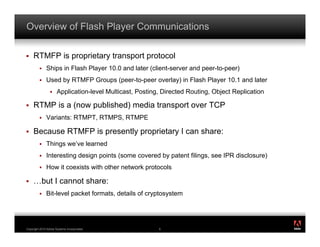
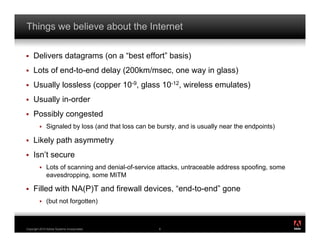
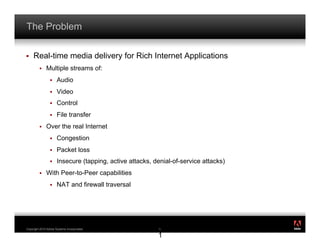
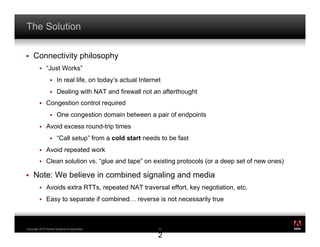
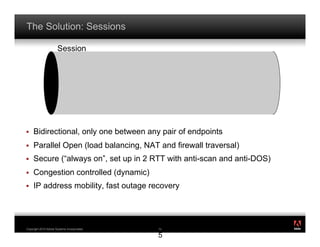
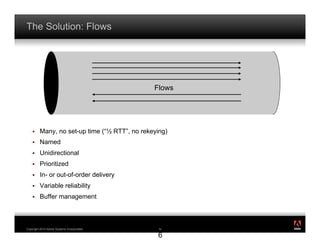
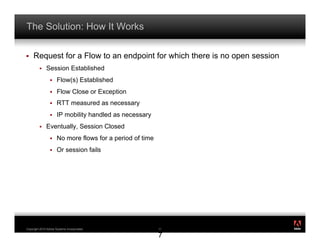
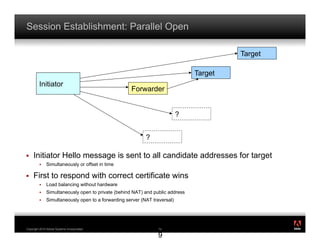
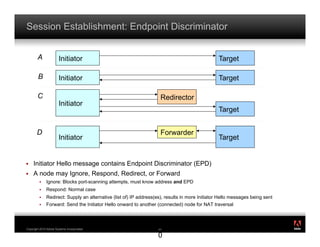
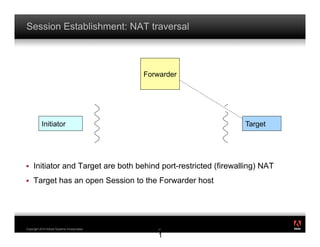
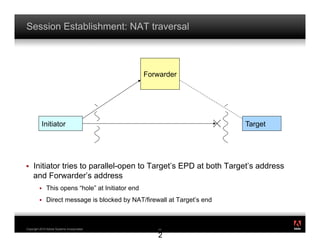
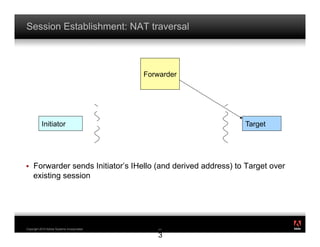
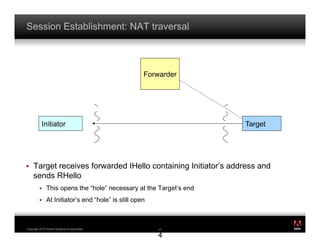
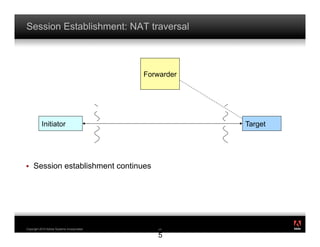
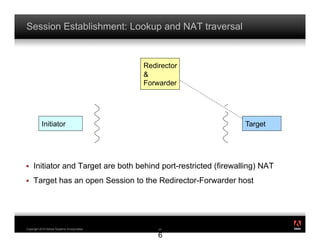
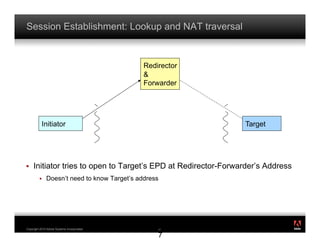
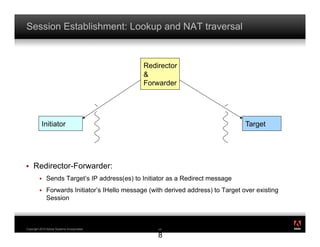
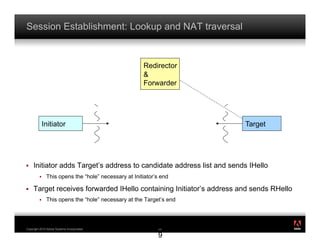
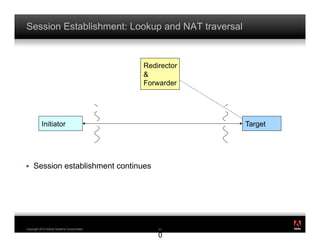
