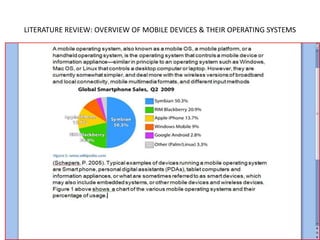
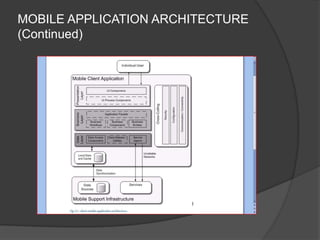
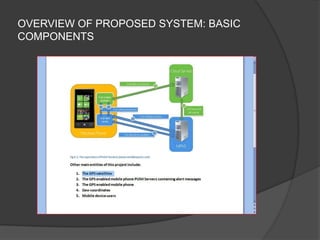
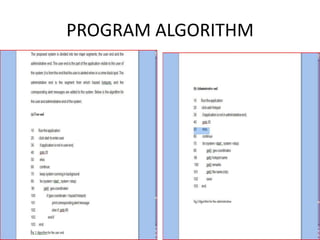
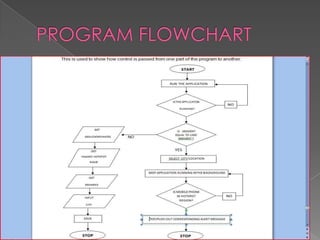
This document outlines a presentation on the Reign Mobile Hotspot Detection System project. The project aims to develop a mobile application to alert users about hazardous areas in Nigeria, such as areas prone to accidents, flooding, or crime. It will use the GPS location of the user's mobile device to check if they are entering a dangerous area and send a notification. The presentation covers the problem statement, objectives, literature review on GPS and mobile devices, proposed system design, methodology using Java and HTML5, and preliminary findings from testing in Nigeria.