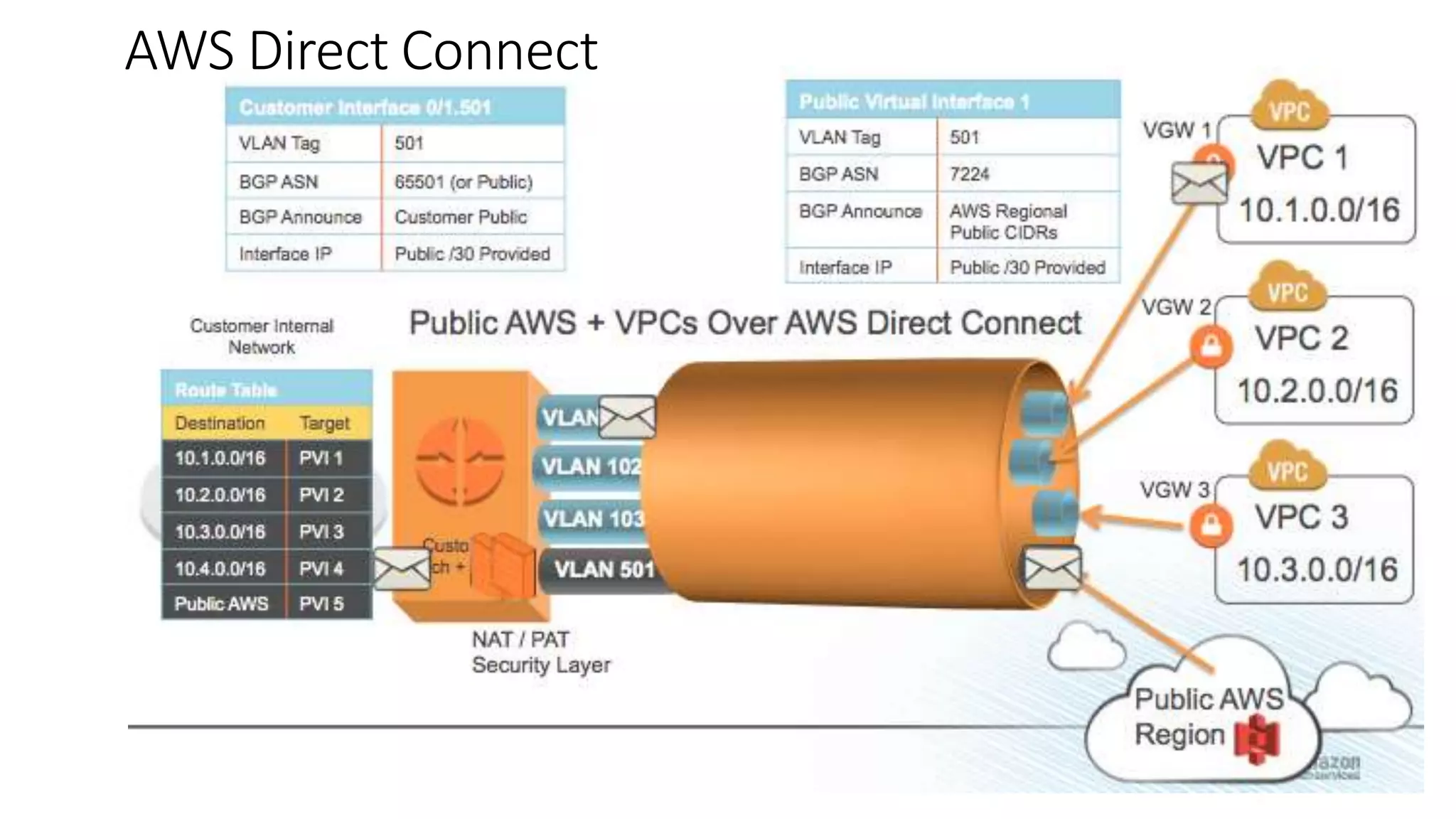
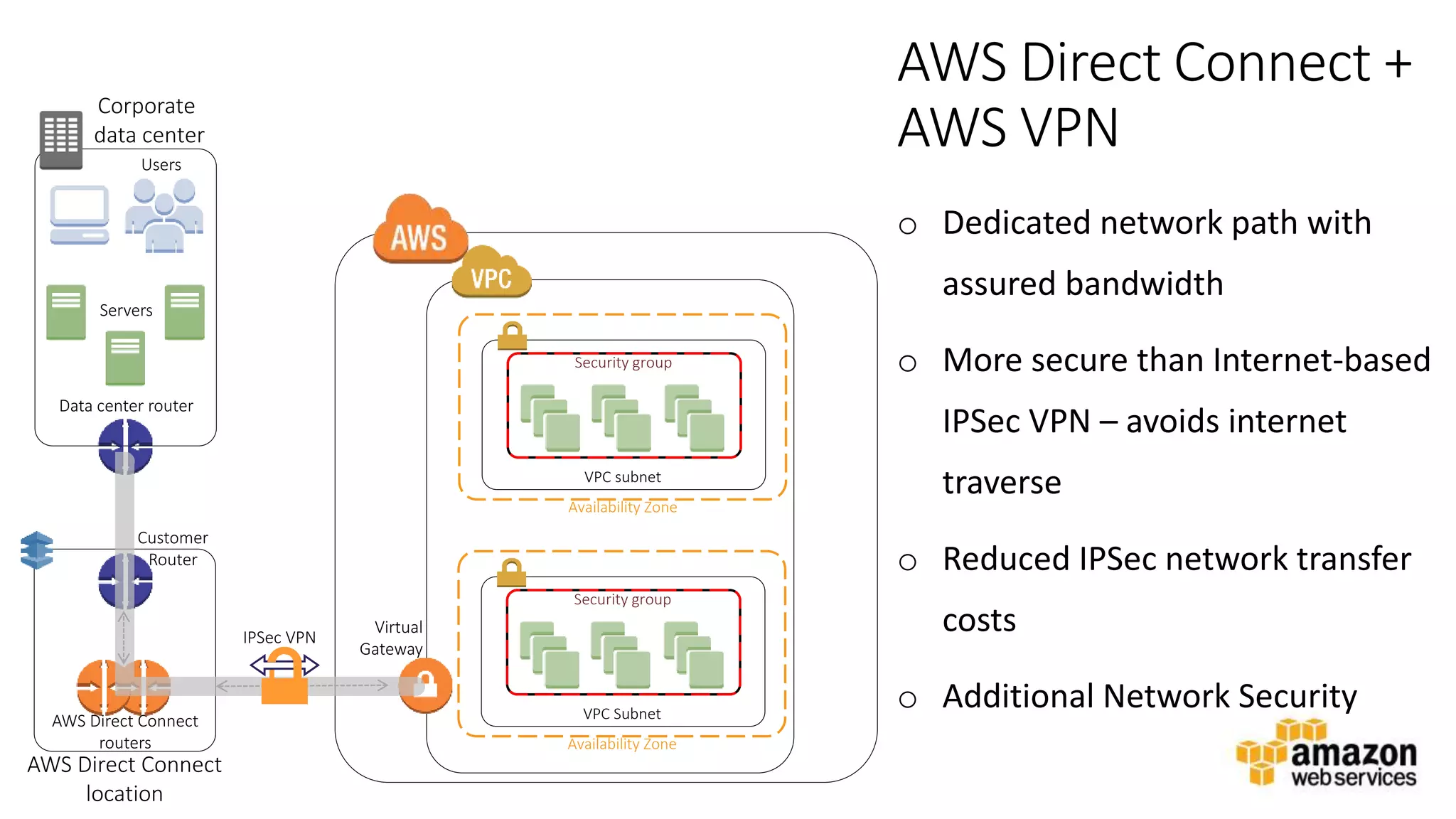
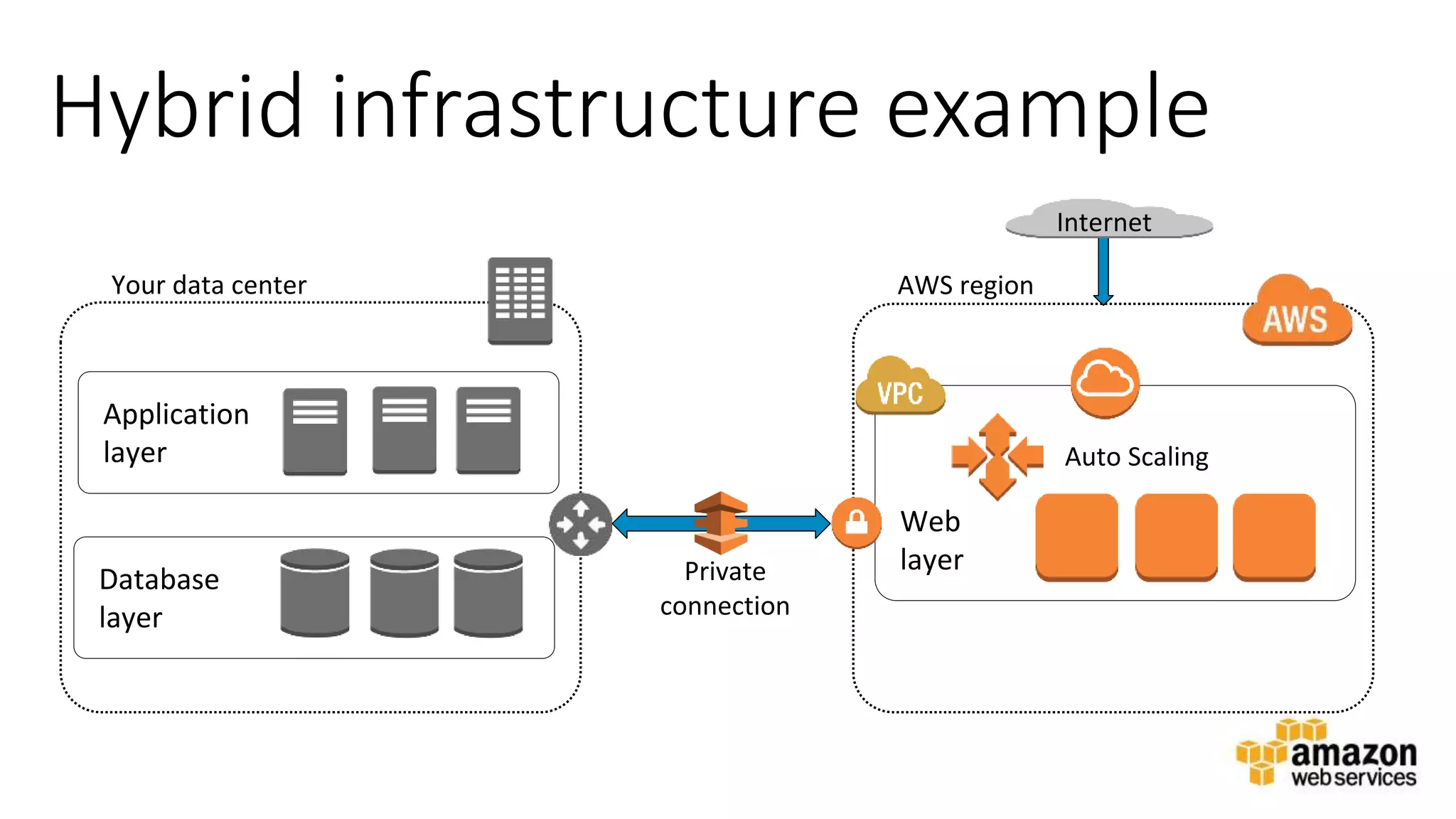
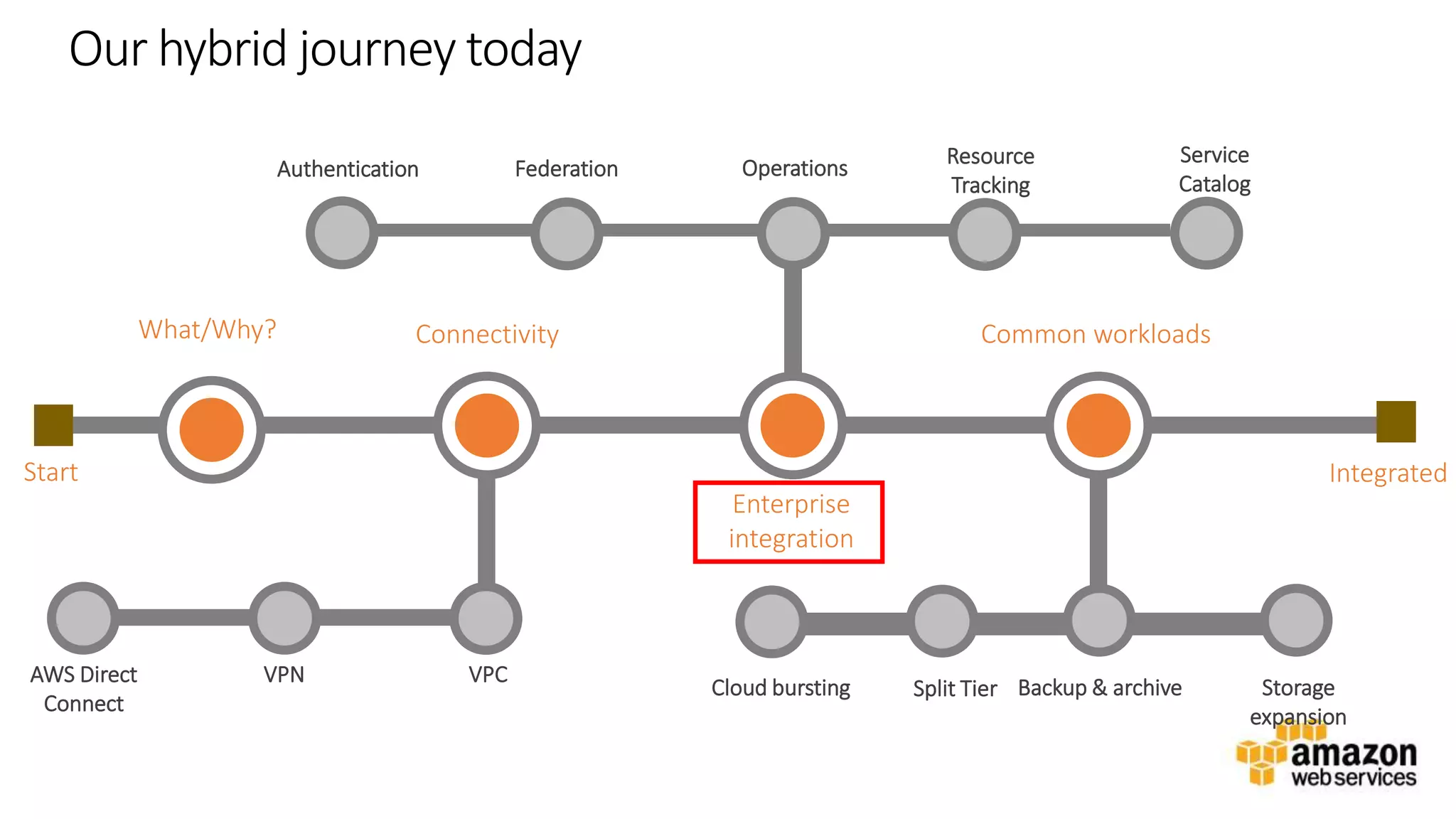
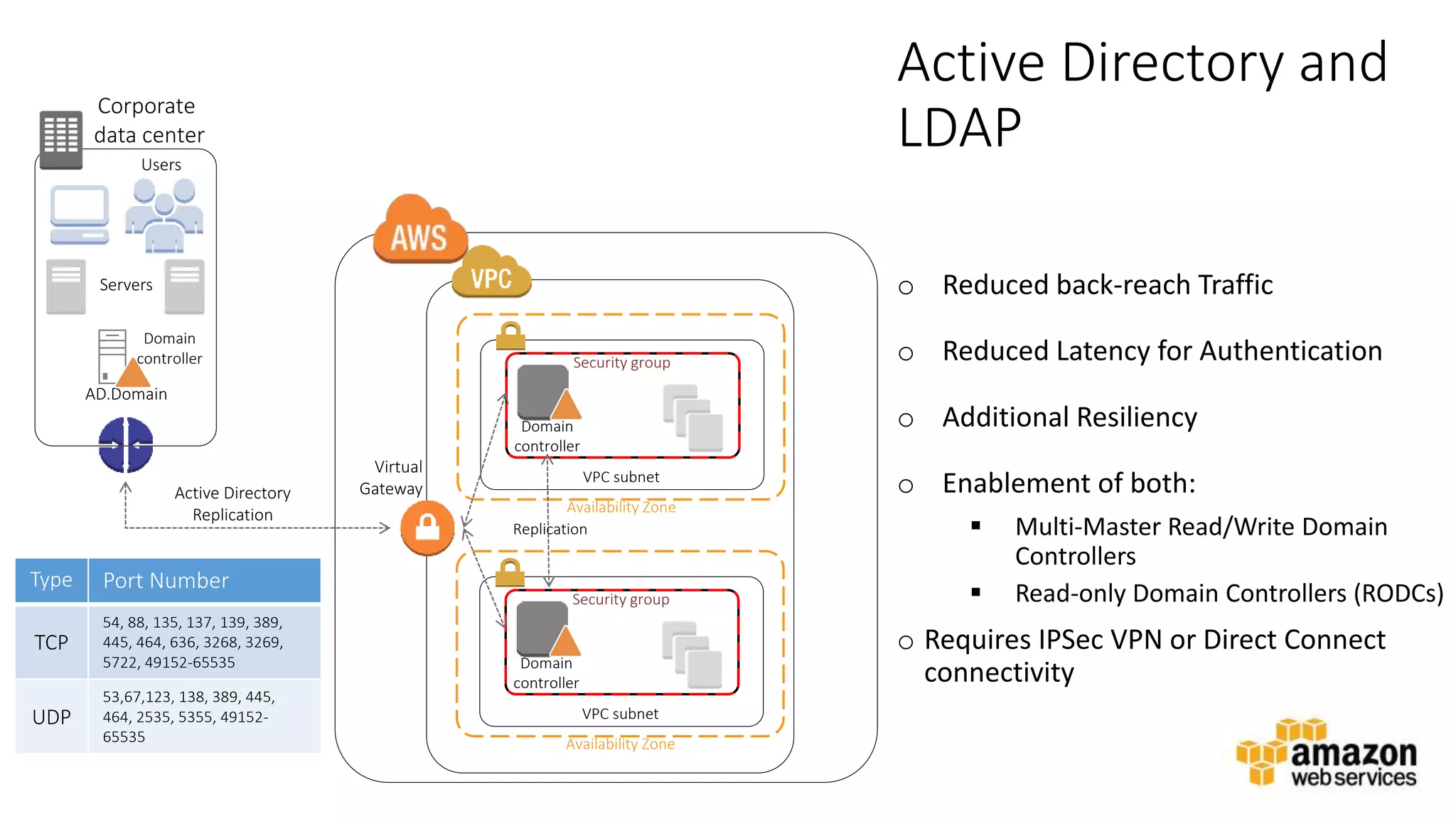