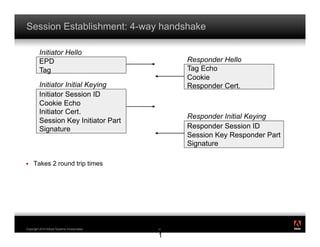
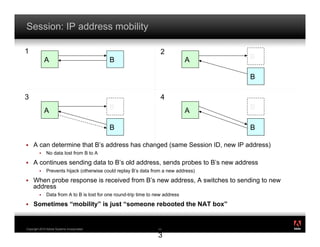
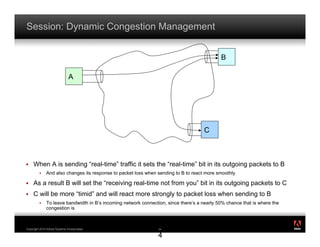
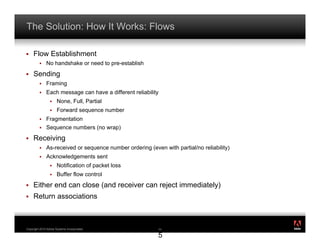
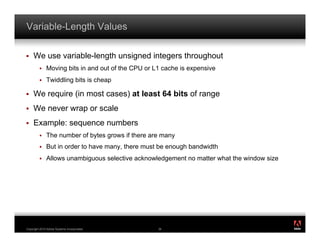
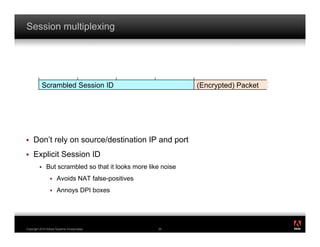
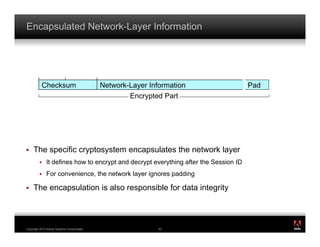
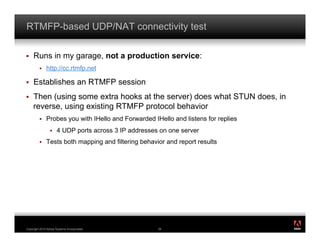
The document discusses RTMFP, a proprietary transport protocol developed by Adobe. It was designed to securely deliver media flows over the internet in a more efficient manner than existing protocols. RTMFP establishes sessions between endpoints to allow for the transfer of multiple unidirectional flows with low latency. It uses techniques like parallel opens and NAT traversal to establish sessions quickly while being secure and congestion controlled.