Embed presentation
Downloaded 80 times





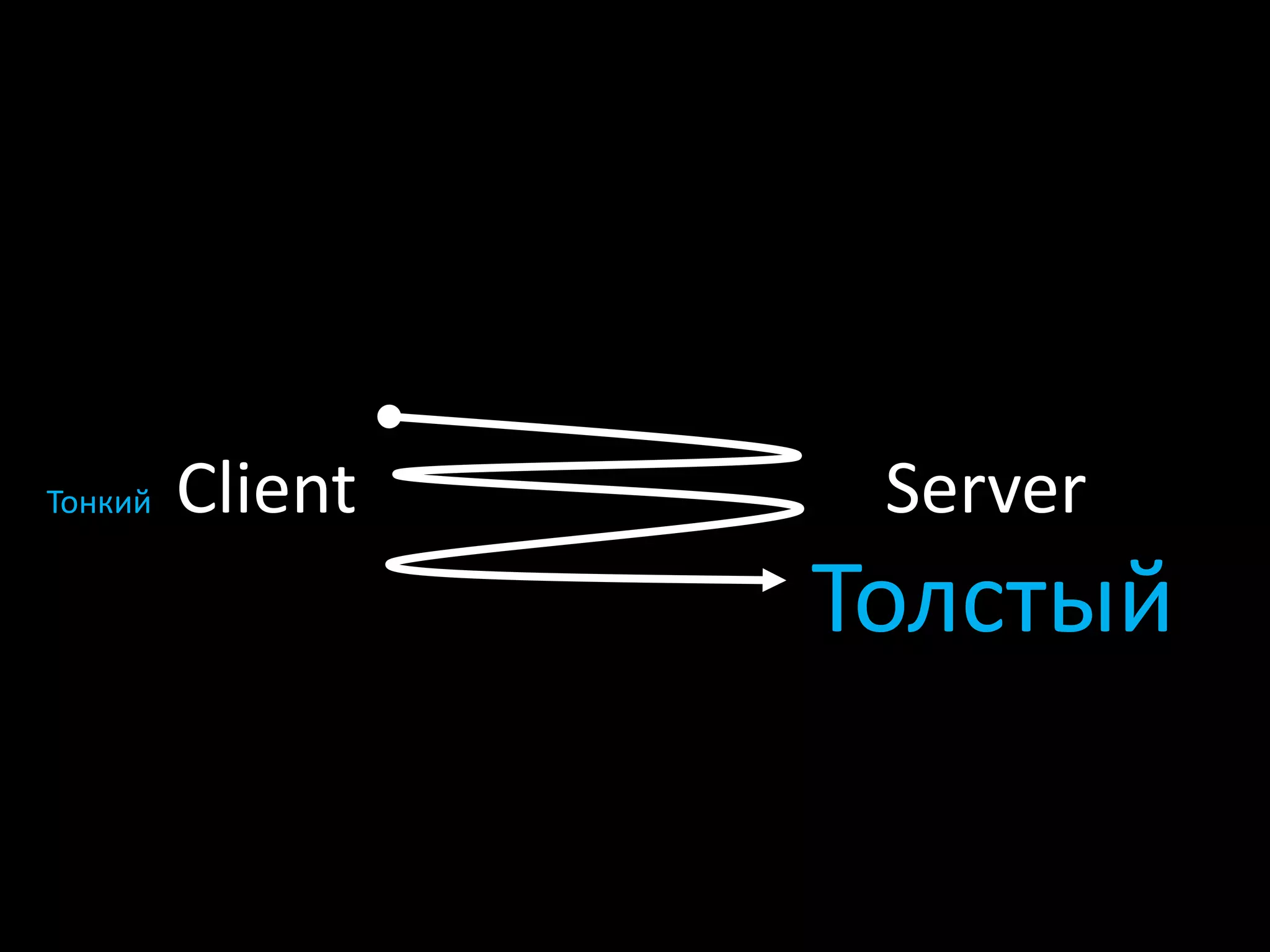













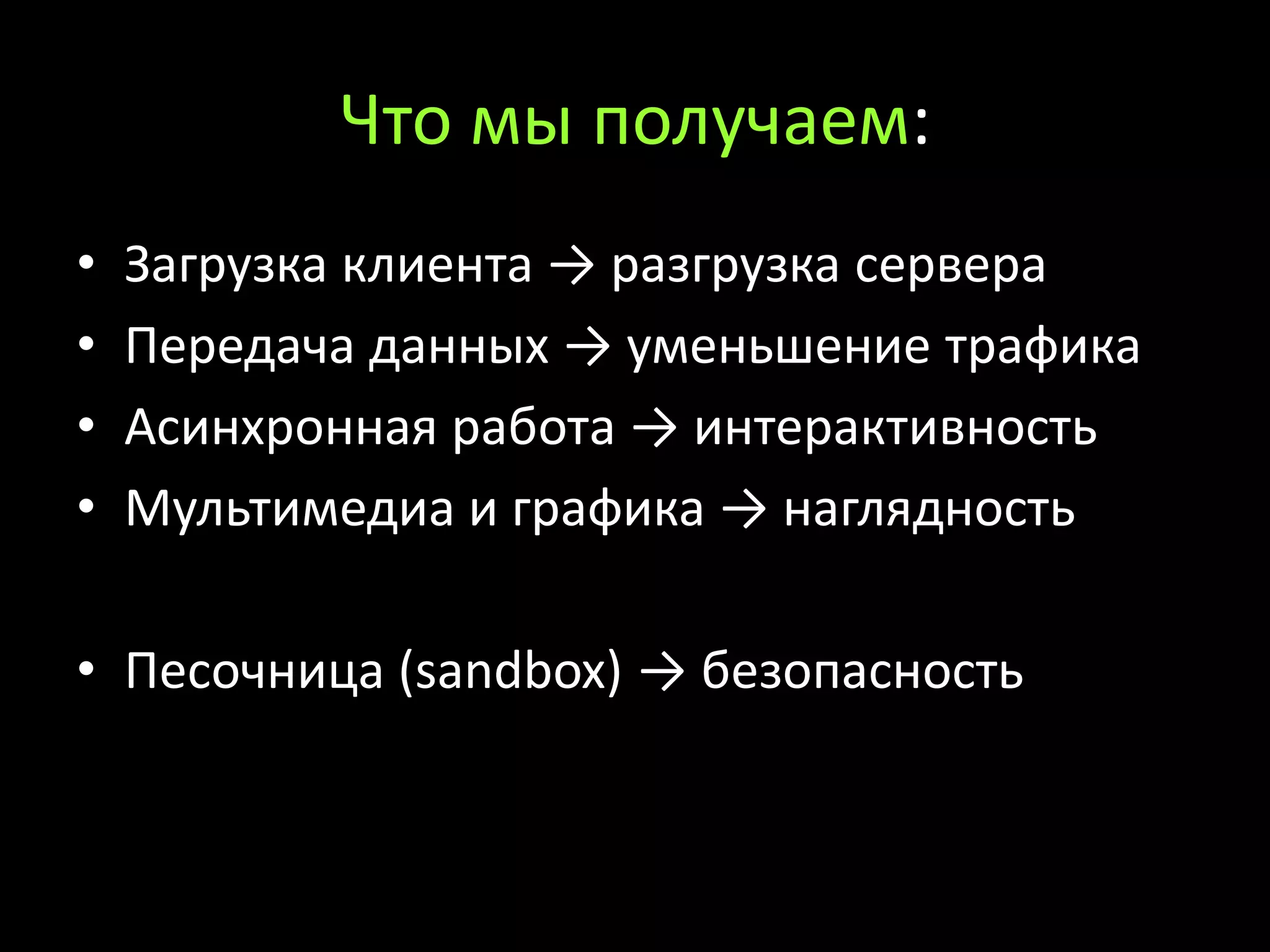