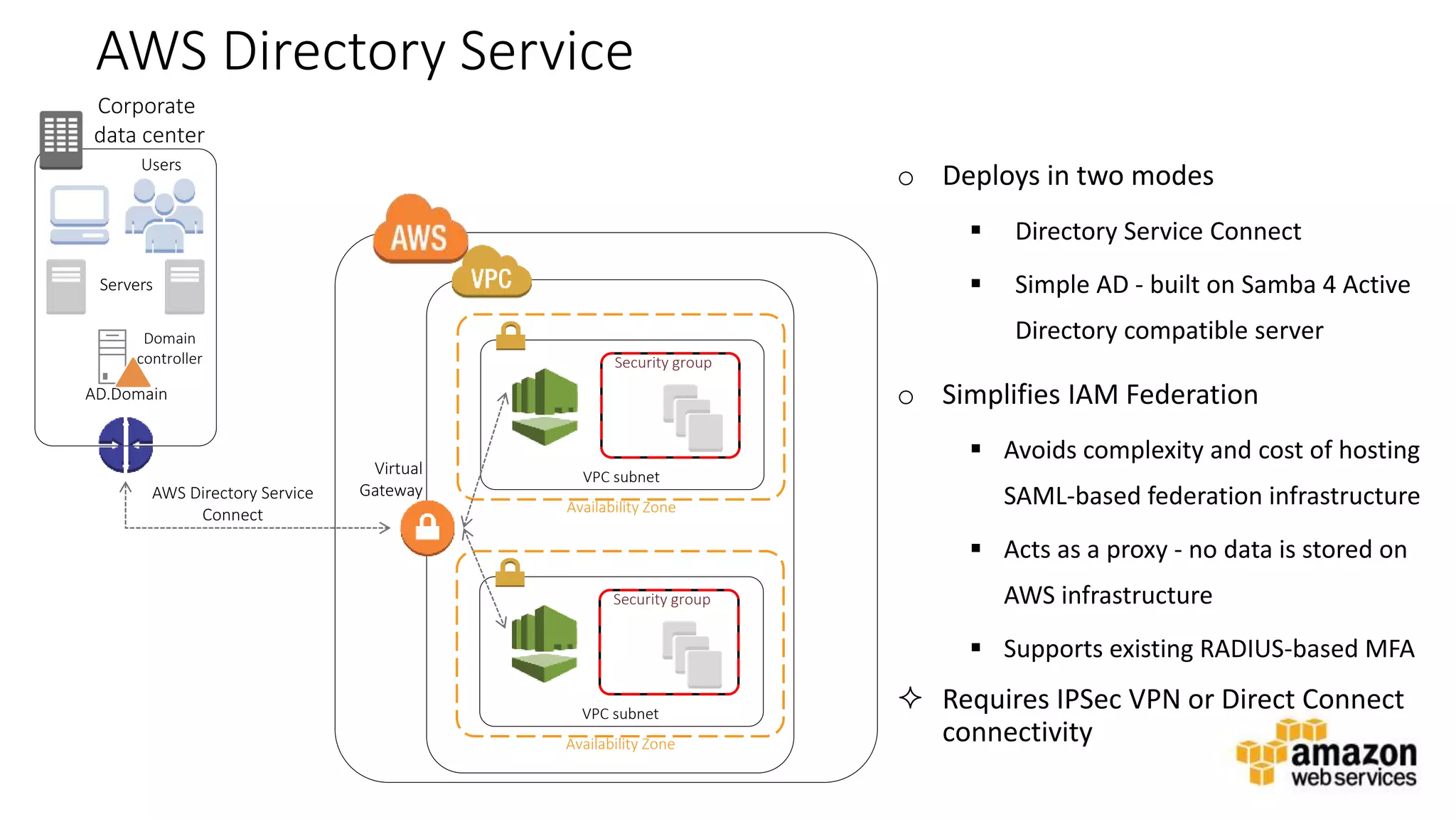
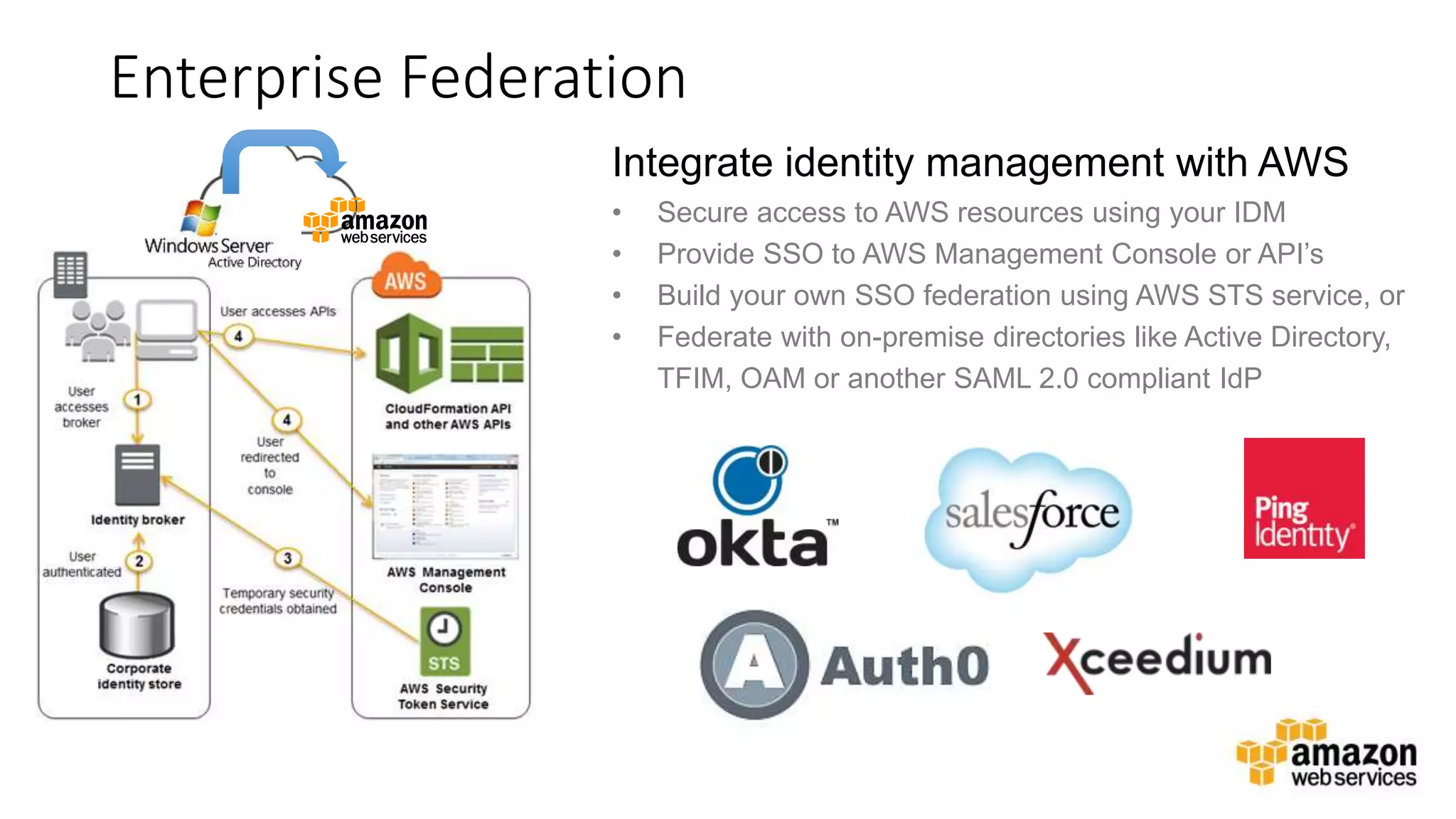
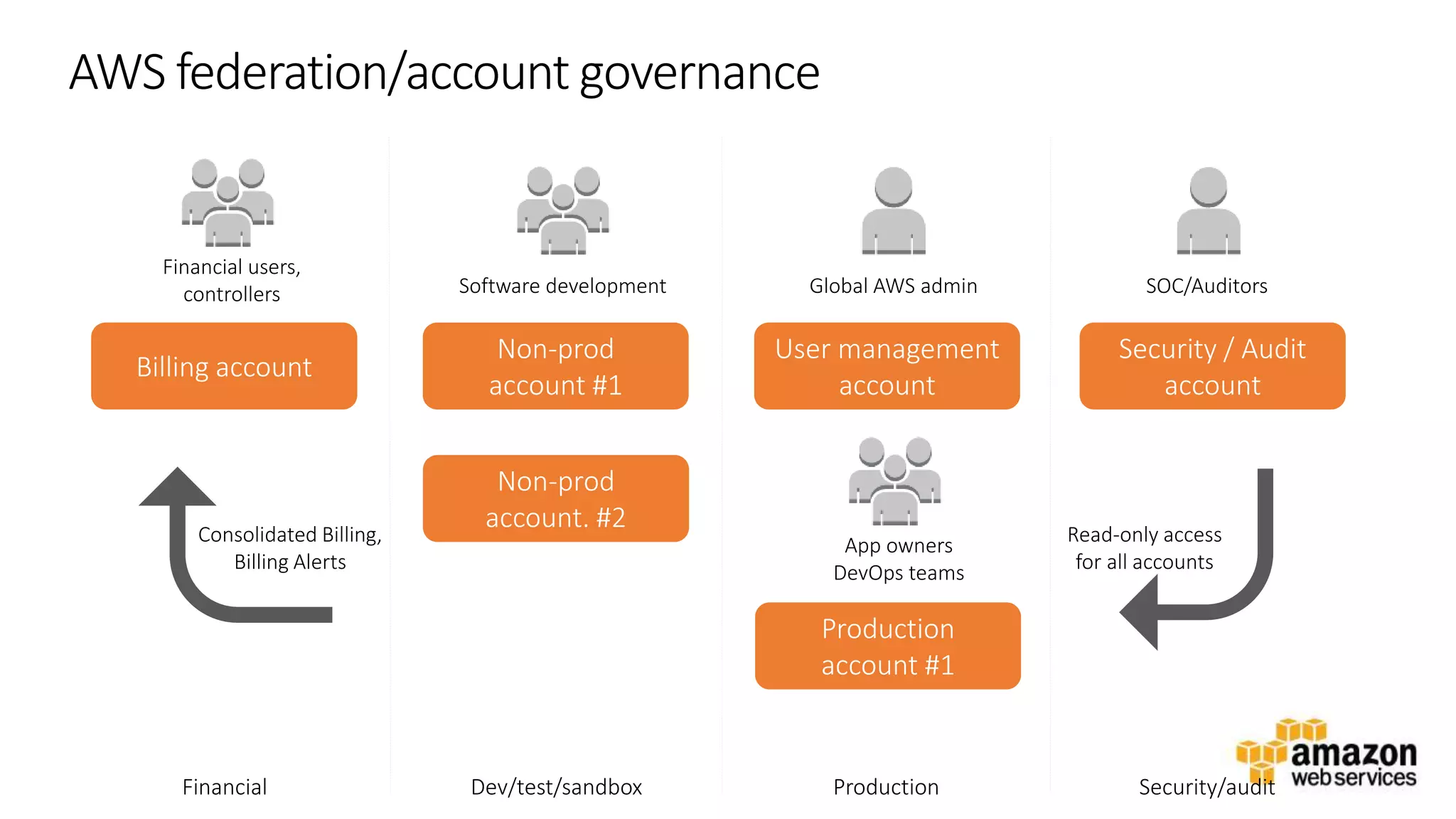
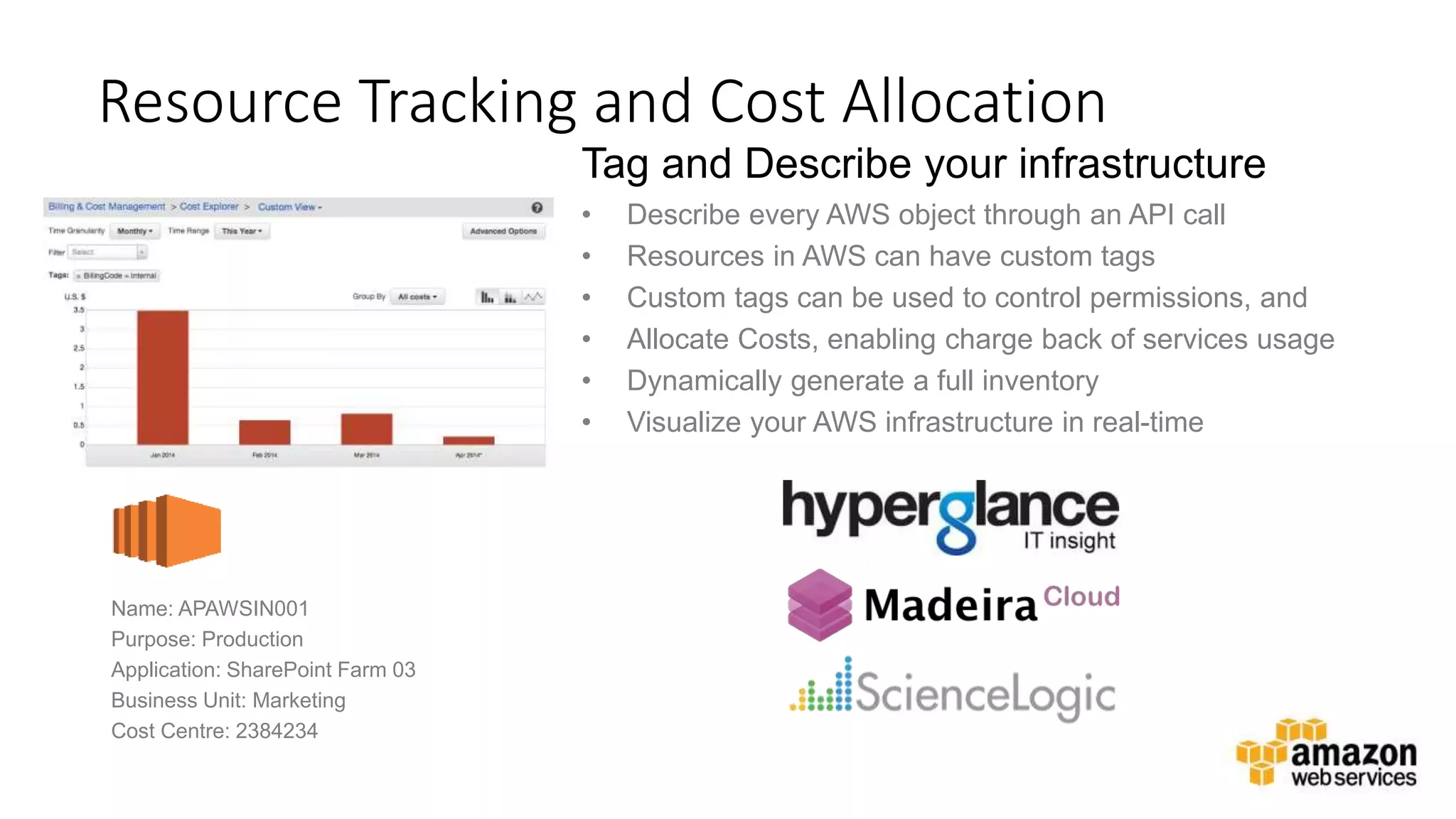
