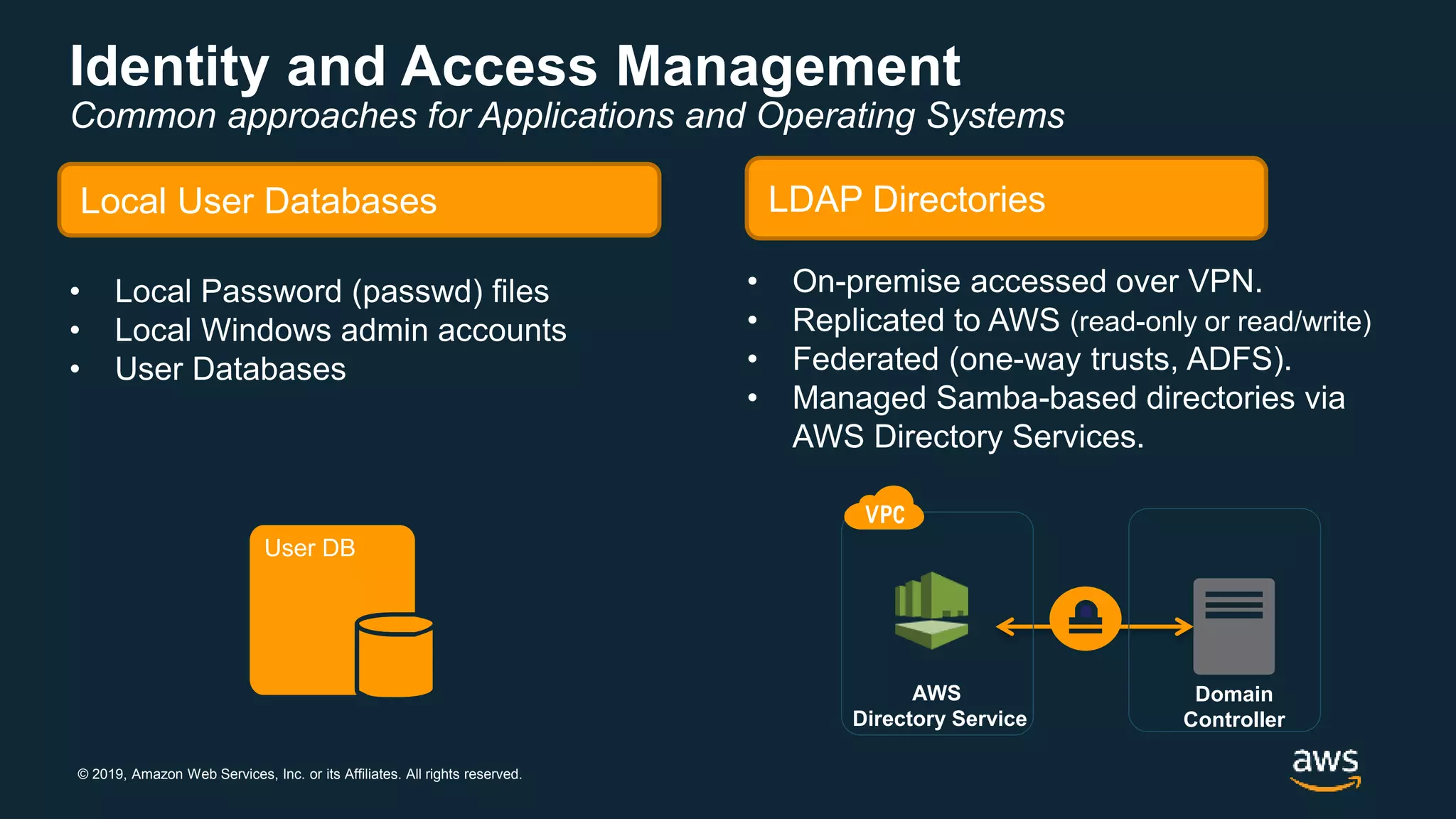
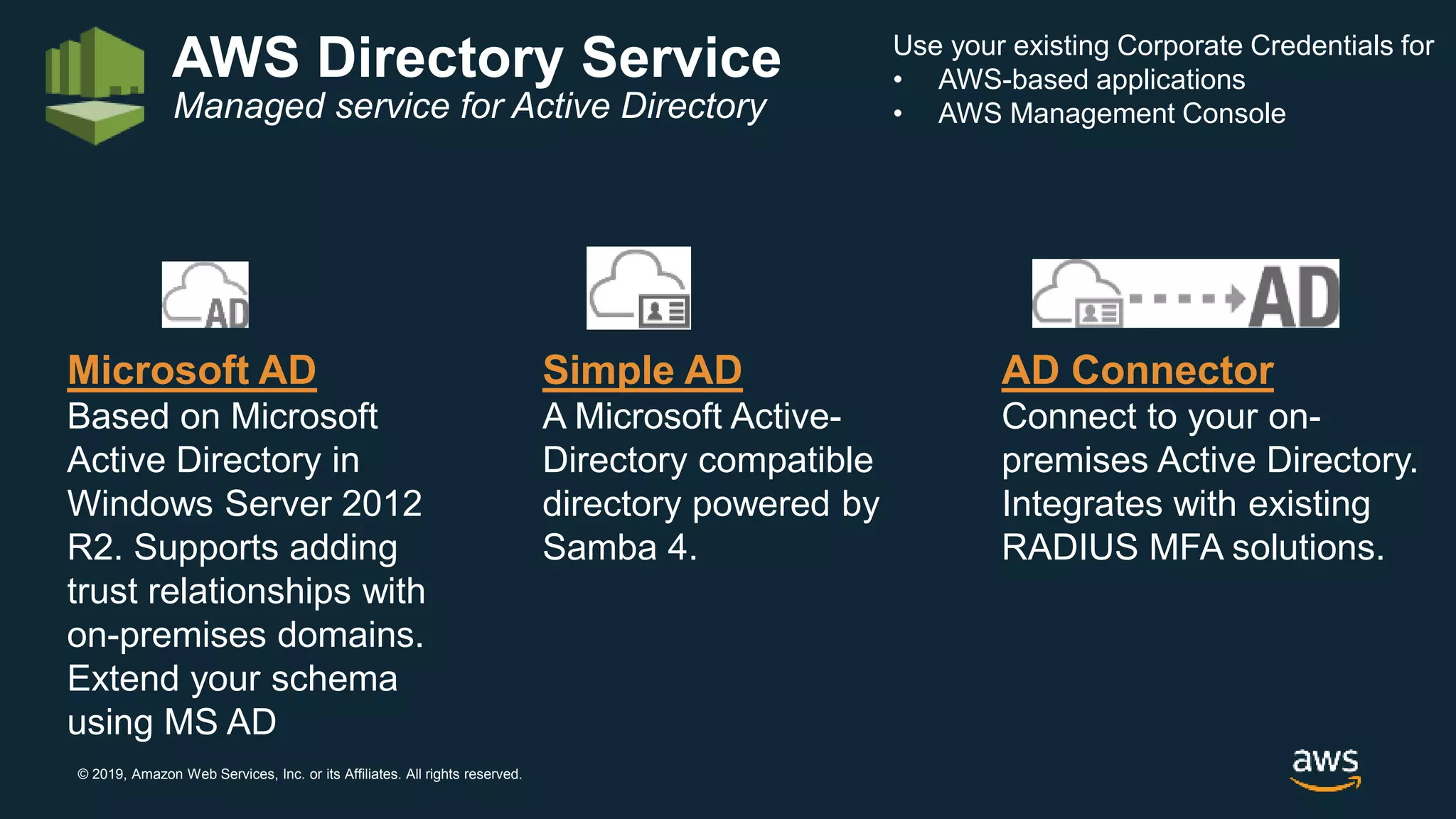
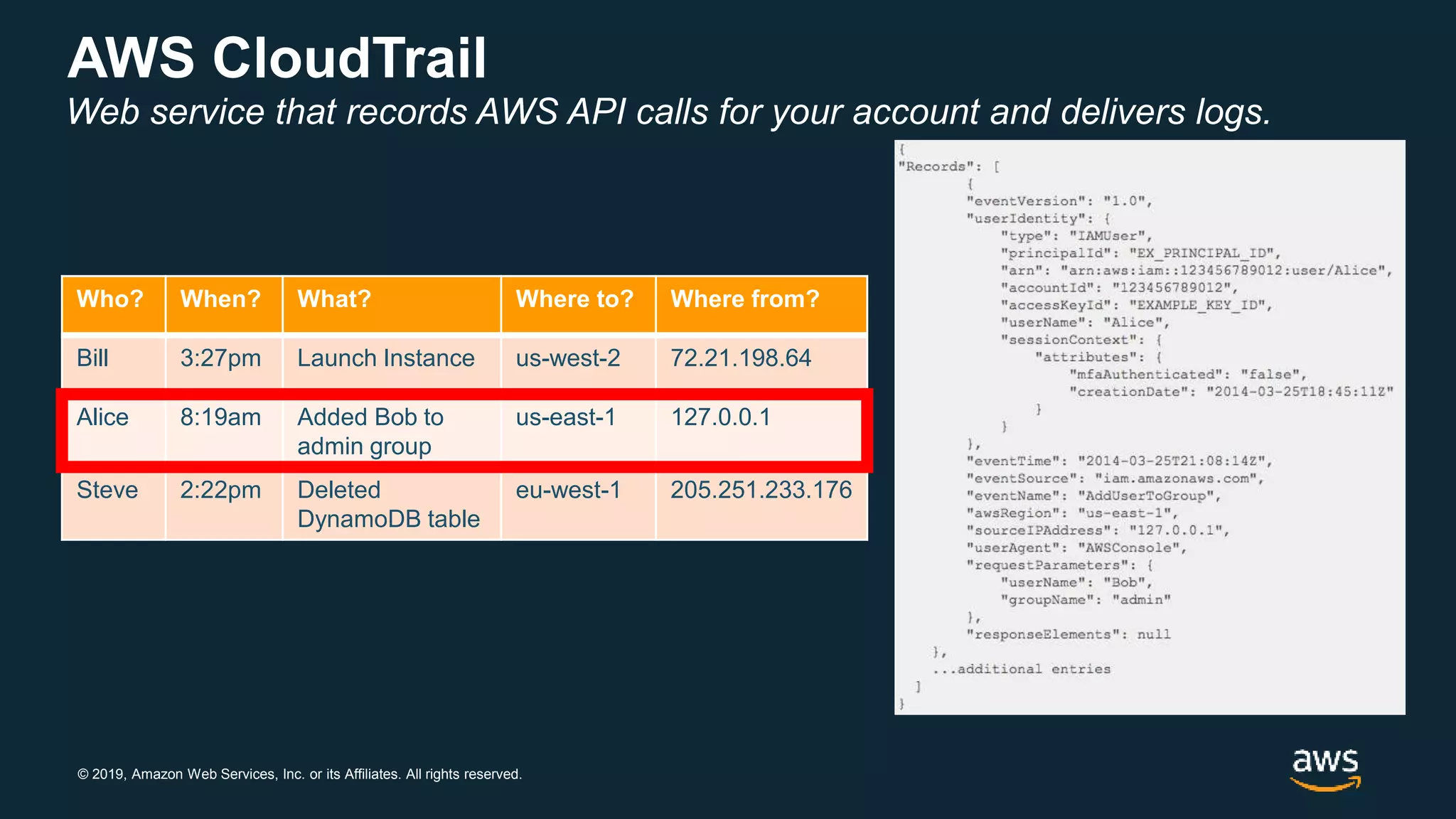
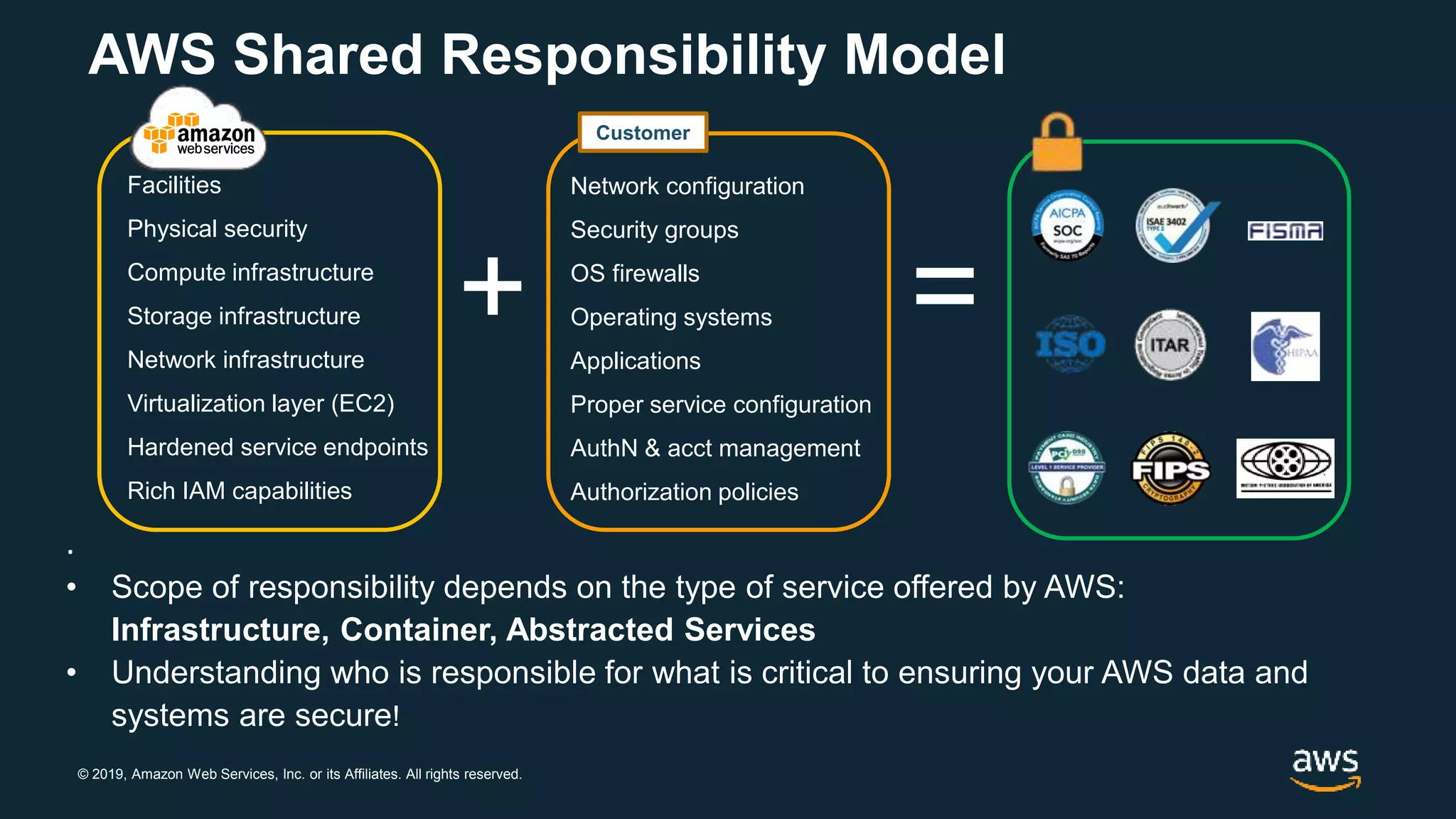
