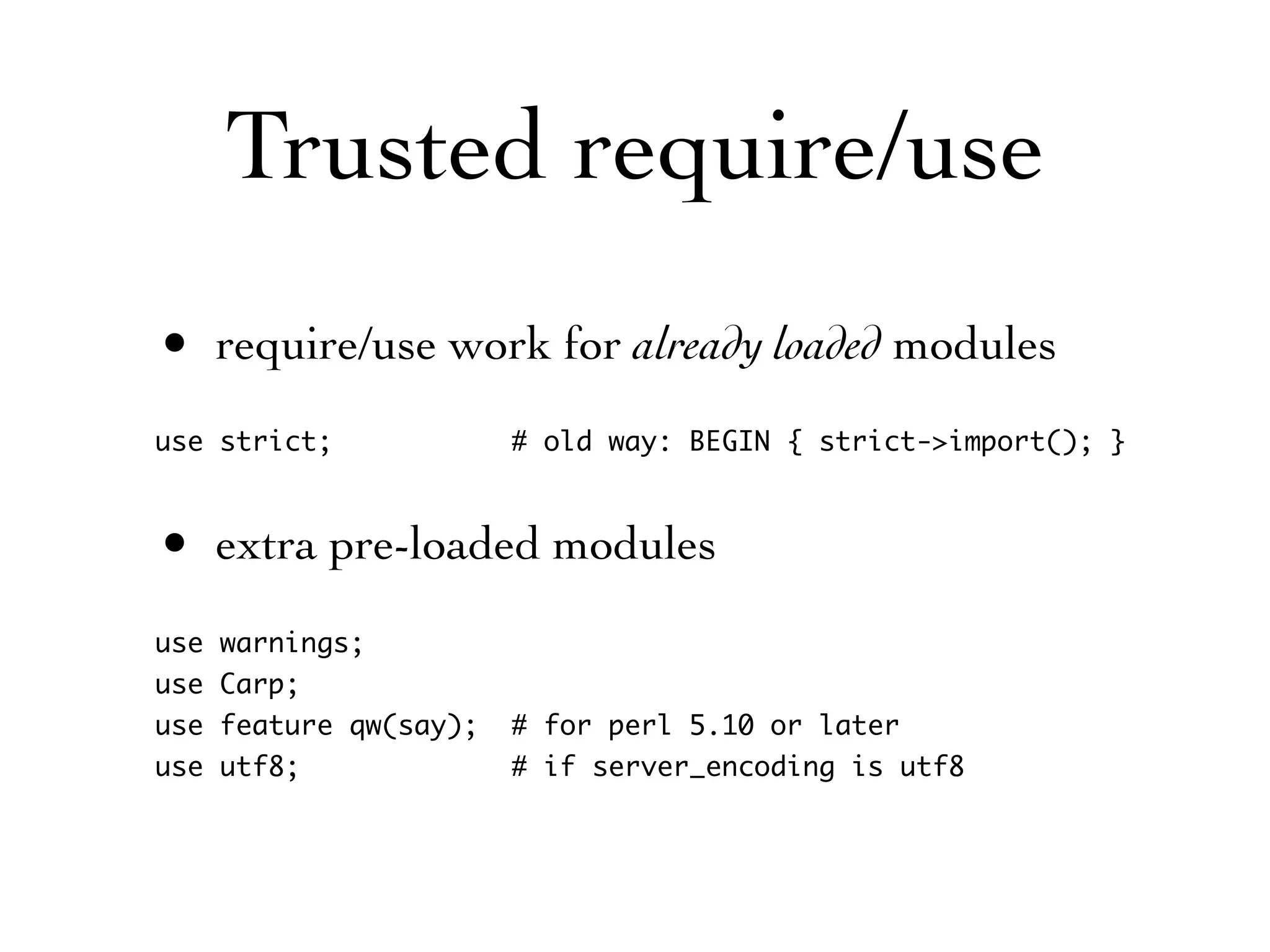
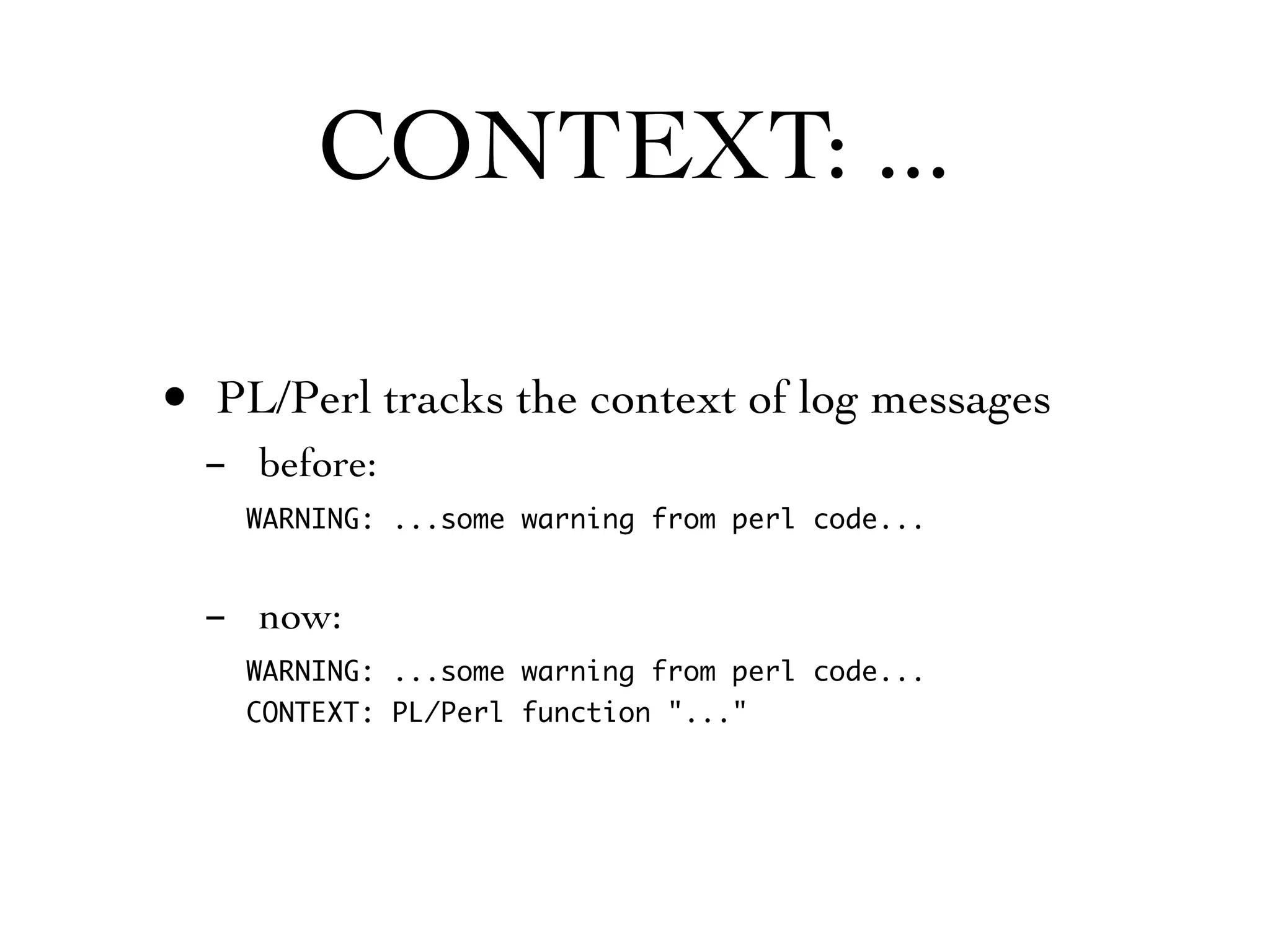
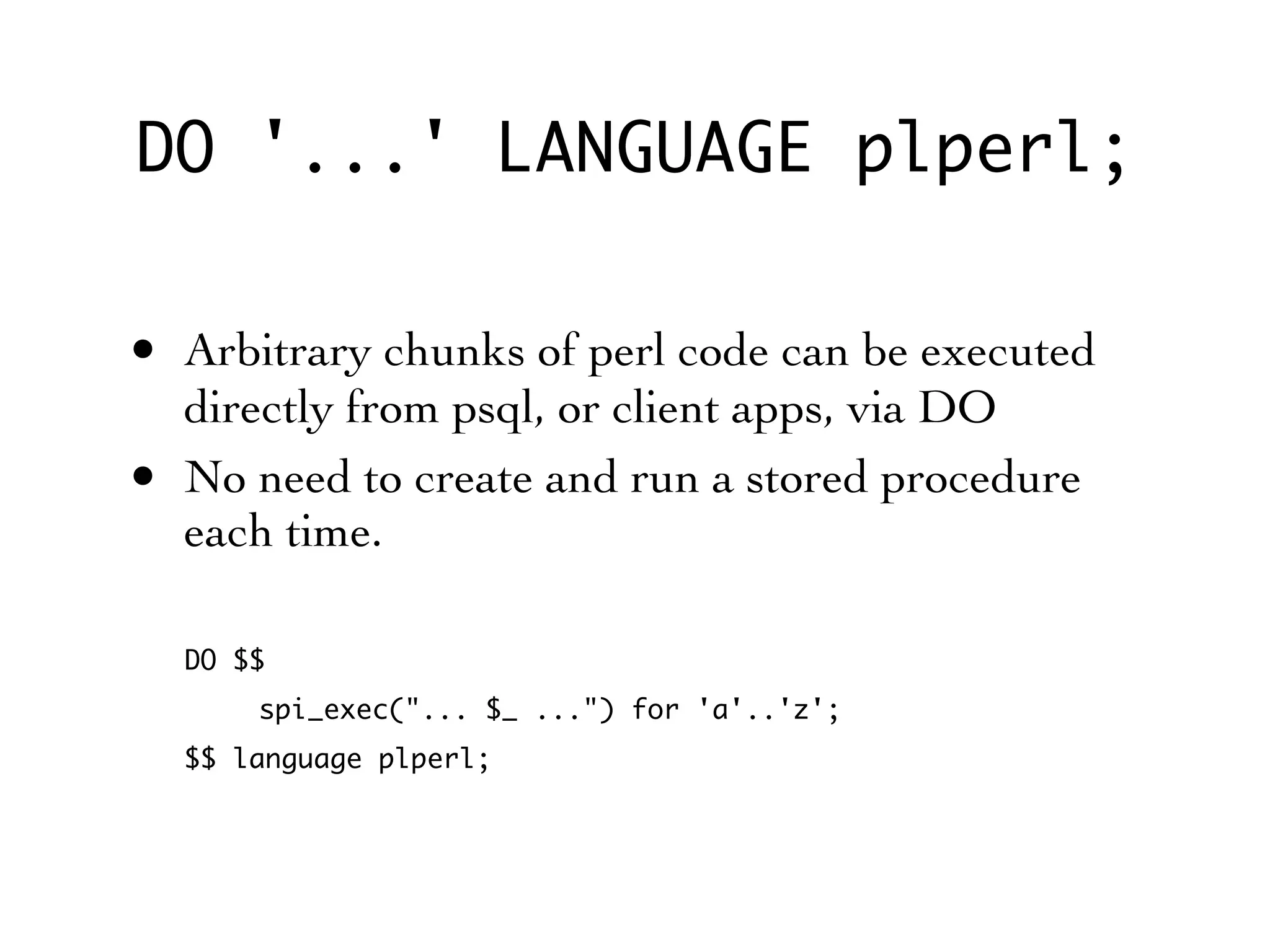
