RESUME - Marc Bercier - Long
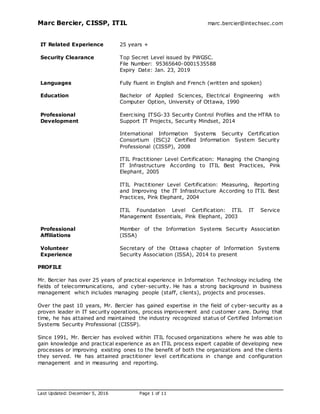
- 1. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 1 of 11 IT Related Experience 25 years + Security Clearance Top Secret Level issued by PWGSC. File Number: 95365640-0001535588 Expiry Date: Jan. 23, 2019 Languages Fully fluent in English and French (written and spoken) Education Bachelor of Applied Sciences, Electrical Engineering with Computer Option, University of Ottawa, 1990 Professional Development Exercising ITSG-33 Security Control Profiles and the HTRA to Support IT Projects, Security Mindset, 2014 International Information Systems Security Certification Consortium (ISC)2 Certified Information System Security Professional (CISSP), 2008 ITIL Practitioner Level Certification: Managing the Changing IT Infrastructure According to ITIL Best Practices, Pink Elephant, 2005 ITIL Practitioner Level Certification: Measuring, Reporting and Improving the IT Infrastructure According to ITIL Best Practices, Pink Elephant, 2004 ITIL Foundation Level Certification: ITIL IT Service Management Essentials, Pink Elephant, 2003 Professional Affiliations Member of the Information Systems Security Association (ISSA) Volunteer Experience Secretary of the Ottawa chapter of Information Systems Security Association (ISSA), 2014 to present PROFILE Mr. Bercier has over 25 years of practical experience in Information Technology including the fields of telecommunications, and cyber-security. He has a strong background in business management which includes managing people (staff, clients), projects and processes. Over the past 10 years, Mr. Bercier has gained expertise in the field of cyber-security as a proven leader in IT security operations, process improvement and customer care. During that time, he has attained and maintained the industry recognized status of Certified Information Systems Security Professional (CISSP). Since 1991, Mr. Bercier has evolved within ITIL focused organizations where he was able to gain knowledge and practical experience as an ITIL process expert capable of developing new processes or improving existing ones to the benefit of both the organizations and the clients they served. He has attained practitioner level certifications in change and configuration management and in measuring and reporting.
- 2. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 2 of 11 In 2014, Mr. Bercier created InTechSec Ltd. focusing his core competencies in order to provide professional IT security consulting services to government and private enterprises. Mr. Bercier is a recognized people leader who is able to motivate and encourage teams to work together to achieve a stated purpose. He has demonstrated this ability as a direct manager and in a matrix organization. As a project manager, he has been able to deliver quality project deliverables by leveraging architecture, deployment, IT support and IT security operations teams. Mr. Bercier has also positively contributed to the bottom line of his organization by, for example, organically growing revenues from the existing client base by more than $2 million while at CGI. Mr. Bercier is fully bilingual with the ability to help clients in both official languages via spoken and written communications. RELEVANT WORK EXPERIENCE Project #10 Shared Services Canada Cyber and IT Security (CITS) Transformation Services Information Technology Security Consultant June 2014 to present (2 Years and 6 months) Description: Working within the Cyber and IT Security (CITS) Transformation Services and the Security Operations groups of Shared Services Canada, Mr. Bercier is involved with several IT strategic security planning initiatives applicable to the Security Operations Centre (SOC) transformation. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Maturity Assessment: Mr. Bercier developed a maturity model with the long term goal of assessing and improving SSC’s security operations. Using available information from existing maturity models, he developed a self-assessment questionnaire that SSC SOC managers are able to leverage to determine their current operational maturity. Mr. Bercier has performed an analysis of answers provided and produced a report explaining the finding and providing recommendations that, when implemented, will lead SSC’s security operations to higher operational maturity. Standards Development: Mr. Bercier has produced the following standard documentation of SSC’s security operations: o Incident Management Standard o Vulnerability Management Standard Assessment of current SSC Security Operations practices, providing recommendations for improvement. Disaster recovery and service continuity planning: Mr. Bercier performed a thorough analysis of disaster recovery and service continuity models for the SSC SOC 43 government partners (departments and agencies). He provided recommendations based on the requirements of SSC and its partners. SOC Consolidation: Mr. Bercier provided recommendations on the approach to consolidate the 12 partner facilities providing IT security services into a single SOC, ensuring that the level of service provided to the 43 partners remain the same or better than the current situation. Security Service Definition: Mr. Bercier worked with CITS and Security Operations staff to define the end-state IT security services that will be offered by the SSC SOC. As part of this initiative, Mr. Bercier took the lead in writing the Service Definition document. Mr.
