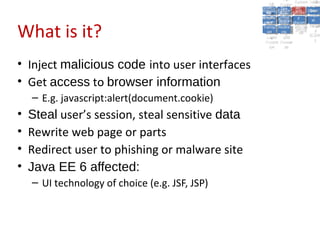
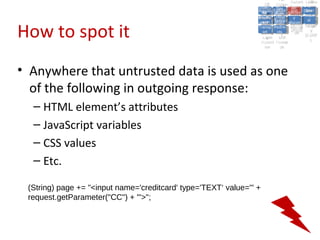
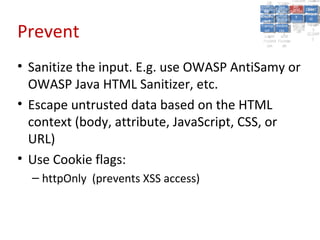
Cross-Site Scripting (XSS) involves injecting malicious scripts into web pages viewed by other users. Attackers can use XSS to steal user cookies and session tokens, or hijack user sessions to impersonate them. To prevent XSS, developers must sanitize all user input, escape output, and configure browsers to prevent script execution. The best practices are to use container security features whenever possible and review the OWASP Application Security Verification Standard.