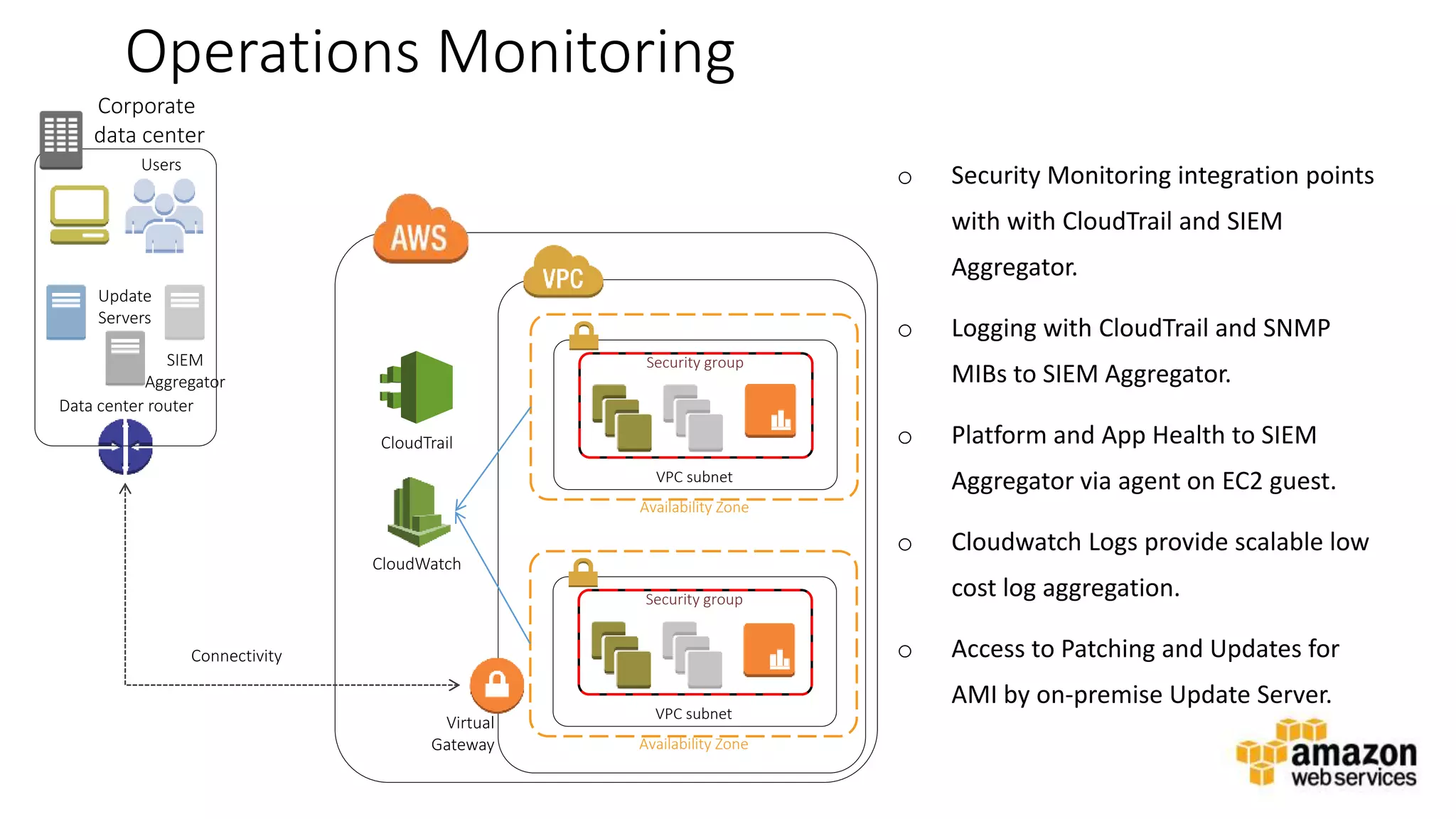
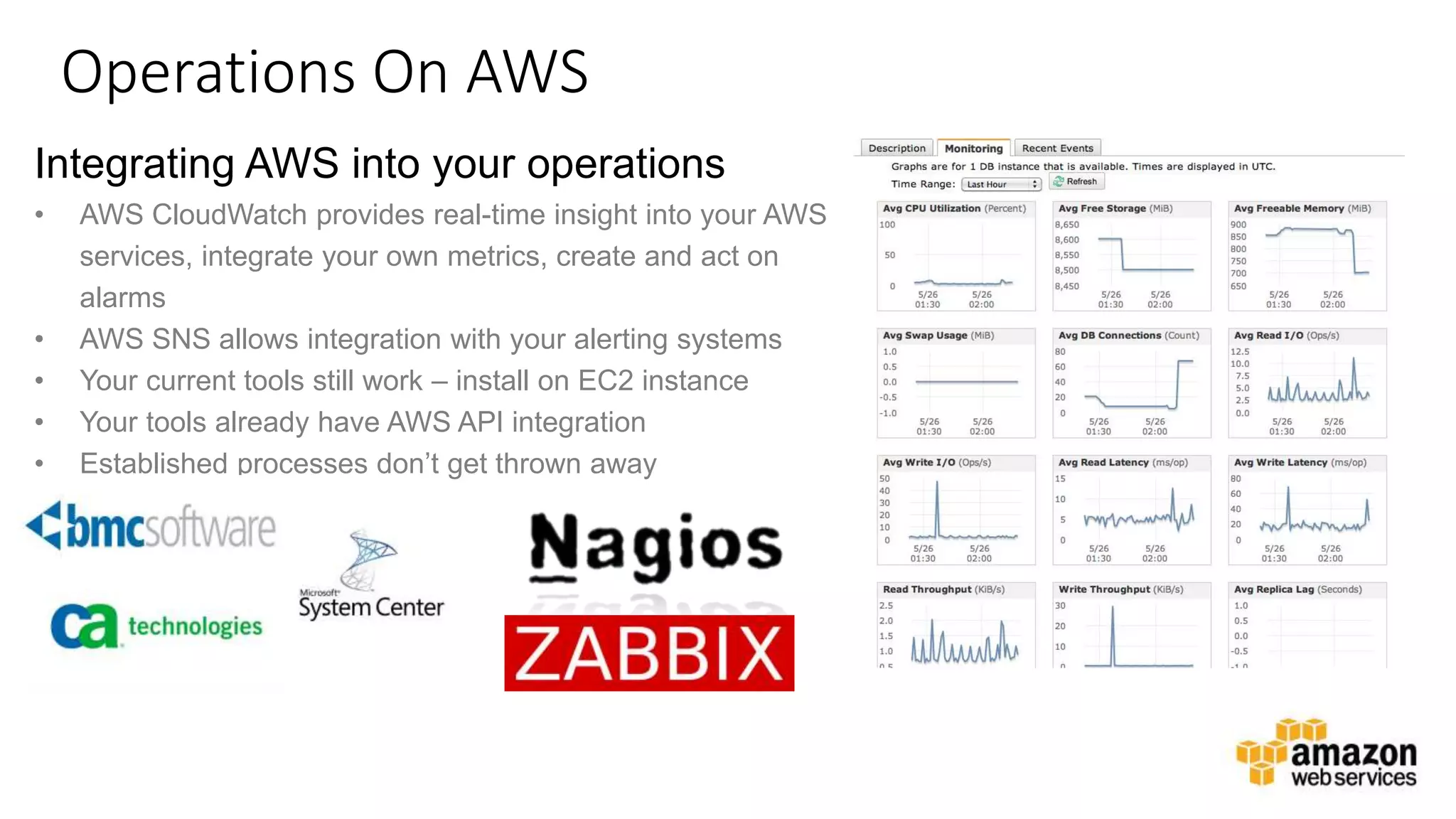
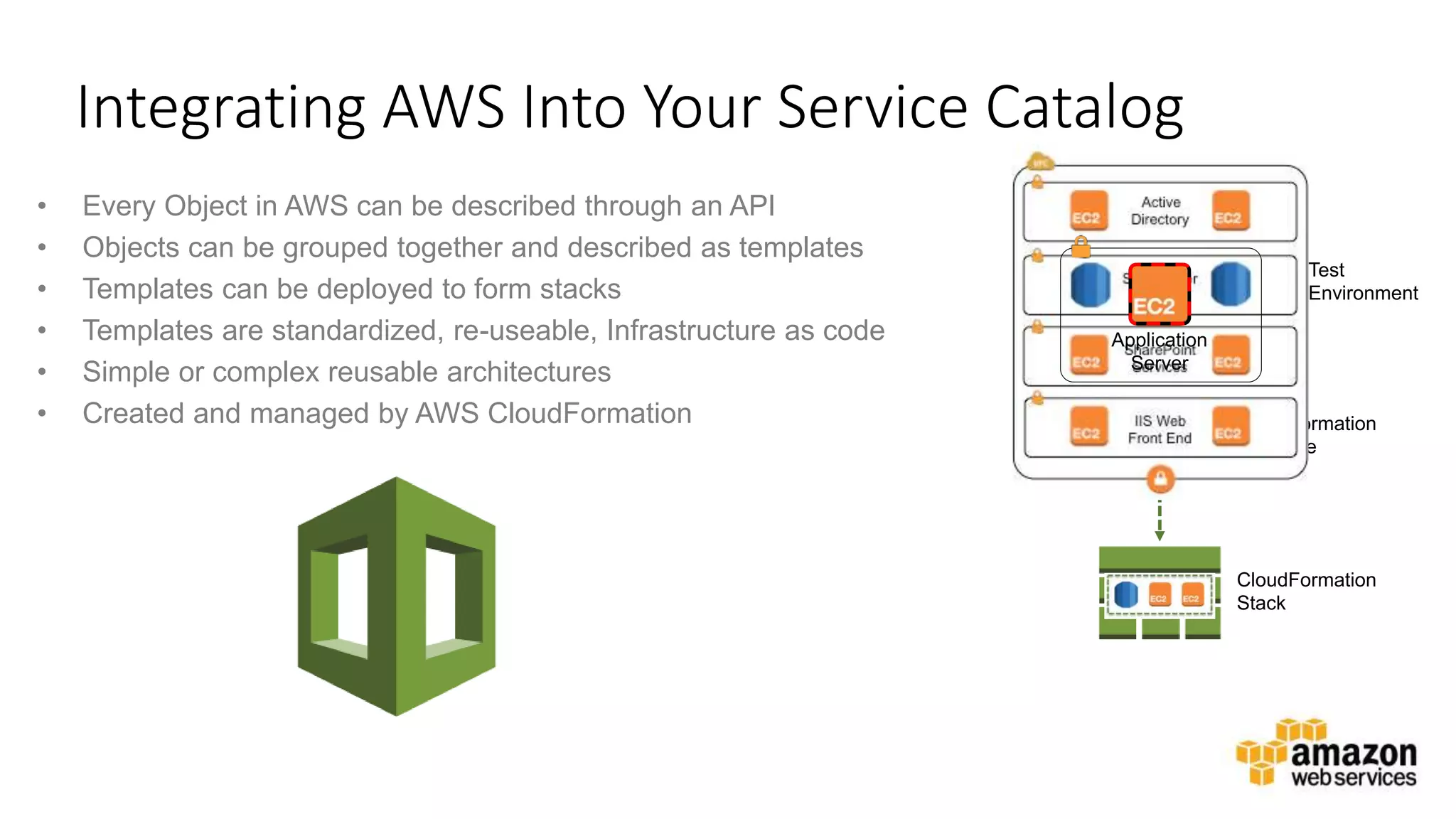
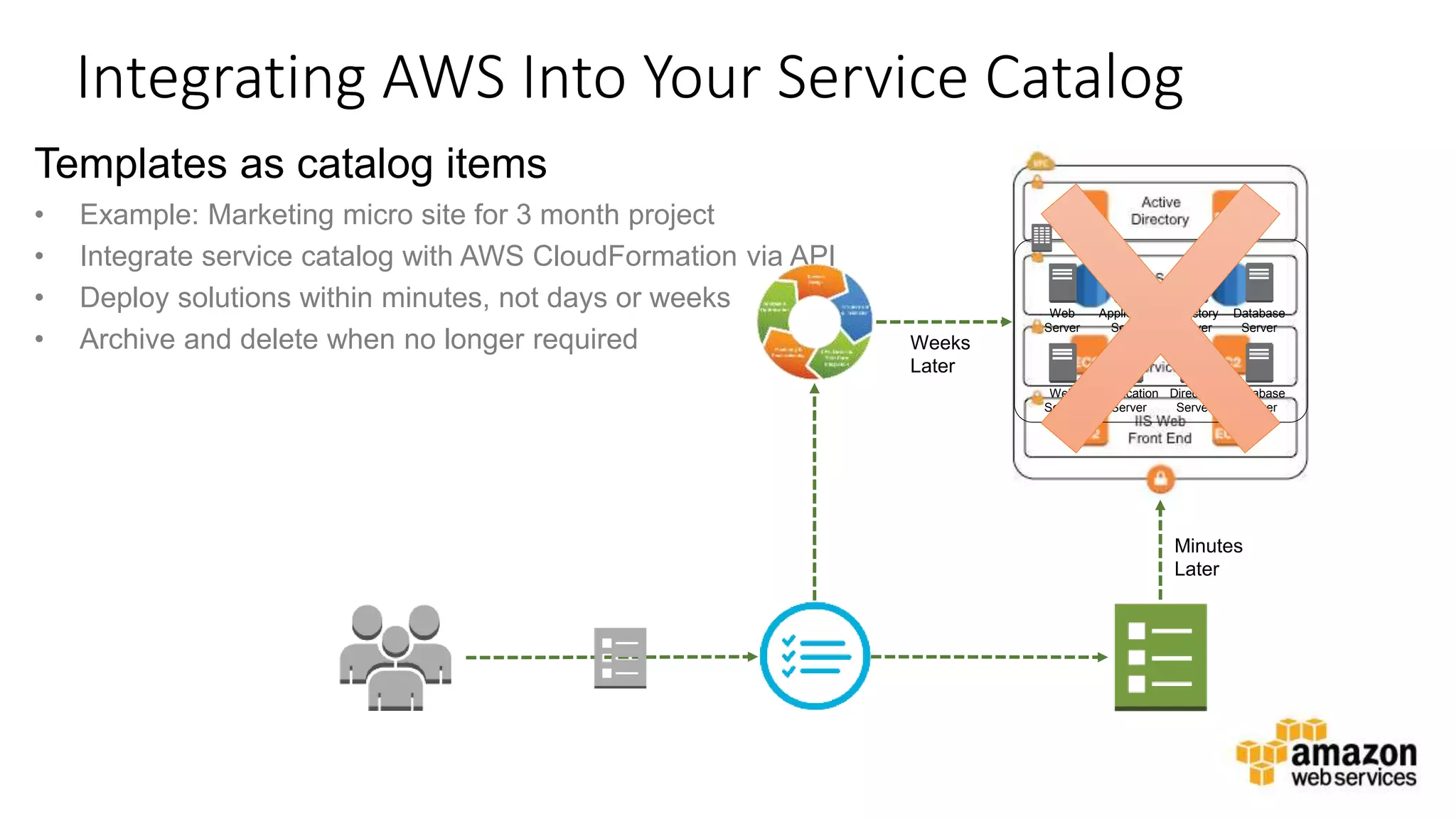
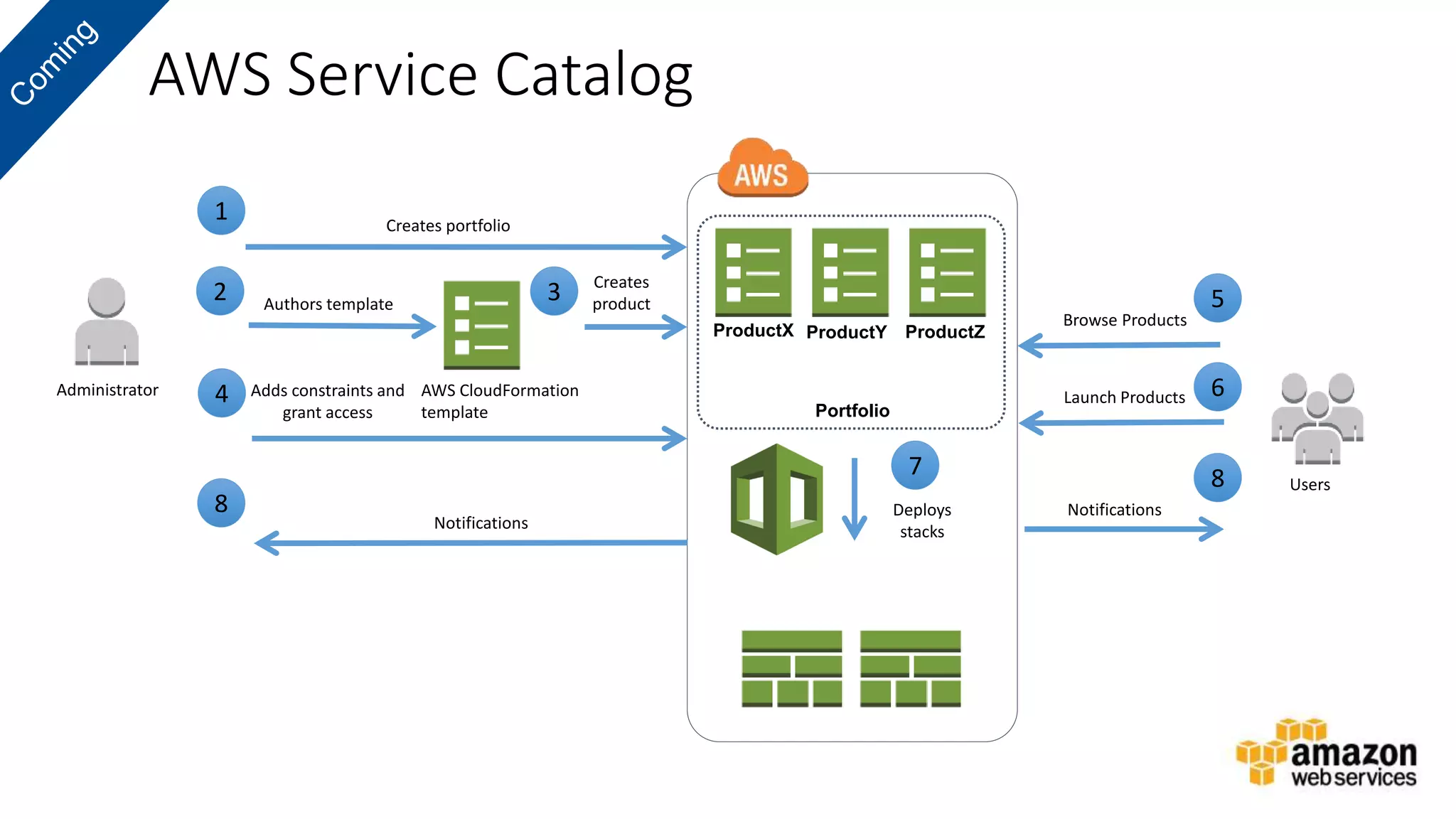