- 3. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 3 of 11 Bercier defined the use cases that describe these end-state services. He lead the development of Request for Proposals (RFPs) that will be used to setup supply arrangements with multiple vendors to enable the SSC SOC to provide state of the art IT security monitoring and security management (SM&SM) services. Mr. Bercier’s expertise helped SSC define the following services: o Event Logging and Auditing Service (ELAS) o Security Incident Management Service (SIMS) o Compliance, Threat and Vulnerability Management Service (CTVMS) Security Service Improvement Initiatives: Mr. Bercier has lead several improvement opportunities to measure and improve SSC’s operation security service delivery, including: o Security Operations Maturity Model Development o Security Operations Metrics and KPI development o Security Readiness Reporting Development Application Security: Mr. Bercier provided a recommendation to SSC on the need to offer application security services to ensure layered defence of the government of Canada infrastructure. Mr. Bercier developed the first version of the CITS program reporting dashboard to ensure a harmonised progress reporting mechanism across SSC CITS. Mr. Bercier has been part of the quality control team for several CITS publication including: o Data Protection Service Definition Document o Data Centre Zoning Standard o Security Monitoring and Security Management Statement of Sensitivity o ITSG-33 Security Controls related to Security Monitoring and Security Management o Infrastructure Protection Statement of Sensitivity o Privacy Protection within IT Security Standard o Vulnerability Management Strategy o Network Security Zoning Guidelines o Security Log Standards o Privilege Access Management (PAM) Framework Mr. Bercier has acted as the chair of the CITS & Security Operations Working group, leading discussions and logging minutes and actions. Project #9 CGI Global Managed Security Services Project Manager and Member of the ISO 27001 Compliance Initiative January 2013 to present (2 years and 3 months) Description: Working within the Global Managed Security Services group of CGI, Mr. Bercier provided management guidance to IT security specialists integrated within cross-functional teams, including architecture, deployment, IT support and security monitoring to implement large and medium security products and services into operational environments including: Intrusion Detection (network, host and wireless), Log Management and Continuous Vulnerability Management services for a national securities regulator. Log Management, Continuous Vulnerability Management and Strong Authentication services for a large financial institution. Network Intrusion Detection and Log Management services for a satellite communication service provider with offices worldwide. Network Intrusion Detection service for a credit union. Log Management service for 2 large financial institutions. Host Intrusion Detection Service for Canada Post Corporation (CPC)
- 4. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 4 of 11 The projects managed by Mr. Bercier represented total revenues of over $8.5 million for CGI. Mr. Bercier applied the CGI Client Partnership Management Framework (CPMF) methodology which is based on the Project Management Book of Knowledge (PMBOK) and includes the following knowledge areas: Project Integration Management, Project Scope Management, Project Time Management, Project Communications Management, Project Cost Management, Project Quality Management, Project Risk Management, and Project Procurement Management. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Contract Review including analysis of requirements. Gap analysis between proposed and contracted solutions. Current Situation Analysis / Due Diligence based on validated assumptions after contract awards. Created Project Management Plans including: o Work Breakdown Structures using MS Project 2010 o Risk Management Plans o Issues Management Plans o Procurement Management Plans o Communication Management Plans o Requirement Management Plans o Quality Management Plans o Measurement Plans o Change Request Management Plans o Project Status Reports Maintenance of the WBS, Risk, Issues and Change Registers and other project documentation. Mobilized resources at the start of each project and managed project resources for efficient delivery, balancing time, scope, cost, and quality. Vendor and Procurement management. Change Request Management including keeping a change register. On-going project communication including chairing meetings and producing meeting minutes, status reports and updated work breakdown structures. In addition to his project management role, Mr. Bercier has been involved in other initiatives within CGI’s Global Managed Security Services (GMSS), including: Process Creation and Improvement: Mr. Bercier has lead several initiatives to improve the efficiency of CGI’s Managed Security Services group. He has proposed several changes to the Operational Readiness Review process