Optism Permission-Based Mobile Marketing Solution Overview
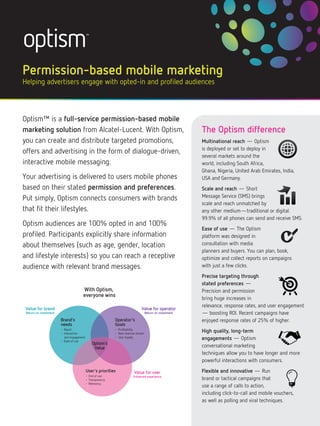
- 1. Permission-based mobile marketing Helping advertisers engage with opted-in and profiled audiences Optism™ is a full-service permission-based mobile marketing solution from Alcatel-Lucent. With Optism, The Optism difference you can create and distribute targeted promotions, Multinational reach — Optism is deployed or set to deploy in offers and advertising in the form of dialogue-driven, several markets around the interactive mobile messaging. world, including South Africa, Ghana, Nigeria, United Arab Emirates, India, Your advertising is delivered to users mobile phones USA and Germany. based on their stated permission and preferences. Scale and reach — Short Put simply, Optism connects consumers with brands Message Service (SMS) brings scale and reach unmatched by that fit their lifestyles. any other medium—traditional or digital. 99.9% of all phones can send and receive SMS. Optism audiences are 100% opted in and 100% Ease of use — The Optism profiled. Participants explicitly share information platform was designed in about themselves (such as age, gender, location consultation with media planners and buyers. You can plan, book, and lifestyle interests) so you can reach a receptive optimize and collect reports on campaigns audience with relevant brand messages. with just a few clicks. Precise targeting through stated preferences — With Optism, Precision and permission everyone wins bring huge increases in relevance, response rates, and user engagement Value for brand Value for operator Return on investment Return on investment — boosting ROI. Recent campaigns have Brand’s Operator’s enjoyed response rates of 25% of higher. needs Goals • Reach • Interaction • Profitability • New revenue stream High quality, long-term and engagement • Ease of use • User loyalty engagements — Optism Optism’s Value conversational marketing techniques allow you to have longer and more powerful interactions with consumers. User’s priorities Value for user Flexible and innovative — Run • End of use Enhanced experience • Transparency brand or tactical campaigns that • Relevancy use a range of calls to action, including click-to-call and mobile vouchers, as well as polling and viral techniques.
- 2. 100% opted-in, Delivering results 100% profiled Optism’s highly engaged audiences audiences provide industry-leading response rates Rich dialogue — and you only pay for communications Put the audience in control and drive that are delivered. You’ll receive detailed engagement with a rich dialogue analytics and insights, so you can campaign — perfect for polls, gaining develop a better understanding of your insight and increasing loyalty through audience. For example, you can learn mobile communities. Combine images how different demographics engage with and question-and-answer exchanges to campaigns by the choices they make. adidas® rich dialogue grab people’s attention and focus in on Because Optism audiences have campaign in Egypt — an individual’s preferences. Wrap up the 35% response rate explicitly opted in to receive ads and exchange with an easy one-click call to told us about themselves, you won’t be adidas used Mobinil Ad’s Optism- action, including click-to-call or click- wasting media spend directing football enabled service to encourage people through to your website. ads to someone who isn’t interested in to visit its new Originals store in Cairo. The campaign was equally well Text dialogue sports. We help you achieve your received by men and women, both Think rich dialogue — without the campaign objective, whether that’s to Arabic and English speaking. pictures. Text dialogues are a simple increase brand awareness, strengthen and effective way to engage in a customer loyalty, or reach untapped conversation with a consumer and offer market segments. the same calls to action using 160 characters. Volkswagen text dialogue campaign in Ghana — Rich and text push 30% response rate Use picture-enriched or plain text Universal Motors, the exclusive dealer messages to create brand awareness. for Volkswagen in Ghana, wanted to For rich push messages, make an impact alert customers that a new shipment with a full screen image and up to 500 of cars was in stock. 90% of respon- characters. Text push messages use 160 dents were interested in receiving characters. Again, you can use click-to- more information. call and click-through calls to action to keep the conversation going. For more information go to www.optism.com
