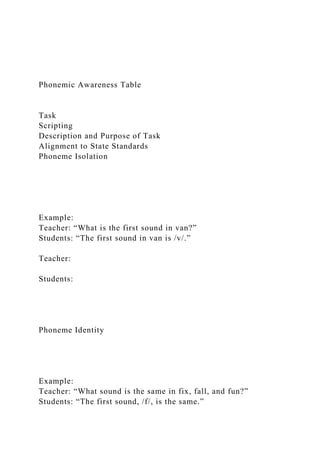
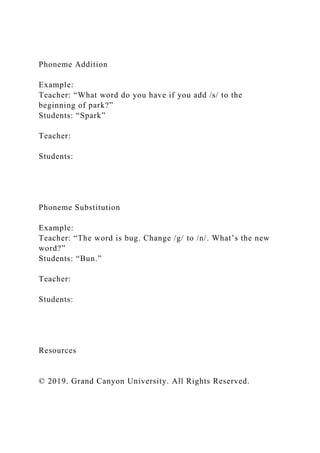
The document outlines the importance of phonemic awareness in relation to reading and spelling, providing examples of phoneme isolation, identity, categorization, blending, segmentation, deletion, addition, and substitution for educational purposes. It emphasizes the need for script preparation by educators to facilitate engaging literacy lessons while aligning with state standards. Additionally, it includes guidelines for creating a security strategy as an IT professional, detailing the development of policies, standards, and practices for a business environment.