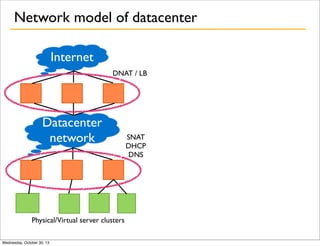
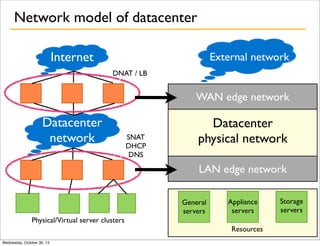
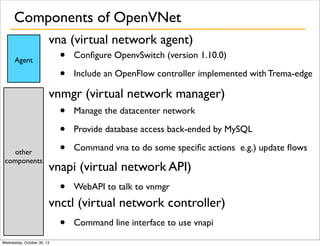
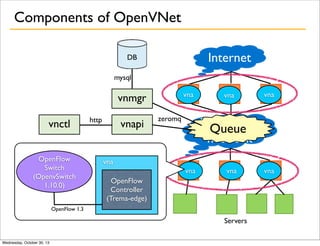
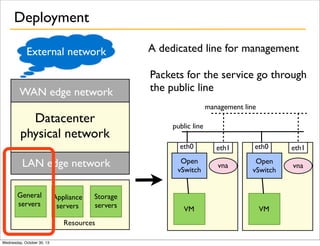
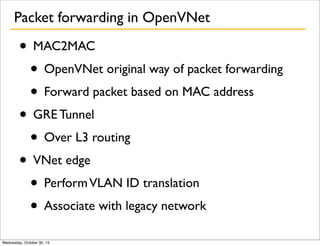
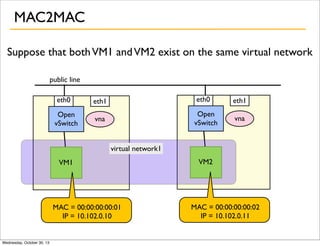
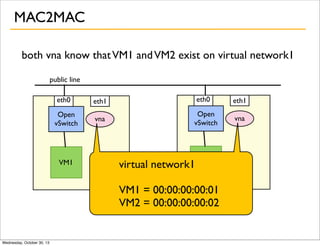
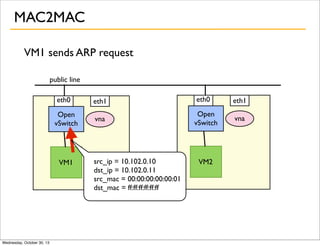
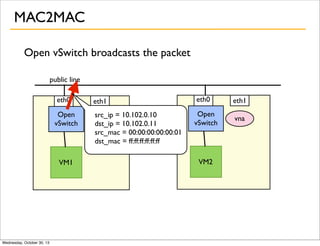
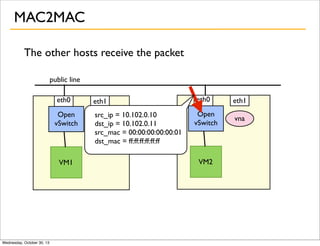
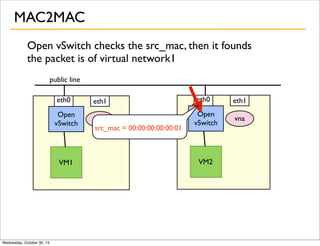
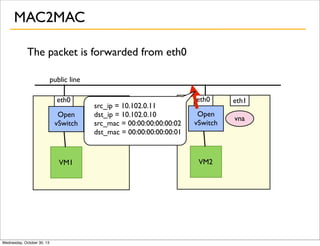
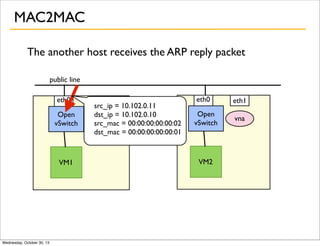
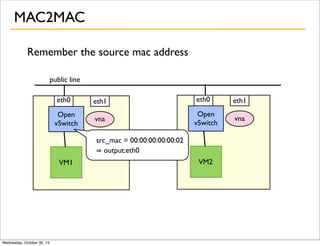
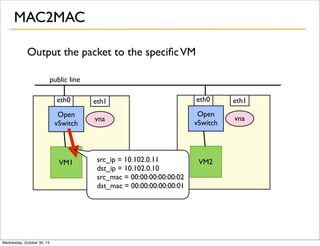
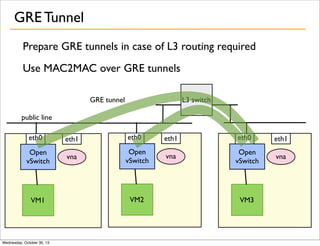
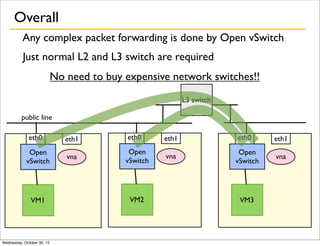
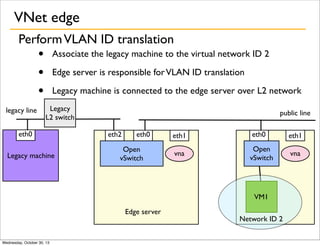
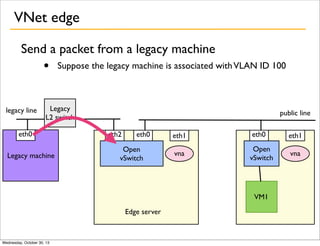
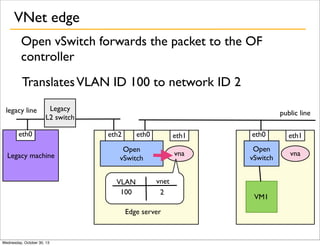
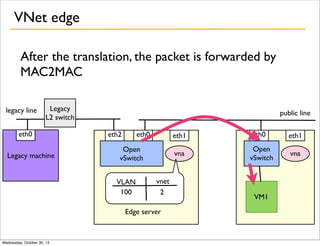
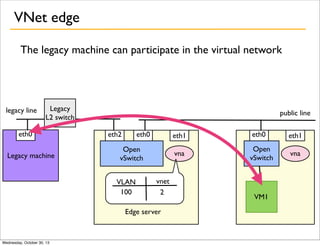
OpenVNet is a network virtualization project that started as a spin-off from Wakame-VDC, allowing users to create and manage networks easily and at no cost. The system employs a virtual network agent (VNA) and utilizes Open vSwitch to handle packet forwarding and VLAN ID translation, enabling complex multi-tenant networks while simplifying physical infrastructure. Key advantages include reduced maintenance costs and the ability to integrate with legacy networks.