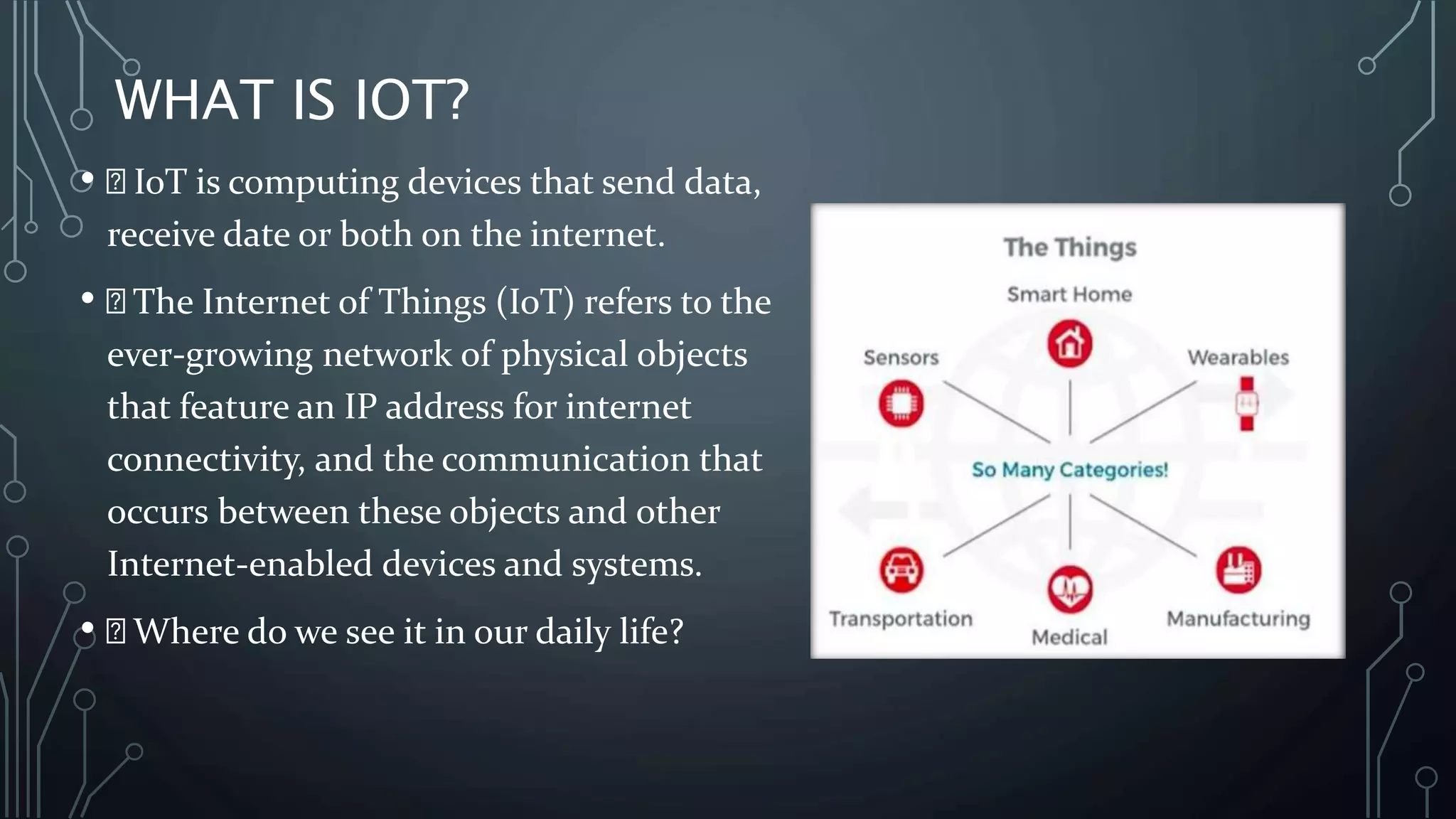
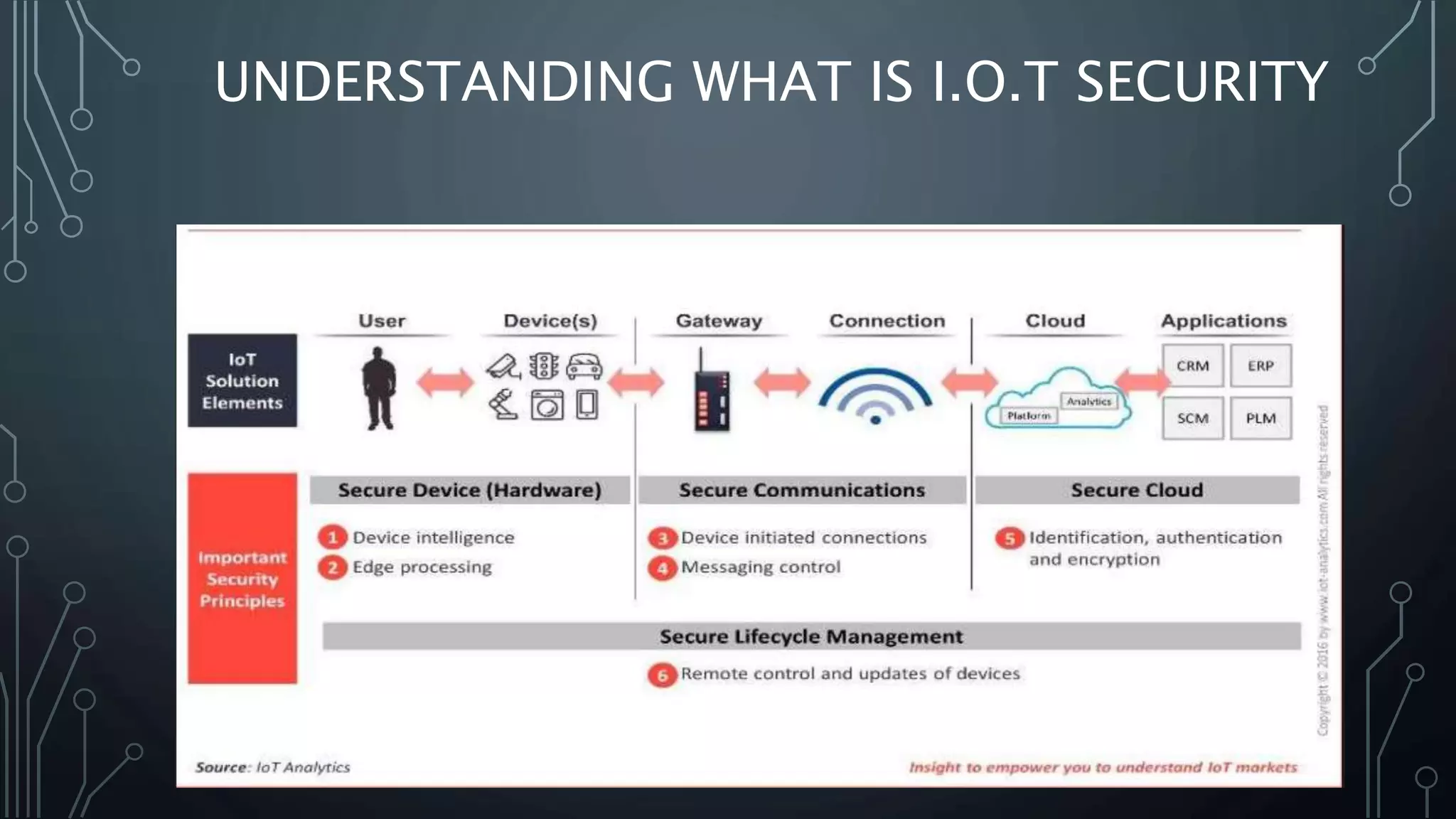
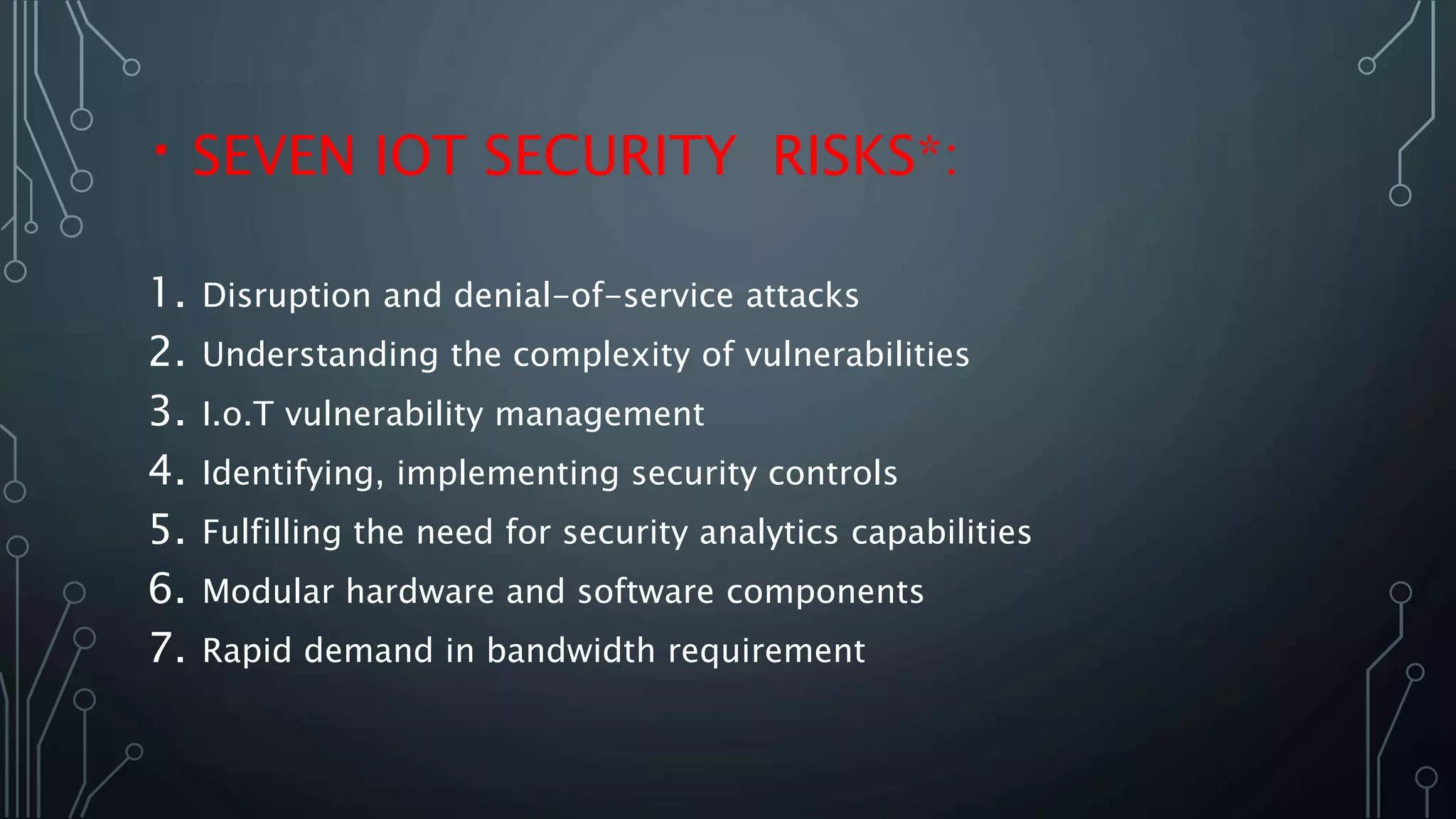
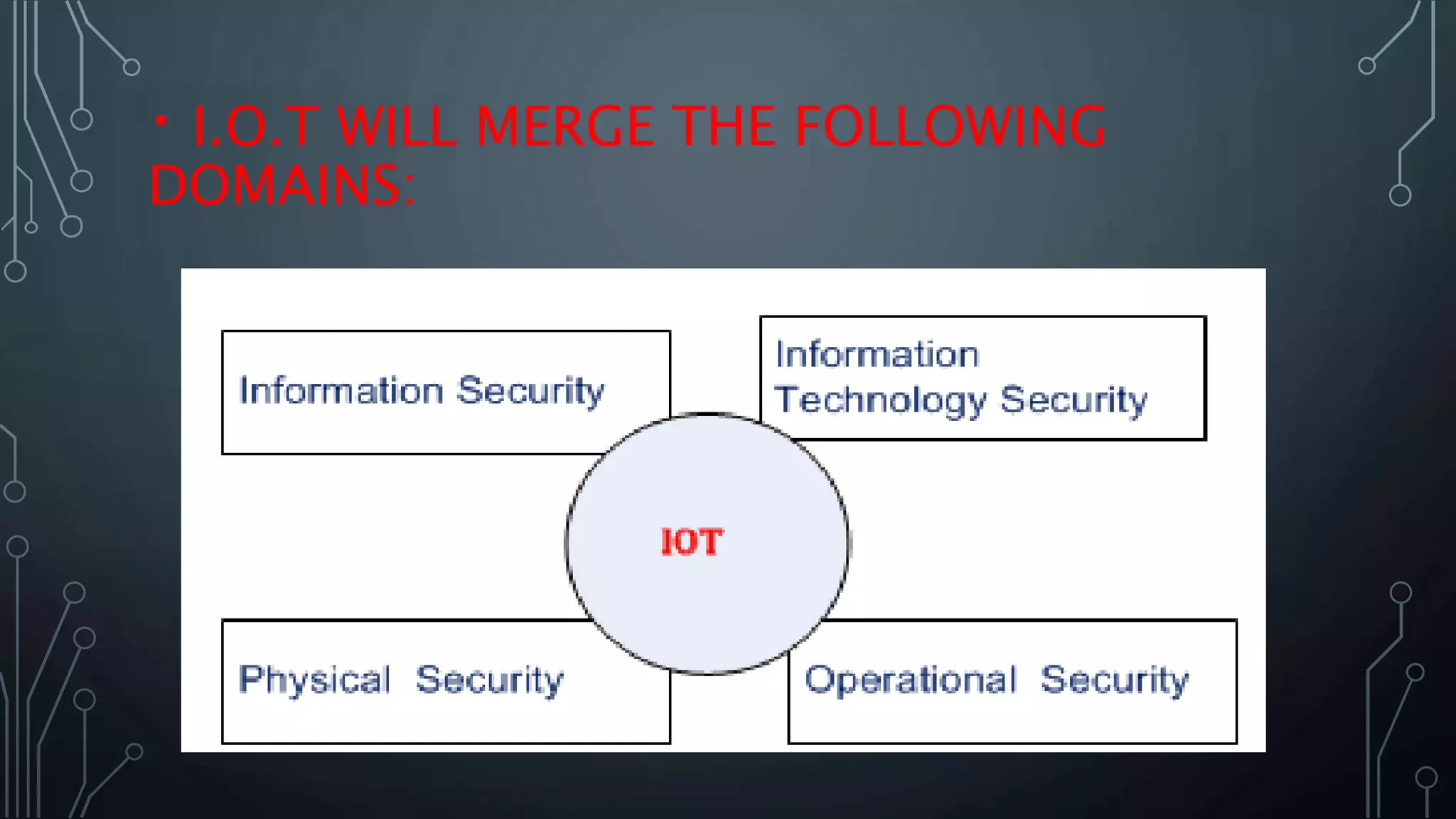