which have been adopted. He has improved the request procedure used by Project Managers to implement Web reports for new services or new clients. Mr. Bercier successfully led a business growth initiative resulting in organic growth of $1 million over 4 years. Mr. Bercier has provided assistance to CGI’s GMSS compliance officer to become ISO 27001 compliant. Specifically, he has: o Written the Information Security Management System (ISMS) Manual o Written the first version of the Metrics and Key Performance Indicators (KPI) Strategy document o Revised and corrected the Asset Management Policy Mr. Bercier has written the first draft of the CGI GMSS Project Handbook. Mr. Bercier is part of the senior leadership team providing input to the strategic direction of CGI's Global Managed Security Services division.
- 5. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 5 of 11 Project #8 CGI Global Managed Security Services Security Operations Centre (SOC) Manager November 2007 to December 2012 (5 years and 2 months) Description: Working within the Global Managed Security Services group of CGI, Mr. Bercier was accountable for planning and overseeing the day-to-day operational delivery of security and technology monitoring and support services on IT security infrastructure and applications solutions, while providing management guidance to technical and IT security specialists integrated within cross-functional teams to ensure support of IT security services and solutions in the production environment. Mr. Bercier led interactions with IT Architecture and service deployment specialists to ensure an ongoing understanding of issues emerging from technology and security monitoring and support services delivery, and to support the planning of changes in the IT environment that result in optimized levels of technology performance. He was responsible for establishing and ensuring that policies, protocols, processes and controls were implemented and adhered to in regard to all security monitoring, technology monitoring and support services. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Oversaw the day-to-day operational management, scheduling and delivery of a combined Security and Network Operations Centre (SOC & NOC) staffed 365/24/7 with 10+ Security Analysts and 3 Senior Security Analysts providing security monitoring, technical monitoring and security incident response to CGI’s 50+ Managed Security Services clients. Oversaw the day-to-day scheduling and delivery of an Infrastructure Protection Centre (IPC) staffed 365/24/7 with 7 Security Analysts providing security monitoring and security incident response in a dedicated Public Works and Government Services Canada (PWGSC) environment. Oversaw the day-to-day operational management, scheduling and delivery of the CGI Security Incident Response Team (SIRT) in providing security analysis and recommendations and taking actions to protect CGI’s 50+ clients subscribing to Managed Security Services. Oversaw the day-to-day operational management, scheduling and delivery of a team of 20+ Security Infrastructure Support Specialists providing 365/24/7 on-call support to CGI’s dedicated and shared Managed Security Services Infrastructure. The team under Mr. Bercier’s responsibility provided support for hardware, Windows, UNIX, Linux and VMWare Operating Systems (OS), database and security applications. Led a team of IT support and Cyber Security professionals providing Managed Security Services to Government of Canada departments and agencies, including: o Canada Post Corporation o Canada Revenue Agency o Canada School of Public Service o Canadian International Development Agency (CIDA) o Canadian Payment Association o Department of Finance o Department of Foreign Affairs and International Trade Canada (DFAIT) o Department of Justice o Federal Treasury Board o Health Canada o Heritage Canada o Industry Canada o Library and Archives Canada
- 6. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 6 of 11 o National Research Council o Parks Canada o Public Health Agency o Public Works and Government Services Canada (PWGSC) o Shared Services Canada o Supreme Court o Transport Canada o Transport Safety Board o Treasury Board o Workplace Safety and Insurance Board (WSIB) The security services provided under Mr. Bercier’s responsibility included: o Network Intrusion Detection and Protection Service (NIDS and NIPS) using SourceFire (Snort), Cisco, Enterasys Dragon, IBM ISS and Juniper. o Host Intrusion Detection and Protection Service (HIDS and HIPS) using TrendMicro, McAfee and IBM ISS. o Wireless Intrusion Detection using Motorola Air Defense. o Log Management service using ArcSight and Splunk. o Mail filtering (anti-spam) service using Cisco Ironport, McAfee and Postini. o Host Anti-Virus service using McAfee and Symantec o Mail and gateway anti-virus service using McAfee o Web Content Filtering service using BlueCoat and WebSense. o Strong Authentication (two-factor authentication) service using RSA SecurID. o Continuous Vulnerability Management using Rapid7 and Nessus. o File