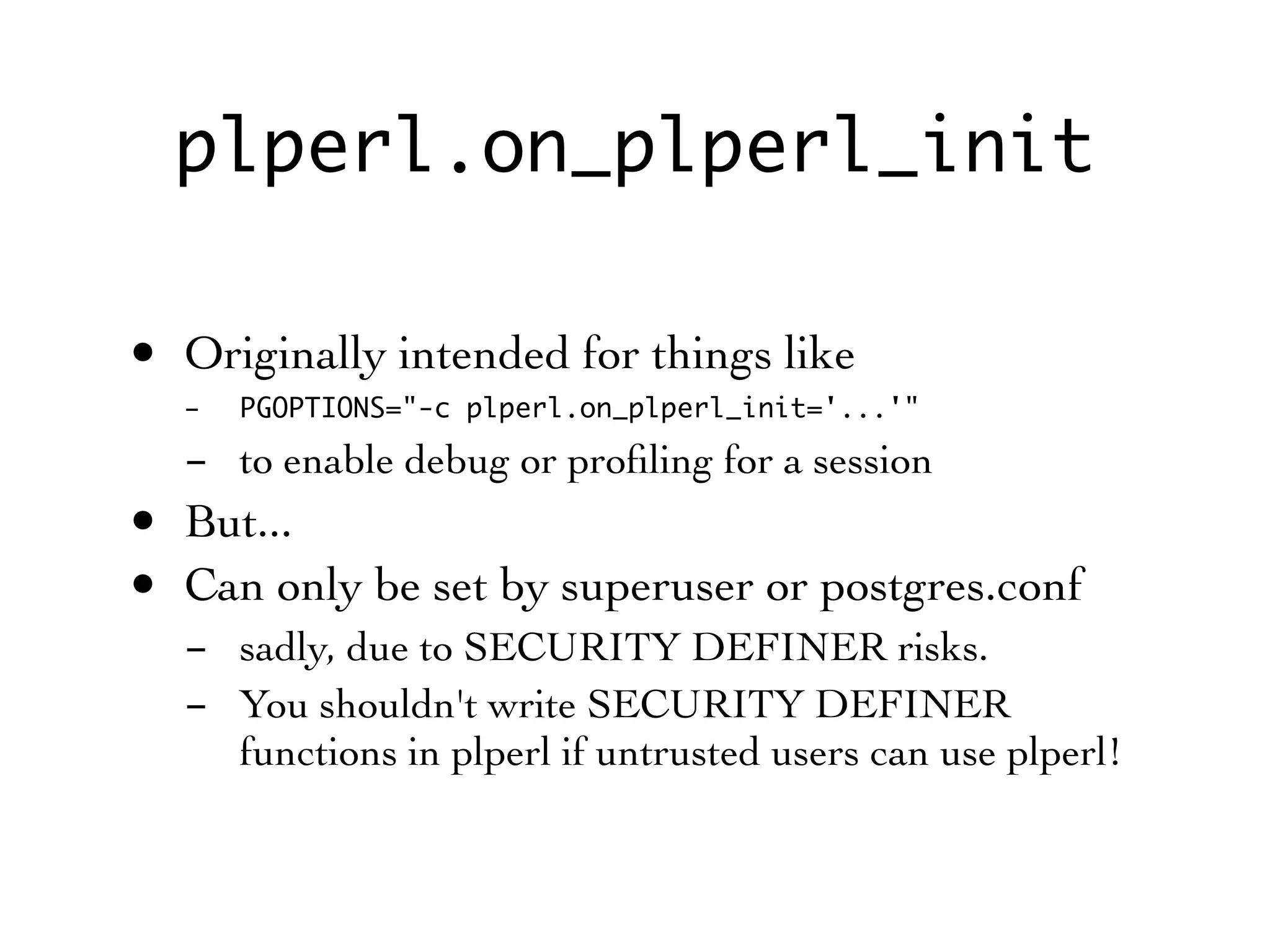
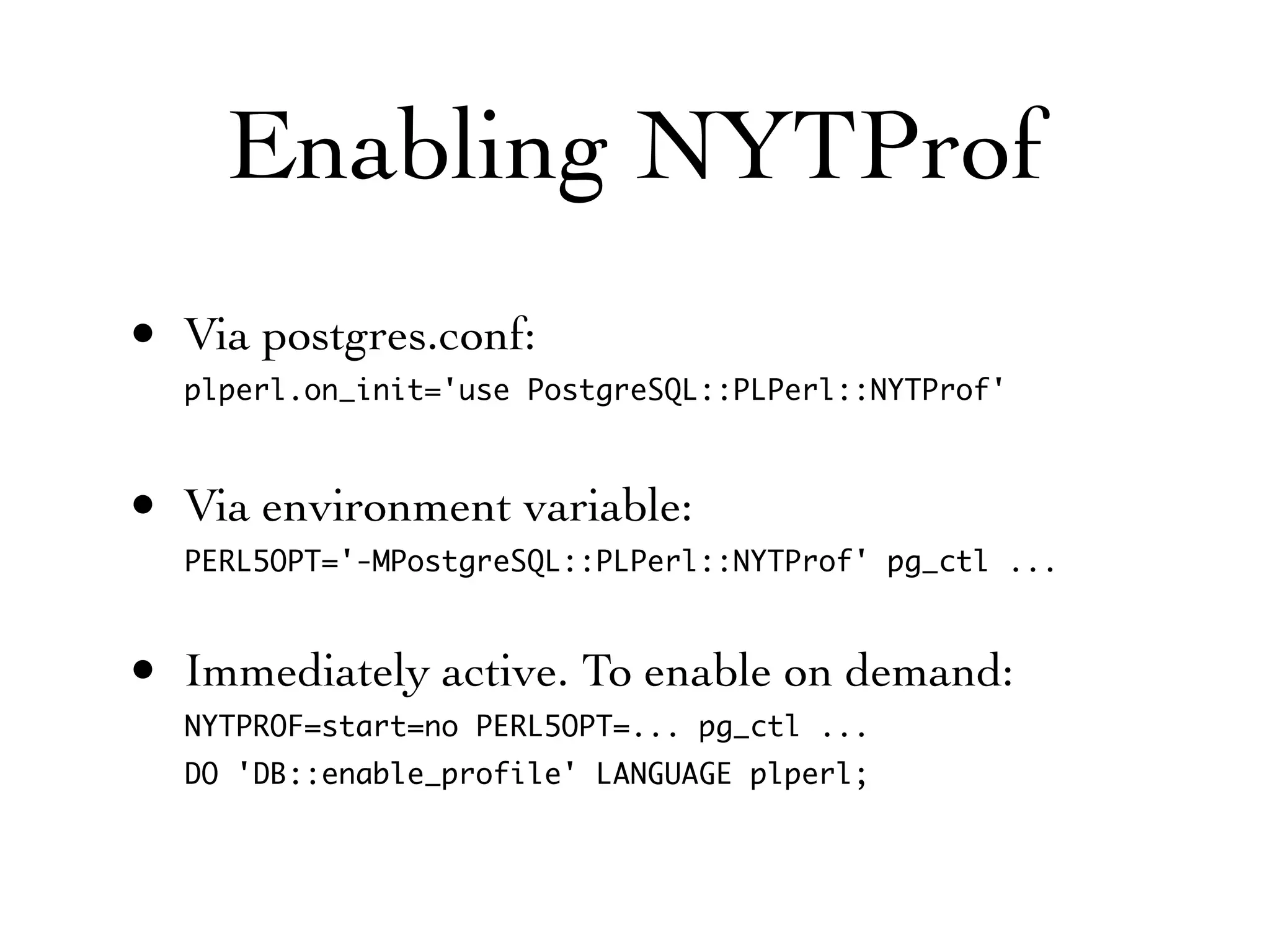
This document summarizes new features in PL/Perl for PostgreSQL 9.0. It introduces new built-in functions for quoting, encoding bytea, and checking if a value looks like a number. It describes improved support for arrays, trusted modules, and executing arbitrary Perl code using DO. The document also covers internal changes like removing the Safe module, new configuration options, and integration with the NYTProf profiler.