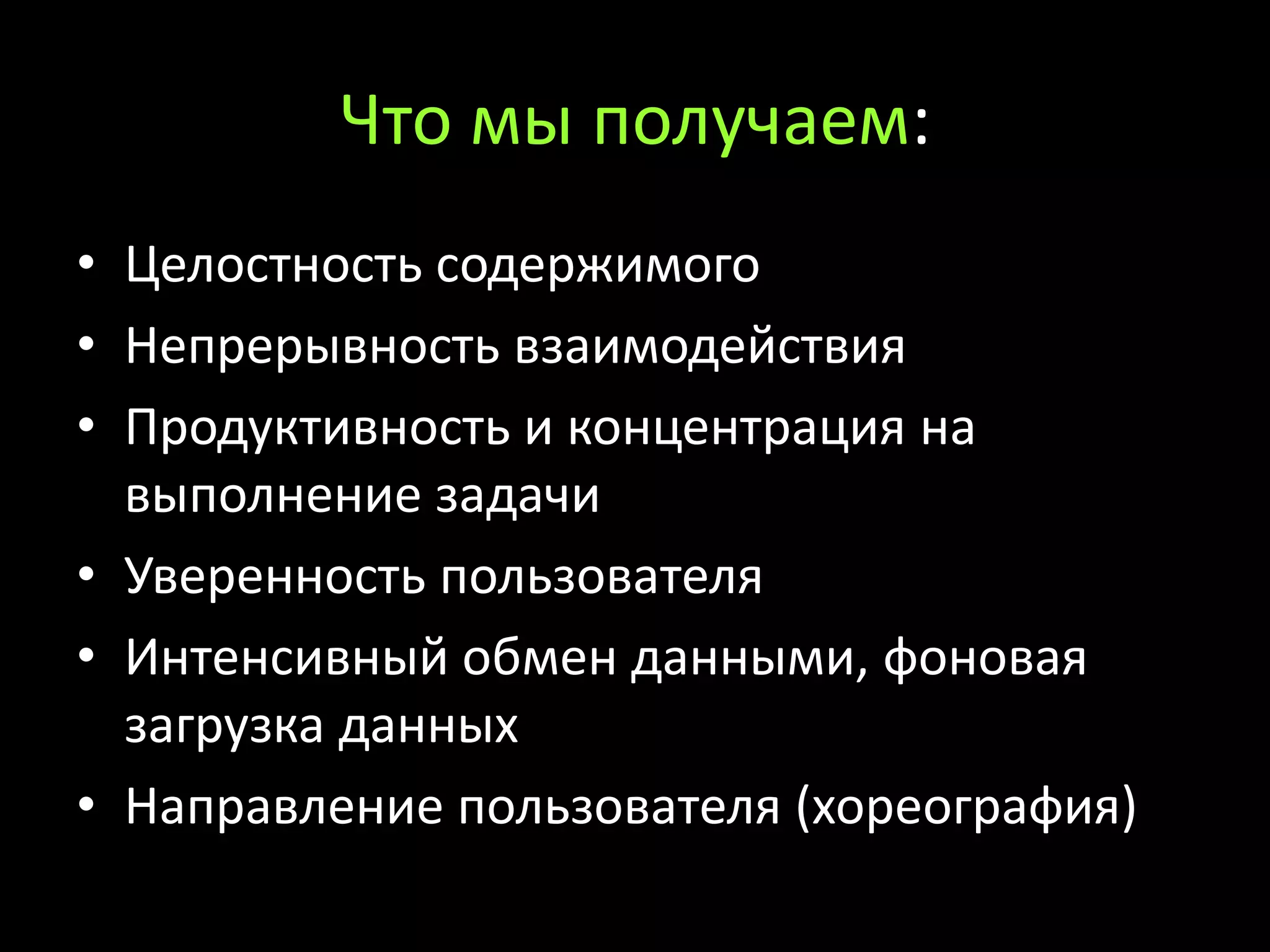









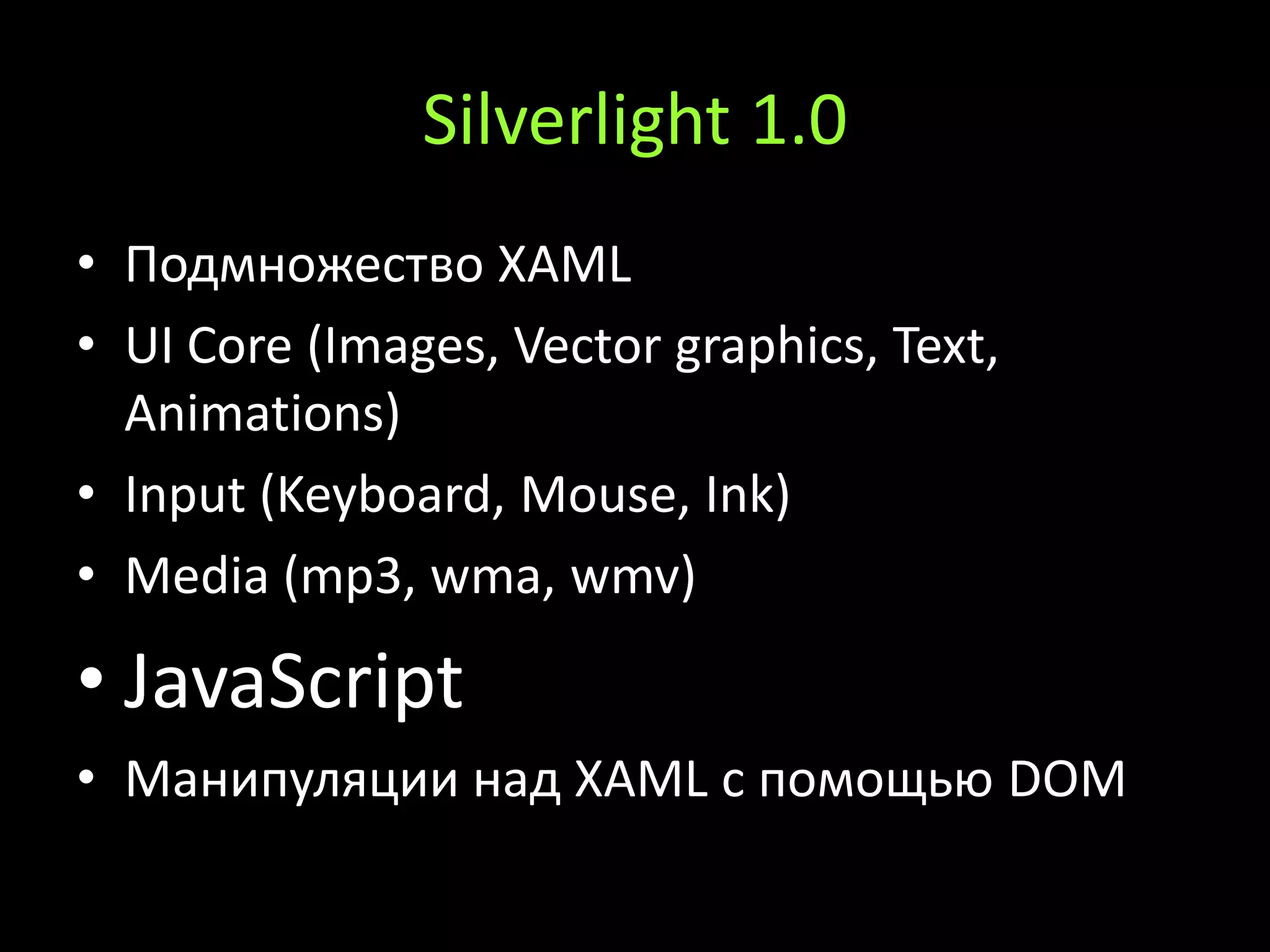







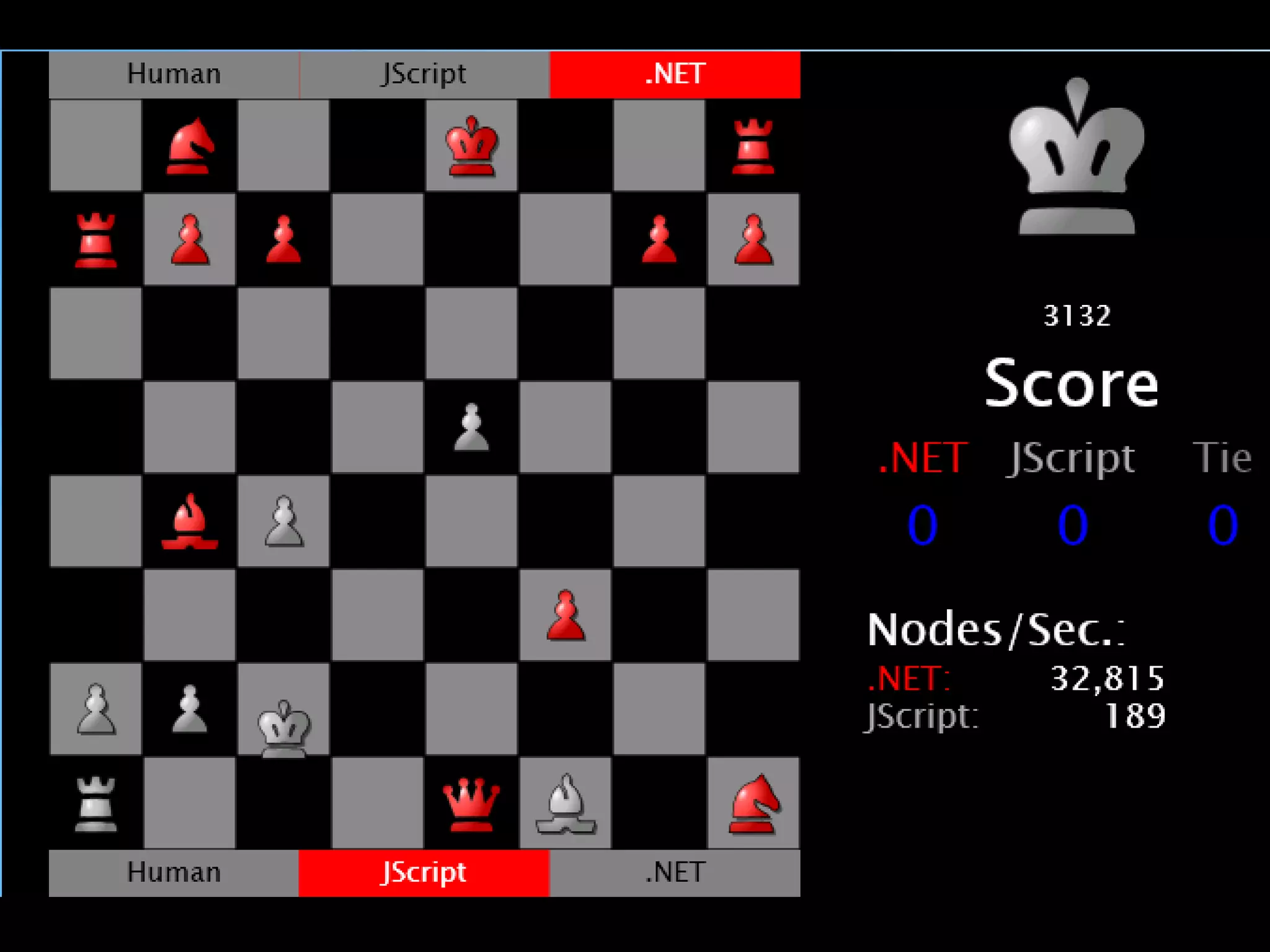


