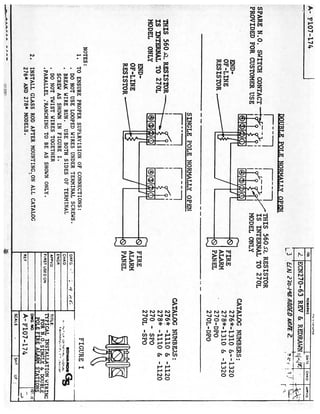
Edwards Signaling P-039250 Installation Manual
•
0 likes•168 views
Buy the Edwards Signaling P-039250 at JMAC Supply. https://www.jmac.com/Edwards_Signaling_P_039250_p/edwards-signaling-p-039250.htm?=slideshare
Report
Share
Report
Share
Download to read offline
Recommended
Stb 2091 2010

Russia petroleum, construction, development, import, export, customs, oil and gas, steel, metallurgy, mineral resources, railway, railroad, codes, rules, norms, laws, approval, certification, decrees, regulations
Your Story in Three Minutes and How to Make It Matter!

How do you capture your audience and tell your story when you only have three to five minutes to thank your donor, shake hands and accept the check? How do you take advantage of those small but mighty pockets of time to inspire your audience and increase their support and goodwill? Andrea Beaulieu will share how you can make your story matter to your audience no matter how much, or how little time you have so they walk away knowing why they support you and why they want to continue to do so.
Recommended
Stb 2091 2010

Russia petroleum, construction, development, import, export, customs, oil and gas, steel, metallurgy, mineral resources, railway, railroad, codes, rules, norms, laws, approval, certification, decrees, regulations
Your Story in Three Minutes and How to Make It Matter!

How do you capture your audience and tell your story when you only have three to five minutes to thank your donor, shake hands and accept the check? How do you take advantage of those small but mighty pockets of time to inspire your audience and increase their support and goodwill? Andrea Beaulieu will share how you can make your story matter to your audience no matter how much, or how little time you have so they walk away knowing why they support you and why they want to continue to do so.
Centrality Prediction in Mobile Social Networks

By analyzing evolving centrality roles using time dependent graphs, researchers may predict future centrality values. This may prove invaluable in designing efficient routing and energy saving strategies and have profound implications on evolving social behavior in dynamic social networks. In this paper, we propose a new method to predict centrality values of nodes in a dynamic environment. The proposed method is based on calculating the correlation between current and past measure of centrality for each corresponding node, which is used to form a composite vector to represent the given state of centralities. The performance of the proposed method is evaluated through simulated predictions on data sets from real mobile networks. Results indicate significantly low prediction error rate occurs, with a suitable implementation of the proposed method.
Dificuldades no mindfulness

Ao praticar Mindfulness lidamos com dificuldades que nem sempre sabemos dar resposta. Aqui seguem algumas sugestões para um novo olhar sobre a sua prática.
Bosch ALTV244UL Data Sheet

Buy the Bosch ALTV244UL at JMAC Supply!
https://www.jmac.com/Bosch_Security_ALTV244UL_p/bosch-altv244ul.htm?=slideshare
Bosch AL1002WAL Data Sheet

Buy the Bosch AL1002WAL at JMAC Supply!
https://www.jmac.com/Bosch_Security_AL1002WAL_p/bosch-al1002wal.htm?=slideshare
Bosch AIM-AEC21-CVT Data Sheet

Buy the Bosch AIM-AEC21-CVT at JMAC Supply!
https://www.jmac.com/Bosch_Security_AIM_AEC21_CVT_p/bosch-aim-aec21-cvt.htm?=slideshare
Bosch AI1 Data Sheet

Buy the Bosch AI1 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AI1_p/bosch-ai1.htm?=slideshare
Bosch AH-24WP-R Data Sheet

Buy the Bosch AH-24WP-R at JMAC Supply!
https://www.jmac.com/product_p/bosch-ah-24wp-r.htm?=slideshare
Bosch AEC-8I8O-EXT Data Sheet

Buy the Bosch AEC-8I8O-EXT at JMAC Supply!
https://www.jmac.com/Bosch_Security_AEC_8I8O_EXT_p/bosch-aec-8i8o-ext.htm?=slideshare
Bosch AE774 Data Sheet

Buy the Bosch AE774 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE774_p/bosch-ae774.htm?=slideshare
Bosch AE203R Data Sheet

Buy the Bosch AE203R at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE203R_p/bosch-ae203r.htm?=slideshare
Bosch AE101 Data Sheet

Buy the Bosch AE101 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE101_p/bosch-ae101.htm?=slideshare
Bosch AE4 Data Sheet

Buy the Bosch AE4 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE4_p/bosch-ae4.htm?=slideshare
Bosch AE1 Data Sheet

Buy the Bosch AE1 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE1_p/bosch-ae1.htm?=slideshare
Bosch ACD-IC16K37-50 Data Sheet

Buy the Bosch ACD-IC16K37-50 at JMAC Supply!
https://www.jmac.com/Bosch_Security_ACD_IC16K37_50_p/bosch-acd-ic16k37-50.htm?=slideshare
Bosch ACD-IC2K37-50 Data Sheet

Buy the Bosch ACD-IC2K37-50 at JMAC Supply!
https://www.jmac.com/Bosch_Security_ACD_IC2K37_50_p/bosch-acd-ic2k37-50.htm?=slideshare
More Related Content
Viewers also liked
Centrality Prediction in Mobile Social Networks

