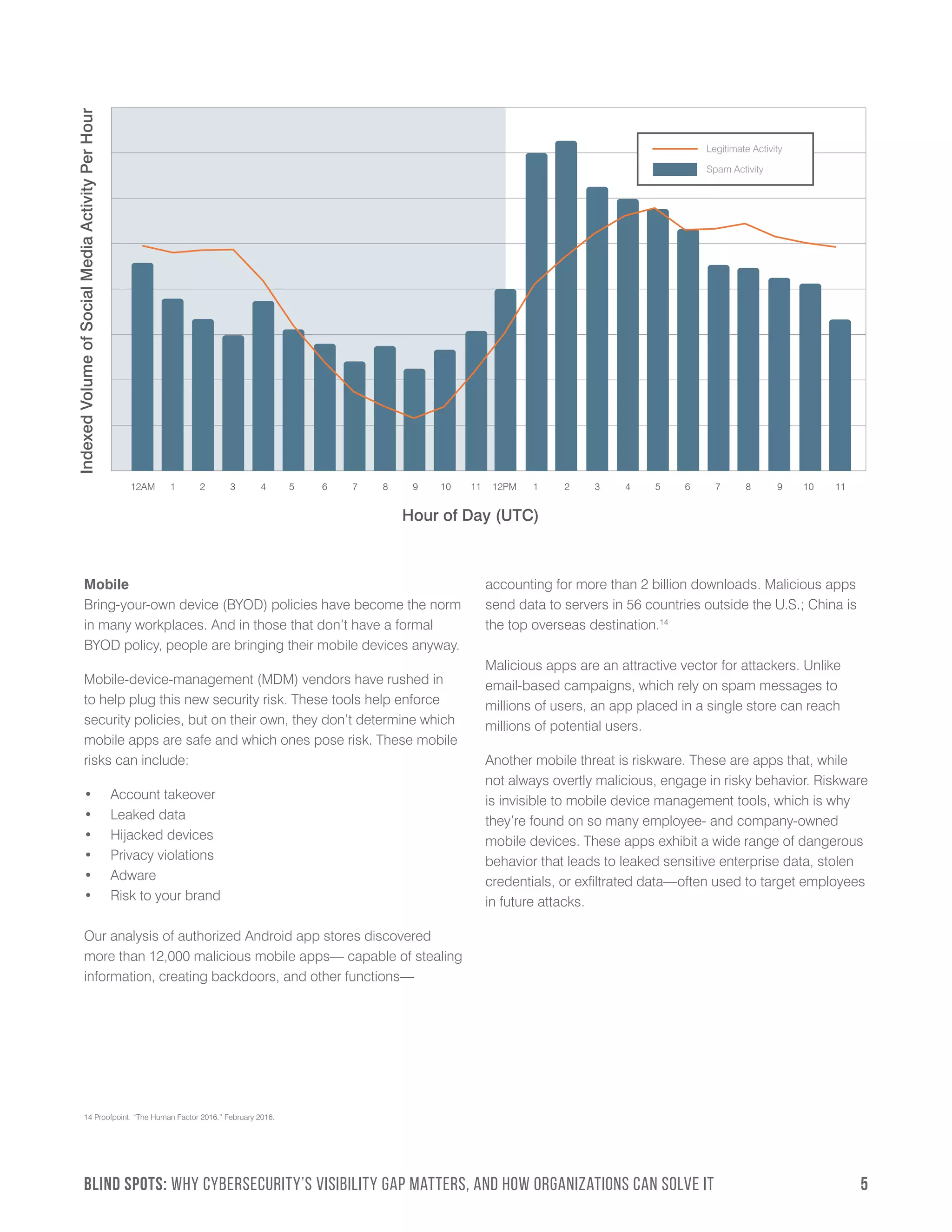
This document discusses the visibility gap in cybersecurity and how threats now originate outside traditional network perimeters. It notes that most attacks start through email, social media, and mobile devices rather than within networks. Without visibility into these channels, organizations are missing most attacks and only see threats late in the attack cycle after attackers are already inside systems. The document argues organizations need to expand their view beyond networks to properly protect against modern cyber attacks.