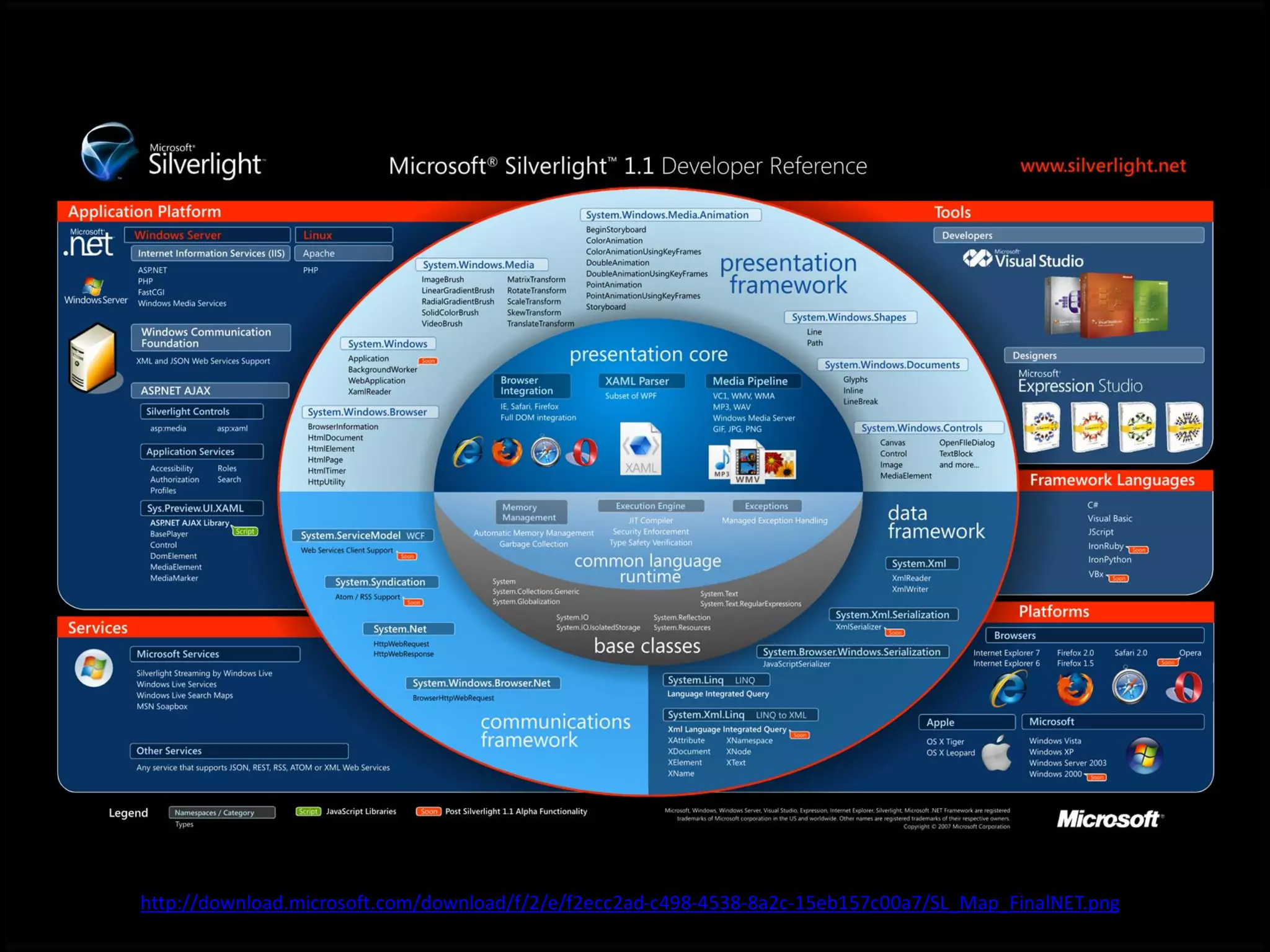




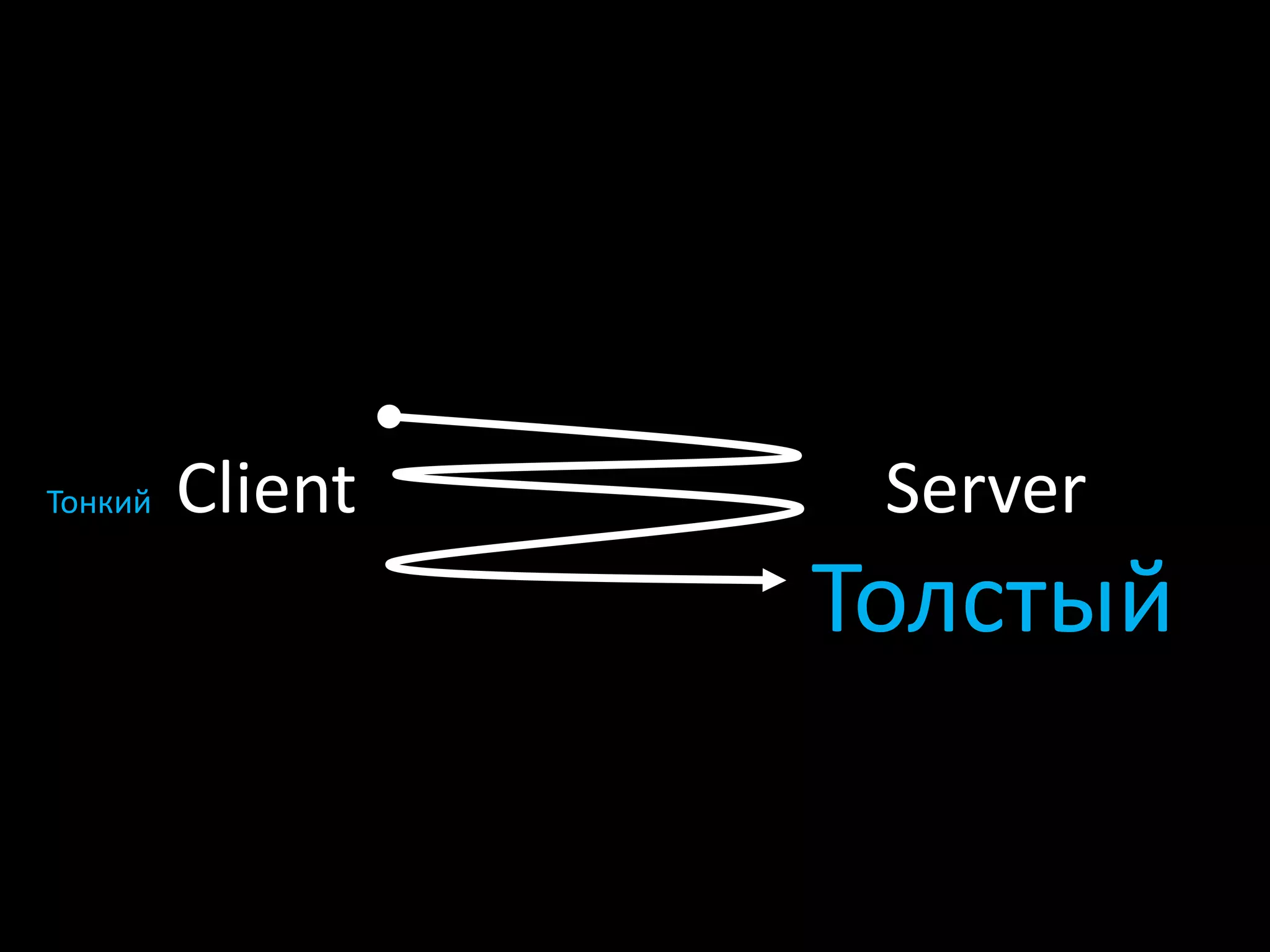
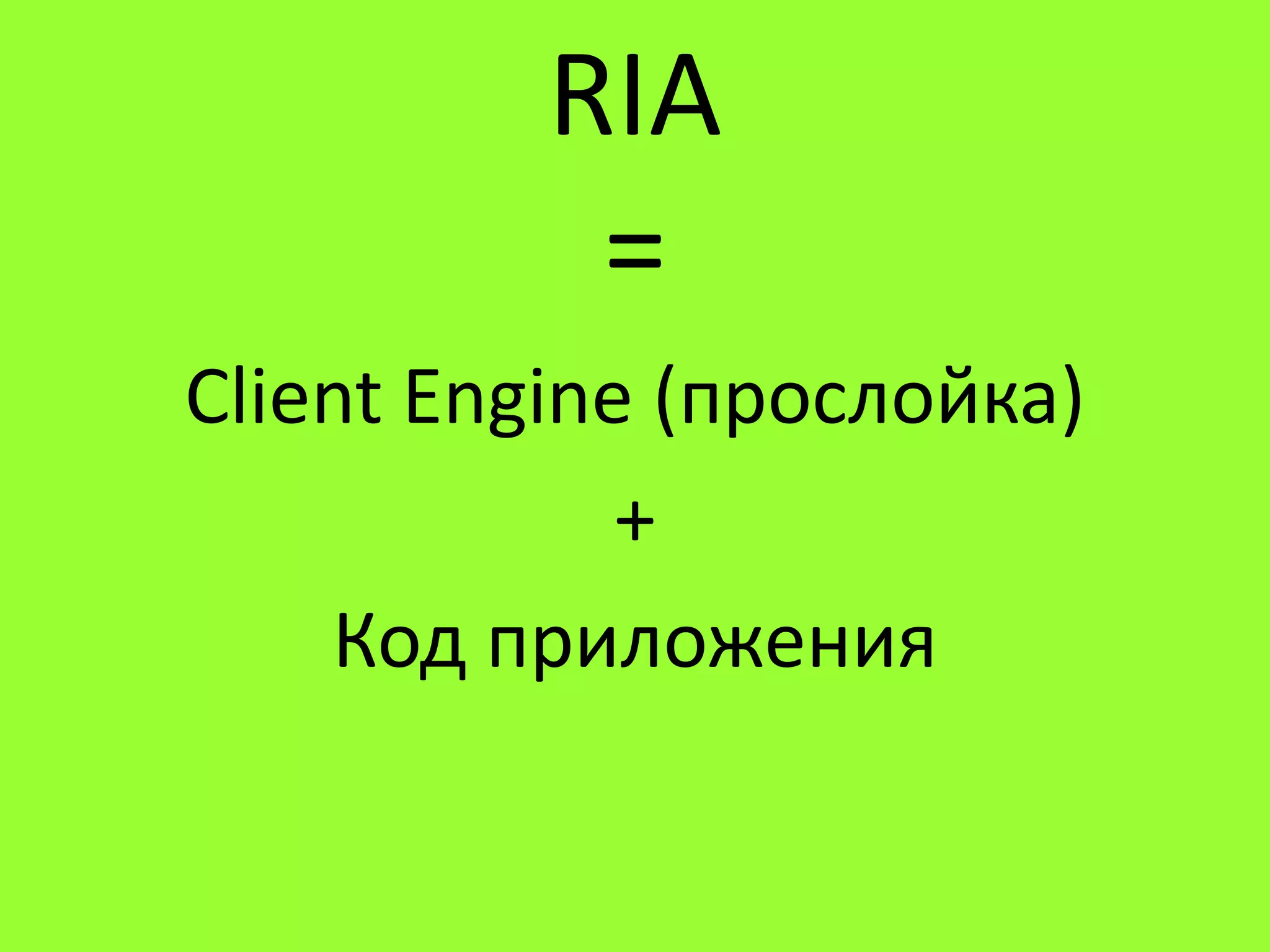
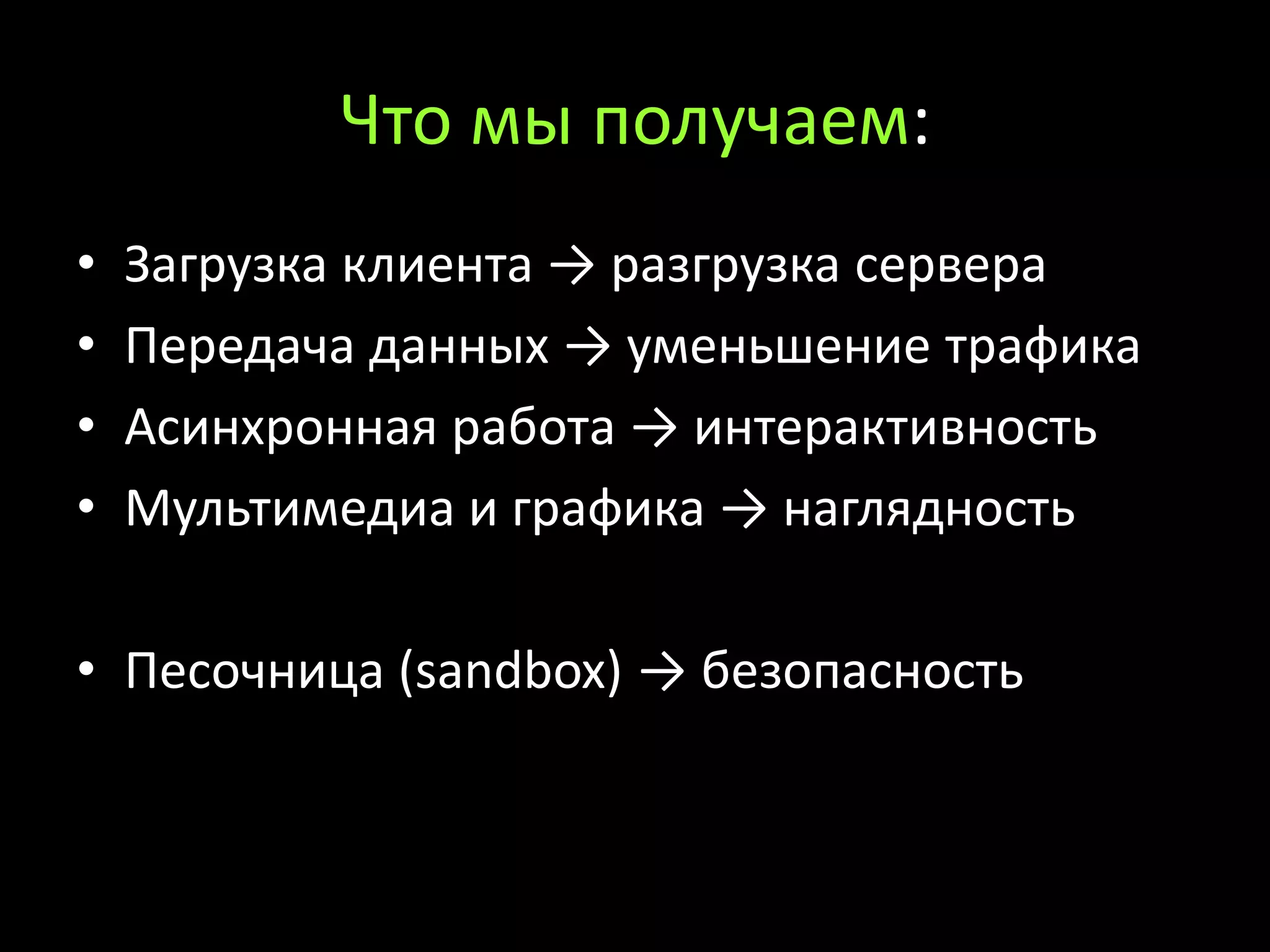
