PCI Challenges
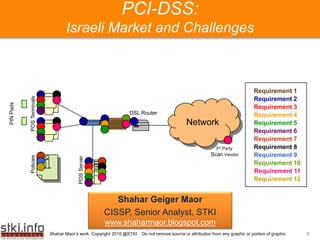
- 1. PCI-DSS: Israeli Market and Challenges Requirement 1 POS Terminals Requirement 2 PIN Pads Requirement 3 DSL Router Requirement 4 Network Requirement 5 Your Text here Your TextRequirement 6 here Requirement 7 3rd Party Requirement 8 Scan Vendor Requirement 9 Policies POS Server Requirement 10 Requirement 11 Requirement 12 Shahar Geiger Maor CISSP, Senior Analyst, STKI www.shaharmaor.blogspot.com Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 1
- 2. Presentation’s Agenda A short review of the Israeli market The Idea here Your Text behind PCI DSS Your Text here PCI trends and challenges Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 2
- 3. Information Security: Israeli Market Size (M$) 2009 changes 2010 changes 2011 changes 2012 Security 85.0 23.53% 105.0 4.76% 110.0 9.09% 120.0 Software GRC &Your Text here Your Text here 50.0 50.00% 75.0 9.33% 82.0 9.76% 90.0 BCP Security 85.0 11.76% 95.0 8.42% 103.0 6.80% 110.0 VAS totals 220.0 25.00% 275.0 7.27% 295.0 8.47% 320.0 Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 3
- 4. What’s on the CISO’s Agenda? (STKI Index 2009) Sec Tools SIEM/SOC 5% Miscellaneous 5% 5% NAC Encryption 18% 9% Access/Authent Market/Trends ication 10% 15% Your Text here Your Text here DB/DC SEC 10% EPS/mobile DLP 15% 10% Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 4
- 5. What’s on the PCI DSS Agenda? Control Objectives PCI DSS Requirements 1. Install and maintain a firewall configuration to protect Build and Maintain a Secure Network cardholder data 2. Do not use vendor-supplied defaults for system passwords and other security parameters Protect Cardholder Data 3. Protect stored cardholder data 4. Encrypt transmission of cardholder data across open, public networks 5. Use and regularly update anti-virus software on all Maintain a Vulnerability Management Program systems commonly affected by malware Your Text here Your Text here 6. Develop and maintain secure systems and applications 7. Restrict access to cardholder data by business need- Implement Strong Access Control Measures to-know 8. Assign a unique ID to each person with computer access 9. Restrict physical access to cardholder data 10. Track and monitor all access to network resources Regularly Monitor and Test Networks and cardholder data 11. Regularly test security systems and processes Maintain an Information Security Policy 12. Maintain a policy that addresses information security Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 5
- 6. What’s on the CISO’s Agenda? (STKI Index 2009) Build and Maintain a Sec Tools Regularly Monitor and Secure Network SIEM/SOC Test Networks 5% Miscellaneous 5% 5% NAC Encryption 18% 9% Protect Access/Authent Cardholder Data ication Market/Trends 10% Maintain a Vulnerability 15% Your Text here Management Program Your Text here Maintain an Information Security Policy DB/DC SEC 10% EPS/mobile DLP 15% 10% Implement Strong Protect Access Control Cardholder Data Measures Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 6
- 7. What’s on the CISO’s Agenda? (STKI Index 2009) Sec Tools SIEM/SOC 5% Miscellaneous 5% 5% NAC Encryption 18% 9% Access/Authent Market/Trends ication 10% 15% Your Text here Your Text here DB/DC SEC 10% EPS/mobile DLP 15% 10% Protect Cardholder Data Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 7
- 8. Presentation’s Agenda A short review of the Israeli market The Idea here Your Text behind PCI DSS Your Text here PCI trends and challenges Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 8
- 9. What is the Incentive? Your Text here Your Text here Shahar Maor’s work Copyright 2010 @STKI Source: http://datalossdb.org/statistics?timeframe=all_time Do not remove source or attribution from any graphic or portion of graphic 9
- 10. What is the Incentive? 2,754 • Data loss incidents 396 (35%) • Credit-card related data loss Hack (48%) • How? Your Text here Your Text here 297,704,392 • CCN compromised 751,779 • …CCNsIncident ? • Actual $$$ loss… Shahar Maor’s work Copyright 2010 @STKI Source: http://datalossdb.org/statistics?timeframe=all_time (2000-2010) Do not remove source or attribution from any graphic or portion of graphic 10
- 11. Data Loss Analysis –Answering the “How?” Q Hack Fraud LostStolen X Web General Your Text here Your Text here Unknown CCN Disposal_Document Email Virus 0% 10% 20% 30% 40% 50% 60% Shahar Maor’s work Copyright 2010 @STKI Source: http://datalossdb.org/statistics?timeframe=all_time (2000-2010) Do not remove source or attribution from any graphic or portion of graphic 11
- 12. Who’s Who PCI Council (By the PCI DSS): • outlined the MINIMUM data security protections measures for payment card data • Defined merchants and service providersYour Text here Your Text here levels and compliance validation requirements Cards brands(PCI Regime): • Initiated PCI DSS • Will enforce PCI Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 12
- 13. Who’s Who Your Text here Your Text here merchants and service providers Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 13
- 14. PCI DSS Payment Card Payment Card Industry Your Text here Your Text here (Data security) Data Security Standard Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 14