Integrity Management service using TripWire. o Web Application Firewall (WAF) service using Imperva and InfoSphere Guardium. o Database Access monitoring (DAM) service using Imperva. o Firewall Management service using Cisco and Checkpoint firewalls o VPN Management using Cisco ASA. o Security Surveillance and Monitoring service using ArcSight Security Event and Incident Management (SEIM) tools. Provided oversight and technical guidance to the 365/24/7 management of incidents and problems related to the IT security services and solutions delivered by CGI GMSS, and managed the provision of the necessary distance or field support requirements. Led the definition and implementation of the incident responses and corrective measures necessary to address problems in such areas as IT security, infrastructure, applications and services, including the escalation of incident resolution to the security architecture team or other CGI support teams. Oversaw the implementation of performance metrics pertaining to monitoring and support activities to ensure compliance to Service Level Agreements and other aspects tied to service delivery. Process Creation and Improvement: Mr. Bercier led several initiatives to improve the efficiency of CGI’s Managed Security Services group. o He was instrumental in ensuring the viability and stability of the Operational Readiness Review Process. As a result, the operational support teams he managed were confident that all the required information was available during after hour incident management. o Mr. Bercier worked with his team to establish a patching strategy for the systems they managed ensuring that all systems and applications were properly secured as new vulnerabilities emerged. o Mr. Bercier spearheaded the improvement of the security incident process and ensured alignment to the SANS Institute (System Administration, Networking, and Security Institute) best practice by developing and clarifying the classification of
- 7. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 7 of 11 security incidents along with the required response to meet the Service Level Agreement (SLA) of CGI’s clients. o He collaborated with the other MSS teams to improve the Change Management process ensuring that all changes to the managed infrastructures were logged and documented according to ITIL best practices. o Mr. Bercier improved the efficiency of the Technical Incident process by directing his team to avoid duplicate incident records across the multiple incident management systems used by CGI and ensuring consistent incident record quality and completeness of information. Audits and Compliance: Mr. Bercier provided leadership to ensure continued annual compliance during PCI and 5970 audits. Mr. Bercier directed his team in the development of reporting used as evidence of SOX compliance. To maintain compliance Mr. Bercier: o Reviewed control objectives and assigned resources to provide evidence of compliance o With respect to non-compliant items, developed and led action plans to ensure future compliance Developed annual resource and training plans supporting the operational delivery of security and technology monitoring and support services, and developed inputs to financial budgeting and forecasting requirements. Human Resources: Mr. Bercier was responsible to interview and hire candidates for the available positions within CGI’s Managed Security Service group. His responsibilities included suggested starting salaries and increases. He was responsible for annual performance assessments including the setting of goals and objectives and compensation review. Mr. Bercier initiated performance improvement plans resulting in focusing the impacted team members to start performing up to the level that Mr. Bercier knew they could reach. As part of his responsibility he terminated members who could not function at the level required for the position. Mr. Bercier worked with the CGI HR department to follow all the appropriate process and due diligence to protect CGI and ensure that affected members were clearly informed of the requirements of the performance improvement plan. Mr. Bercier was part of the senior leadership team providing input to the strategic direction of CGI's Global Managed Security Services division. Project #7 CGI Global Managed Security Services Senior Client Service Manager May 2006 to November 2007 (1 year and 6 months) Description: Mr. Bercier was responsible for the customer care of CGI’s Managed Security Services’ clients to which he was assigned. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Close involvement in the day to day operational management of his client’s expectations along with ensuring a superior level of service for the CGI operational delivery teams within MSS. Mr. Bercier’s assigned clients included: o 3 large financial institutions o Canada Post Corporation (CPC) o Canadian International Development Agency (CIDA) o World Anti-Doping Agency (WADA) Operational escalation point during service issues in which the resolution was not meeting the client’s expectations.