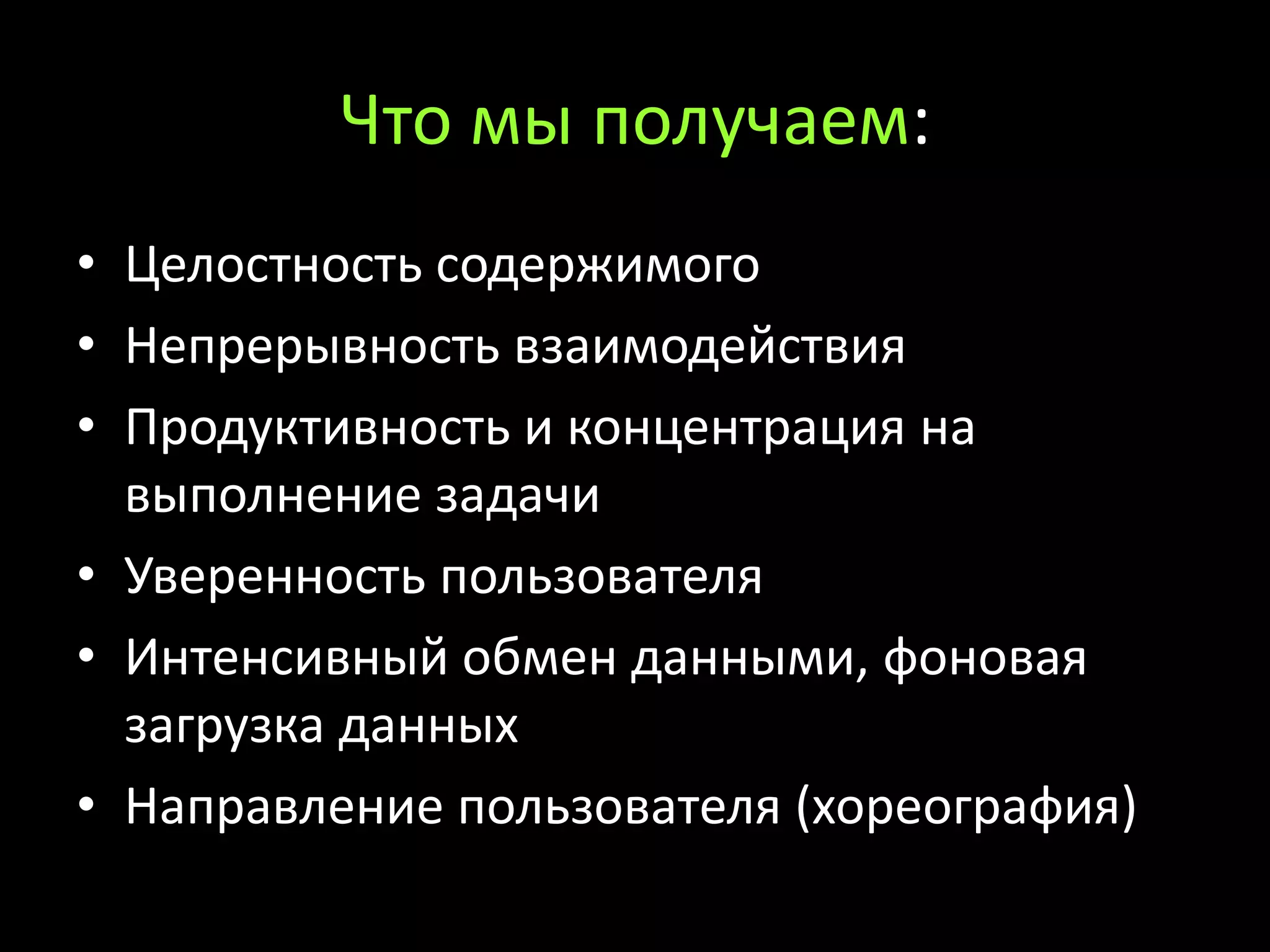
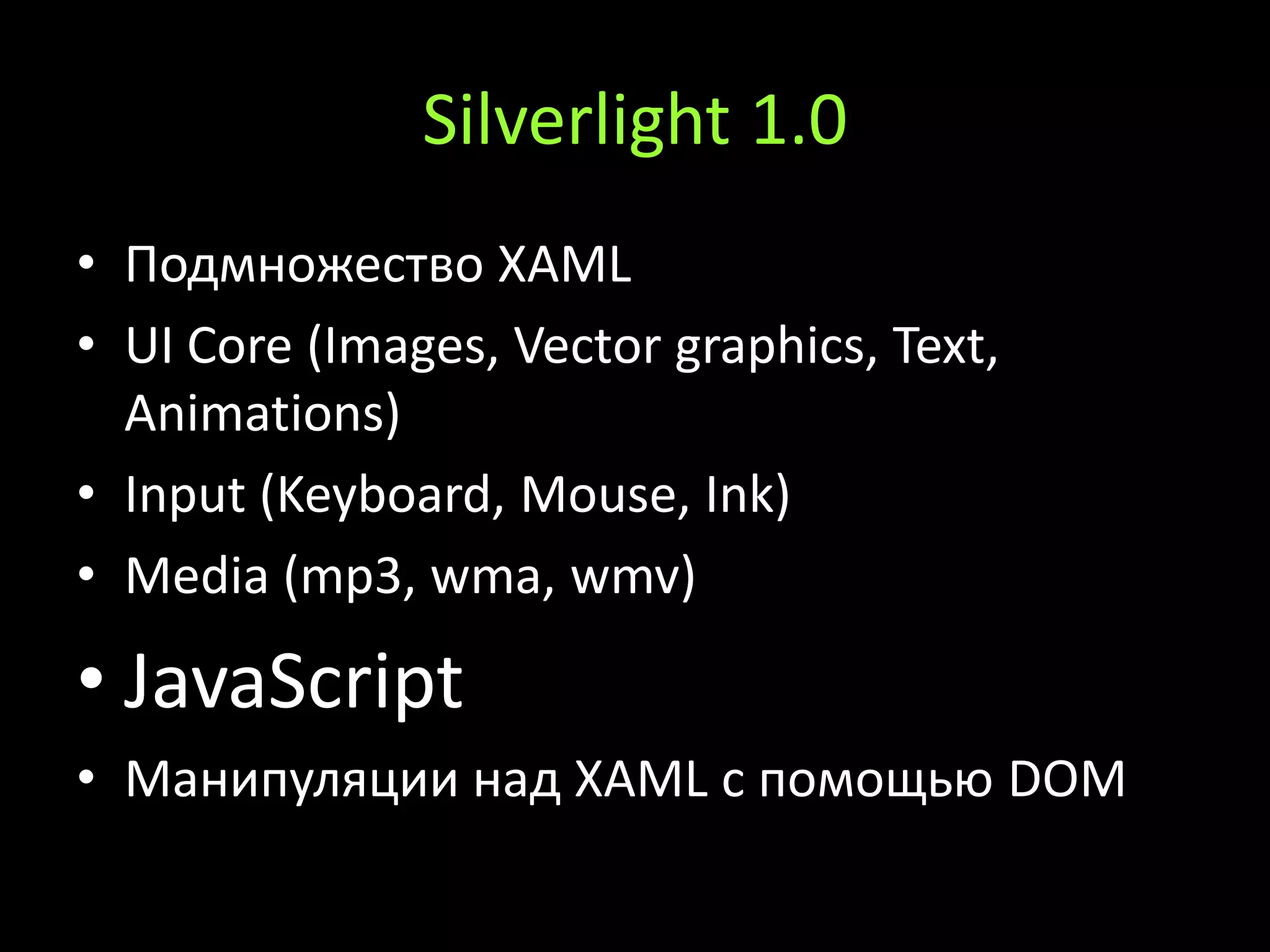
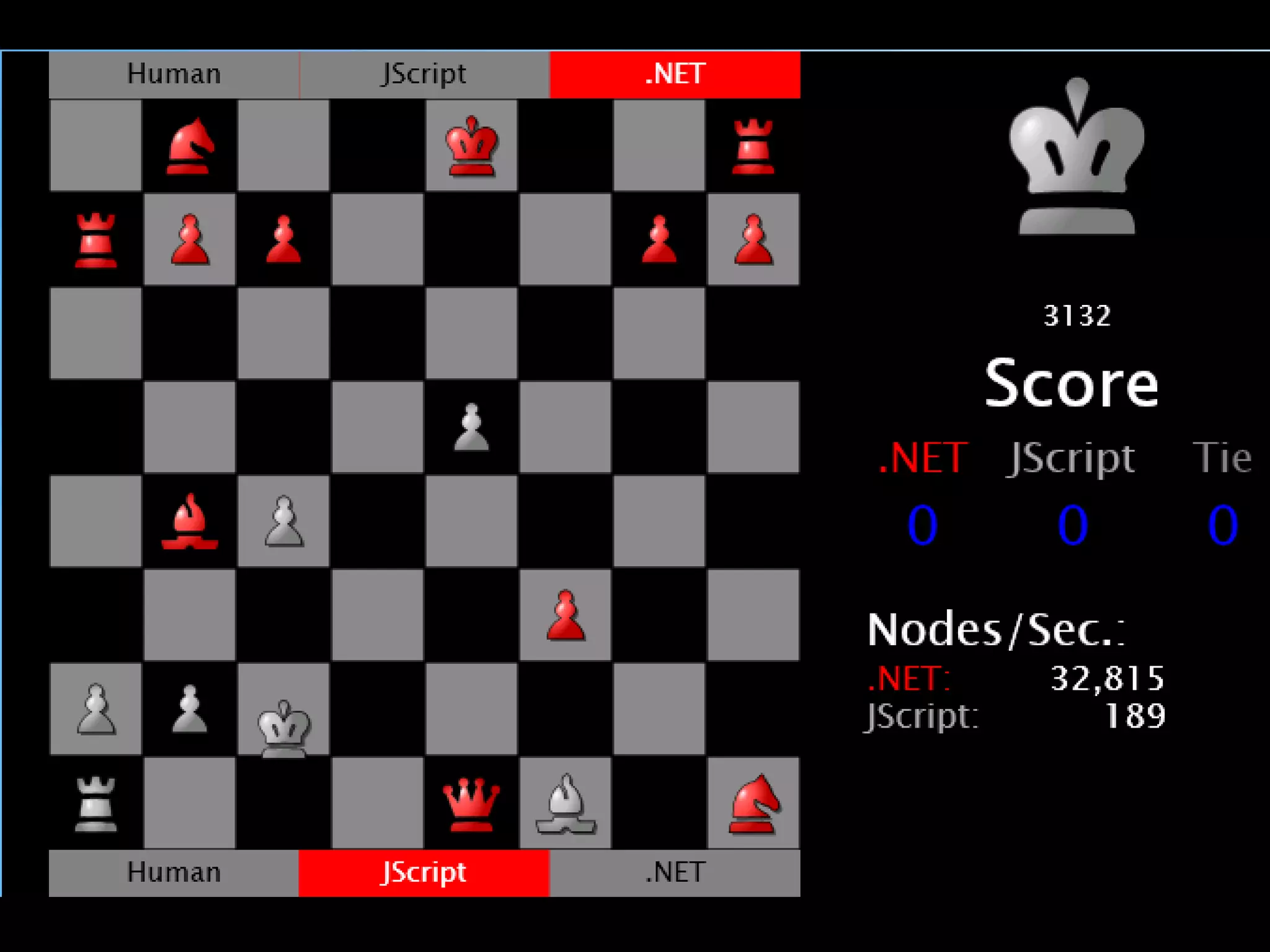
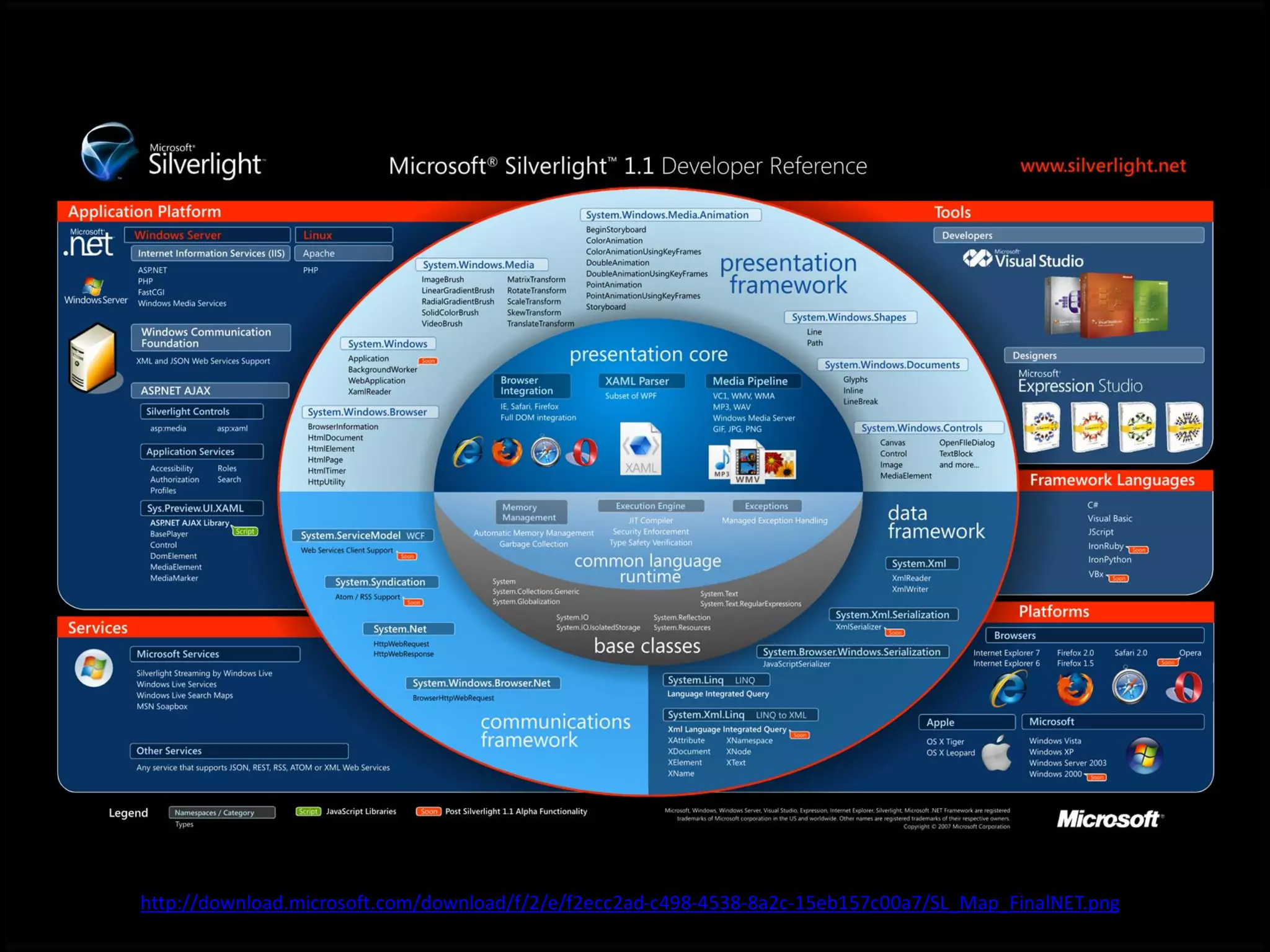
The document discusses Rich Internet Applications (RIA) and Silverlight. It notes that RIAs allow for interactive, visual, and multimedia capabilities from client to server. Some benefits of RIAs include richer user experiences, asynchronous data handling, support for graphics and multimedia. RIAs work by processing requests on the client, performing calculations on the client, and providing an interactive data exchange rather than just presenting static pages. They can improve the user experience by providing a more responsive interface tailored to individual users.