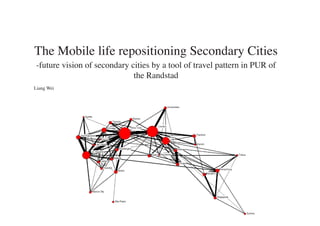
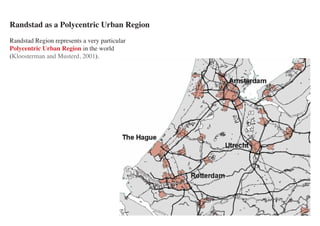
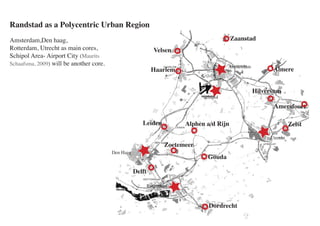
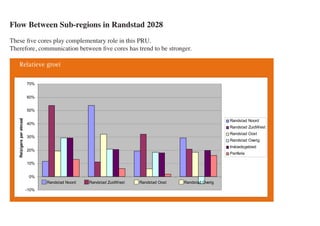
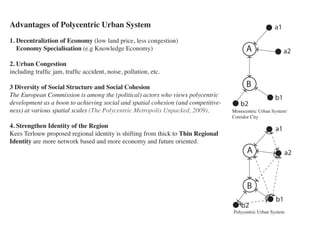
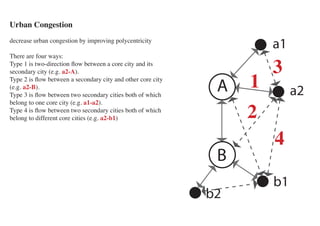
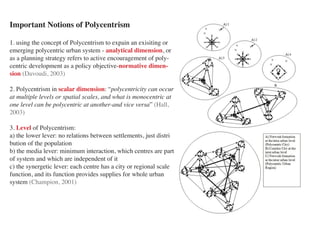
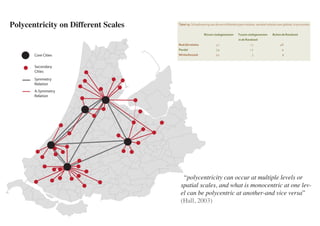
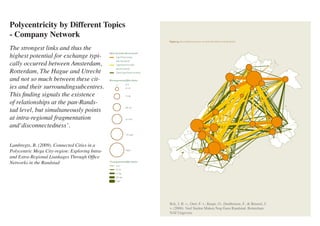
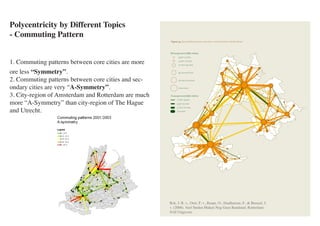
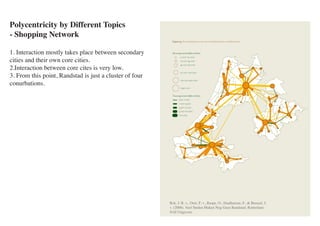
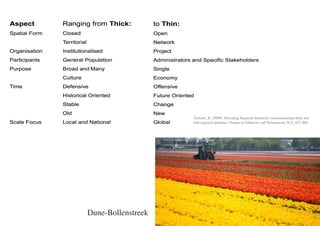
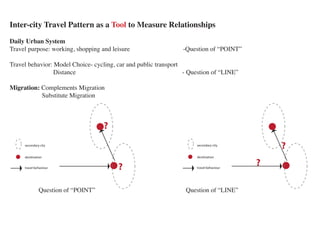
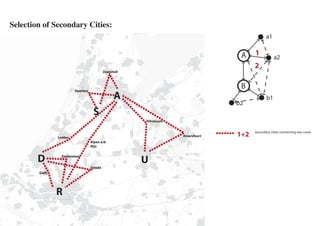
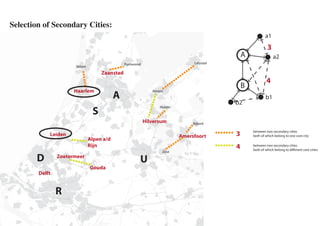
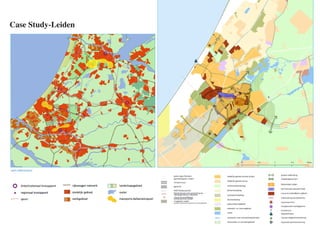
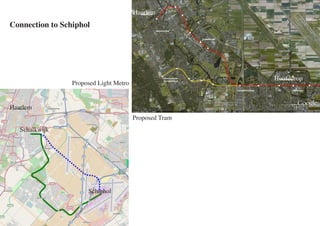
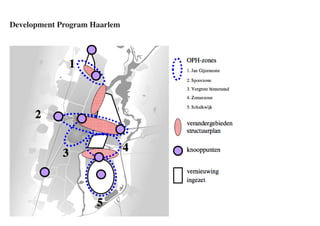
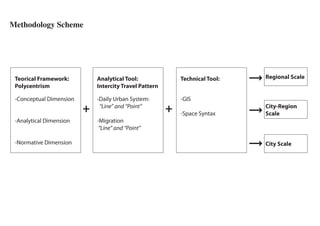
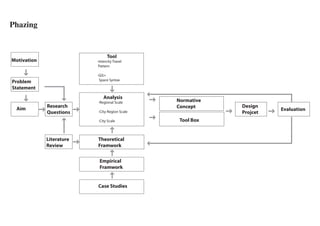
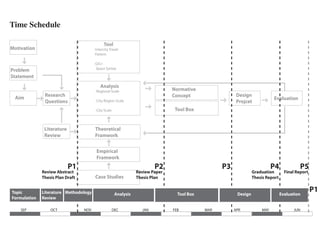
Secondary cities in the Randstad play various roles in contributing to the emergence of a polycentric spatial structure. The document analyzes how secondary cities connect core cities through travel patterns, and discusses their development potentials. It also examines case studies of Leiden and Haarlem to understand how urban form and identities can promote regional polycentricity and identity.