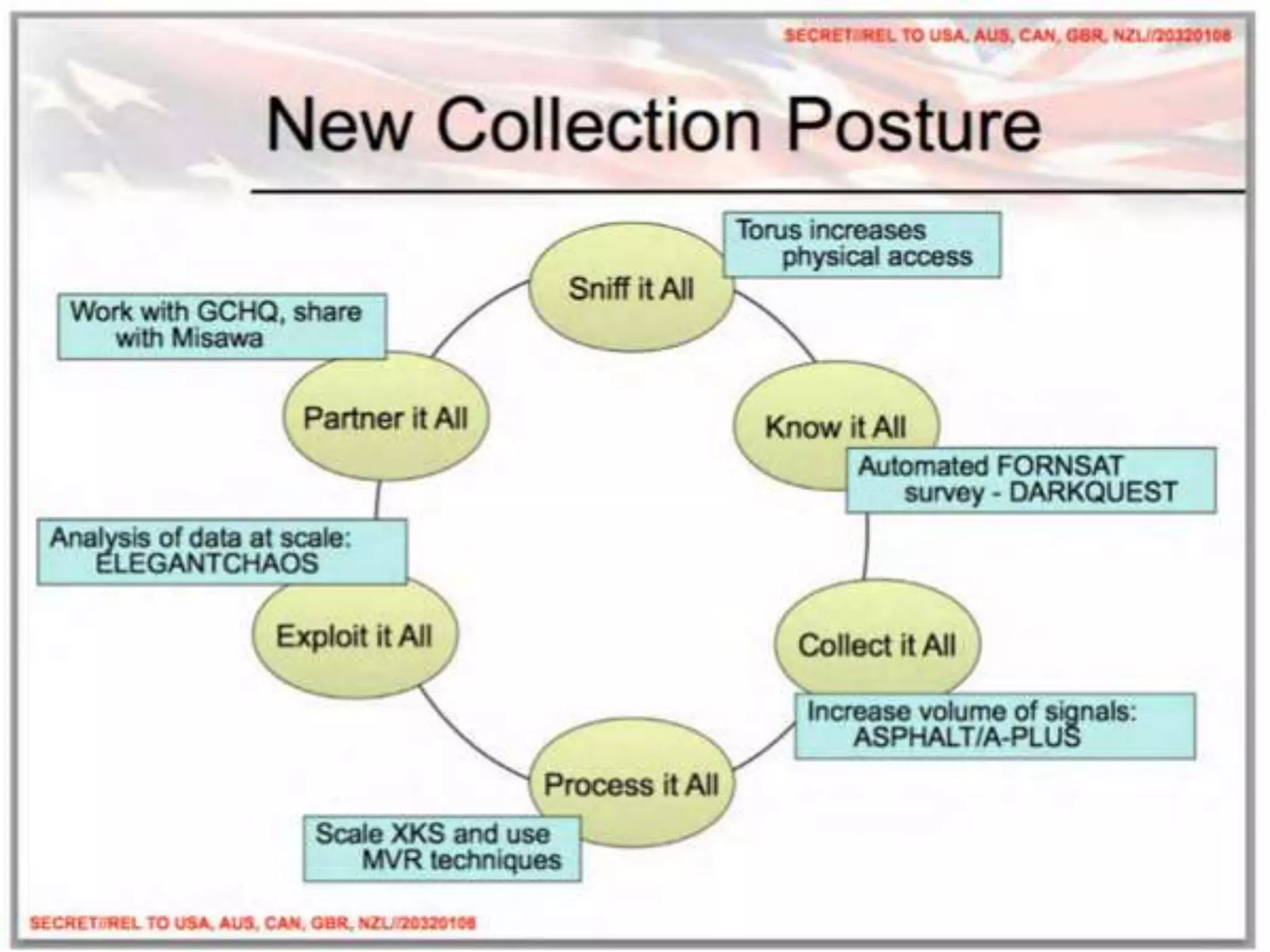
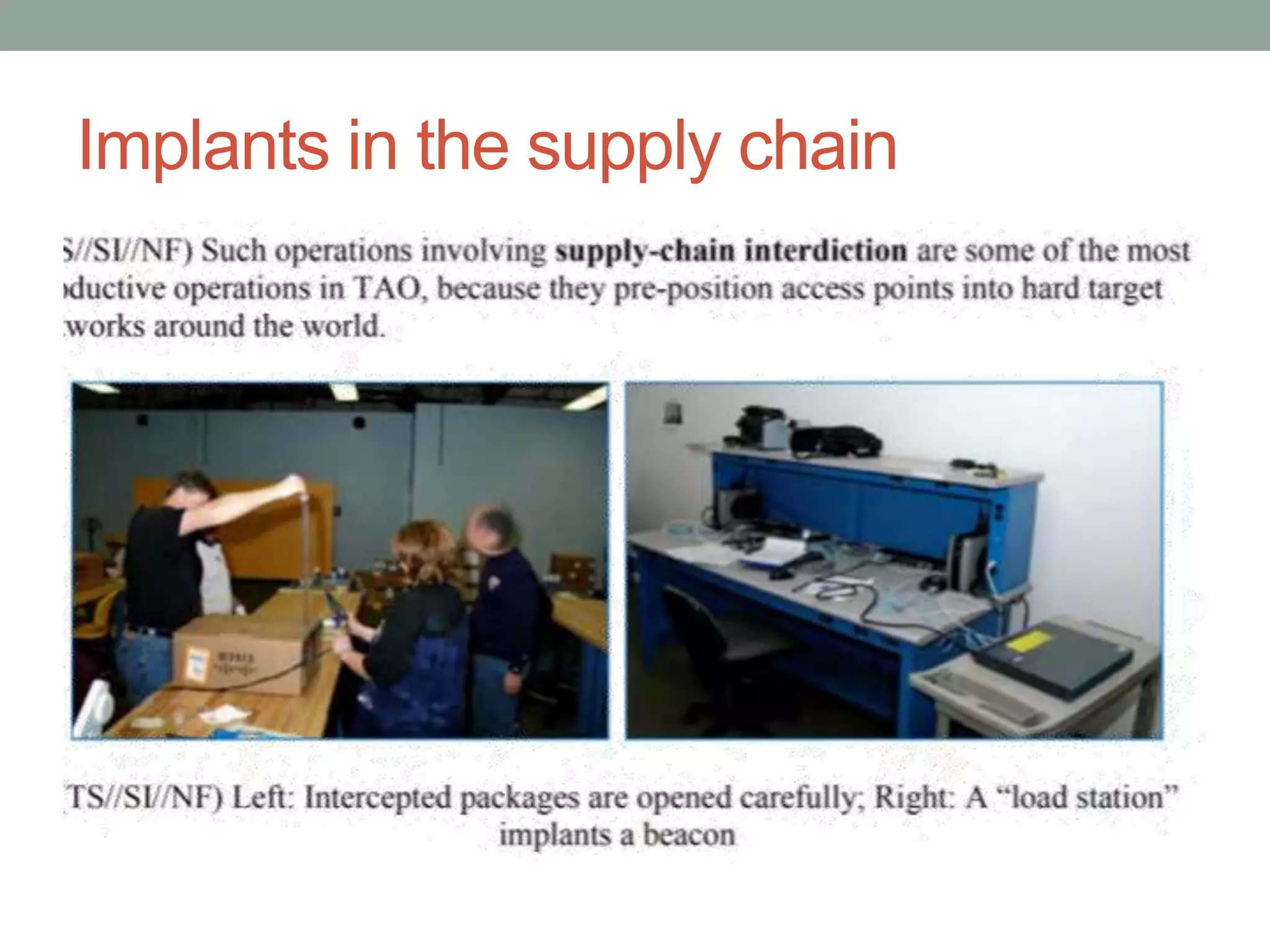
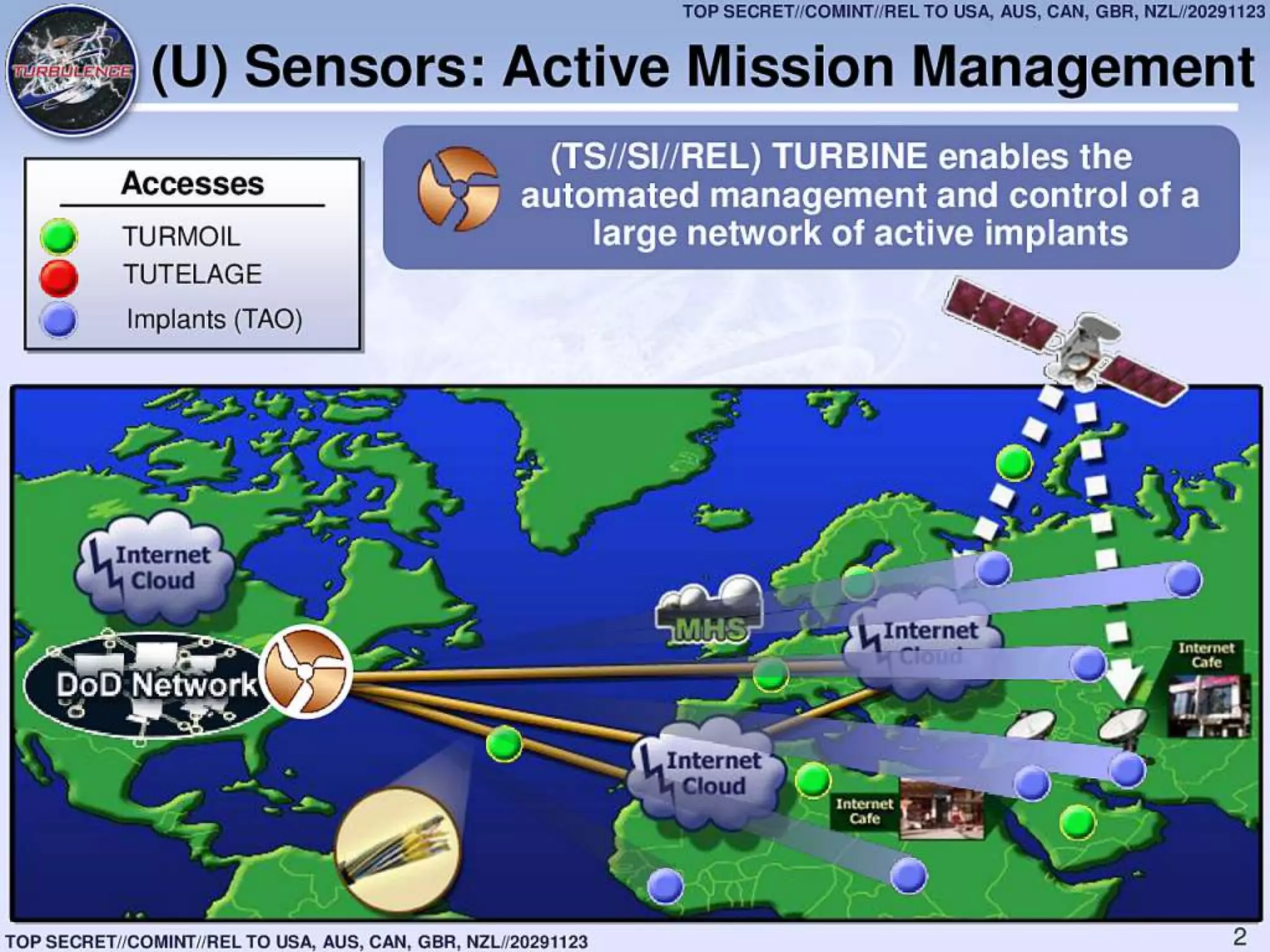
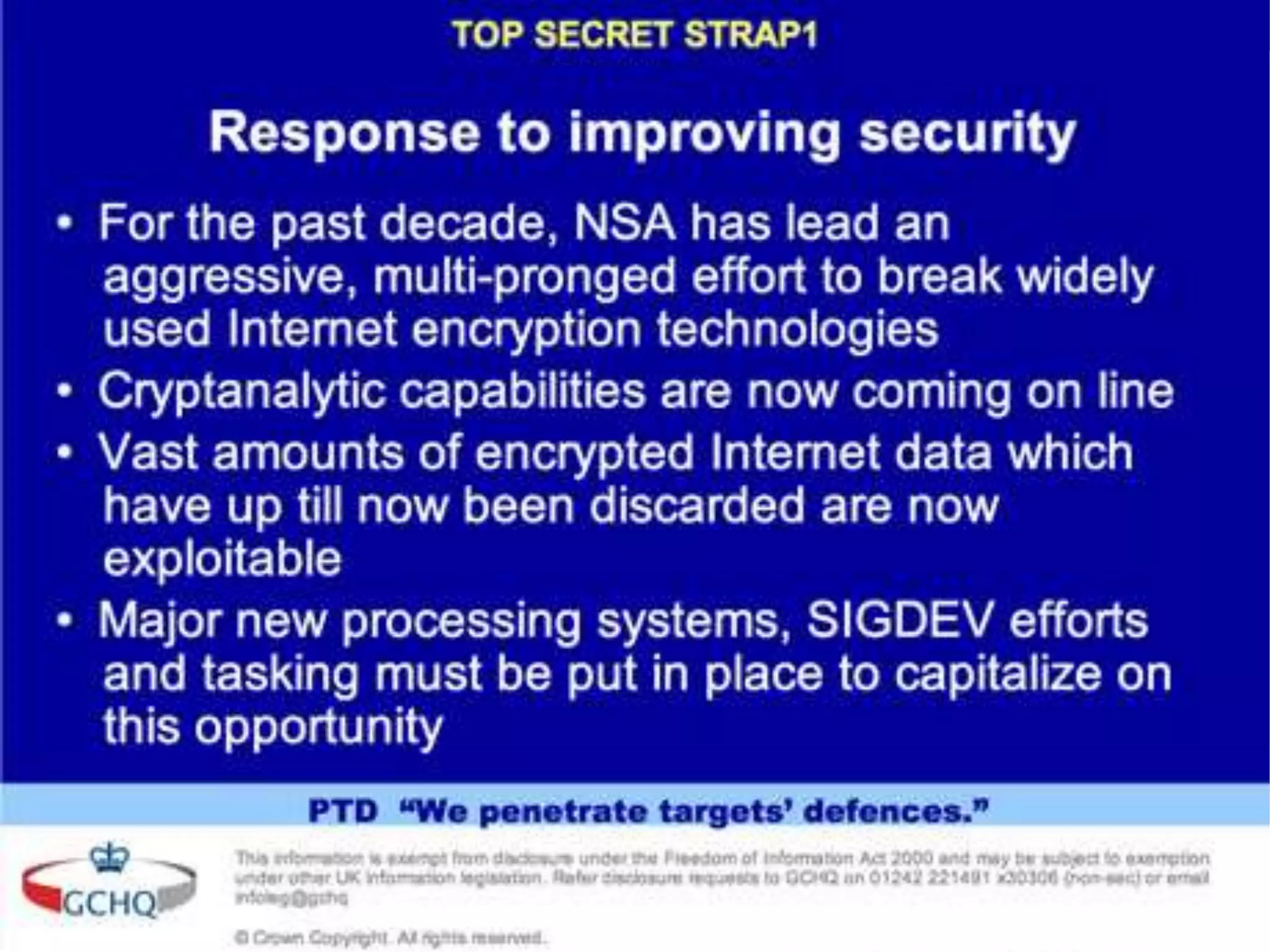