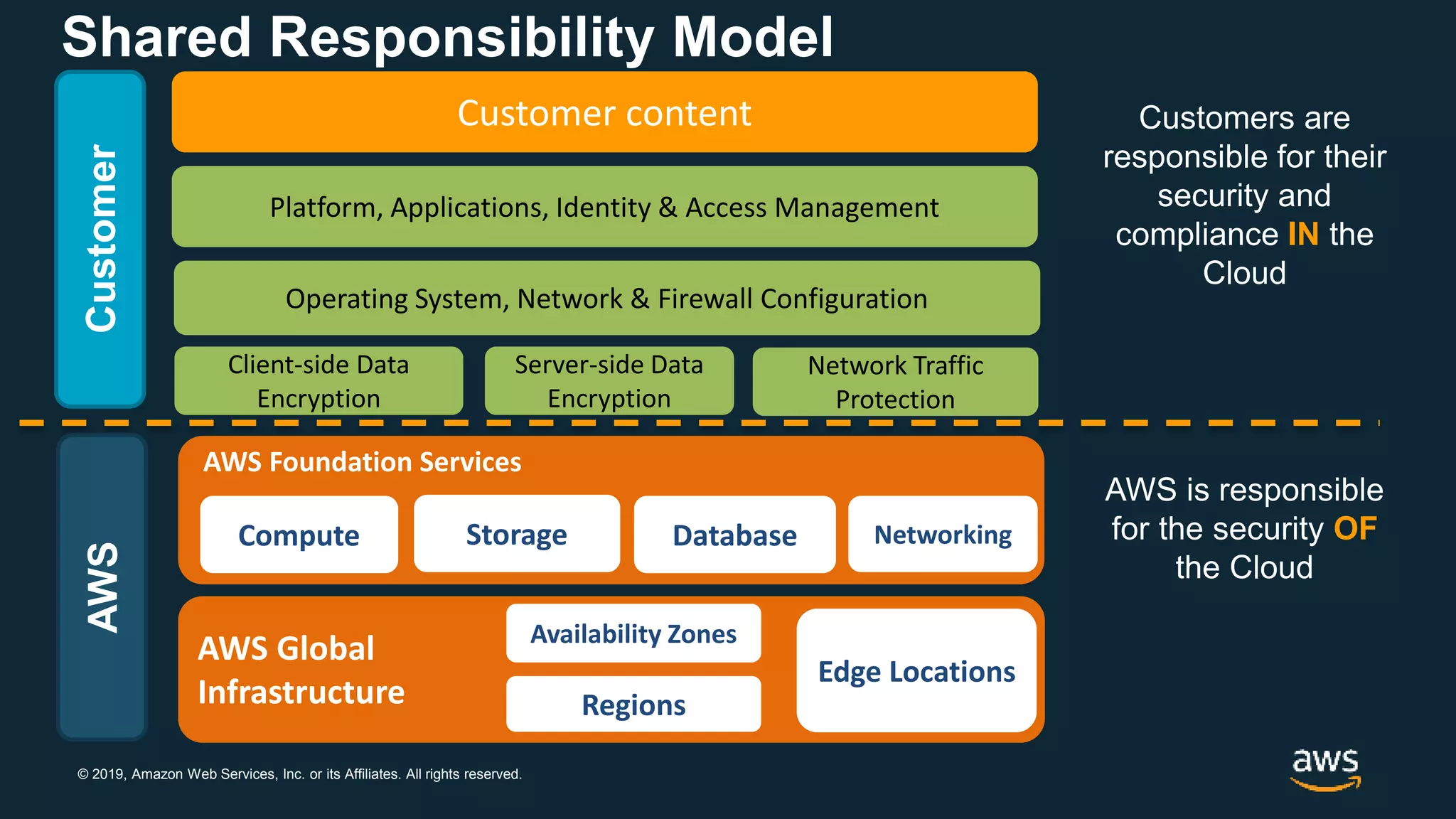
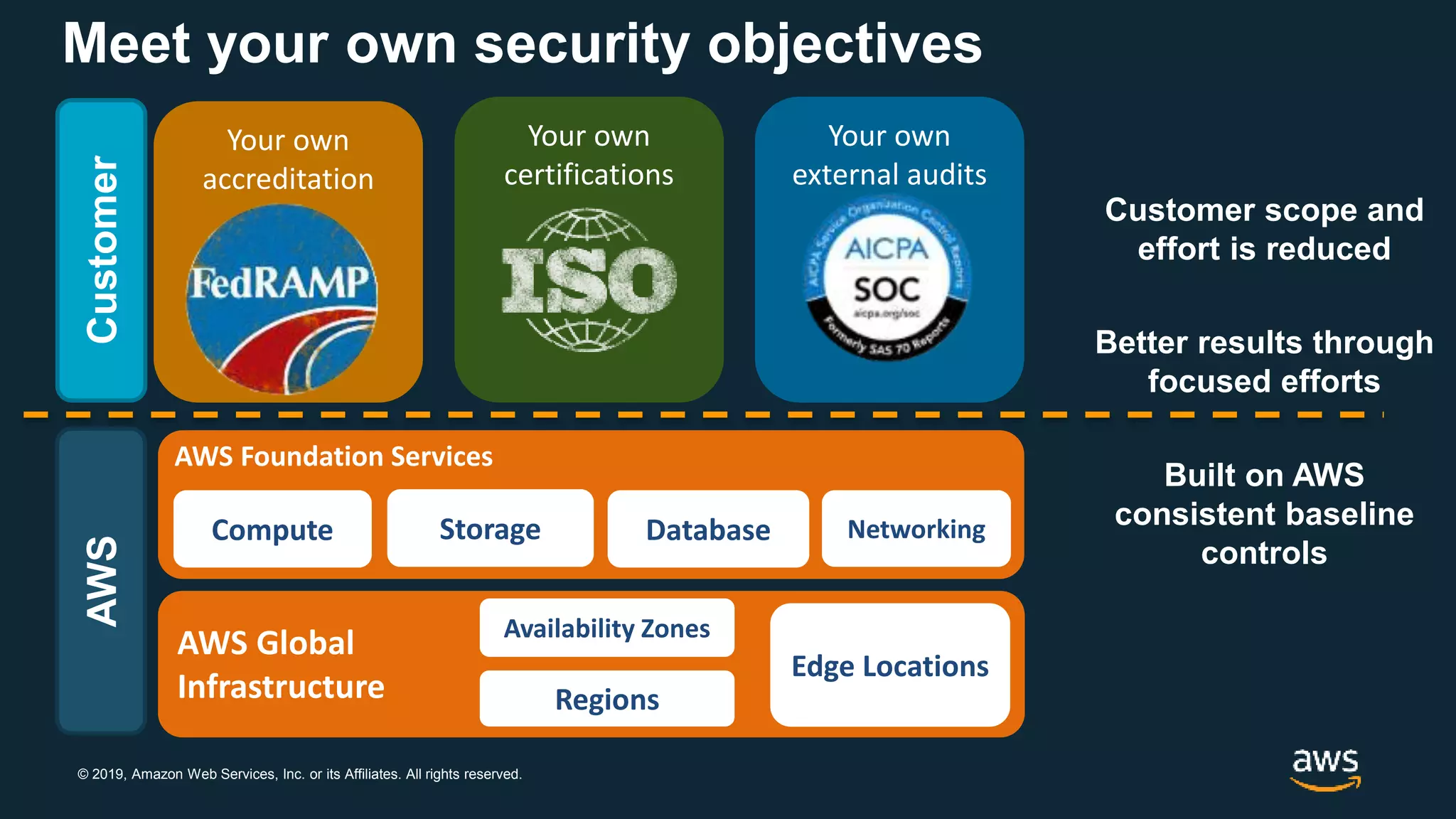
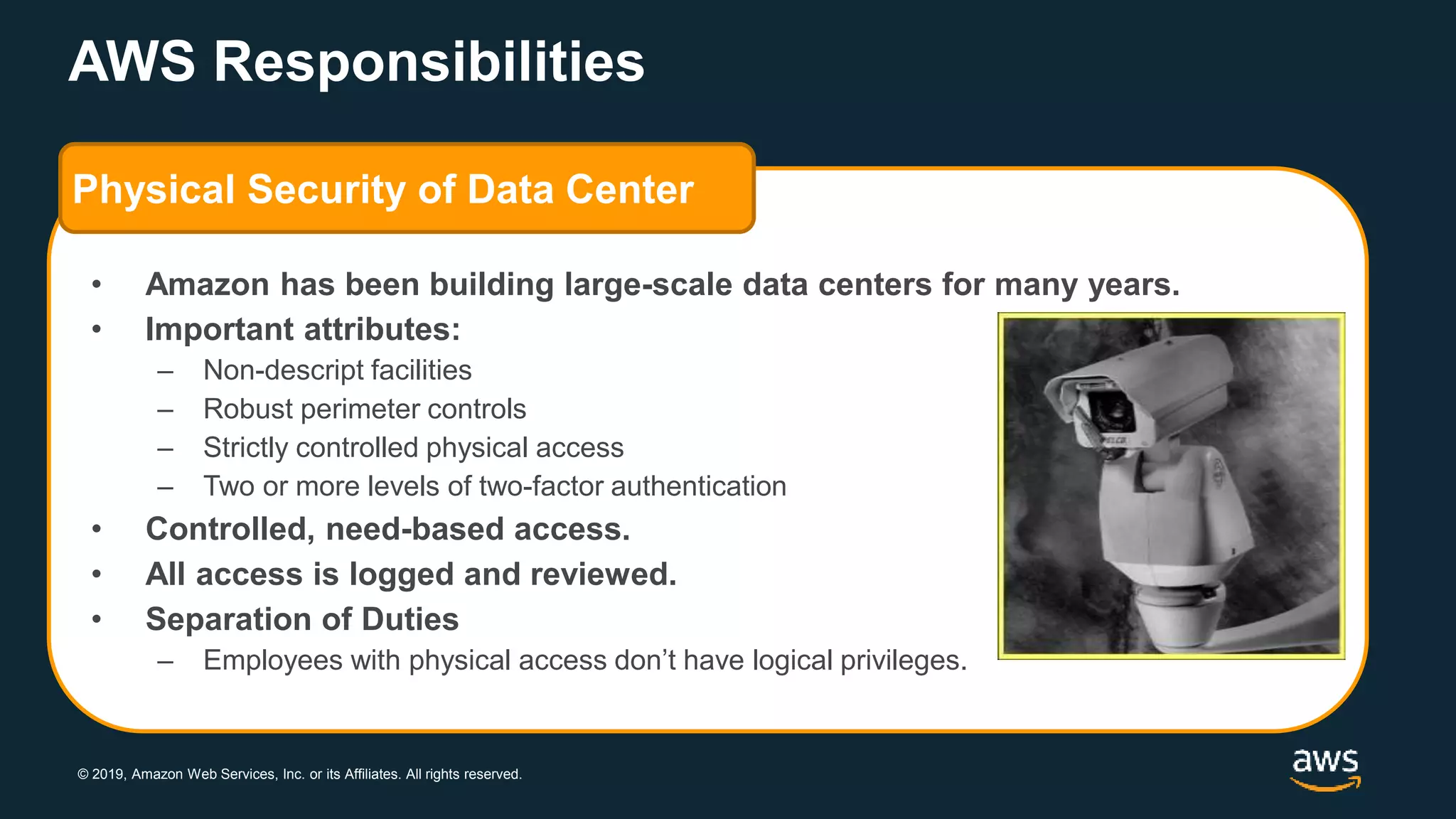
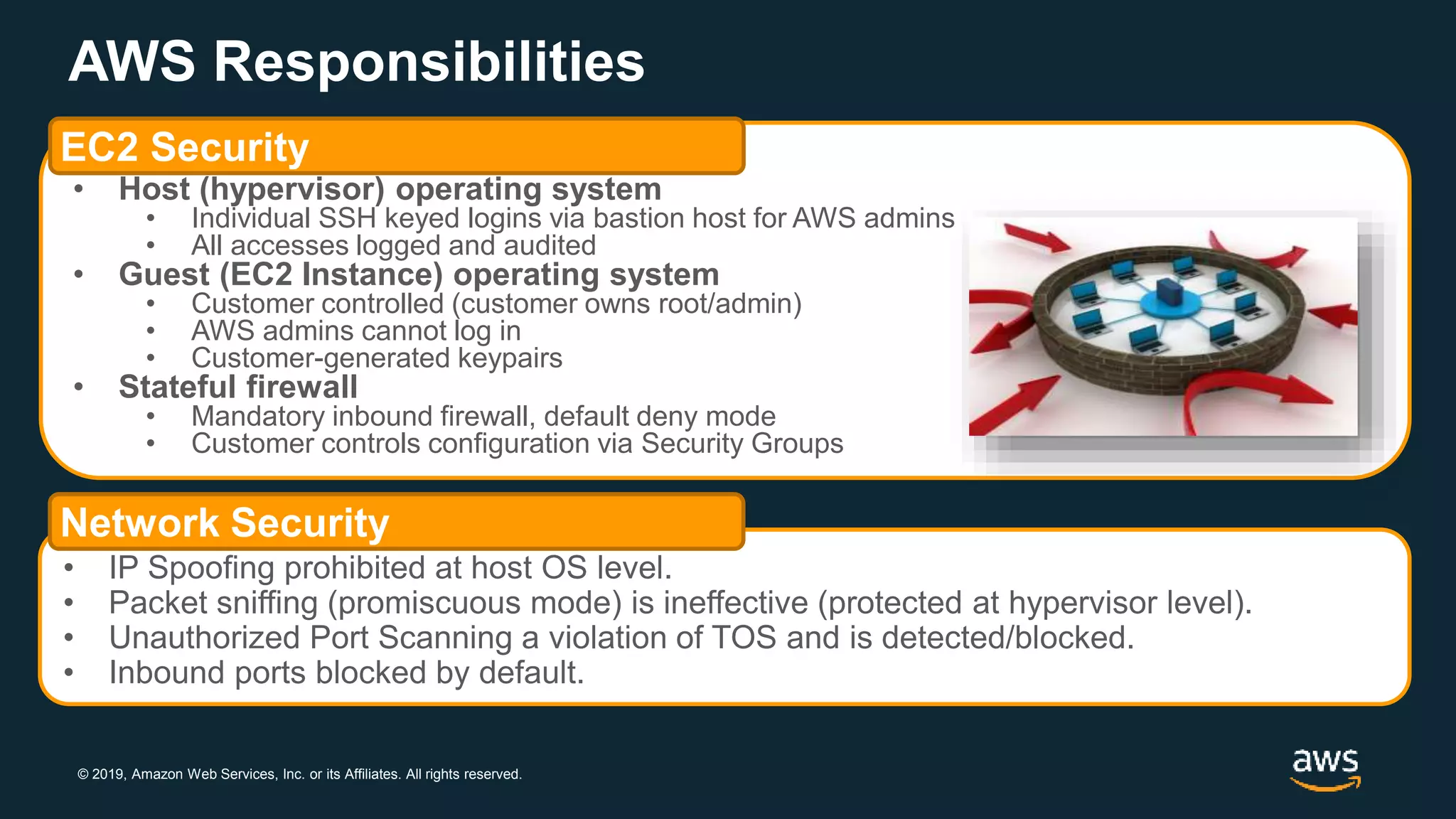