By analyzing evolving centrality roles using time dependent graphs, researchers may predict future centrality values. This may prove invaluable in designing efficient routing and energy saving strategies and have profound implications on evolving social behavior in dynamic social networks. In this paper, we propose a new method to predict centrality values of nodes in a dynamic environment. The proposed method is based on calculating the correlation between current and past measure of centrality for each corresponding node, which is used to form a composite vector to represent the given state of centralities. The performance of the proposed method is evaluated through simulated predictions on data sets from real mobile networks. Results indicate significantly low prediction error rate occurs, with a suitable implementation of the proposed method.
Dificuldades no mindfulness

Ao praticar Mindfulness lidamos com dificuldades que nem sempre sabemos dar resposta. Aqui seguem algumas sugestões para um novo olhar sobre a sua prática.
Viewers also liked (9)
More from JMAC Supply
Bosch ALTV244UL Data Sheet

Buy the Bosch ALTV244UL at JMAC Supply!
https://www.jmac.com/Bosch_Security_ALTV244UL_p/bosch-altv244ul.htm?=slideshare
Bosch AL1002WAL Data Sheet

Buy the Bosch AL1002WAL at JMAC Supply!
https://www.jmac.com/Bosch_Security_AL1002WAL_p/bosch-al1002wal.htm?=slideshare
Bosch AIM-AEC21-CVT Data Sheet

Buy the Bosch AIM-AEC21-CVT at JMAC Supply!
https://www.jmac.com/Bosch_Security_AIM_AEC21_CVT_p/bosch-aim-aec21-cvt.htm?=slideshare
Bosch AI1 Data Sheet

Buy the Bosch AI1 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AI1_p/bosch-ai1.htm?=slideshare
Bosch AH-24WP-R Data Sheet

Buy the Bosch AH-24WP-R at JMAC Supply!
https://www.jmac.com/product_p/bosch-ah-24wp-r.htm?=slideshare
Bosch AEC-8I8O-EXT Data Sheet

Buy the Bosch AEC-8I8O-EXT at JMAC Supply!
https://www.jmac.com/Bosch_Security_AEC_8I8O_EXT_p/bosch-aec-8i8o-ext.htm?=slideshare
Bosch AE774 Data Sheet

Buy the Bosch AE774 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE774_p/bosch-ae774.htm?=slideshare
Bosch AE203R Data Sheet

Buy the Bosch AE203R at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE203R_p/bosch-ae203r.htm?=slideshare
Bosch AE101 Data Sheet

Buy the Bosch AE101 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE101_p/bosch-ae101.htm?=slideshare
Bosch AE4 Data Sheet

Buy the Bosch AE4 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE4_p/bosch-ae4.htm?=slideshare
Bosch AE1 Data Sheet

Buy the Bosch AE1 at JMAC Supply!
https://www.jmac.com/Bosch_Security_AE1_p/bosch-ae1.htm?=slideshare
Bosch ACD-IC16K37-50 Data Sheet

Buy the Bosch ACD-IC16K37-50 at JMAC Supply!
https://www.jmac.com/Bosch_Security_ACD_IC16K37_50_p/bosch-acd-ic16k37-50.htm?=slideshare
Bosch ACD-IC2K37-50 Data Sheet

Buy the Bosch ACD-IC2K37-50 at JMAC Supply!
https://www.jmac.com/Bosch_Security_ACD_IC2K37_50_p/bosch-acd-ic2k37-50.htm?=slideshare
Bosch ACA-IC2K26-10 Data Sheet

Buy the Bosch ACA-IC2K26-10 at JMAC Supply!
https://www.jmac.com/Bosch_Security_ACA_IC2K26_10_p/bosch-aca-ic2k26-10.htm?=slideshare
Bosch 9208B Data Sheet

Buy the Bosch 9208B at JMAC Supply!
https://www.jmac.com/Bosch_Security_9208B_p/bosch-9208b.htm?=slideshare
Bosch 7110XC Data Sheet

Buy the Bosch 7110XC at JMAC Supply!
https://www.jmac.com/Bosch_Security_7110XC_p/bosch-7110xc.htm?=slideshare
Samsung Techwin SNB-1000 Data Sheet

Buy the Samsung Techwin SNB-1000 at JMAC Supply!
https://www.jmac.com/Samsung_Techwin_SNB1000_p/samsung-techwin-snb1000.htm?=slideshare
Samsung Techwin SMT-4031 Data Sheet

Buy the Samsung Techwin SMT-4031 at JMAC Supply!
https://www.jmac.com/Samsung_Techwin_SMT_4031_p/samsung-techwin-smt-4031.htm?=slideshare
Samsung Techwin SMT-4023 Data Sheet

Buy the Samsung Techwin SMT-4023 at JMAC Supply!
https://www.jmac.com/Samsung_Techwin_SMT_4023_p/samsung-techwin-smt-4023.htm?=slideshare
Samsung Techwin SMT-3232 Data Sheet

Buy the Samsung Techwin SMT-3232 at JMAC Supply!
https://www.jmac.com/Samsung_Techwin_SMT3232_p/samsung-techwin-smt3232.htm?=slideshare
More from JMAC Supply (20)
Recently uploaded
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Recently uploaded (20)
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