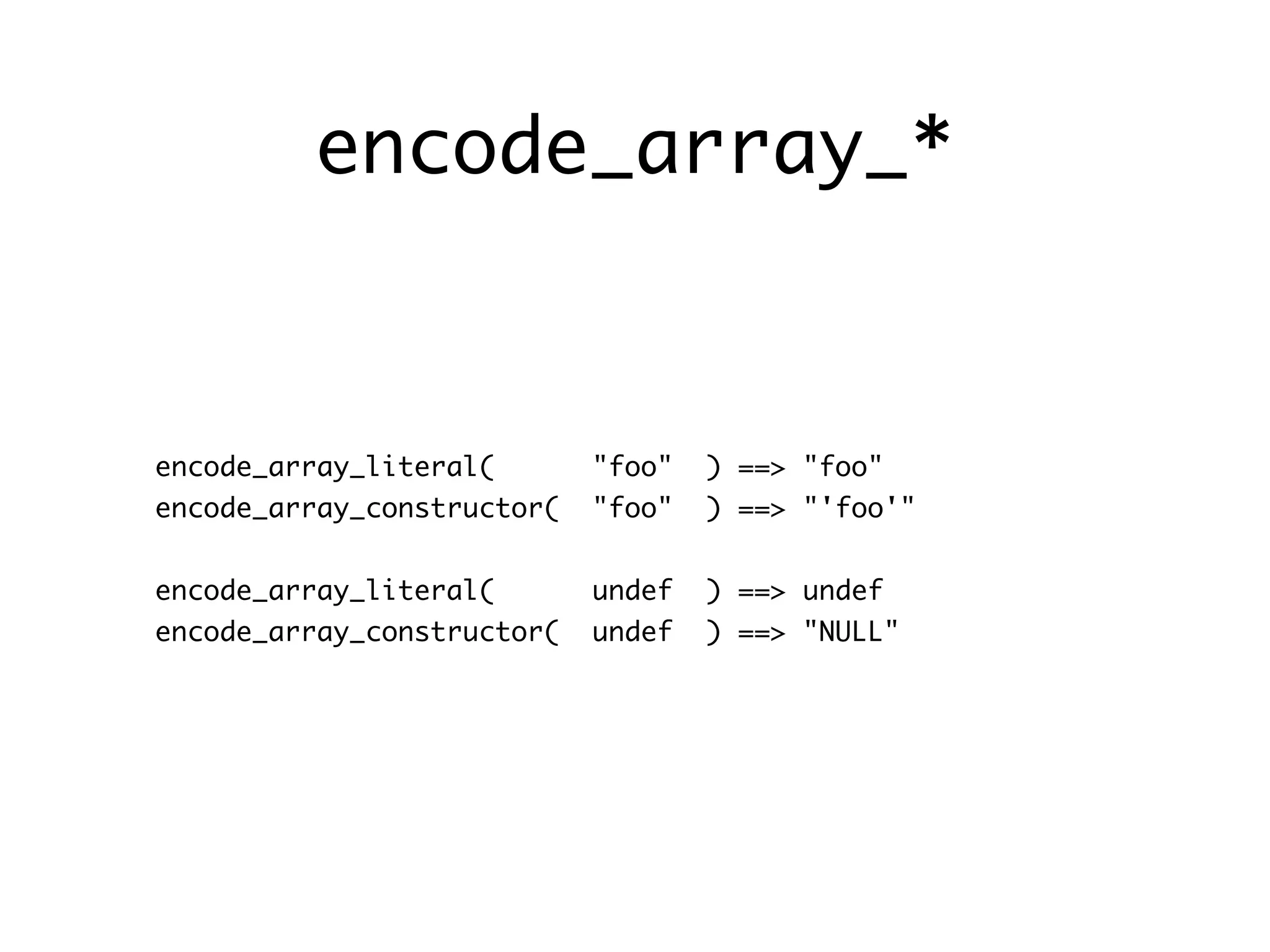
![encode_array_*
encode_array_literal( ["foo","bar"] )
==> "{"foo", "bar"}"
encode_array_constructor( ["foo","bar"] )
==> "ARRAY['foo', 'bar']"
encode_array_literal( [1,[2,[undef]]] )
==> "{"1", {"2", {NULL}}}"
encode_array_constructor( [1,[2,[undef]]] )
==> "ARRAY['1', ARRAY['2', ARRAY[NULL]]]"](https://image.slidesharecdn.com/plperl90-201004-100530163625-phpapp01/75/PL-Perl-New-Features-in-PostgreSQL-9-0-9-2048.jpg)