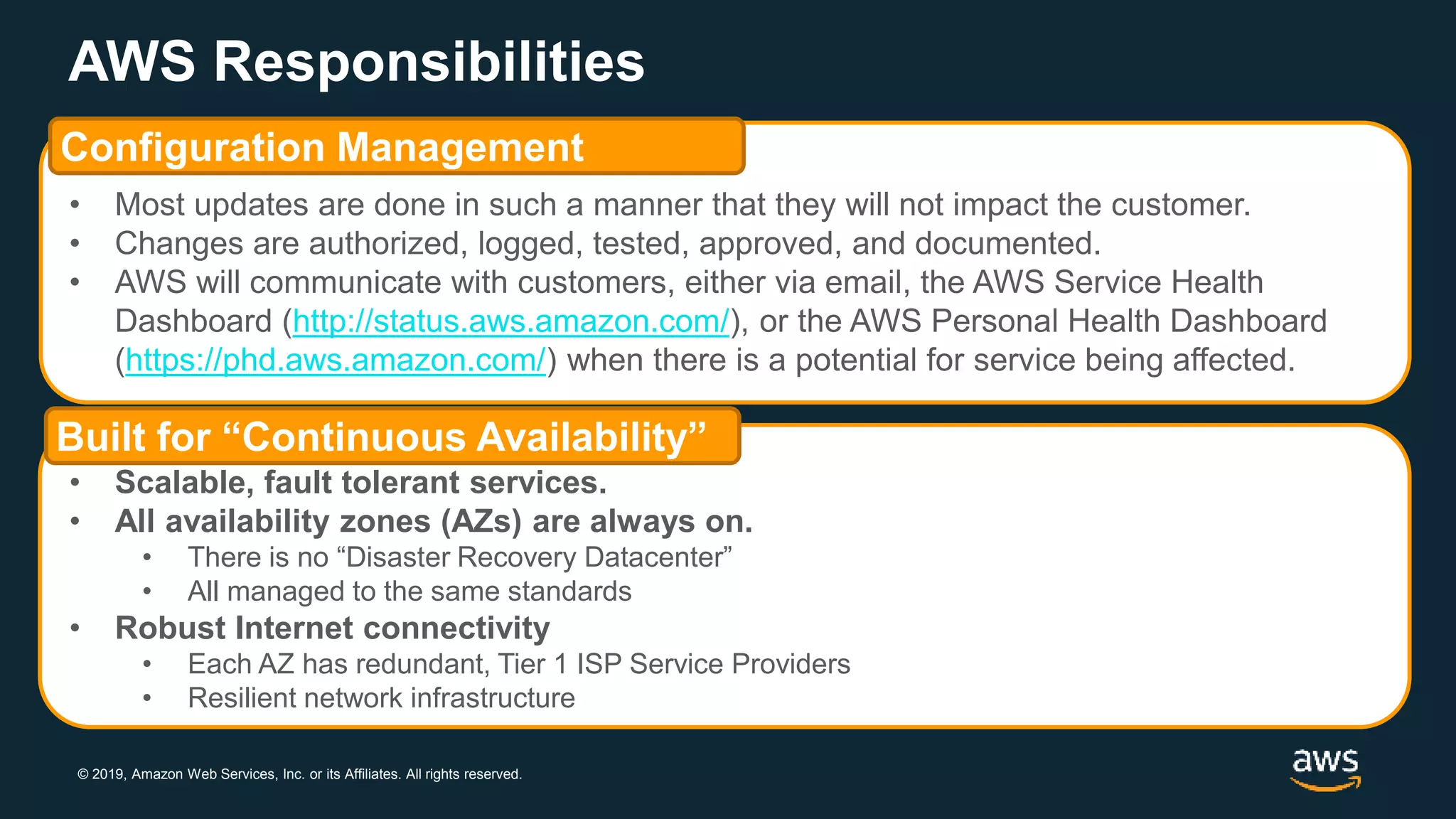
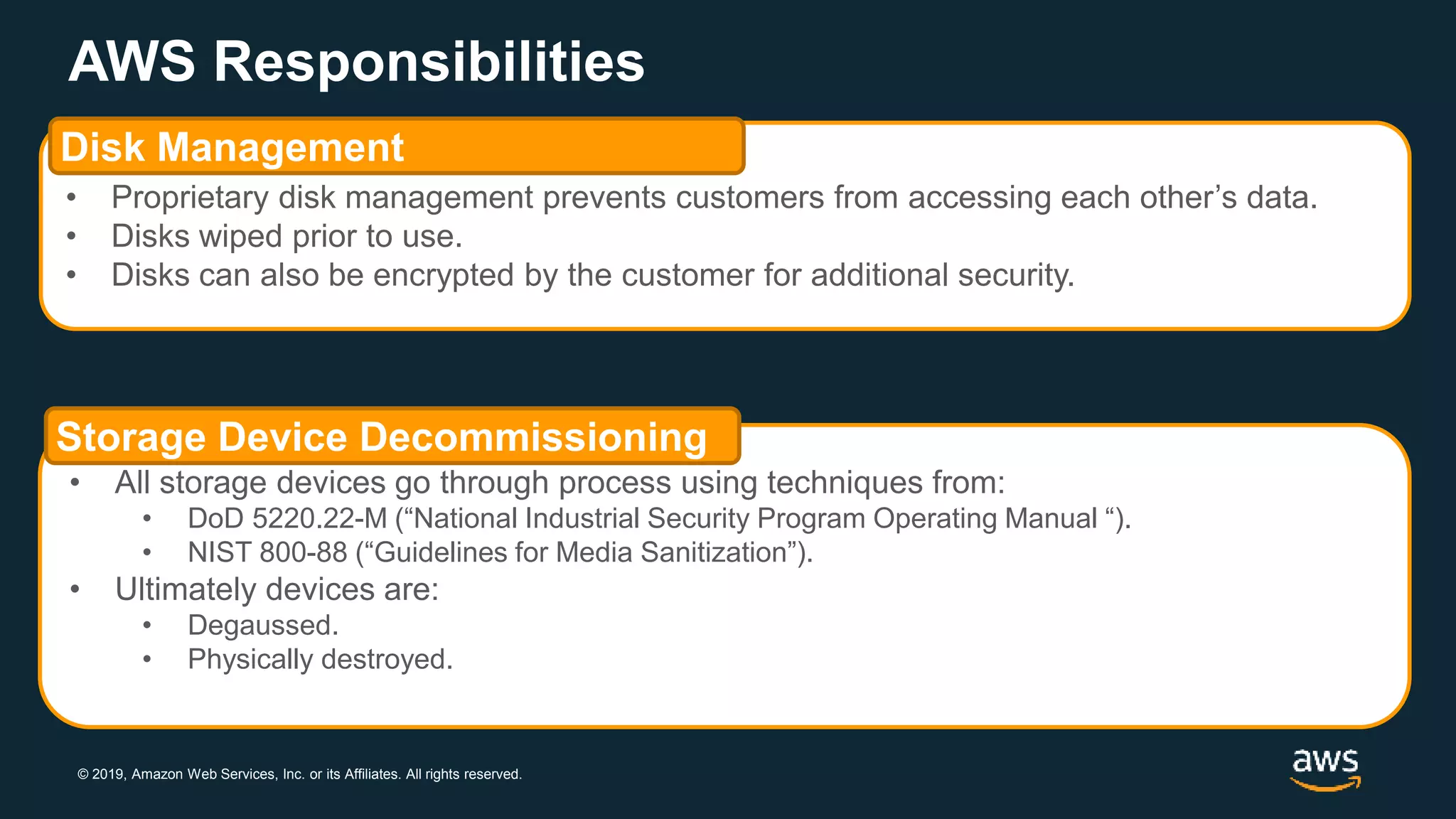
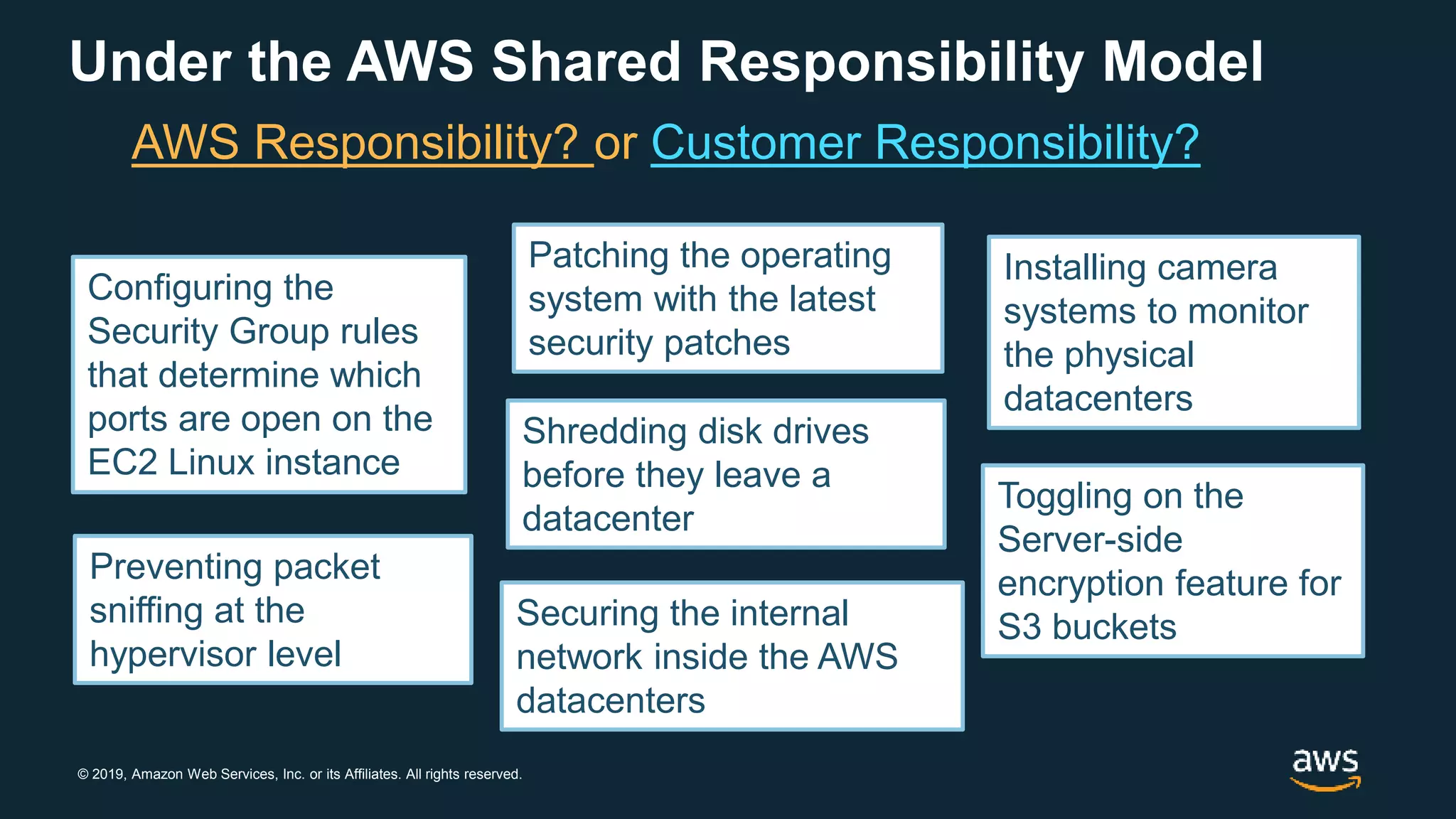
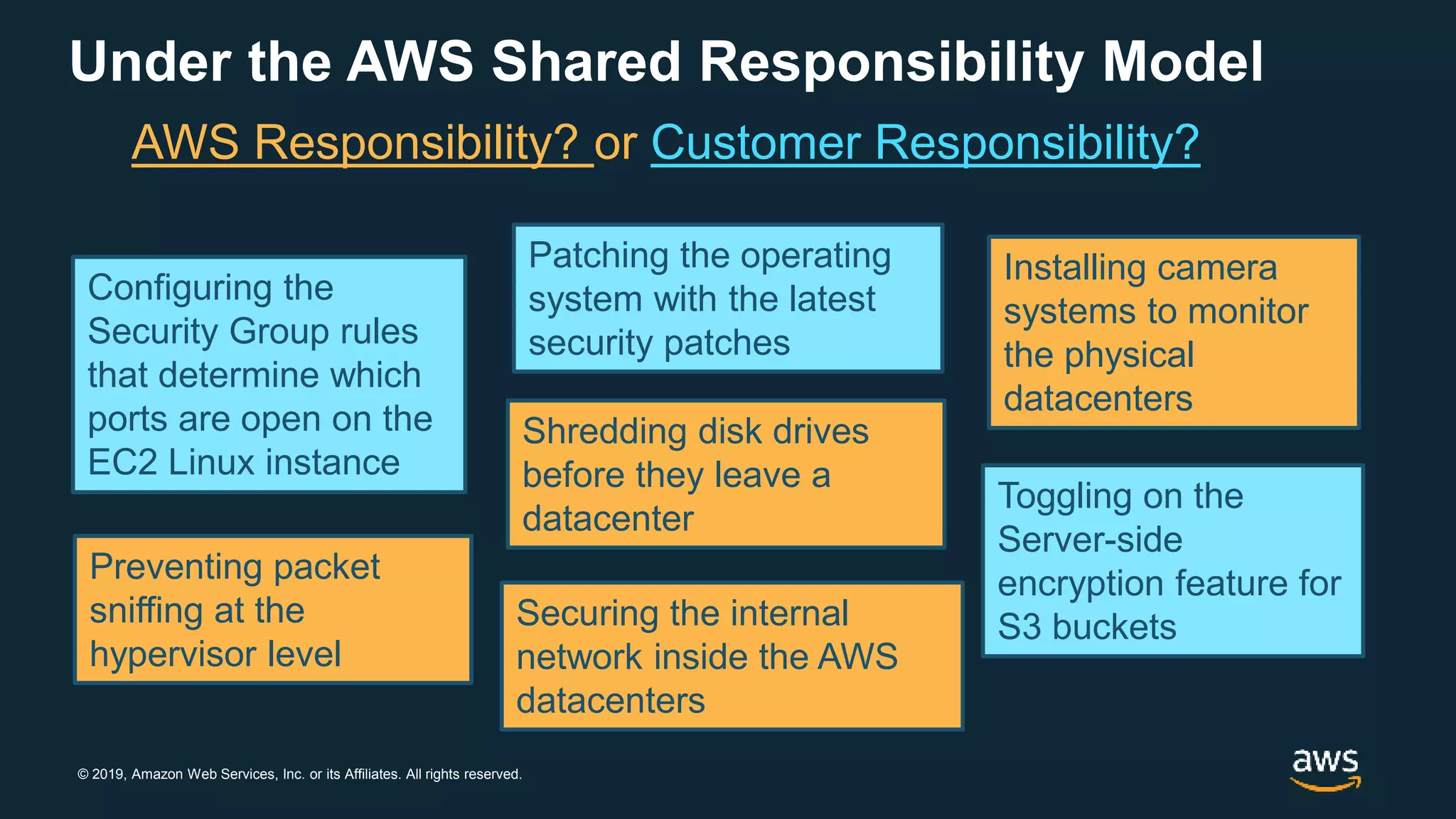
