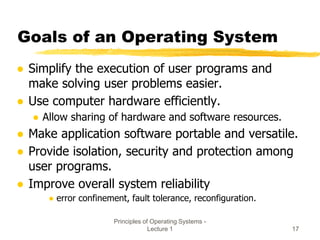
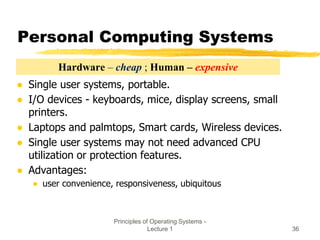
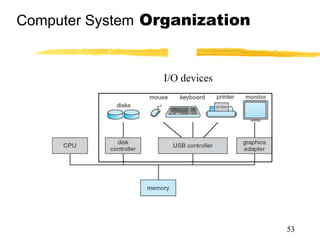
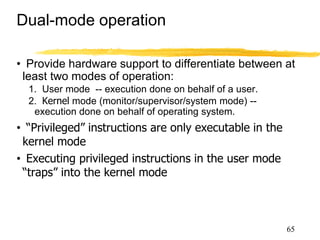
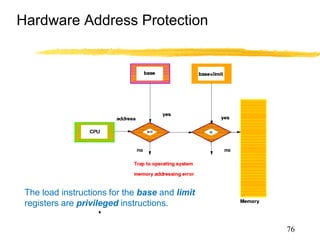
This document provides an overview of an introductory lecture on operating systems principles. It introduces the course, including the instructor, teaching assistants, schedule, textbook, and grading policy. It also covers basic topics that will be discussed over the course of the term, such as operating system structures and functions, components of a computer system, goals of an operating system, and the history of operating systems from early batch systems to modern parallel and distributed systems.
![Principles of Operating Systems -
Lecture 1 1
ICS 143A - Principles of
Operating Systems
(Spring 2020)
Lecture 1 - Introduction and Overview
MWF 11:00- 11:50 a.m.
Prof. Nalini Venkatasubramanian
( nalini@uci.edu )
[lecture slides contains some content adapted from :
Silberschatz textbook authors, John Kubiatowicz (Berkeley)
Anderson textbook, John Ousterhout(Stanford), Prof. Ardalan
Sani, )
]](https://image.slidesharecdn.com/oslectureset1spr20-230829051119-f23b383f/85/oslectureset1spr20-pptx-1-320.jpg)