Embed presentation
Download as PDF, PPTX












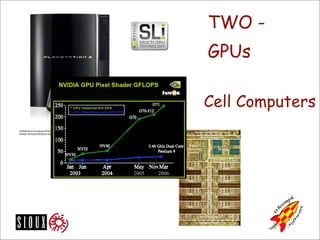

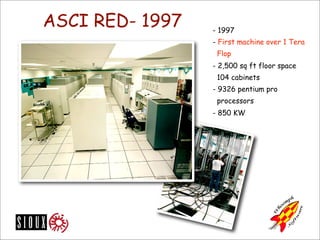










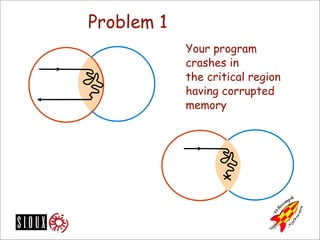







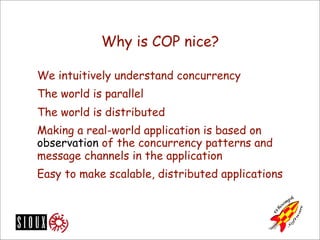

















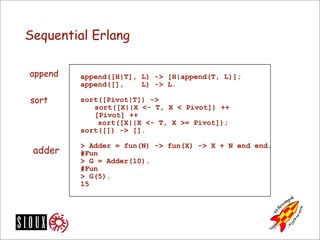


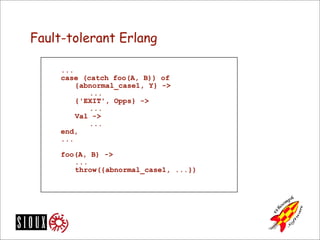
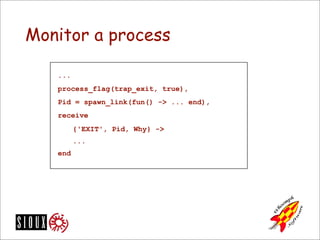










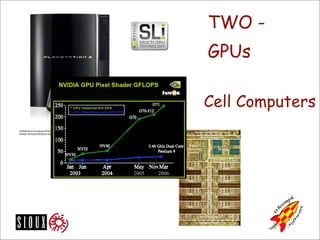
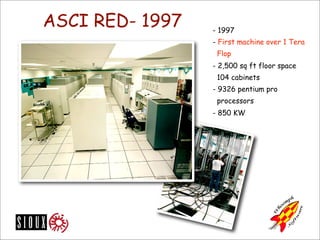
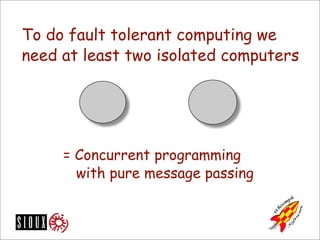
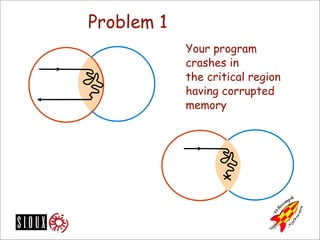
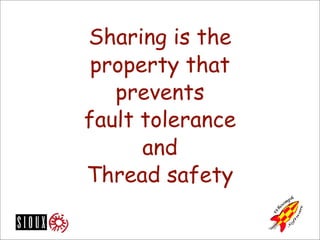
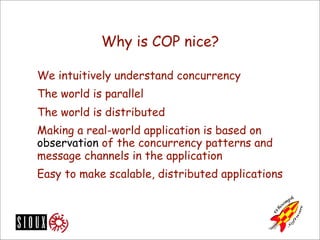
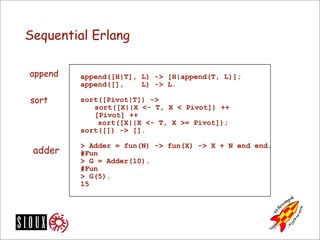
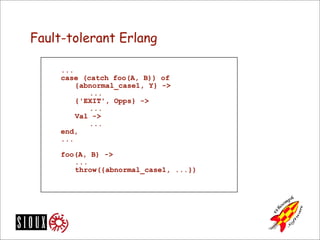
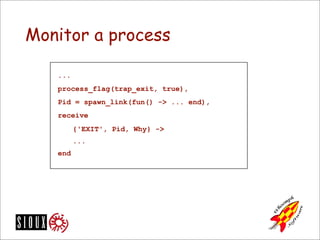
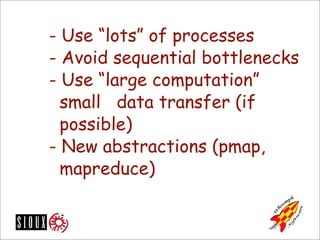
The document discusses Erlang as a functional programming language optimized for concurrent programming and fault tolerance in distributed systems, highlighting its lightweight processes and rapid message passing. It contrasts concurrent and shared memory programming, advocating for pure message passing and no mutable state to ensure reliability and scalability. Additionally, the text reviews the evolution of CPU architectures, emphasizing the necessity of adapting software to leverage the capabilities of multicore processors effectively.