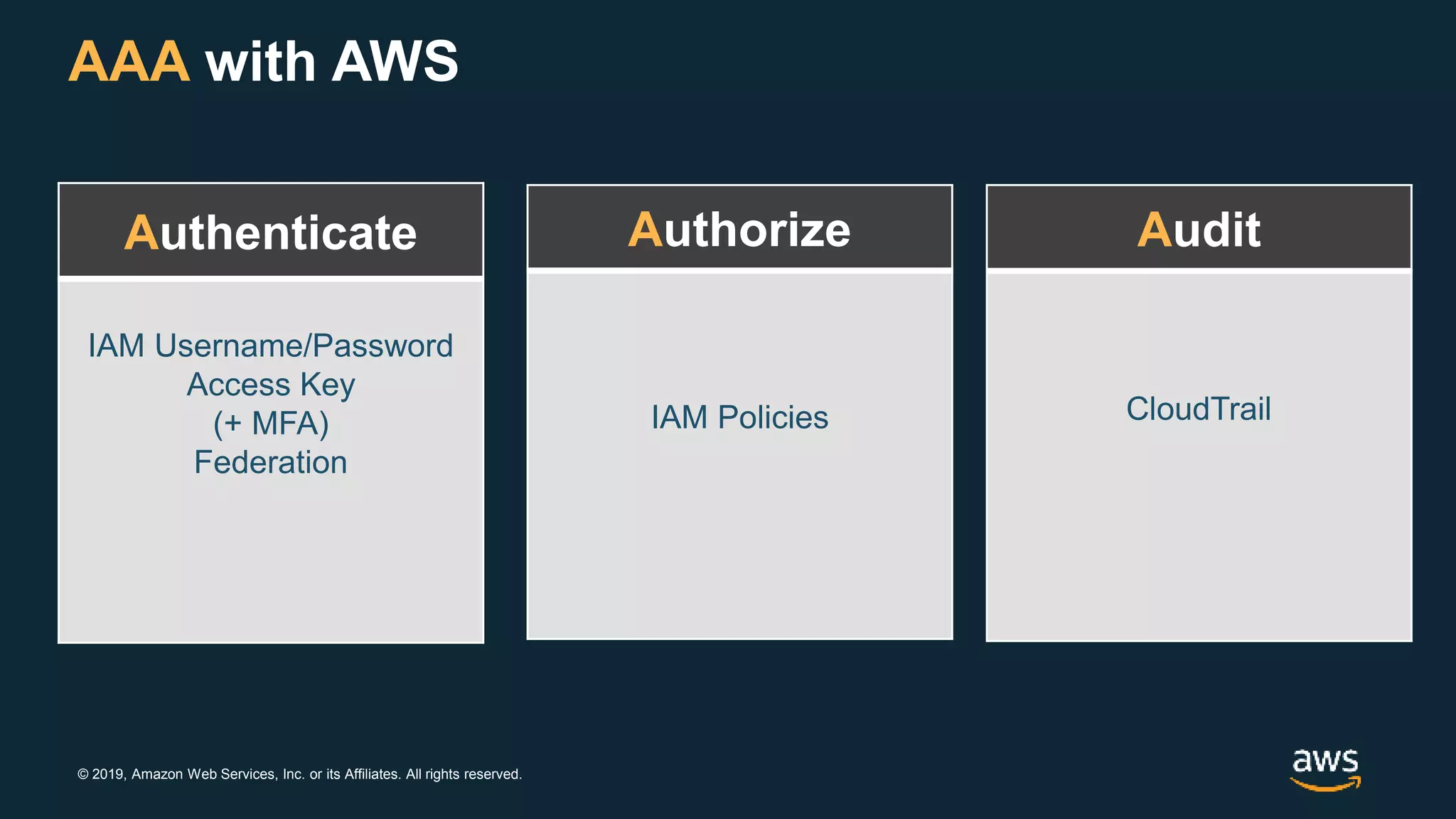
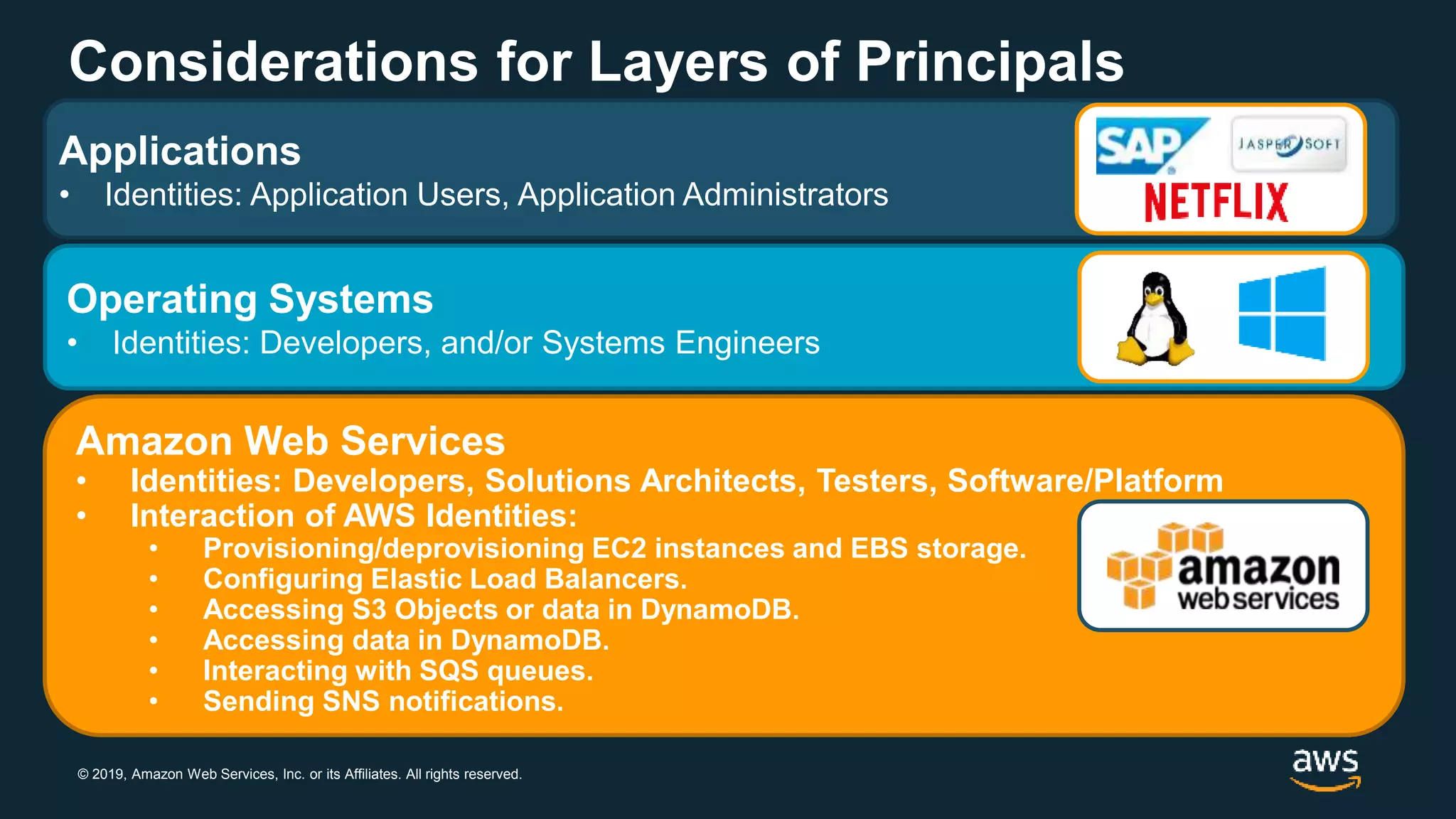
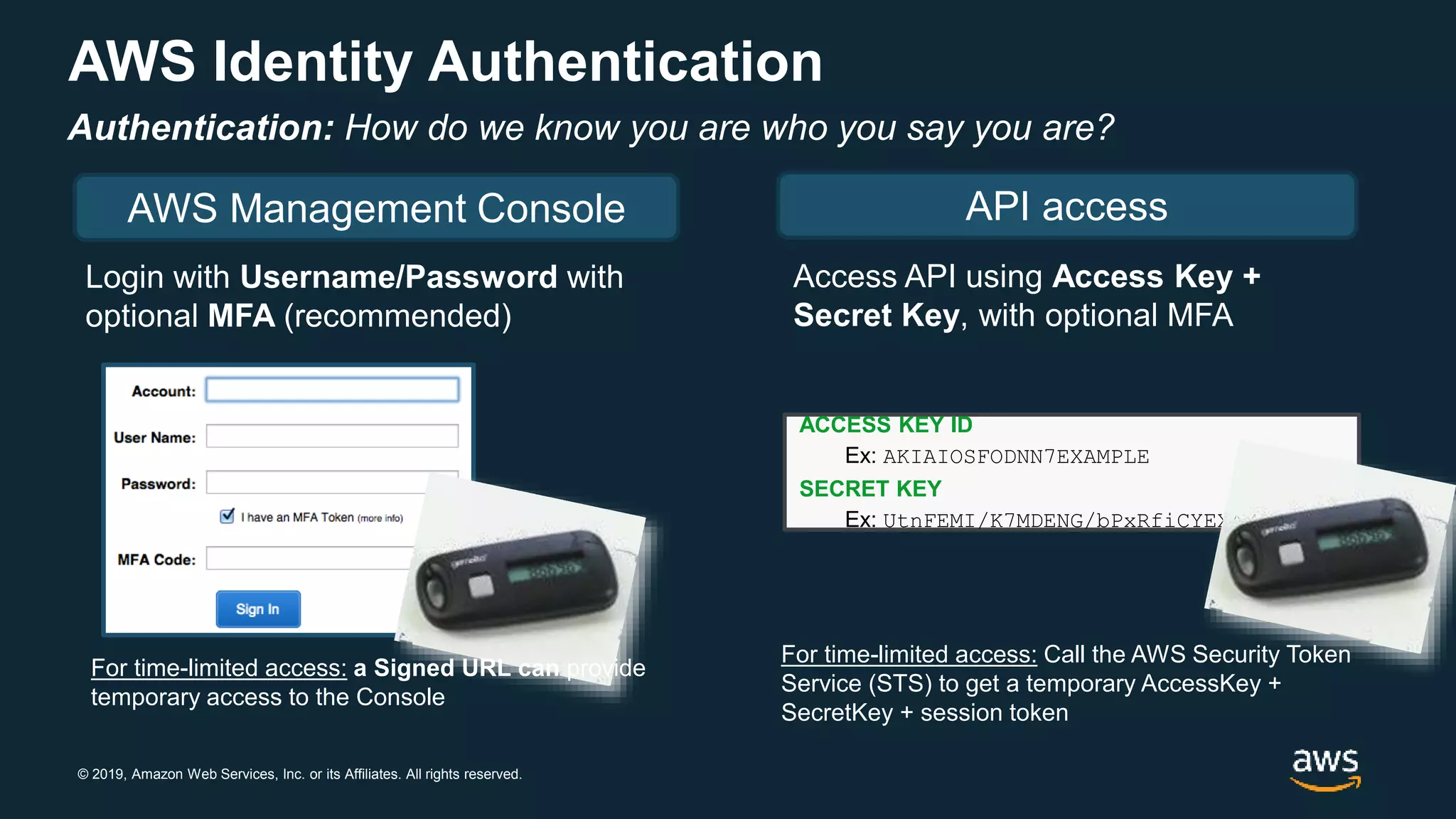
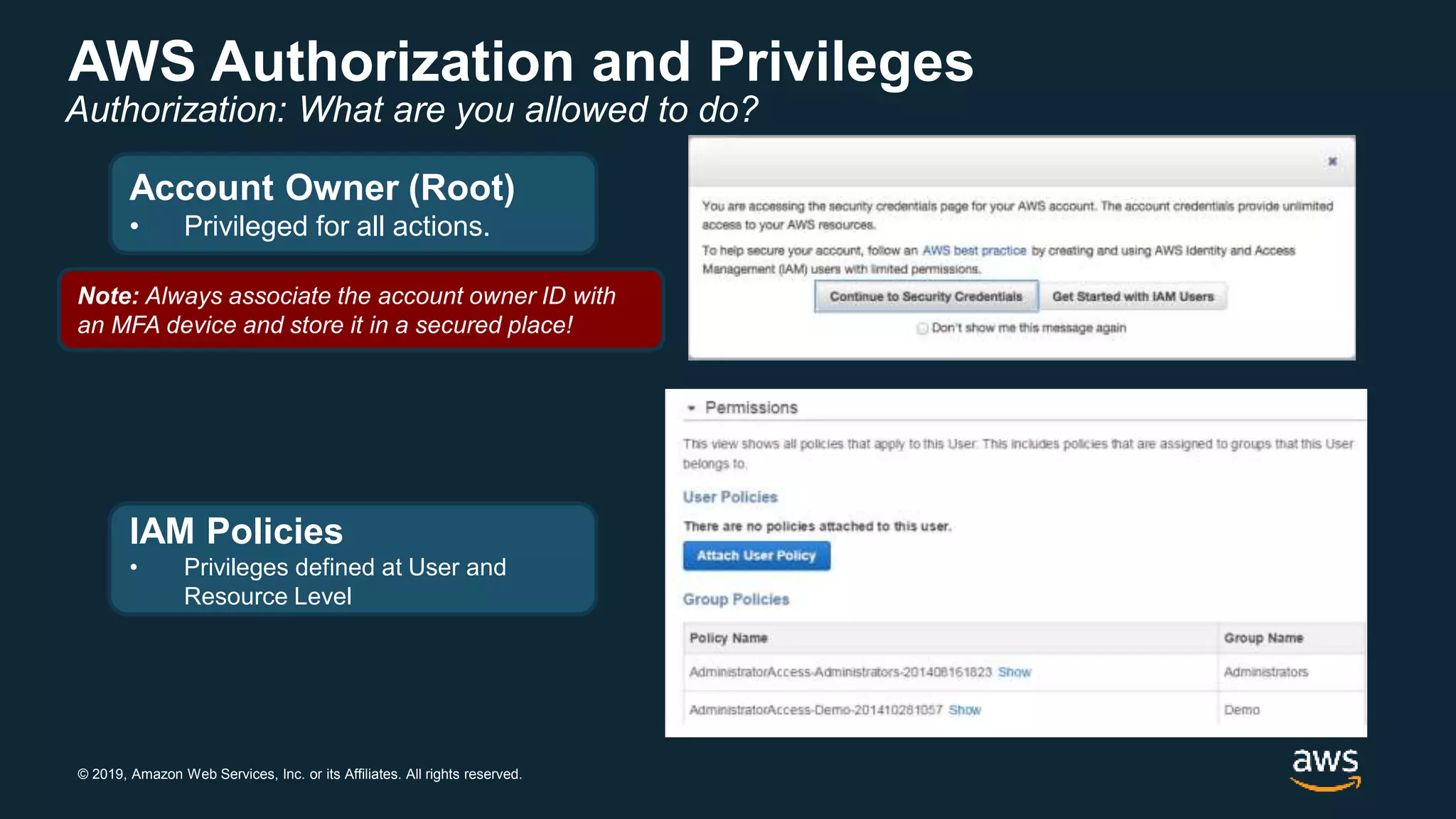
The document provides an overview of AWS cloud security concepts, including the shared responsibility model and identity and access management (IAM). It discusses how AWS is responsible for security of the cloud, including physical and network security of data centers, while customers are responsible for security in the cloud, such as operating systems and applications. The document also describes IAM principles for authentication, authorization, and auditing using tools like IAM users, policies, and CloudTrail.






