This document provides an overview of Silverlight, including:
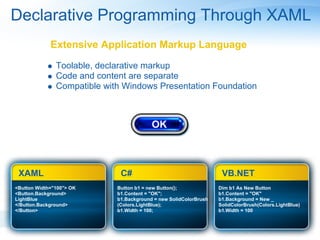
1. Silverlight allows for cross-browser, cross-platform rich media and interactive applications to be built and delivered to the web.
2. It is a .NET technology that extends the reach of .NET across browsers, desktops, devices and mobile.
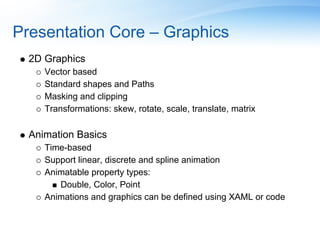
3. The document demonstrates Silverlight's core features like graphics, animation, data binding, networking and security.