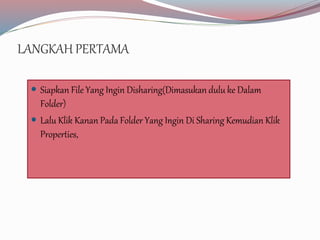
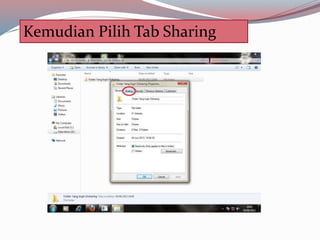
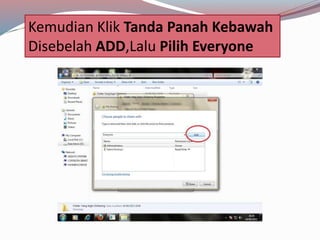
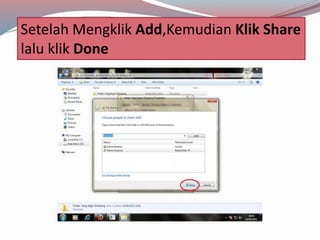
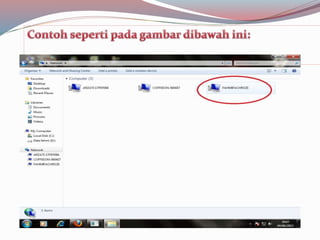
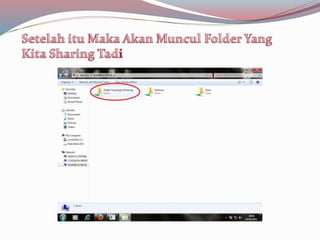
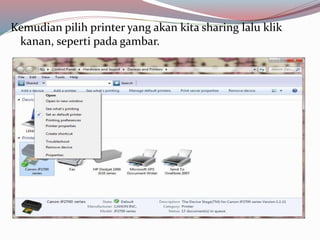
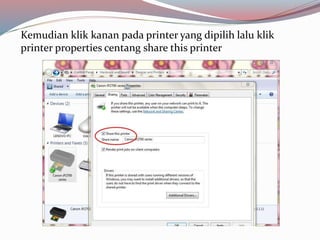
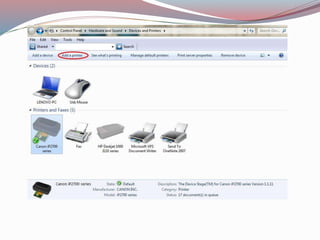
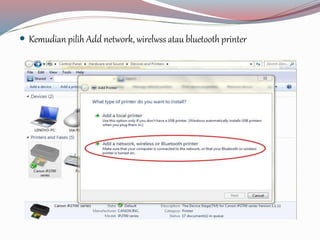
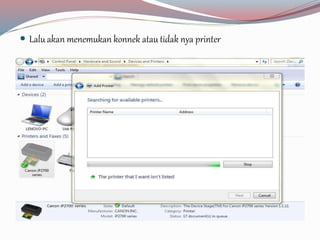
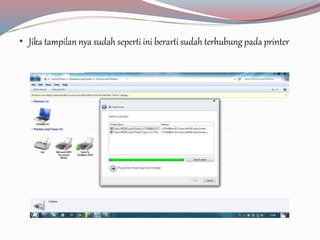
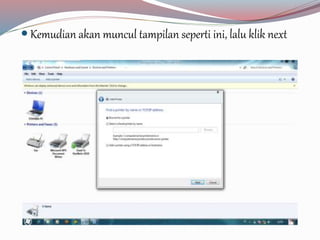
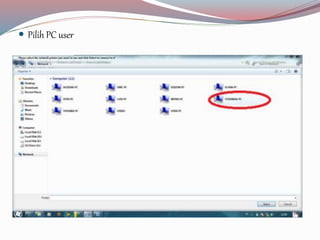
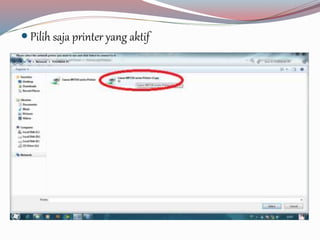
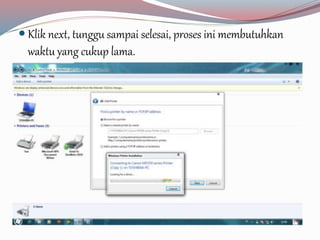
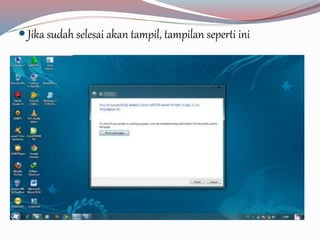
File sharing adalah proses penyediaan dan penerimaan file digital melalui jaringan, sementara printer sharing memungkinkan beberapa PC terhubung ke satu printer untuk efisiensi kinerja. Langkah-langkah untuk file sharing meliputi mempersiapkan file dan mengatur folder sharing, sedangkan untuk printer sharing meliputi menghubungkan PC ke jaringan dan mengatur printer agar dapat diakses oleh perangkat lain. Dokumentasi ini memberikan panduan praktis mengenai langkah-langkah tersebut.