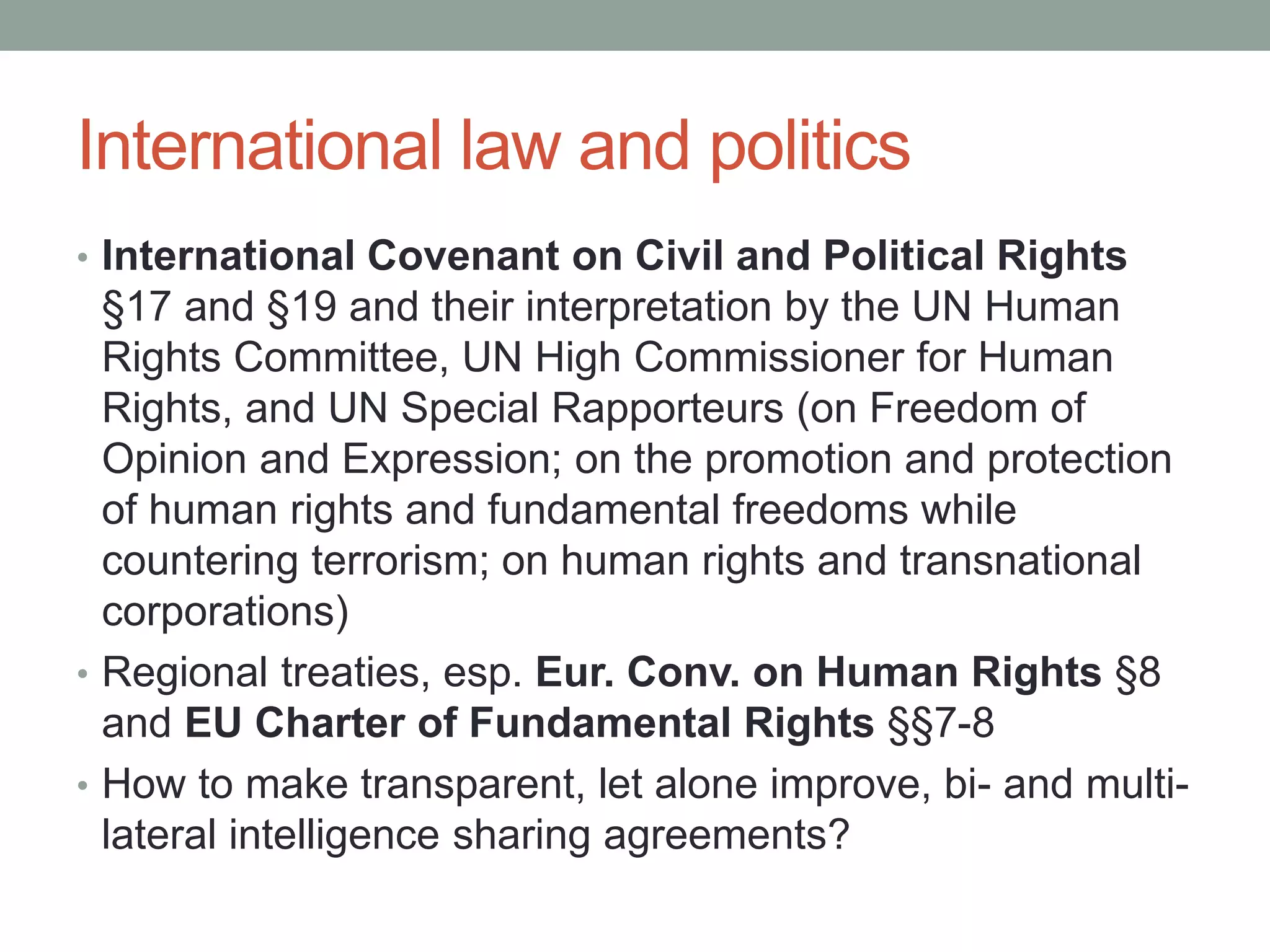
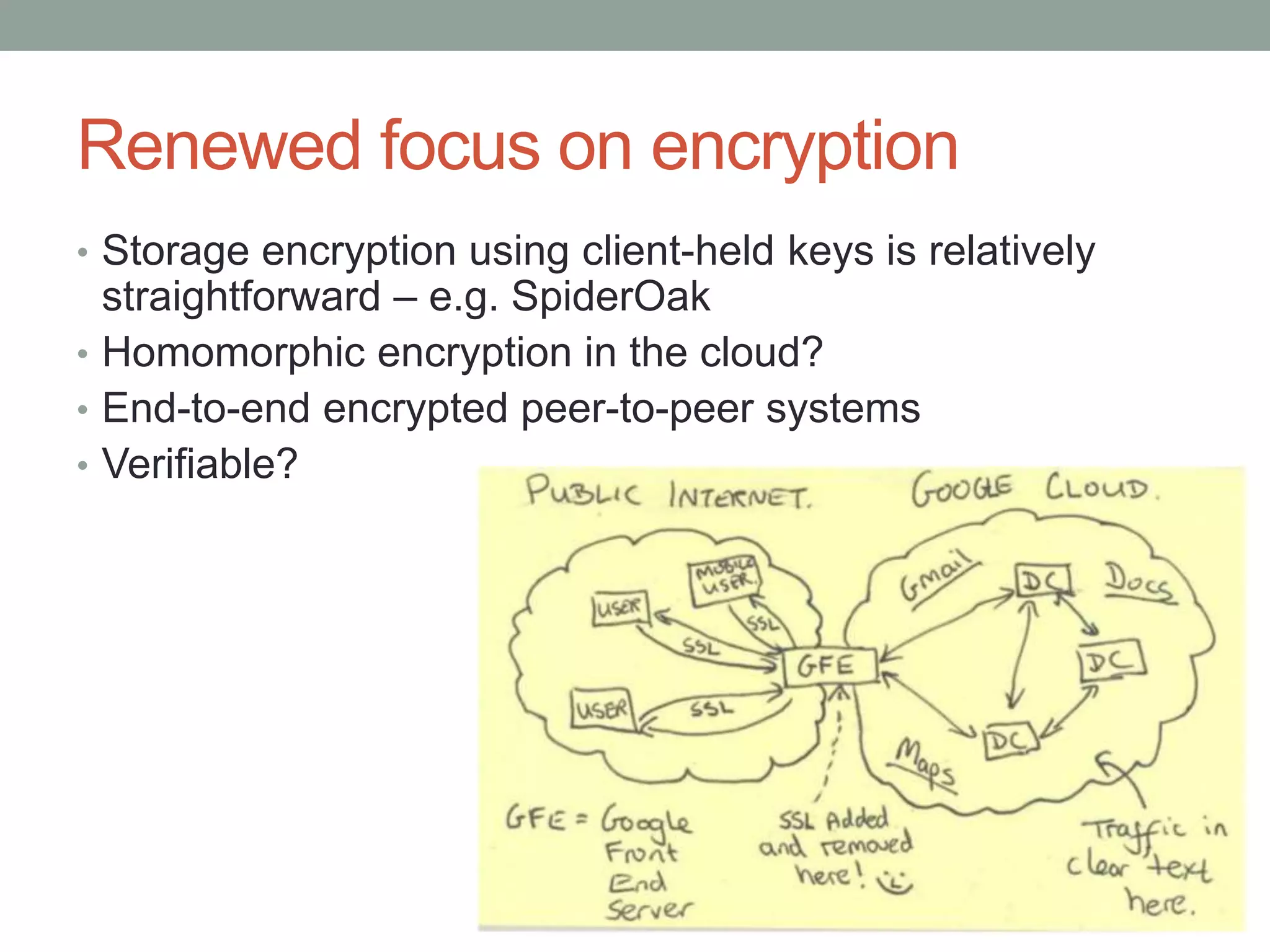
This document summarizes international laws and policies regarding privacy and mass surveillance in the post-Snowden era. It discusses obligations under international human rights law, calls by the UN General Assembly to review surveillance practices, and reports by the UN High Commissioner for Human Rights criticizing secret interpretations of law and lack of protections for individuals. The document also reviews data privacy regulations in Europe, debates around data localization, encryption technologies, and concludes that strengthening international law and information security is needed to curb mass surveillance by powerful states.