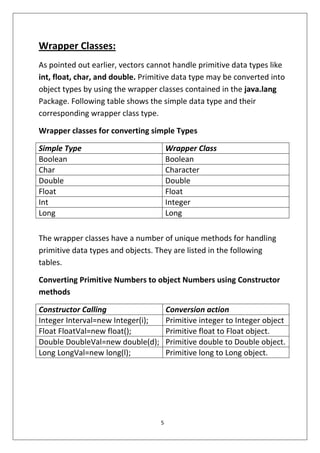
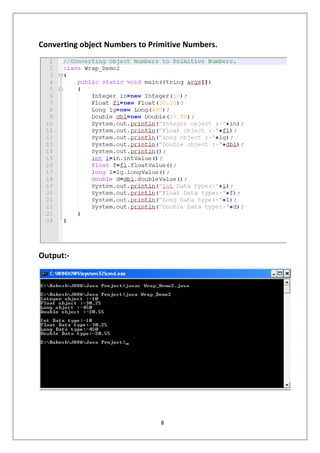
The document is a project report on Java programming by Rakesh Bijawat, focusing on wrapper classes and nesting methods as part of his BCA studies at Dezyne E'cole College. It covers the conversion between primitive data types and their corresponding wrapper classes, including auto boxing and unboxing, as well as the concept of method nesting within a class. Acknowledgments and a synopsis highlight the project's significance in reinforcing fundamental Java concepts.