- 8. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 8 of 11 Provide guidance and direction to the CGI MSS Operational teams involved in delivery of services to his clients. Organic growth of his existing client base. Mr. Bercier increased organic revenue by $1.2 million over 3 years. Project Management: Mr. Bercier successfully managed implementation of several security related projects including: o Web content filtering, host anti-virus and e-mail filtering services for a major Canadian courier company o Web content filtering and host intrusion detection services for a large financial institution o Strong authentication service for an international foundation o Web content filtering for a Government of Canada agency o Intrusion detection (network, host) and anti-virus services for a large financial institution Project #6 MTS Allstream (Formerly AT&T Canada) Managed Network Services Process Consultant September 2004 to February 2006 (1 year & 5 months) Description: Mr. Bercier’s responsibilities included the development of ITIL processes to support the operations of MTS Allstream Managed Network Services group. The scope of his responsibilities included configuration management, service level management and key performance indicators. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Designed a working scalable Configuration Management Process to meet the requirements of ITIL implementation across the entire Managed Services Division. Created Operational Level Agreements (OLA) with internal suppliers in compliance with signed Service Level Agreements (SLA) for continued effective customer support across all groups at Allstream. Ensured the effective long term measuring and improving of existing ITIL processes (Incident, Problem, Change, Configuration and Service Level Management Processes) by determining Key Performance Indicators (KPI) for eac h process and producing monthly KPI reports with common-sense actionable recommendations. Project #5 Allstream (Formerly AT&T Canada) Managed Network Services Operations Manager April 2003 to September 2004 (1 year & 5 months) Description: Led a team of 1st level support specialists by coaching and directing with a focus on minimizing downtime and improving customer service. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Reduced daily incident review and correction process by managers from 1.5 hours to 15 minutes daily. Contributed to the increase of customer satisfaction during escalations by listening to customers or Customer Service Managers concerns and acting in quick, decisive ways to ensure that issues were resolved in a timely manner. Initiated and created training material for 1st level specialists to enable new staff to transition into position quickly and effectively.
- 9. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 9 of 11 Led a project team in aligning procedures and toolset configuration between the Ottawa and Toronto Enterprise Management Centers (EMC) that resulted in quick responsibility transfer during backup situations and seamless management of customer networks. Human Resources Management: Led performance reviews, shift scheduling in a 7/24 environment, interviewing, selecting and hiring network resources. Prioritized technical incidents and tasks. Provided guidance to network operation members. Ensured new networks were ready for ongoing operations. Continually focused on improving ITIL processes for ongoing service delivery excellence. Project #4 AT&T Canada Managed Network Services Solutions Engineer September 2002 to April 2003 (7 months) Description: As part of a team of Network Solutions Engineers, Mr. Bercier was responsible to design and implement new Cisco based IP networks comprised of routers and switches. He was also responsible for providing 3rd level support to existing networks and clients. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Developed comprehensive templates to empower the Engineering team to deliver clear and effective Customer Network Analysis Reports. Analyzed client requirements and designed internetworks based on those requirements. Contributed to the success of implementing, on time and on budget, a network of over 200 nodes. Documented the network and procedures for the support team and the field technicians including procedures, configuration information and network diagrams. Configured network devices and troubleshooting during implementation. Trained 2nd and 1st level support staff to enable them to support new networks. Implemented wide-area network security by using access lists in Cisco routers. Implemented secure authentication methods for dial-up networking in Cisco routers. Configured ISDN backup in Cisco routers. Project #3 AT&T Canada Managed Network Services Internetworking Consultant (2nd level support) September 2000 to September 2002 (2 years) Description: Mr. Bercier was responsible to provide 2nd level support to existing Cisco based IP networks for several large and medium clients. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Pioneered the production of Customer Network Analysis Reports, which became part of AT&T Canada’s standard service offering. Presented Network Analysis Reports to customers and service managers. Ensured client satisfaction by resolving incidents quickly or escalating to 3rd level in a timely manner. Implemented wide-area network security by using access lists in Cisco routers. Implemented secure authentication methods for dial-up networking in Cisco routers. Configured ISDN backup in cisco routers. Configured and troubleshot Cisco routers and switches.