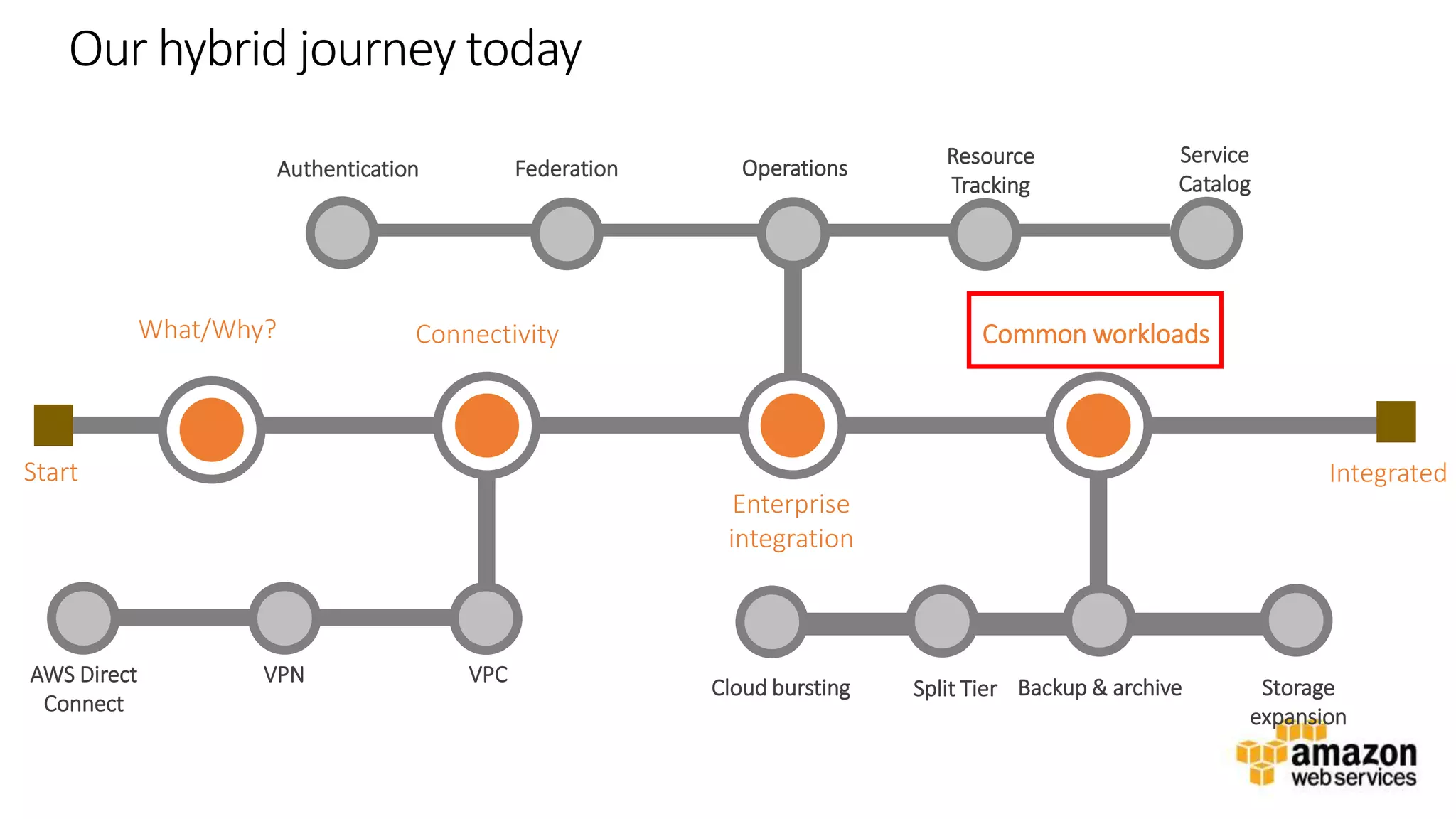
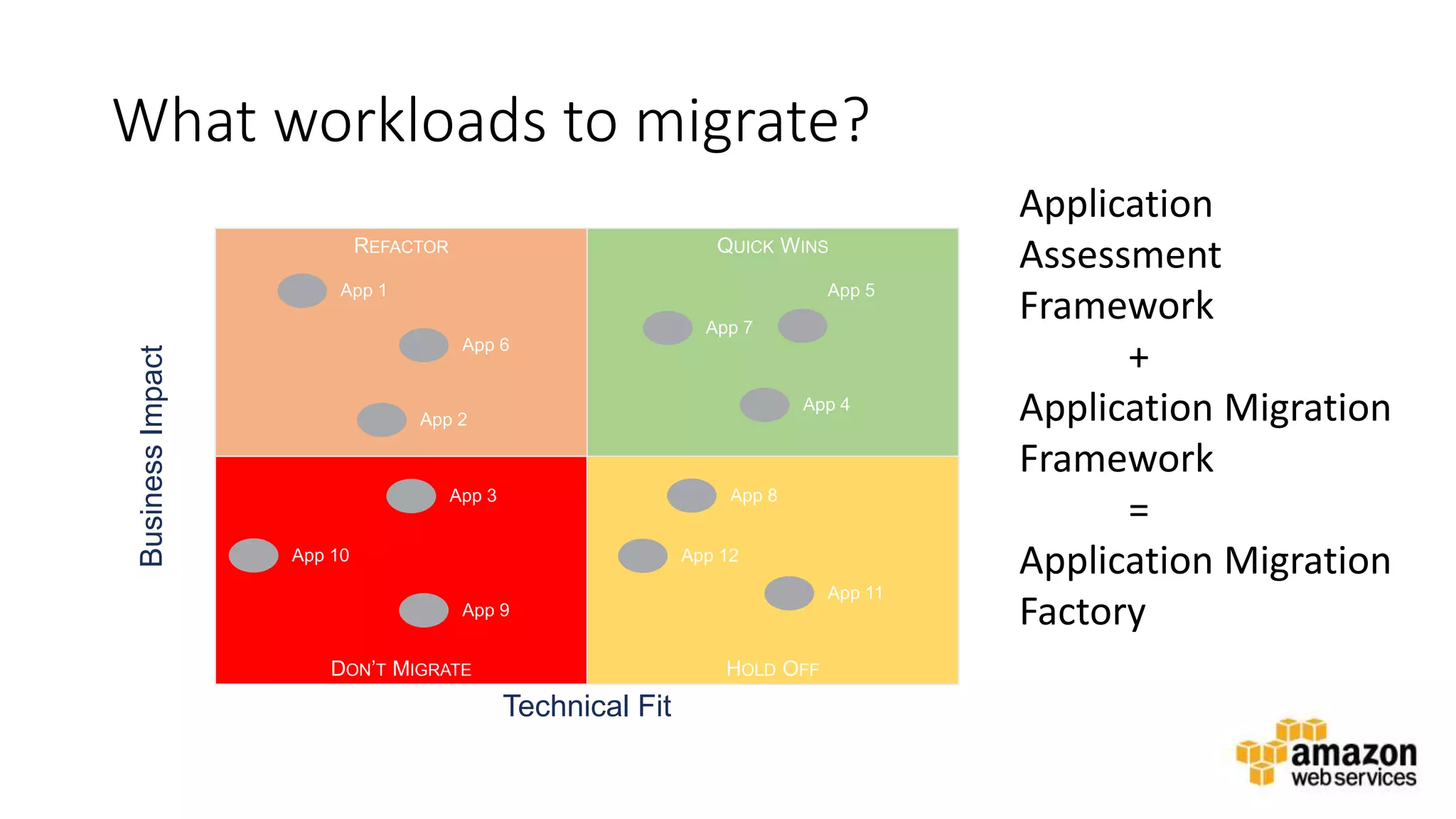
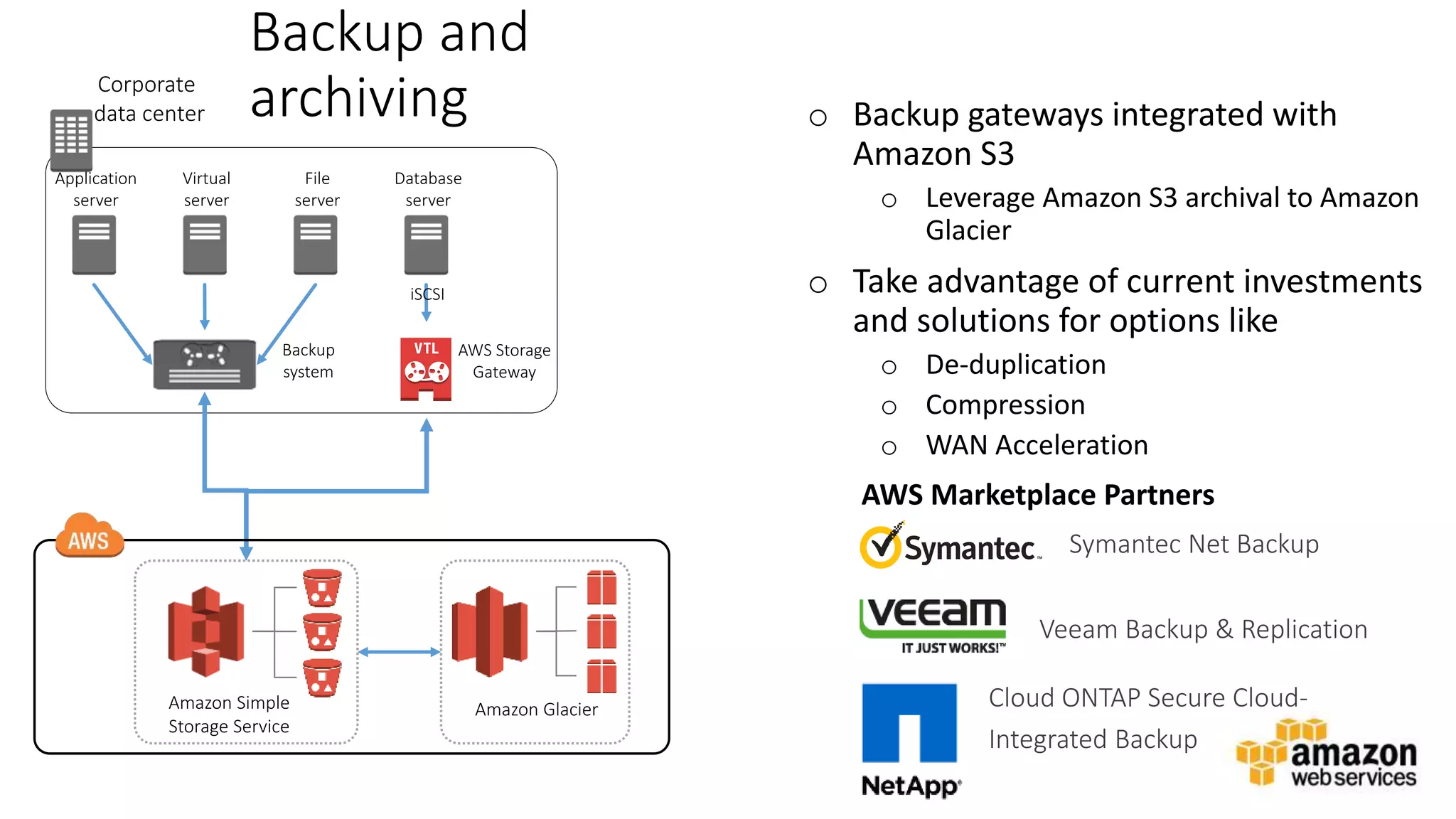
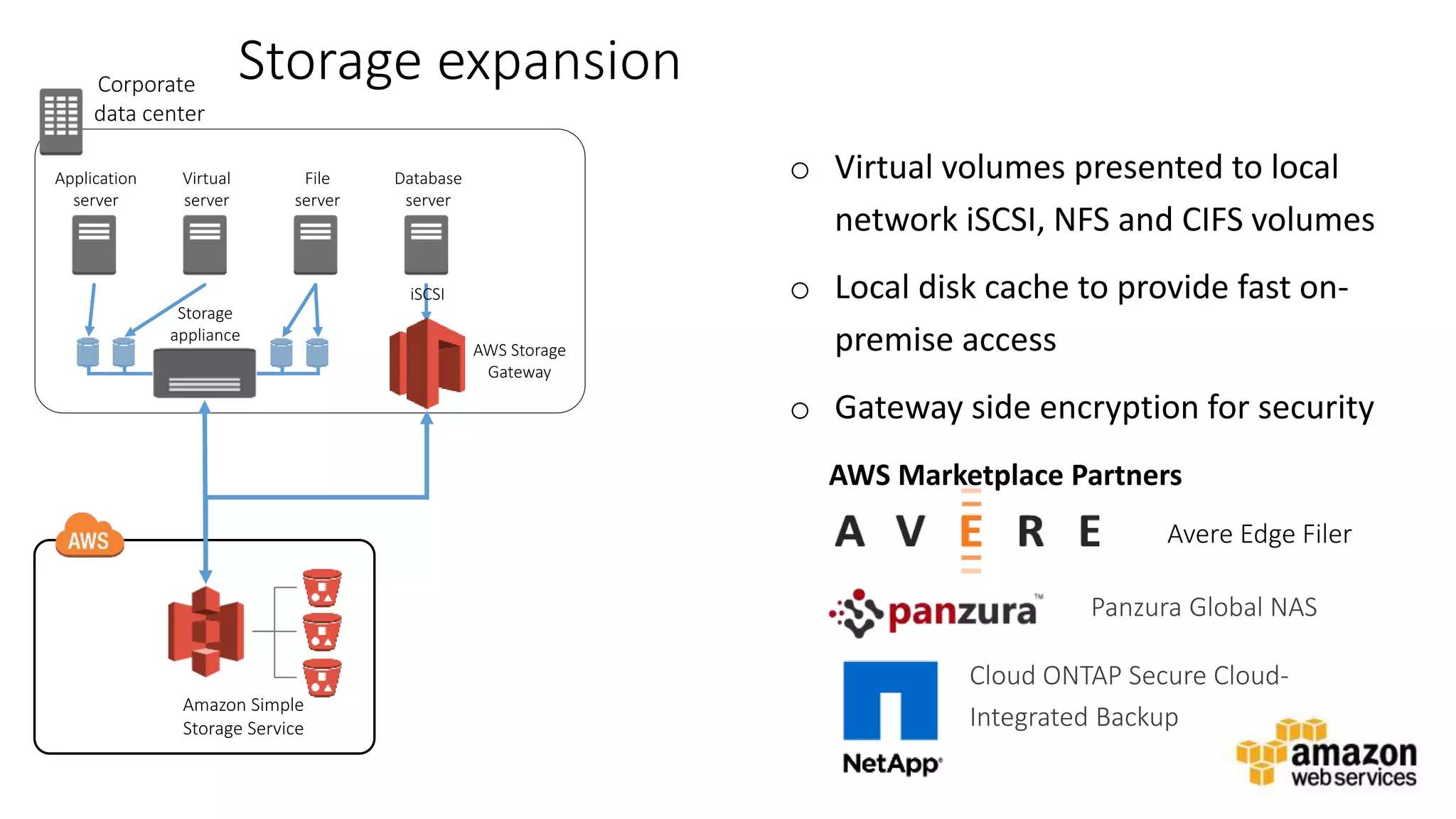
