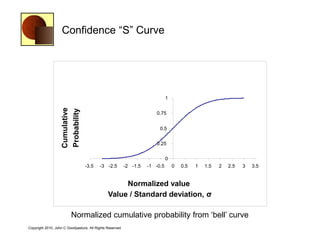
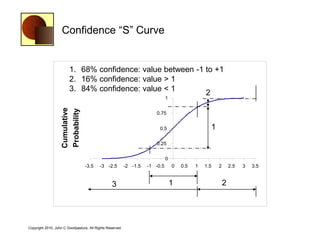
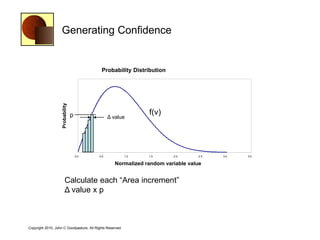
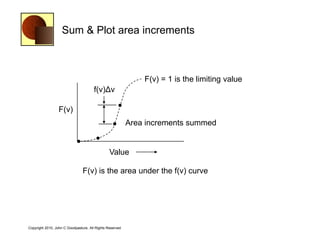
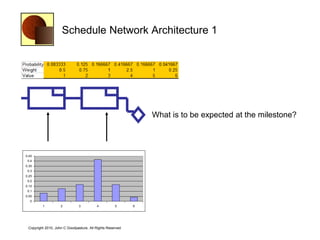
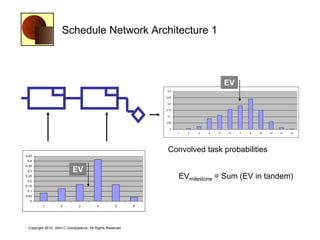
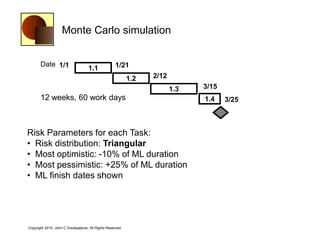
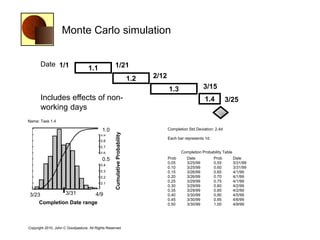
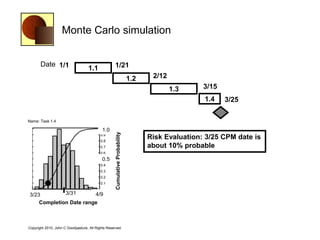
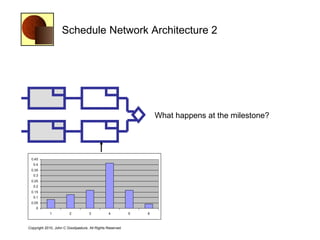
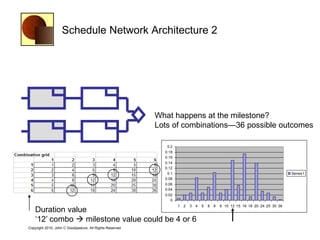
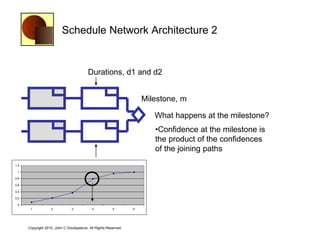
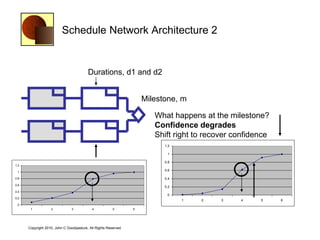
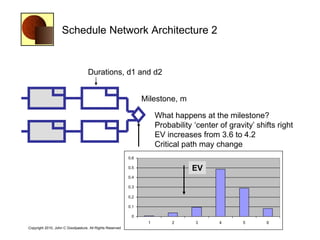
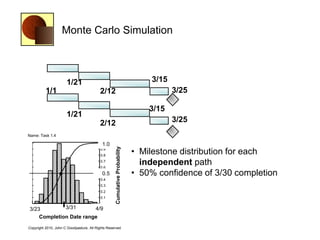
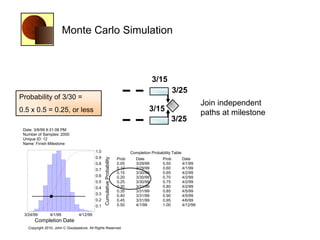
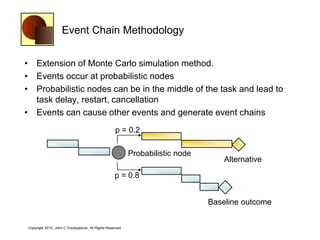
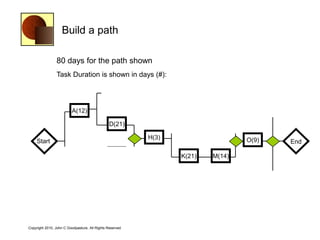
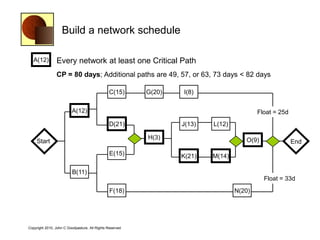
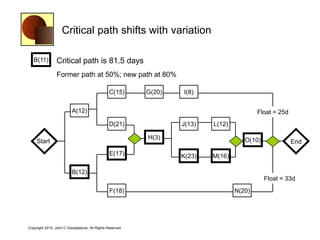
This document discusses quantitative risk analysis methods for project schedules. It introduces concepts like confidence intervals and S-curves that show the probability of completing a task within a certain date range. Monte Carlo simulation is presented as a method to model schedule risk by assigning probability distributions to task durations. The results provide expected values and confidence levels for completion dates. Network architectures with probabilistic nodes that can generate event chains are also proposed to extend Monte Carlo analysis.