Physics jeopardy review
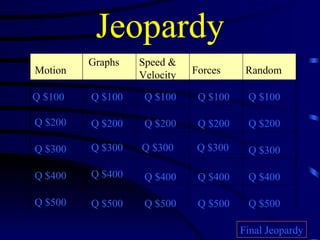
- 1. Jeopardy Motion Graphs Speed & Velocity Forces Random Q $100 Q $200 Q $300 Q $400 Q $500 Q $100 Q $100 Q $100 Q $100 Q $200 Q $200 Q $200 Q $200 Q $300 Q $300 Q $300 Q $300 Q $400 Q $400 Q $400 Q $400 Q $500 Q $500 Q $500 Q $500 Final Jeopardy
- 2. $100 Question from Motion A place or object used for comparison to determine if something is in motion
- 3. $100 Answer from Motion What is a reference point
- 4. $200 Question from Motion A car travels 100 miles north. It turns and heads 150 miles south. What is the distance the car traveled? What is the displacement of the car?
- 5. $200 Answer from Motion 250 miles total distance 50 miles South displacement
- 6. $300 Question from Motion Describe the motion in the following diagram. Assume the object is travelling from LEFT TO RIGHT . . . . . . . . . . . . . . . . . …………|.|
- 7. $300 Answer from Motion . . . . . . . . . . . . . . . . . …………|.| Constant Speeding up Slowing down Constant Stop
- 8. $400 Question from Motion A flea is sitting on the back of a dog. The dog walks in front of a person seated in a chair. The flea thinks the dog is A) Moving B) Not Moving The person thinks the flea is A) Moving B) Not Moving Explain why
- 9. $400 Answer from Motion The flea thinks the dog is B) Not Moving The flea is not changing position relative to the dog The person thinks the flea is A) Moving The flea changes position relative to the person as the dog moves past the chair
- 10. $500 Question from Motion How far has this object traveled after 16 seconds? What is the total distance traveled? What is the displacement?
- 11. $500 Answer from Motion 8 meters at 16 seconds 16 meters total distance 0 meters displacement
- 12. $100 Question from Graphs What kind of motion graph is this? Describe the motion in this graph
- 13. $100 Answer from Graphs Distance/Time graph Constant speed of 10 meters/second
- 14. $200 Question from Graphs Describe the motion in this graph
- 15. $200 Answer from Graphs Waits 3 second to begin moving, moves at constant speed of 1m/s for 8 seconds, does not move for 5 seconds, moves at constant speed of 3m/s for 2 seconds, pauses for 2 seconds, moves at constant speed of 0.5m/s for 4 seconds, pauses for 4 seconds
- 16. $300 Question from Graphs Graph the following situation: A puppy is lost 80 meters away from his home. It’s home is zero. It begins to head home at 10 m/s for 8 seconds until it makes it back home
- 17. $300 Answer from Graphs
- 18. $400 Question from Graphs What does the horizontal line represent in Graph A? What does the horizontal line represent in Graph B? A B
- 19. $400 Answer from Graphs Graph A – Staying still (not moving) Graph B – Constant speed A B
- 20. $500 Question from Graphs What is the average speed of the marble? What is the speed at 3 seconds?
- 21. $500 Answer from Graphs Average speed = 10 meters/7 seconds = 1.43 m/s Speed at 3 seconds = 4 meters/3seconds = 1.33 m/s
- 22. $100 Question from Speed & Velocity What is speed? How do you calculate speed?
- 23. $100 Answer from Speed & Velocity Speed is the rate of motion; the distance an object travels in a unit of time Speed (m/s) = Distance (meters) Time (seconds)
- 24. $200 Question from Speed & Velocity Bart ran 5,000 meters from the cops at an average speed of 6 meters/second before he got caught. How long was he running?
- 25. $200 Answer from Speed & Velocity Speed = Distance Time Rearrange the formula Time = Distance Speed 5, 000 meters = 833.33 seconds 6 m/s
- 26. $300 Question from Speed & Velocity What is the speed of a walking person in m/s if the person travels 1000 m in 20 minutes?
- 27. $300 Answer from Speed & Velocity 20 minutes x 60 seconds = 1,200 seconds 1 minute 1,000 meters = 0.833 meters/second 1,200 seconds
- 28. $400 Question from Speed & Velocity If Justin races his BMW M5 down I-71 for 2,560 meters in 60 seconds, what is his average speed?
- 29. $400 Answer from Speed & Velocity 2,560 meters = 42.67 meters/second 60 seconds
- 30. $500 Question from Speed & Velocity Which of these 3 lines has the fastest average speed?
- 32. $100 Question from Forces What forces are involved in this situation? Are the forces balanced or unbalanced?
- 33. $100 Answer from Forces Normal Force (F N ) Gravity (F G ) Balanced Forces
- 34. $200 Question from Forces Are the forces acting upon this skydiver balanced or unbalanced? Which way is he moving? Is he speeding up or slowing down?
- 35. $200 Answer from Forces Unbalanced forces. Accelerating (speeding up) toward the ground.
- 36. $300 Question from Forces Describe the direction the Batmobile is moving and speed at which it is moving.
- 37. $300 Answer from Forces Moving to the right and speeding up
- 38. $400 Question from Forces What forces are acting on this skier? Draw a diagram showing the force arrows.
- 39. $400 Answer from Forces
- 40. $500 Question from Forces Describe the direction the fridge is moving and the speed of the fridge.
- 41. $500 Answer from Forces Moving left and slowing down.
- 42. $100 Question from Random Which graph shows increasing speed?
- 43. $100 Answer from Random They both do!
- 44. $200 Question from Random If it takes Jill 3 seconds to run from the batter’s box to 1 st base at an average speed of 6.5 m/s, what is the distance she covers in that time?
- 45. $200 Answer from Random Speed = Distance rearrange the formula to Speed x Time = Distance Time 6.5 m/s x 3 s = 19.5 meters
- 46. $300 Question from Random A physics teacher walks 4 meters East, 2 meters South, 4 meters West, and finally 2 meters North. What is his total distance traveled? What is his displacement?
- 47. $300 Answer from Random Distance = 12 meters Displacement = 0
- 48. $400 Question from Random Does the object depicted in this graph ever move at constant speed? If so, when?
- 49. $400 Answer from Random Moves at constant speed of 1 m/s from 0 seconds to 3 seconds.
- 50. $500 Question from Random Describe the motion of this object from 4 seconds to 6 seconds.
- 51. $500 Answer from Random No motion. Staying put 6 miles away from origin.
- 52. Final Jeopardy So, is the ball moving?
- 53. Final Jeopardy Answer It depends on your perspective and what you choose as your reference point.