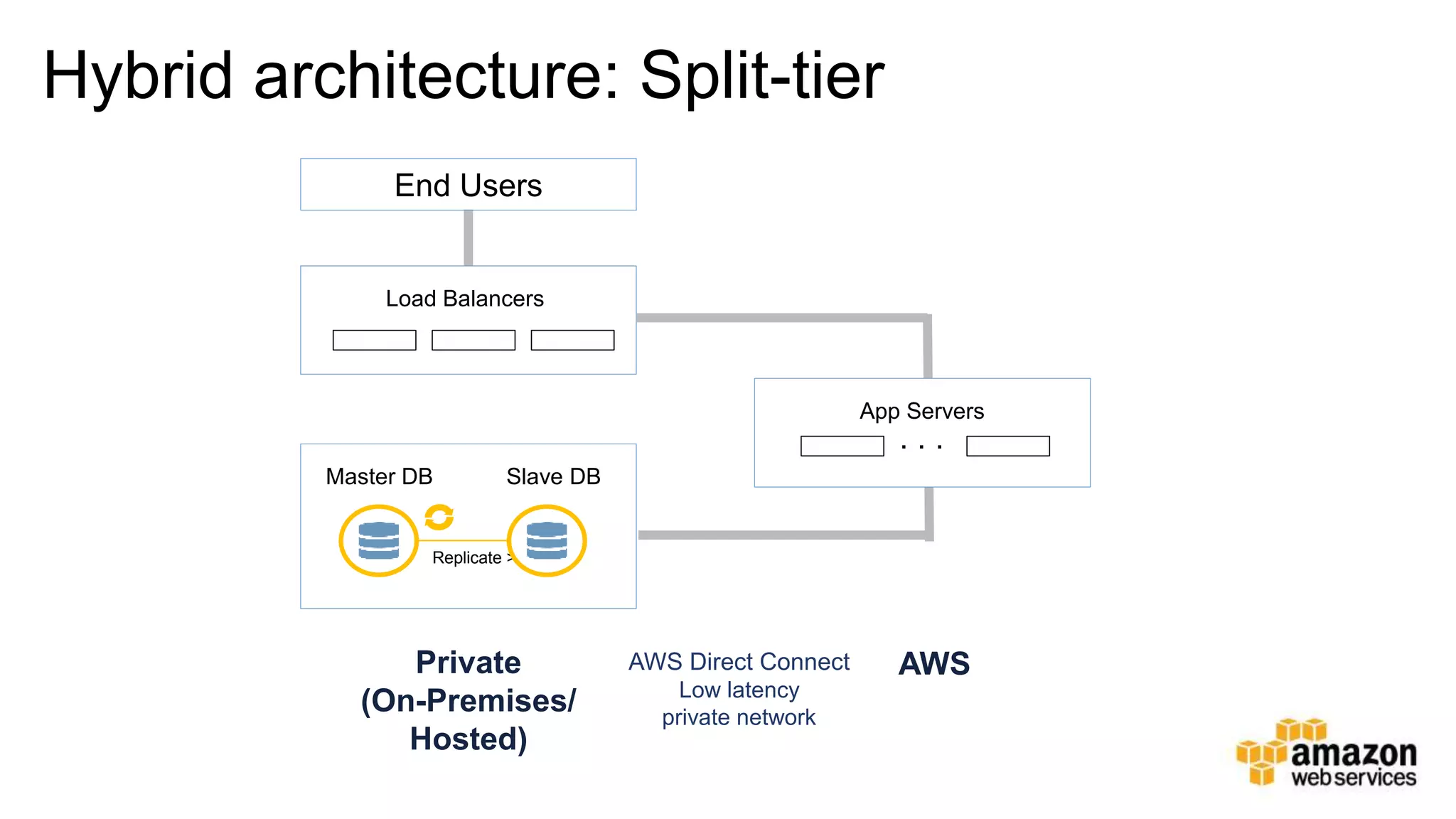
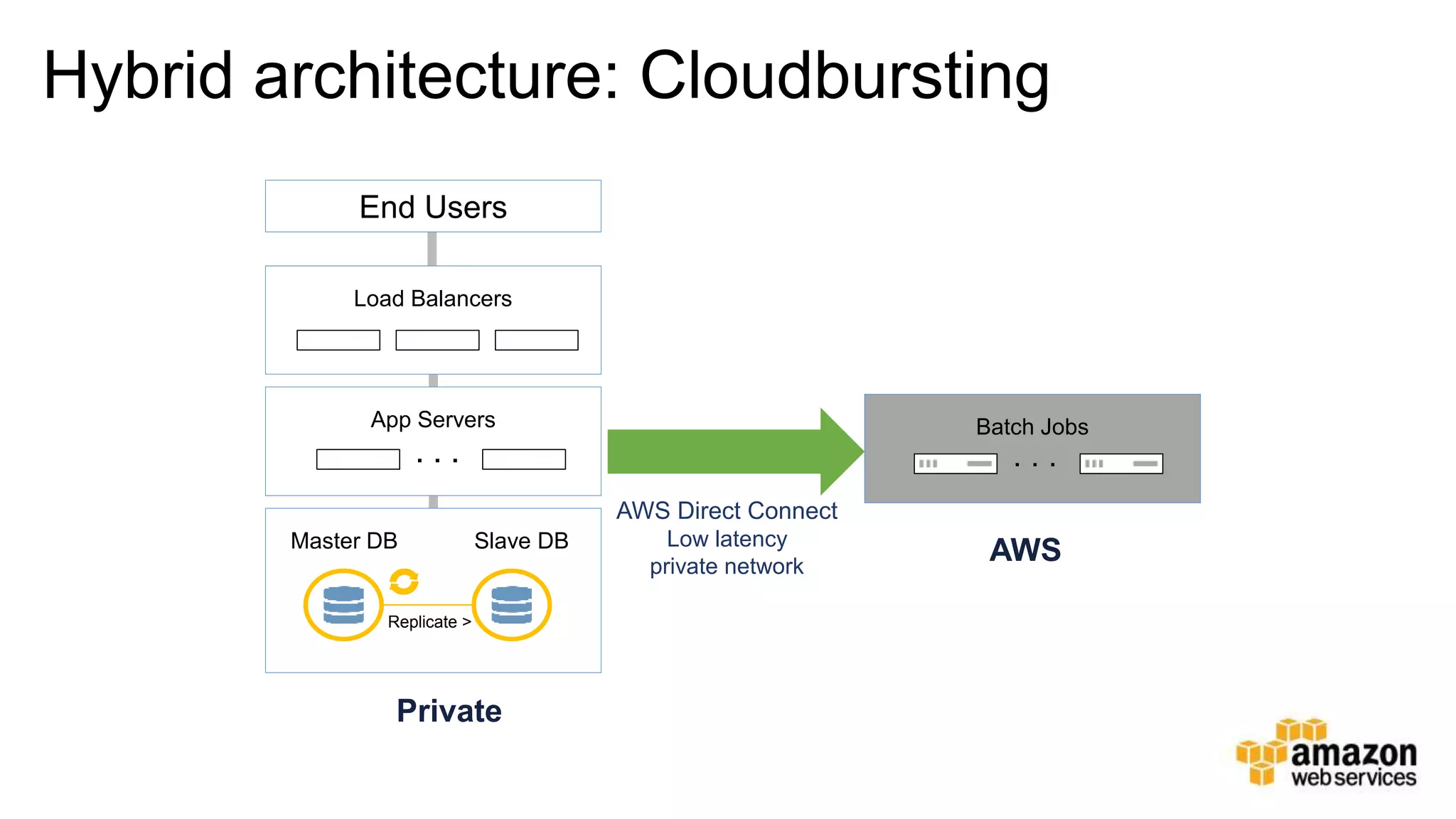
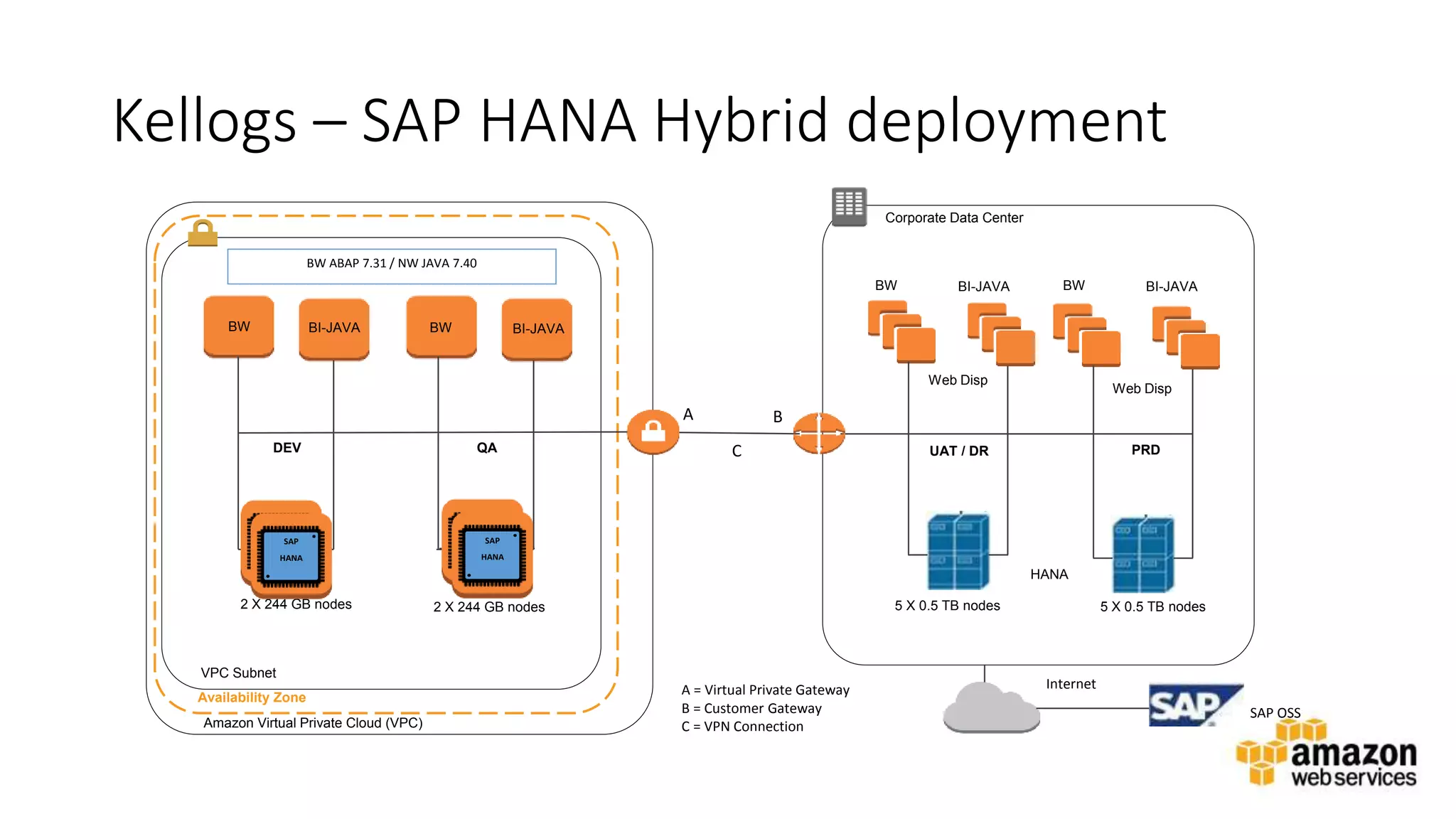
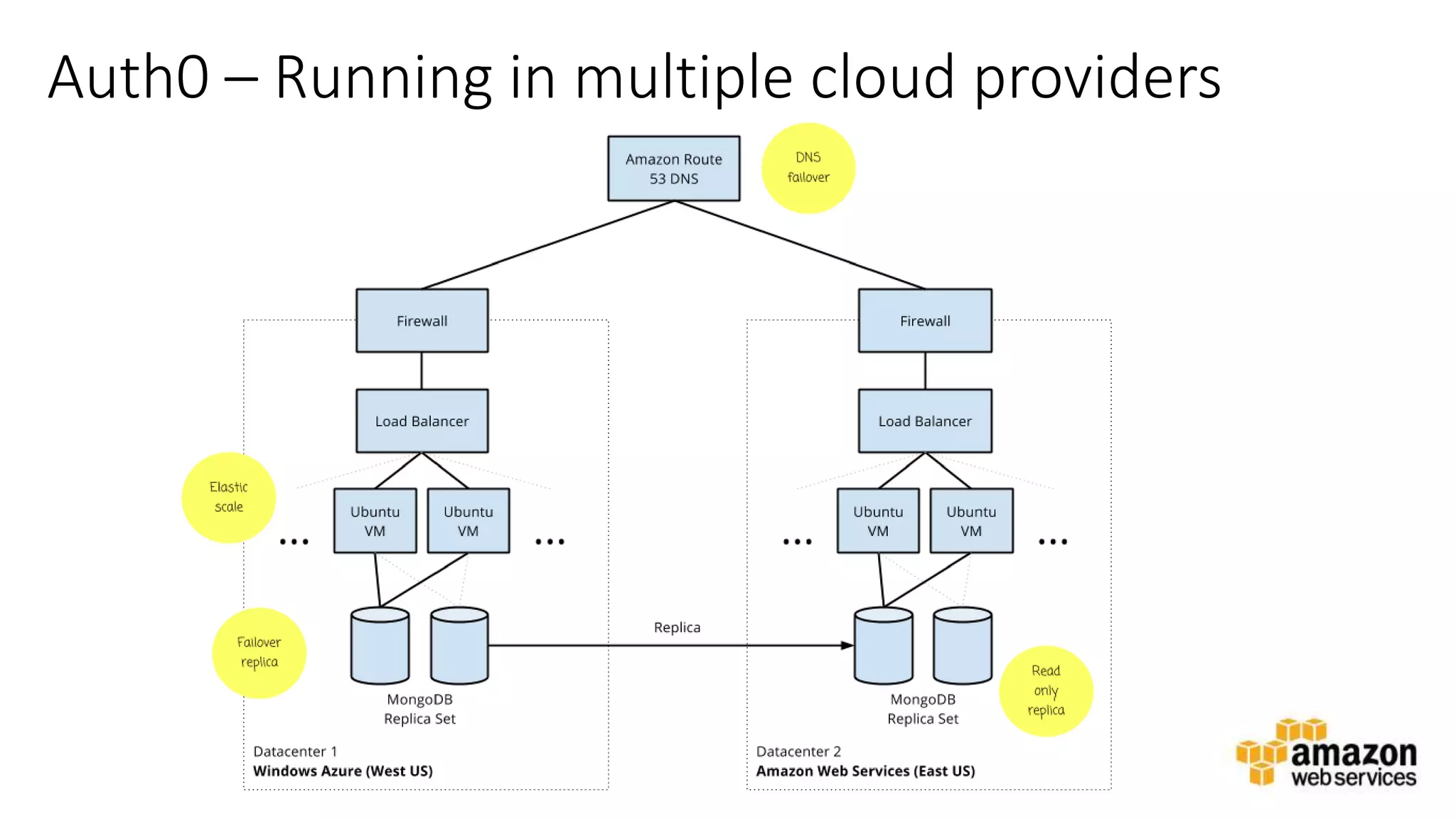
The document discusses strategies for running hybrid IT architectures between on-premises data centers and AWS. It describes common use cases like backup/archival storage, storage expansion, and splitting application tiers between on-prem and cloud. The document also discusses best practices for connectivity options like VPC VPN and AWS Direct Connect, identity federation, operations monitoring, and integrating AWS services into existing processes. Overall, the document provides an overview of approaches for building hybrid architectures that span both traditional IT and cloud-based infrastructure.