![© 2019, Amazon Web Services, Inc. or its Affiliates. All rights reserved.
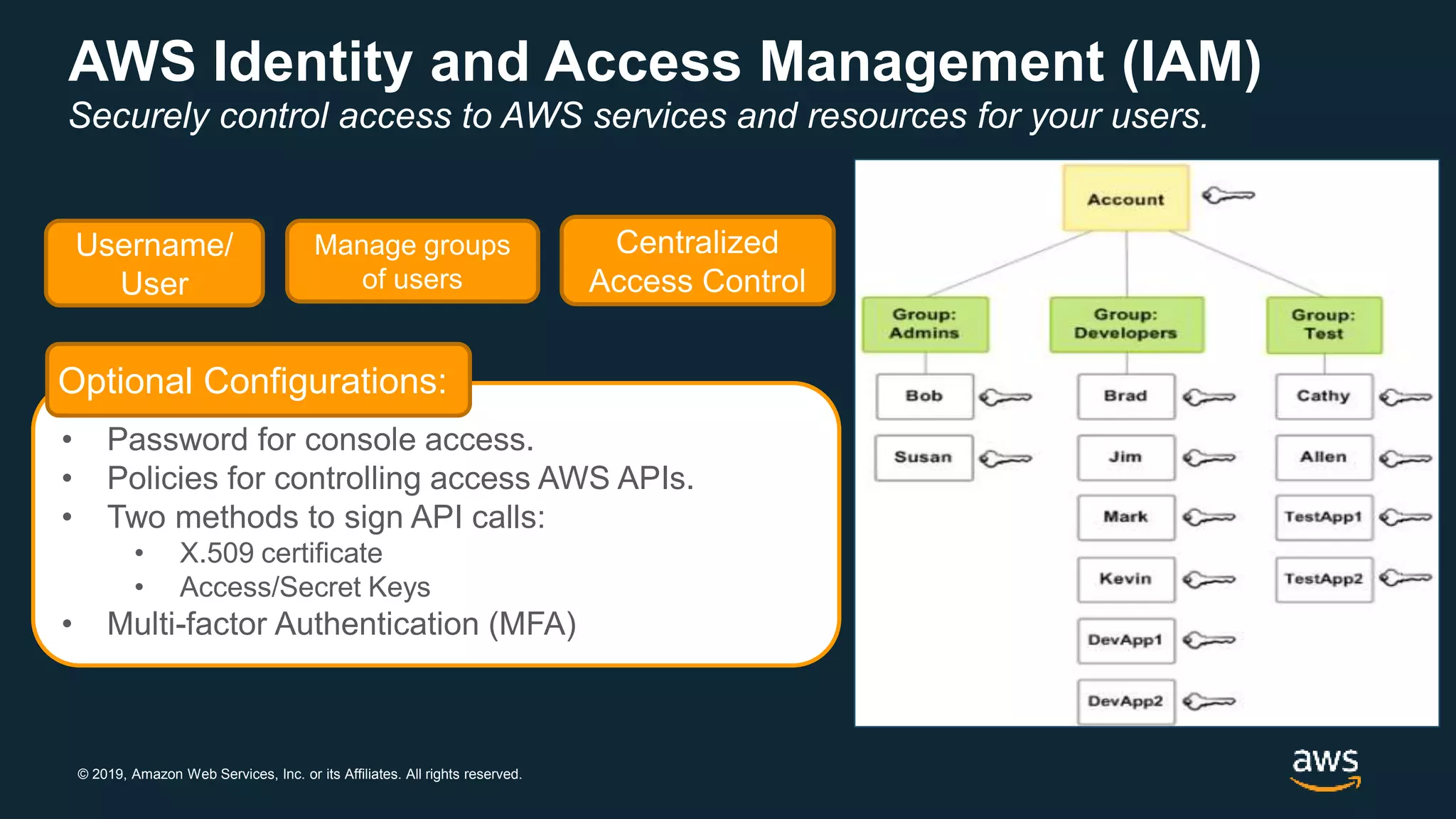
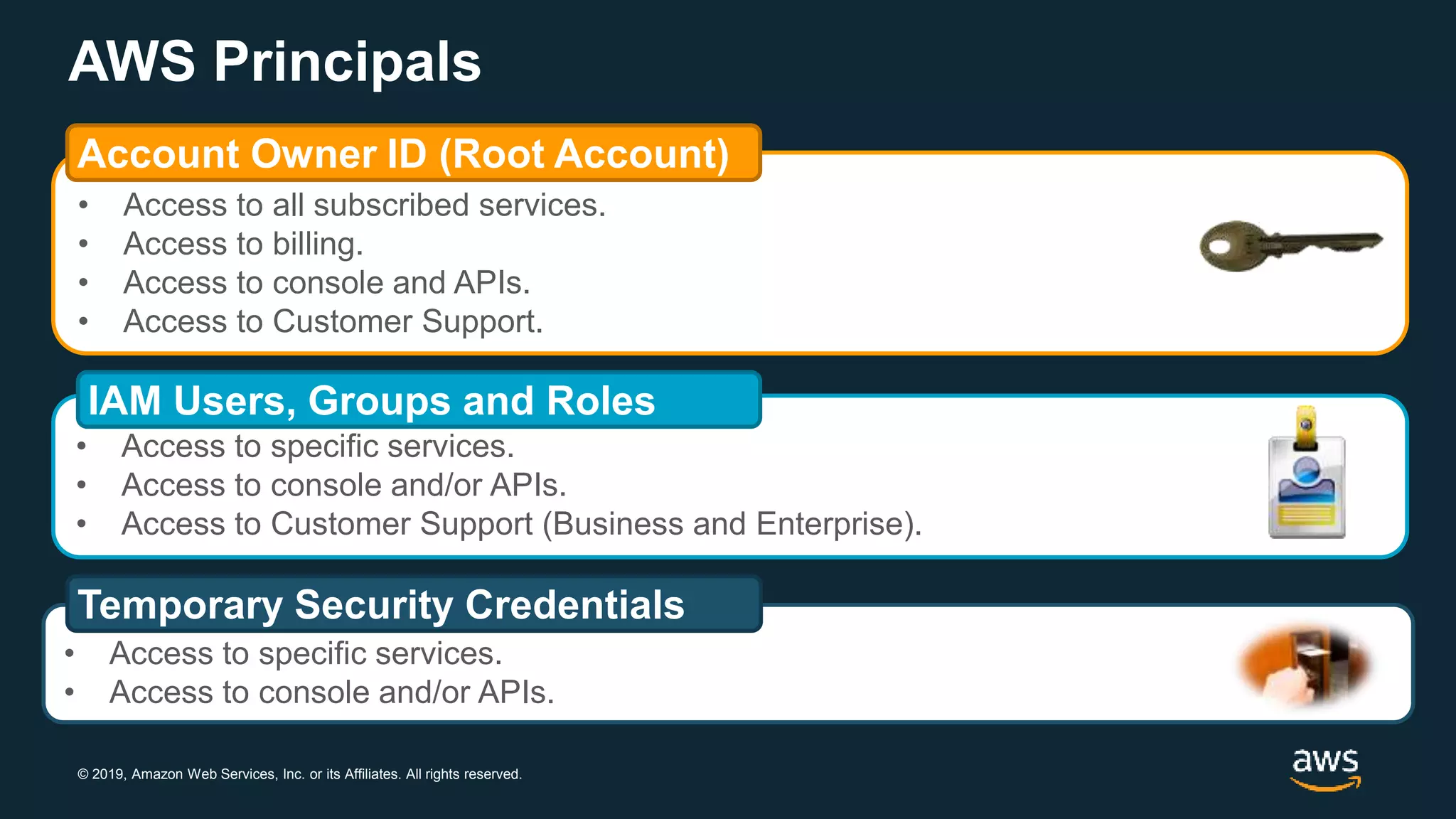
AWS IAM Hierarchy of Privileges
AWS Account
Owner (Root)
AWS IAM
User
Temporary
Security
Credentials
Permissions Example
Unrestricted access to all
enabled services and
resources.
Action: *
Effect: Allow
Resource: *
(implicit)
Access restricted by
Group and User policies
Action:
[‘s3:*’,’sts:Get*’]
Effect: Allow
Resource: *
Access restricted by
generating identity and
further by policies used
to generate token
Action: [ ‘s3:Get*’ ]
Effect: Allow
Resource:
‘arn:aws:s3:::mybucket/*’
Enforce principle of least privilege with Identity and Access Management (IAM)
users, groups, and policies and temporary credentials.](https://image.slidesharecdn.com/new-module5-security-overview-191024205408/75/Pitt-Immersion-Day-Module-5-security-overview-25-2048.jpg)