- 15. PCI DSS (in other words…) PCI DSS Your Text here Your Text here Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 15
- 16. Presentation’s Agenda A short review of the Israeli market The Idea here Your Text behind PCI DSS Your Text here PCI trends and challenges Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 16
- 17. Israeli PCI: Market Status (May 2010) RetailWhole saleManu’ Sector PCI Financial Compliance Sector TelcoServices Sector 1-4 4+ Milestones Milestones Your Text here PCI work Your Text here plan (Prioritized Healthcare Sector Gap Approach?) Analysis PCI “Newborns” Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 17
- 18. PCI Challenges: Requirement No 3 Control Objectives PCI DSS Requirements 1. Install and maintain a firewall configuration to protect Build and Maintain a Secure Network cardholder data 2. Do not use vendor-supplied defaults for system passwords and other security parameters Protect Cardholder Data 3. Protect stored cardholder data 4. Encrypt transmission of cardholder data across open, public networks 5. Use and regularly update anti-virus software on all Maintain a Vulnerability Management Program systems commonly affected by malware Your Text here Your Text here 6. Develop and maintain secure systems and applications 7. Restrict access to cardholder data by business need- Implement Strong Access Control Measures to-know 8. Assign a unique ID to each person with computer access 9. Restrict physical access to cardholder data 10. Track and monitor all access to network resources Regularly Monitor and Test Networks and cardholder data 11. Regularly test security systems and processes Maintain an Information Security Policy 12. Maintain a policy that addresses information security Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 18
- 19. PCI Challenges: Requirement No 3 Control Objectives PCI DSS Requirements 1. Install and maintain a firewall configuration to protect Build and Maintain a Secure Network cardholder data 2. Do not use vendor-supplied defaults for system passwords and other security parameters Protect Cardholder Data 3. Protect stored cardholder data 4. Encrypt transmission of cardholder data across open, public networks 5. Use and regularly update anti-virus software on all Maintain a Vulnerability Management Program systems commonly affected by malware Your Text here Your Text here 6. Develop and maintain secure systems and applications 7. Restrict access to cardholder data by business need- Implement Strong Access Control Measures to-know 8. Assign a unique ID to each person with computer access 9. Restrict physical access to cardholder data 10. Track and monitor all access to network resources Regularly Monitor and Test Networks and cardholder data 11. Regularly test security systems and processes Maintain an Information Security Policy 12. Maintain a policy that addresses information security Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 19
- 20. PCI Challenges: Requirement No 3 R 3.3: • Masking -mask PAN (Primary Account Number) when displayed (the first six and last four digits are the maximum number of digits to be displayed). R 3.4: • Index Token -A cryptographic token that replaces the PAN, Your Text here Your Text here based on a given index for an unpredictable value. • One-way hashes based on strong cryptography • Truncation -only a portion (not to exceed the first six and last four digits) of the PAN is stored. • Strong cryptography with associated key management processes Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 20
- 21. PCI Challenges: The “New trend Syndrome” Your Text here Your Text here Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 21
- 22. PCI Challenges: End-User Experience System heterogeneity –Sensitive data is scattered around in all sorts of formats Main-Frame here other legacy systems –how Textit possible Your Text and Your is here to protect sensitive data without changing the source code? What happened to risk management??? (PCI vs. SOX) Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 22
- 23. PCI Challenges: End-User Experience 2 “My DB does not support PCI” –the “Upgrade vs. pay the fine” dilemma “Index token is cheaper than other alternatives” –True or false? Your Text here Your Text here should be Inadequate knowledge of the QSAs? answered by Who audit the auditors? the PCI Council Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 23
- 24. PCI Challenges -The PCI paradox PCI compliance Remember 1 security that security patch is Your Text herepatch? Your missing Text here An A data loss investigation incident starts occurs… Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 24
- 25. Conclusions and Opportunities Needs a house cleaning? PCI can help PCI is basic security. Almost nothing new here… Think “security & risk” instead of “compliance & audit” PCI (and other regulations) are the “floor” andhere the Your Text here Your Text not “ceiling” of security measures Stop waiting! act now (….but not before 11.7.2010) Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 25
- 26. Thank you! shahar@stki.info Shahar Maor’s work Copyright 2010 @STKI Do not remove source or attribution from any graphic or portion of graphic 26