- 10. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 10 of 11 Project #2 AT&T Canada Managed Network Services Internetworking Specialist (1st level support) May 2000 to September 2000 (4 months) Description: Mr. Bercier was responsible to provide 1st level support to existing Cisco based IP networks for several large and medium clients. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: As a result of a merger of two AT&T clients, Mr. Bercier worked with the client to migrate their two networks into one. Ensured client satisfaction by resolving incidents quickly or escalating to 2nd level in a timely manner. Configured and troubleshot Cisco routers and switches. Project #1 NAV Canada / Transport Canada, Aviation Network Engineering Life Cycle Engineer August 1991 to May 2000 (8 years & 10 months) Description: Mr. Bercier was responsible to manage the day-to-day activities of the NAV Canada Intranet (NCI) WAN. Mr. Bercier’s roles, responsibilities and objectives for this position included the following: Successfully led a project to secure funds for the purchase of equipment to migrate sites from dial-up to Frame-Relay connectivity increasing performance and user satisfaction. Successfully led a project resulting in the implementation of a Metropolitan Area Network (MAN) interconnecting three NCI sites in Ottawa. Trained NAV Canada field technicians ensuring that they could effectively maintain deployed equipment.
- 11. Marc Bercier, CISSP, ITIL marc.bercier@intechsec.com Last Updated: December 5, 2016 Page 11 of 11 SUMMARY OF SKILLS Cyber Security Governance and Risk Management (GRM) Policies Security Incident Response Team (SIRT) Security Operations Centre (SOC) Infrastructure Protection Centre (IPC) Log Management Network Intrusion Detection/Prevention Host Intrusion Detection/Prevention Wireless Intrusion Detection/Prevention Anti-Virus Web Content Filtering Mail Filtering Security Events and Incident Management (SEIM) SANS Institute Best Practices Audits and Compliance ITSG-33 PCI compliance ISO 27001 compliance SOX compliance 5970 compliance Documentation Requests for Proposal Service Definitions Procedures Service Delivery Maturity ITIL Service Management Incident Management Problem Management Change Management Configuration Management Service Level Management Key Performance Indicators (KPI) Remedy Action Request System Project Management PM Book of Knowledge (PMBOK) MS Project 2010 Office Automation Applications MS Office: Excel, Word, PowerPoint, Visio, Access Operating Systems Windows 3.11, 95, 98, 2000, NT, XP, 7, 8 MS-DOS Network Equipment & Technologies Network Operations Centre (NOC) Cisco Routers Cisco Switches Ethernet Token Ring Frame Relay Wide Area Networks Metropolitan Area Networks Wireless Networking Asynchronous Transfer Mode (ATM) Multiprotocol Label Switching (MPLS) Integrated Services Digital Network (ISDN) Soft Skills People Management and HR Team Leadership Strategic and Tactical Planning Performance Management Operational Planning Client Service Management Process Management Troubleshooting / Problem Solving Individual Contributor & Team Player Documentation Fully Bilingual