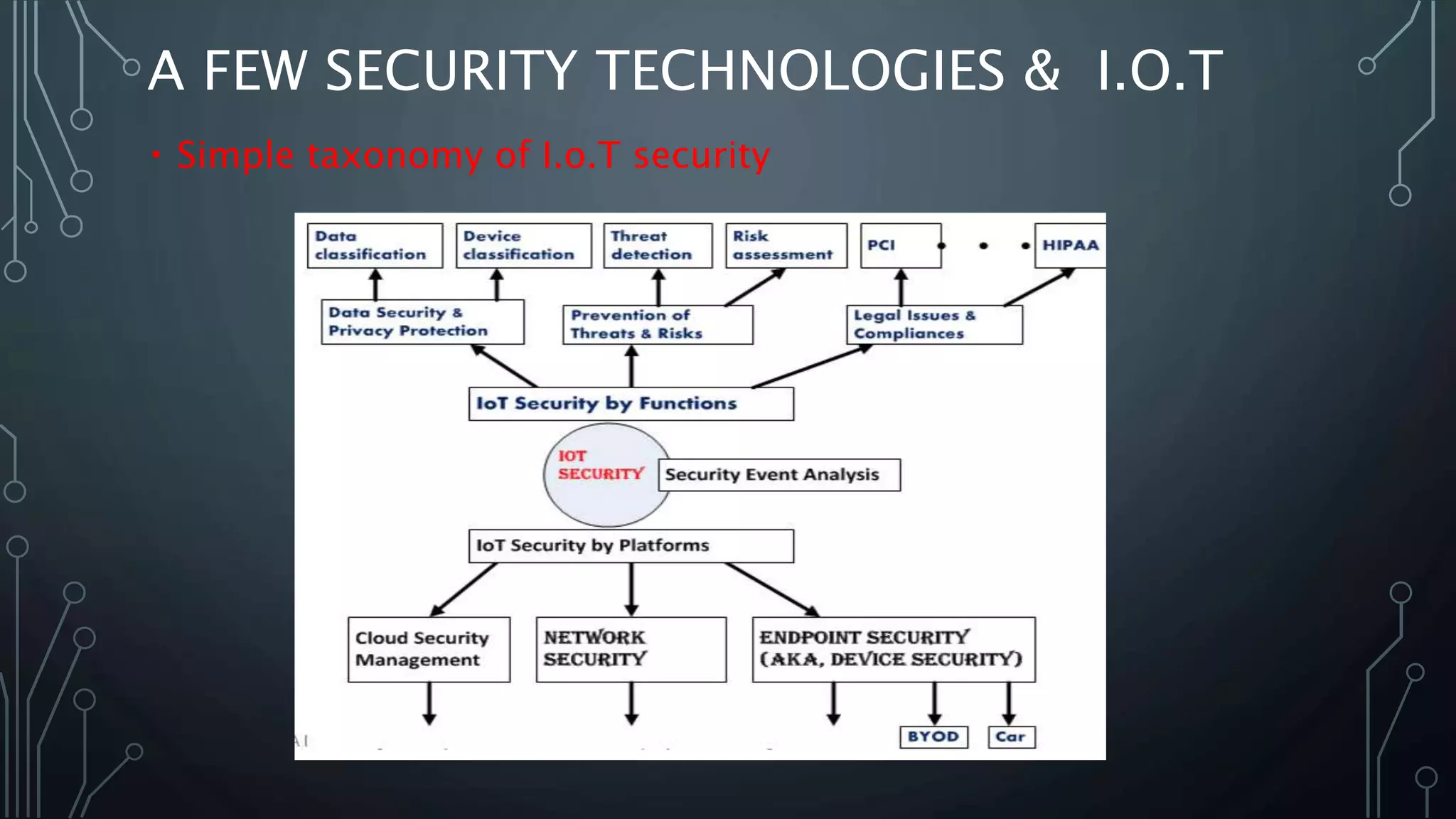
This document discusses Internet of Things (IoT) security issues and challenges. It notes that IoT devices have limited processing power for security tasks like encryption due to hardware constraints. Common IoT security problems include weak authentication through default or easy to guess passwords, use of insecure protocols like Telnet, lack of encryption on network traffic, insecure software updates, and poor physical security of device ports. The document outlines the top 10 IoT security risks according to OWASP and predicts that securing the growing number of IoT devices and their integration of different domains will pose major new challenges for network security.